1. Multi-extortion: the latest ransomware trend to know
Trend: Attackers are now layering encryption with data theft, distributed denial-of-service (DDoS) attacks, and direct client harassment to force payment, even when backups exist.
A robust backup strategy alone doesn’t cut it when ransomware is on the rise, because encryption is often just the final step in a much longer attack chain.
We’re witnessing the standardization of triple and quadruple extortion tactics designed to apply maximum pressure on targets, like the 2023 Black Cat/ALPHV attack, where Black Cat filed a complaint with the Securities and Exchange Commission (SEC) that MeridianLink, an attack victim, failed to report a cyberattack within four days.
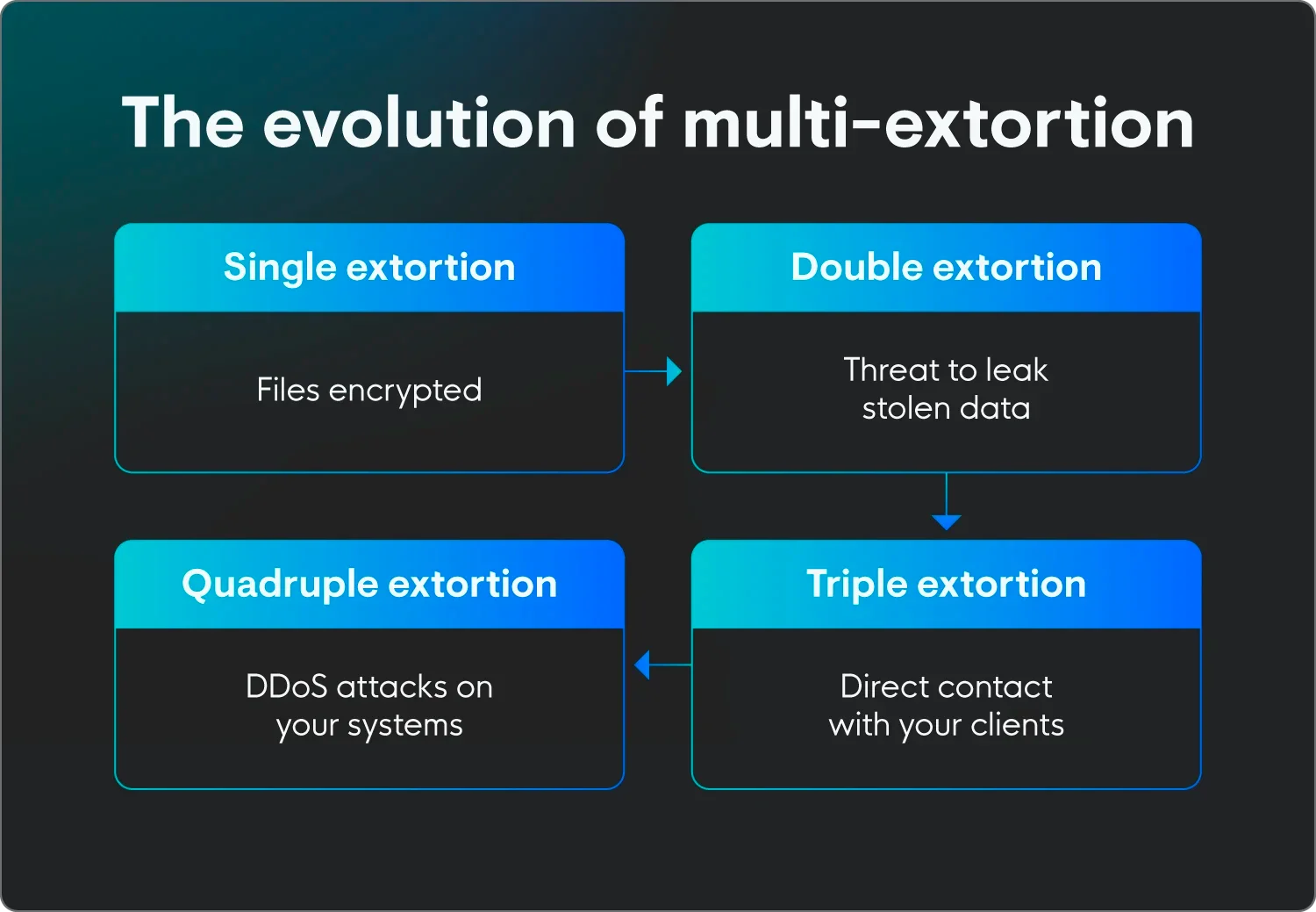
This is how extortion tactics start:
-
Double extortion: Attackers pull sensitive data before locking your systems. They’ll threaten to leak this ransomware data on the dark web if you refuse to pay them for the decryptor, even if you can restore everything from backups.
-
Triple extortion: Attackers take the fight to your stakeholders. They’re contacting clients, patients, or partners directly, telling them that their data has been stolen and urging them to pressure you into paying.
-
Quadruple extortion: While you’re struggling to restore your servers and manage the legal fallout of a data breach, the attackers launch a DDoS attack against your public-facing website or customer portals. It paralyzes your communication channels and creates panic.
How this ransomware trend looks in the real world:
A chilling example of multi-extortion happened when threat actors breached Finnish psychotherapy provider Vastaamo and started individually extorting thousands of patients after the primary organization refused to pay. It proves that triple extortion can extend harm far beyond corporate boundaries.
It’s a total siege mentality that requires defense in depth, like the Huntress Managed Security Platform offers. That includes employee training to spot threats, SIEM for broad-based attack detection, and endpoint and identity detection and response when shady hackers slip through the cracks.