
What is a Security Operations Center?
Published: 10/03/2025
Last Updated: 3/26/2026



A Security Operations Center (SOC) is a team of security analysts who monitor, detect, investigate, and respond to cybersecurity threats — typically around the clock. The SOC is an organization's central hub for security operations: analysts use a combination of SIEM, EDR, and identity monitoring tools to watch for suspicious activity and act on it before damage is done.
Key Takeaways
- A SOC is a team — not a tool or a room — of security analysts responsible for monitoring, investigating, and responding to threats across an organization's environment, 24 hours a day.
- SOC analysts triage security alerts, investigate confirmed incidents, contain active threats, and coordinate remediation. Their job is to turn raw security telemetry into resolved incidents.
- A SOC focuses on security threats (malware, credential theft, ransomware, unauthorized access); a NOC focuses on network performance (uptime, latency, connectivity). They serve distinct functions and operate separately.
- Organizations without in-house SOC capacity can access 24/7 analyst coverage through managed detection and response (MDR) — a service model that delivers SOC outcomes without requiring the organization to build and staff a SOC from scratch.
- Huntress operates a 24/7 SOC whose analysts work as an extension of MSP and IT teams — triaging alerts, investigating incidents, and remediating threats inside the same tools clients already use.
What Does a Security Operations Center Do?
A Security Operations Center (SOC) is essentially your cybersecurity command center. Think of it as the nerve center where a dedicated team monitors, analyzes, and mitigates potential threats 24/7. Whether it’s safeguarding sensitive data, spotting vulnerabilities, or responding to active threats, a SOC orchestrates cybersecurity operations to neutralize risks before they escalate.
SOC responsibilities aren't limited to just identifying threats; they encompass fortifying an organization’s overall security posture. From deploying advanced tools like SIEM (Security Information and Event Management) systems to conducting post-incident forensic analysis, the SOC is crucial in keeping businesses secure against cyberattacks.
How does a SOC work?
An SOC typically operates as a centralized or hybrid team employing a multi-layered approach to cybersecurity. Here’s how typical SOC operations unfold:
1. Threat Monitoring
Continuous surveillance of systems, networks, and endpoints using advanced monitoring tools such as SIEM platforms to identify potential vulnerabilities.
2. Incident Detection
Use of threat intelligence, behavioral analytics, and renowned strategies like anomaly detection to spot potential risks or breaches early.
3. Incident Containment
Once threats are detected, the SOC team swiftly contains and mitigates them to minimize disruption or damage.
4. Investigation and Forensics
SOC analysts analyze security incidents post-mitigation to determine their origin, impact, and potential prevention strategies for future resilience.
5. Continuous Optimization
A proactive SOC constantly adapts and evolves by applying lessons from past incidents and addressing emerging cybersecurity challenges.
What Are the Components of a SOC?
Whether integrated in-house or outsourced to a managed SOC provider, a well-functioning SOC typically consists of the following components:
1. Detection and Response Tools
SIEM Solutions: Aggregate and analyze data streams for unusual activity in real time.
Endpoint Detection and Response (EDR) tools to safeguard devices.
2. Threat intelligence integration
Continuous updates from global threat intelligence platforms help the SOC stay ahead of evolving tactics, techniques, and procedures (TTPs).
3. Skilled personnel
Roles within an SOC, such as cybersecurity analysts, incident responders, and SOC managers, work collaboratively to ensure robust security.
4. Playbooks and policies
Predefined workflows help streamline detection, escalation, and threat resolution processes to minimize errors and response delays.
5. Communication infrastructure
Real-time communication tools ensure coordination across internal teams and stakeholders during cybersecurity incidents.
What Is the Difference Between a SOC and a NOC?
SOC and NOC are often confused because both involve teams monitoring infrastructure around the clock — but they serve fundamentally different purposes. A Network Operations Center (NOC) focuses on keeping network infrastructure available and performing: uptime, latency, connectivity, hardware health. A SOC focuses on security: detecting adversarial activity, investigating breaches, and protecting data and systems from attack.
The distinction matters because the skills, tools, and response processes are different. A NOC engineer responding to a network outage and a SOC analyst investigating a credential theft incident are solving different problems, even if they're both staring at dashboards at 2 a.m.
|
|
SOC (Security Operations Center) |
NOC (Network Operations Center) |
|
Primary focus |
Detecting and responding to security threats |
Maintaining network uptime and performance |
|
What they monitor |
Security alerts, endpoint behavior, identity anomalies, threat indicators |
Network devices, bandwidth utilization, service availability |
|
Incident type |
Malware, ransomware, credential theft, unauthorized access, data breaches |
Outages, latency spikes, hardware failures, connectivity drops |
|
Core skill set |
Security analysis, incident investigation, digital forensics, threat intelligence |
Network administration, infrastructure management, systems monitoring |
|
Primary tools |
SIEM, EDR, identity monitoring, threat intelligence feeds |
Network monitoring platforms, performance dashboards, ticketing systems |
|
Response goal |
Contain the threat, preserve evidence, remediate root cause |
Restore service availability as quickly as possible |
|
Overlap |
SOC may escalate to NOC when network isolation is needed as a containment step |
NOC may escalate to SOC when anomalies suggest a security incident rather than a technical failure |
What Tools Does a SOC Use?
