The Huntress 2026 Cyber Threat Report exposes how cybercriminals shifted their strategies, streamlined playbooks, and leveled up tradecraft to blend in better than ever.
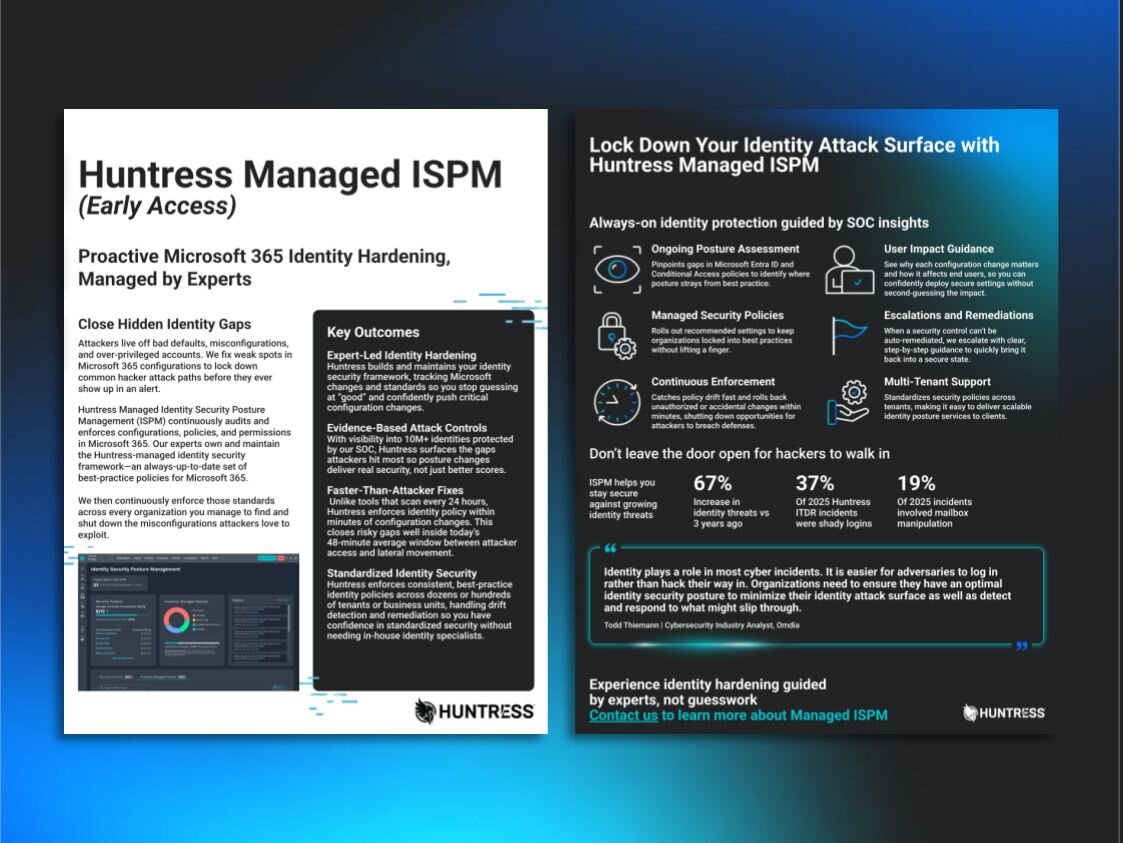
Attackers live off bad defaults, misconfigurations, and over‑privileged accounts. We find and fix those weak spots in Microsoft 365, locking down hacker attack paths before they ever show up in an alert.
Our security experts define the playbook, then continuously enforce a Huntress‑managed identity framework tuned to Microsoft guidance, industry standards, and real‑world attacker techniques.
You shouldn’t need an in‑house identity team to run Microsoft 365 securely. Managed ISPM spots risks and snaps misconfigurations back to safe defaults to give you identity resilience and compliance without extra overhead.

Our experts own and maintain the Huntress‑managed identity security framework—an always‑up‑to‑date set of best‑practice policies for Microsoft 365. Managed ISPM continuously enforces that framework across every organization you manage. We find and shut down the misconfigurations attackers love to exploit.

Keeps a close eye on Microsoft Entra ID and Conditional Access policies, pinpoints gaps, and highlights where your security posture strays from best-practice recommendations.
Rolls out Huntress-maintained policies and recommended settings to keep organizations locked into best practices. This helps you harden identities without lifting a finger.
Catches policy drift fast and rolls back unauthorized or accidental changes within minutes, shutting down opportunities for attackers to breach defenses or move laterally.
Standardizes Microsoft 365 security policies across tenants, making it easy to enforce best-practice configurations and deliver scalable identity posture services to clients.
Breaks down why each configuration change matters and how it affects end users, so you can confidently deploy secure settings without second-guessing the impact.
When a security control can’t be auto-remediated, we’ll escalate with clear, step-by-step guidance to quickly bring it back to a secure state.

ISPM and ITDR make the perfect pair. ISPM hardens your environment to stop attacks before they start. Used together with Huntress Managed ITDR, you get proactive hardening to reduce the attack surface, and a 24/7 SOC to quickly shut down anything that sneaks through.


The Huntress 2026 Cyber Threat Report exposes how cybercriminals shifted their strategies, streamlined playbooks, and leveled up tradecraft to blend in better than ever.

At Huntress, we’ve made our name catching and wrecking the hackers who slip past defenses. Now, we’re making it hard for them to even get a foothold.
This datasheet breaks down how our SOC-led experts standardize identity security across tenants, enforce best‑practice policies within minutes, and reduce risk from shady logins and mailbox manipulation.
Managed Identity Security Posture Management is a fully managed solution that maintains a secure Microsoft 365 framework for security hardening, surfaces misconfigurations, and streamlines remediation to build identity resilience.
Huntress Managed ISPM fixes misconfigurations, risky identity settings, and configuration drift in Microsoft 365, giving you consistent, expert-led hardening across every organization you manage.
Unlike standalone toolkits, Huntress provides a managed approach where our analysts manage the changes and policies, so you don't have to be a Microsoft security expert. The heavy lifting of defining policies, tracking drift, remediating unapproved configurations, and understanding the impact of changes before rollout is all handled for you.
No. ISPM is preventative hardening (proactive posture management), while ITDR is active detection and response. Together, they provide 24/7 identity protection.


Let our team stay on top of threats and changing identity standards so you don’t have to.

