The Huntress 2026 Cyber Threat Report exposes how cybercriminals shifted their strategies, streamlined playbooks, and leveled up tradecraft to blend in better than ever.
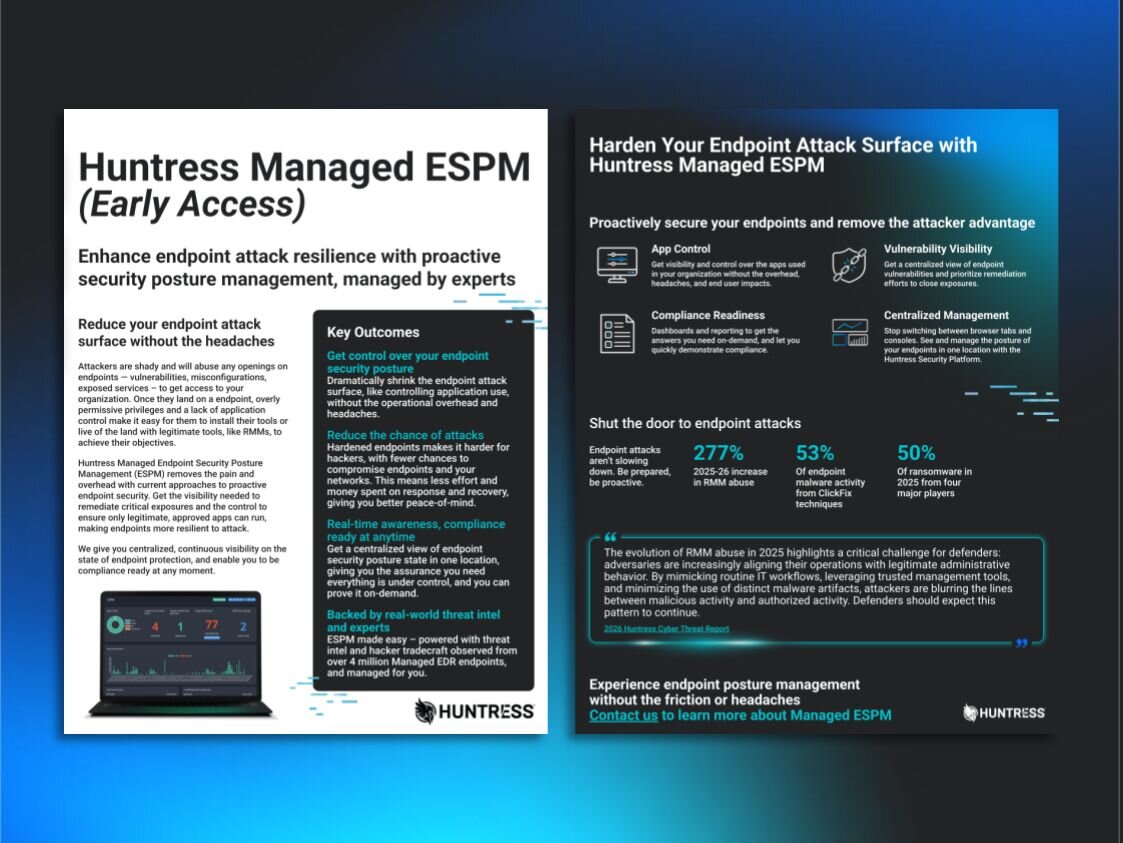
Stop Attacks Before They Start with Endpoint Security Posture Management (ESPM)
Huntress Managed ESPM is proactive endpoint protection made for all businesses, without the operational headaches. Nobody has time for unmanaged endpoint risk. Quickly take control with a single, streamlined security posture solution
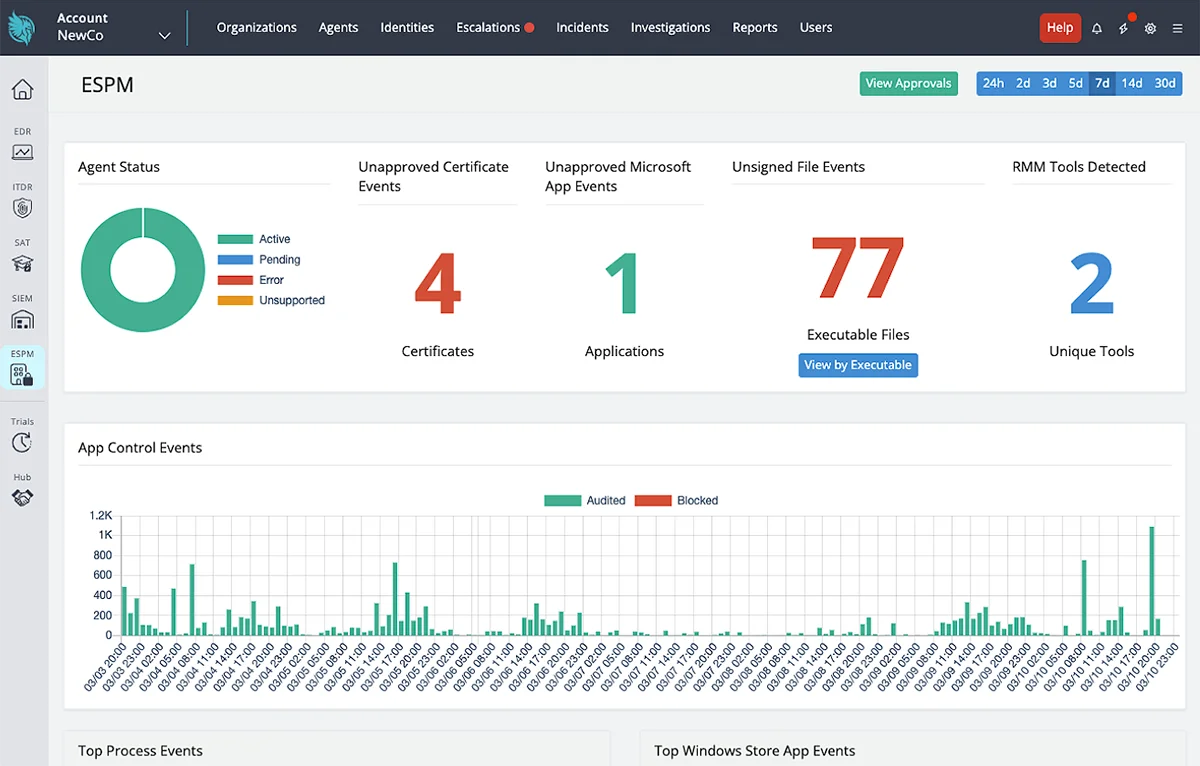
You don’t have to choose between overprotected endpoints and user productivity. Huntress Managed ESPM gives you both, making it faster and easier to reduce your endpoints’ attack surface while clearing the management overhead so you can focus on more critical priorities.
You don’t need a team of analysts to keep your endpoints secure. We’ve taken the friction out of application control, turning vulnerable endpoints into resilient assets that proactively defend against attacks.
Avoid days of manual reporting and get clarity in minutes. Managed ESPM gives you the oversight and source of truth you need to quickly prove compliance to clients, executives, auditors, boards, insurers, and regulators.

