The Huntress Cybersecurity Blog
Welcome to the Huntress Cybersecurity Blog, where we cut through the noise with real-world tradecraft to help you stay ahead of today’s threat actors. Our authors bring diverse backgrounds and hands-on experience to make cybersecurity education engaging, accessible, and grounded in the threats you actually face.
 Threat Analysis
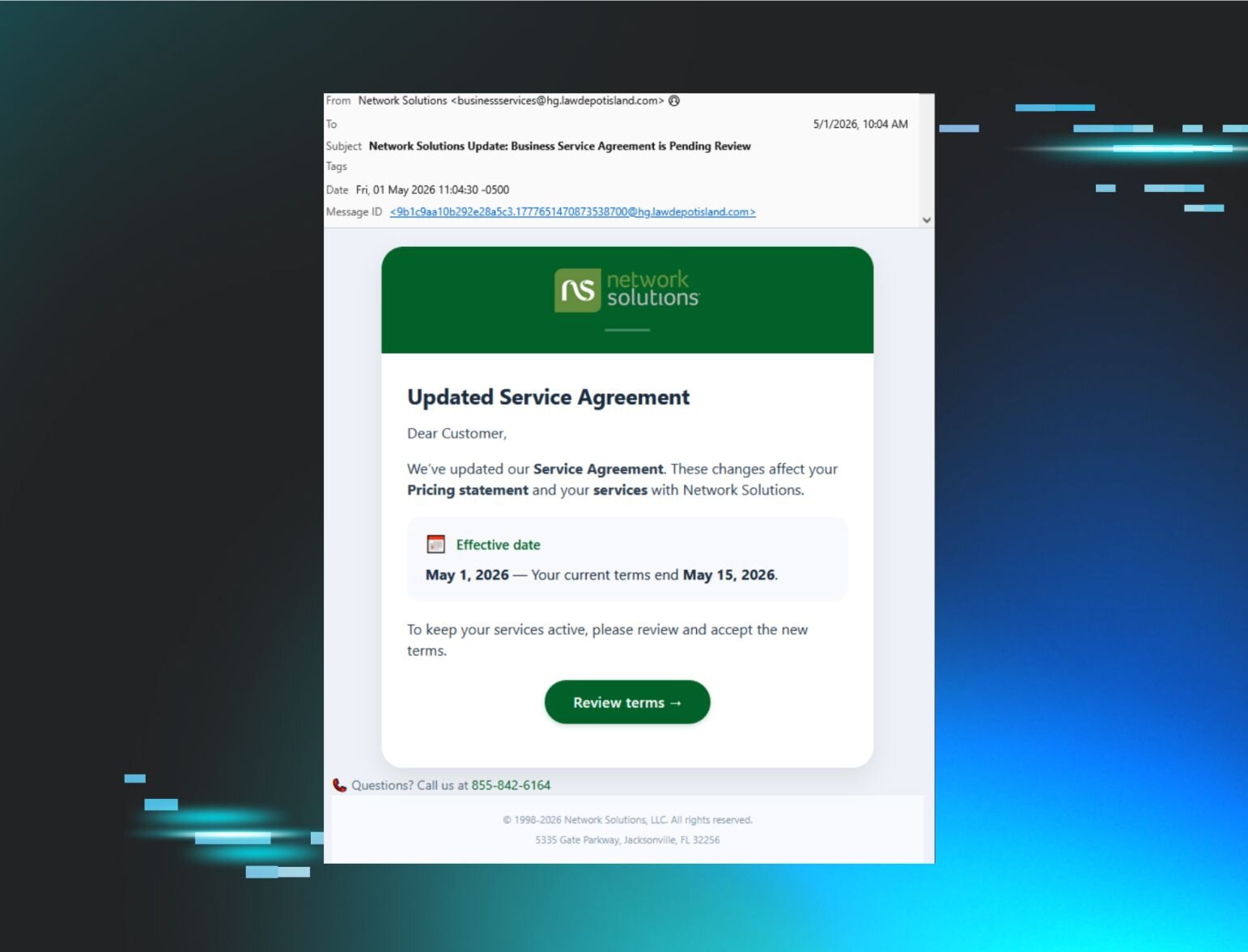
Threat Analysis“Service Agreement” Email Kickstarts Rogue RMM Tiflux Triple Threat
Featured Categories
Threat Analysis
Dive in and nerd out with us on current and emerging cybersecurity threats. We cover attack vectors, threat actors, and new vulnerabilities, providing insights to help you understand and counteract these risks.
No posts found.

Attacker Tradecraft
Understanding how attackers operate is the closest thing to a durable advantage. Attacker Tradecraft covers the techniques that don't make headlines but show up in nearly every investigation: TTPs, persistence mechanisms, defense evasion, living-off-the-land techniques, and offense-informed defense strategies. Not breaking news — evergreen knowledge that empowers your team.
No posts found.