A SOC's effectiveness depends on having visibility across every layer of the environment. Most SOC teams build their toolstack around a core set of platforms that feed alerts into a central analysis workflow:
|
Tool Category |
What It Does |
Role in the SOC |
|
SIEM (Security Information and Event Management) |
Aggregates and correlates logs and security events from across the environment; generates alerts when patterns match known threat indicators |
Central alert intake — the primary queue SOC analysts work from |
|
EDR (Endpoint Detection and Response) |
Monitors activity on individual endpoints; detects malicious processes, lateral movement, and behavioral anomalies at the device level |
Primary source of endpoint telemetry; enables containment actions like isolating a compromised machine |
|
Identity Monitoring / ITDR |
Detects anomalous access patterns, credential misuse, privilege escalation, and identity-based attacks across Active Directory, Microsoft 365, and cloud environments |
Critical for catching credential-based attacks — the most common initial access vector |
|
Threat Intelligence Feeds |
Provides up-to-date data on known attacker infrastructure, malware hashes, and tactics, techniques, and procedures (TTPs) |
Enriches alerts with context — helps analysts determine whether an IP, domain, or file is associated with known adversaries |
|
SOAR (Security Orchestration, Automation, and Response) |
Automates repetitive response tasks — alert enrichment, containment playbooks, ticket creation — to reduce manual workload |
Frees analysts to focus on investigation rather than mechanical triage steps |
|
Case Management / Ticketing |
Tracks each incident from initial detection through resolution; maintains documentation for post-incident review and compliance reporting |
Creates accountability and audit trail; enables escalation and handoff between analysts |
|
Vulnerability Scanners |
Identifies unpatched systems, misconfigured services, and exposed attack surface before attackers can exploit them |
Provides proactive context — SOC analysts can prioritize based on what's actually exposed |
What Are the Benefits of a SOC?
Investing in a SOC offers unparalleled advantages for organizations prioritizing cybersecurity:
Proactive Threat Management: Catch potential attacks before they materialize into full-blown breaches, minimizing the risks of business disruption.
Improved Compliance: Ensure your organization adheres to industry regulations, standards, and frameworks, reducing related liabilities.
Round-the-Clock Monitoring: Cybersecurity doesn’t sleep. SOCs provide 24/7 vigilance to guard against threats.
Enhanced Reporting: Access detailed reports on performance, threats mitigated, and audits that can inform policymakers and improve strategy.
Strong Brand Trust: Preventing breaches safeguards sensitive customer and client information, engendering greater trust in your brand.
What Are the Challenges of Running a SOC?
While SOCs are indisputably valuable, their successful operation can come with challenges:
-
Alert Fatigue: An overabundance of alerts, especially false positives, can overwhelm analysts and slow down responses.
-
Talent Shortage: Cybersecurity remains one of the most in-demand skills, making it challenging to recruit experienced SOC professionals.
-
Cost: Building and maintaining an in-house SOC requires substantial investment in talent, tools, and infrastructure.
-
Scaling Issues: Growing organizations may outpace the capacity of their SOC, needing further resources to scale operations effectively.
Managed SOC services can help mitigate these challenges, providing expertise and infrastructure at a fraction of the effort and internal cost.
Industries that benefit from SOCs
While any business can benefit from a security operations center, certain industries experience the greatest need:
-
Healthcare: Protect sensitive patient data and meet regulations like HIPAA.
-
Finance: Safeguard critical financial systems and customer information while complying with PCI DSS and other standards.
-
Education: Prevent threats to student records and learning systems in compliance with GDPR or FERPA.
-
Government and Legal Services: Handle confidential data and protect against nation-state actors.
Establishing or enhancing a modern SOC
For organizations considering implementing or optimizing their SOCs:
-
Evaluate needs: Identify what components or support your business requires to meet current and future operations.
-
Choose between internal or managed SOC: Build an in-house capability or partner with a dedicated service provider for streamlined expertise and resources.
-
Invest in technology and staff training: Ensure tools are functional and analysts are consistently upskilled on threat landscapes and industry-best practices
-
Regular auditing and feedback: Continuously refine SOC operations, integrating lessons and emerging technologies into security playbooks.