Explore how Huntress Managed ESPM makes it easy to proactively protect Windows endpoints and tougher for hackers to exploit them.

Use insights from Microsoft Defender for Endpoint to get a centralized view of endpoint vulnerabilities and help prioritize remediation efforts.
Stop hopping between browser tabs and screens. See and manage the posture of your endpoints in one location with the Huntress Security Platform.
Protecting your endpoints from shady cybercriminals isn’t a luxury anymore—it’s a necessity. That’s why Managed ESPM includes everything for one straightforward price—no add-ons, no service tiers, no BS. Wreck hackers without breaking your budget.
Managed ESPM removes application control pain points so attackers stop slipping through the cracks. It’s faster than traditional approaches that take weeks to roll out, and gives you time back to focus on what matters most for your business.
Stop scrambling to meet audit requests and manually gather data. Instead, show your security posture to clients, auditors, boards, insurers, and regulators in minutes with real-time dashboards and automated, verifiable reporting.
Managed ESPM and Huntress Managed EDR protect your endpoints across the entire attack lifecycle with threat insights from our team of experts. Your endpoints are backed by our 24/7 human-led AI-assisted SOC that has you covered from prevention to detection and response.

The Huntress 2026 Cyber Threat Report exposes how cybercriminals shifted their strategies, streamlined playbooks, and leveled up tradecraft to blend in better than ever.

At Huntress, we’ve made our name catching and wrecking the hackers who slip past defenses. Now, we’re making it hard for them to even get a foothold.
Learn how Managed ESPM gives you broad endpoint visibility and control over configurations, applications, vulnerabilities, and more in one location and a single solution.
ESPM is a proactive approach that continuously spots and helps close endpoint exposure gaps that attackers exploit to breach your network, systems, and applications. Unlike reactive tools, ESPM brings visibility and control over applications, and flags misconfigurations, missing patches, and security tool gaps (think broken antivirus agents) to shore up endpoint defenses and reduce the attack surface before a breach occurs.
ESPM transforms thousands of individual endpoint settings into a single, simple-to-manage view across a fleet of endpoints. It highlights vulnerabilities and exposures like:
ESPM focuses on prevention (security hygiene), while EDR focuses on detecting and responding to threats. The goal of ESPM is to close exposure gaps before they can be exploited versus EDR catching and stopping attacks where adversaries have slipped past proactive defenses.
Vulnerability management is only one part of endpoint security, focused on missing patches and misconfigurations. But ESPM goes beyond these controls by tracking the endpoint attack surface, like application usage.
We’re targeting the end of Q2 or early Q3 for availability to everyone.
The Huntress security platform is built, owned, and operated entirely by our team from first signal through remediation. Predictable pricing with no noise, just meaningful alerts.












Huntress Managed EDR doesn't just watch your endpoints—it’s a complete solution. From the second a threat appears until it’s eliminated, we handle everything. You get 24/7 continuous protection, detection, and response that disrupts and remediates threats.
Identity Threat Detection and Response (ITDR)
Finds and stops identity-based threats in Microsoft 365 and Google Workspace—because identity is the new endpoint, and attackers know it. Huntress Managed ITDR is designed to detect, respond to, and resolve critical identity-based threats like account takeovers, business email compromise, unauthorized logins, and more.
Huntress Managed SIEM takes away the complexity and overhead usually associated with traditional SIEMs, giving you everything you need and nothing you don’t. 24/7 threat response and strengthened compliance, fully managed by SOC experts, at a predictable price.
Engaging, expert-backed, personalized training content built on real-world threat intelligence and created by Emmy® Award-winning animators to reduce human risk and build a strong security culture.
Most hackers don’t "break in"—they just take advantage of messy settings, bad defaults, and accounts with too much access. Huntress Managed Identity Security Posture Management (ISPM) continuously audits and enforces configurations, policies, and permissions in Microsoft 365 so those easy attack paths are never open in the first place.
Huntress Endpoint Security Posture Management is proactive security that hardens endpoints to defend against attacks like ransomware and infostealers, and prevent breaches. Get broad endpoint visibility and control over configurations, applications, vulnerabilities, and more in one location and a single solution.


Let Huntress take away the overhead and headaches with Managed ESPM.

