One Bad Click Could Cost You Everything: Huntress Phishing Prevention Keeps You Secure
Over 90% of cyberattacks start with phishing. In seconds, one unsuspecting click can mean damage to your business. That’s why Huntress trains your users to prevent phishing attacks from the start and shuts down threats that sneak through.
Over 250k+ businesses protected by Huntress
Attackers see your people as an easy target. Here’s how you prove them wrong.
The best way to prevent phishing attacks is to start at the source: your employees.
A strong security awareness culture means fewer click-happy users and a lower risk of compromise. But people aren’t perfect, and some attacks will slip through the cracks. The Huntress Agentic Security Platform builds a security-minded culture among your employees while shutting down threats to your identities and endpoints.

Shut down phishing, even after a click
With the Huntress Agentic Security Platform, you get defense in depth to stop phishing attacks every step of the way.
From raising alarms to raising awareness
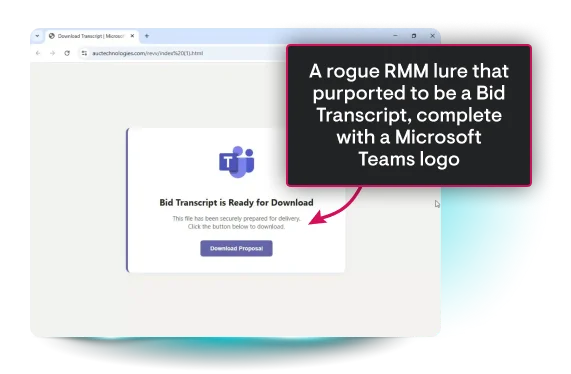
It’s late Friday, and you’re about to log off for the weekend when an employee downloads a malicious remote access installer disguised as a meeting invite for a pay increase. This attacker is using a legitimate tool for nefarious purposes to evade your security tools, but Huntress sees right through them.
With proper Security Awareness Training (SAT), this could’ve been avoided, but Huntress was there immediately, shutting down the threat by:
- Detecting malicious behavior
- Isolating the endpoint
- Kicking out the threat actor
- Recommending relevant SAT episodes to prevent this in the future

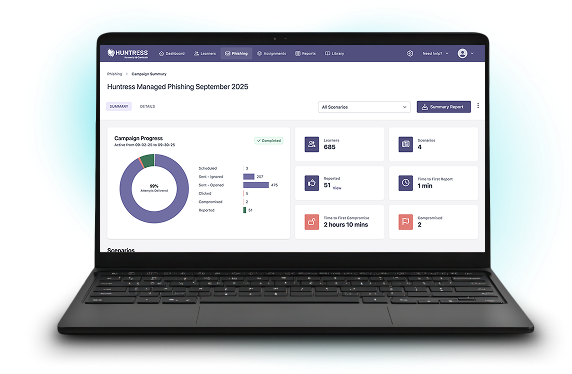
Better phishing detection starts with your people
Huntress turns your employees into your first line of defense against phishing. But it doesn’t stop there. Our SOC—a 24/7 team of elite threat analysts backed by AI—is with you around the clock, isolating hosts, cutting off access, and stopping ransomware before it spreads. You get a fast response that keeps your business running, your plans intact, and your mind at ease.

Better SAT, straight from the experts
Engaging employees in cybersecurity had been a challenge for Williams Technology, which is why they chose Huntress Managed Securtiy Awareness Tranining (SAT) for training. Because it’s built on real threat intelligence straight from the Huntress AI-Centric SOC, Managed SAT better prepares their users for real-world attacks.

Phishing defense you can count on

24/7
Global threat analyst coverage
Led by a team of elite, industry-recognized threat analysts who’ve seen it all, our AI-Centric SOC works around the clock to find and eliminate ransomware threats before they can damage your business.
<1%
False positive rate across 4M+ endpoints
Alert fatigue is brutal, and it’ll burn out your most skilled pros. That's why we cut through the noise and surface only the alerts that matter. Let us handle the distractions, so you and your team can focus on what matters most.
250k+
Organizations protected by Huntress
We see millions of attacks each year, and every one of them makes us smarter. These insights constantly evolve our tech and our approach to wrecking hackers. The result is greater efficiency for your team and herd immunity across our customers.
Huntress Agentic Security Platform
The Huntress security platform is built, owned, and operated entirely by our team from first signal through remediation. Predictable pricing with no noise, just meaningful alerts.












Engaging, expert-backed, personalized training content built on real-world threat intelligence and created by Emmy® Award-winning animators to reduce human risk and build a strong security culture.
- Training built on threat intel from 5M+ endpoints and 11M+ identities
- 98% completion rate for learners who start assignments
Huntress Managed EDR doesn't just watch your endpoints—it’s a complete solution. From the second a threat appears until it’s eliminated, we handle everything. You get 24/7 continuous protection, detection, and response that disrupts and remediates threats.
- Industry-leading MTTR
- 5M+ Endpoints protected
Identity Threat Detection and Response (ITDR)
Finds and stops identity-based threats in Microsoft 365 and Google Workspace—because identity is the new endpoint, and attackers know it. Huntress Managed ITDR is designed to detect, respond to, and resolve critical identity-based threats like account takeovers, business email compromise, unauthorized logins, and more.
- Industry-leading 3min MTTR
- 12M+ identities protected
Huntress Managed SIEM takes away the complexity and overhead usually associated with traditional SIEMs, giving you everything you need and nothing you don’t. 24/7 threat response and strengthened compliance, fully managed by SOC experts, at a predictable price.
- Smart Filtering to capture only security-relevant data
- Total Compliance with long-term retention, search, and reporting
Most hackers don’t "break in"—they just take advantage of messy settings, bad defaults, and accounts with too much access. Huntress Managed Identity Security Posture Management (ISPM) continuously audits and enforces configurations, policies, and permissions in Microsoft 365 so those easy attack paths are never open in the first place.
- Identity hardening guided by experts, not guesswork
- Configuration fixes that are faster than attackers move
Huntress Endpoint Security Posture Management is proactive security that hardens endpoints to defend against attacks like ransomware and infostealers, and prevent breaches. Get broad endpoint visibility and control over configurations, applications, vulnerabilities, and more in one location and a single solution.
- Reduce the attack surface to take away the hacker’s advantage
- A managed approach for less overhead and fewer headaches
2025 World’s 50 Most Innovative Companies
Top 25 CRN Technology Disrupters
2025 Best SIEM Solution SC Awards Europe