Level up your cyber defense with a security operations center
An SOC is your organization’s first line of defense in a world of increasingly sophisticated cyber threats. Whether you’re establishing a new SOC or improving an existing one, the key lies in preparation, collaboration, and continuous optimization.
Need help getting started? Learn how Huntress can empower your organization with our cutting-edge security operations solutions designed to mitigate risks effectively.
A Practical Guide to Security Operations Centers (SOCs)
Our SOC Guide explains what a modern SOC does, why “always‑on” matters, and how to decide if you should build, buy, or borrow one.

FAQ
A SOC provides continuous monitoring and rapid response that most organizations can't sustain with general IT staff alone. It reduces the time between a threat entering the environment and being contained — which directly limits the damage a breach can cause. Without dedicated security operations, alerts go uninvestigated and incidents escalate
A SOC (Security Operations Center) handles security threats — malware, unauthorized access, credential theft, ransomware. A NOC (Network Operations Center) handles network performance — uptime, latency, hardware failures. Both run 24/7, but the skills, tools, and response goals are different. Large organizations often operate both; smaller ones frequently outsource one or both.
Yes. Managed SOC solutions make advanced cybersecurity accessible to small and medium enterprises without the need for costly in-house setups.
No. Any organization handling sensitive data or operating digitally can benefit from a SOC's protective capabilities.
Outsourced SOCs, also known as Managed SOCs, monitors your environment using their own analyst team and tooling. They investigate alerts, contain threats, and provide remediation guidance. The best providers integrate directly into your existing workflows rather than operating as a separate system, so your IT team gets actionable context, not just raw alerts.



Additional Resources
- Read more about What Is Identity Security Posture Management (ISPM)What is Identity Security Posture Management (ISPM)? Learn how ISPM helps organizations reach cybersecurity resilience with identity hardening.
- Read more about Managed Detection and Response (MDR) ExplainedManaged Detection and Response (MDR) ExplainedWhat is Managed Detection and Response (MDR)? It's 24/7 cybersecurity that combines technology & human expertise for threat hunting & rapid response. Learn more here!
- Read more about What is SecOps? Security Operations GuideWhat is SecOps? Security Operations GuideLearn what SecOps (Security Operations) means, core components, tools, and how to build effective security operations programs to protect your organization.
- Read more about What Is SOAR? Security Orchestration ExplainedWhat Is SOAR? Security Orchestration ExplainedDrowning in security alerts? Learn how SOAR (Security Orchestration, Automation, and Response) helps teams fight cyber threats faster and more efficiently.
- Read more about What Is a Security Operations Report? SOC ReportsWhat Is a Security Operations Report? SOC ReportsLearn why security operations reports are essential for safeguarding your organization and learn what they include. Stay ahead in the battle against cyber threats.
- Read more about Mean Time to Respond (MTTR): Cybersecurity GuideMean Time to Respond (MTTR): Cybersecurity GuideLearn what Mean Time to Respond (MTTR) means in cybersecurity, how to calculate it, and proven strategies to improve your incident response times.
- Read more about What are CRUD Operations? CRUD ExplainedWhat are CRUD Operations? CRUD ExplainedLearn what CRUD operations mean, see practical examples, and discover their impact on database performance and security.
- Read more about SOC Analyst Career Guide: Your Path to Cybersecurity SuccessSOC Analyst Career Guide: Your Path to Cybersecurity SuccessLearn the exciting role of SOC analysts in cybersecurity, their crucial responsibilities, and actionable tips to launch your career in threat hunting.
- Read more about Top Security Issues Threatening Organizations in 2026Top Security Issues Threatening Organizations in 2026From RMM abuse to AI-powered attacks, the top security threats of 2026 are more sophisticated than ever. See what's targeting organizations—and how Huntress stops it.


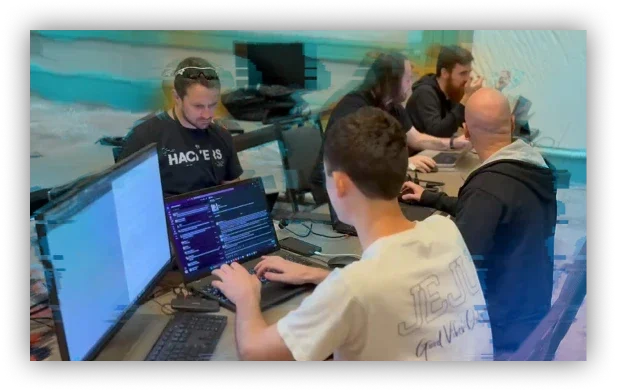
Meet the Huntress SOC
Whether an incident goes down at 3:00 p.m. or 3:00 a.m., the Huntress elite AI-assisted SOC team has your back with always-on SOC monitoring and rapid response.