Frequently Asked Questions
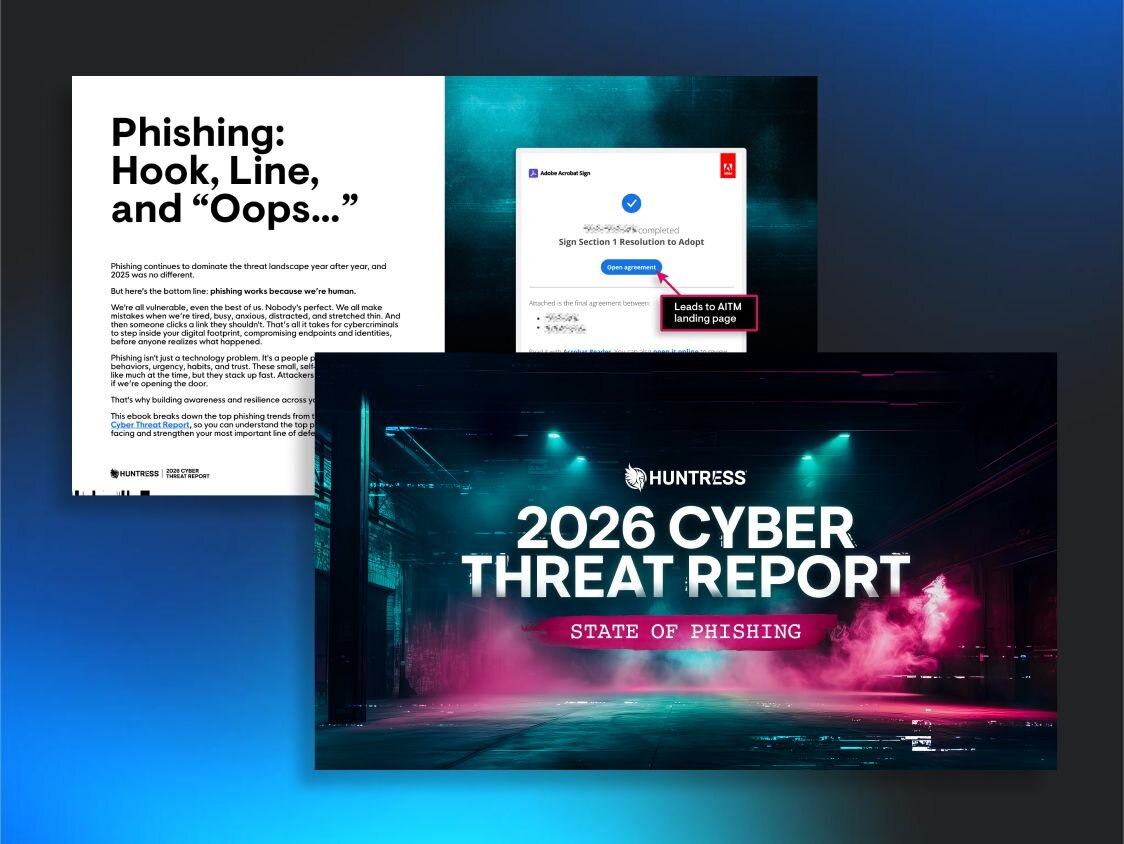
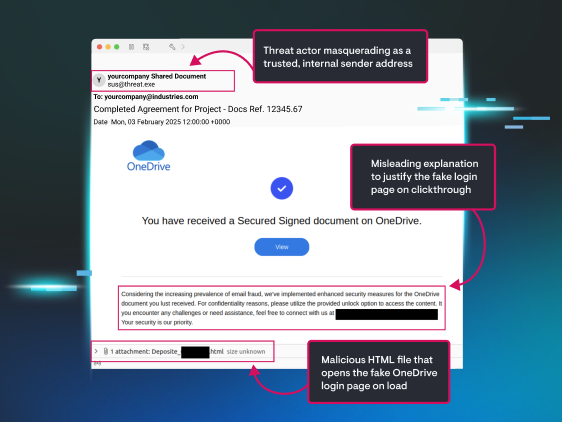
Phishing is an email-based social engineering tactic that aims to trick an unsuspecting user into taking an unwanted or compromising action or disclosing sensitive information. Hackers love using phishing because it's an efficient and highly effective way to achieve their goals. Through phishing, they can easily install malware like ransomware or infostealers, steal credentials, or gain access to your organization's data to use in a future attack or sell on the dark web.
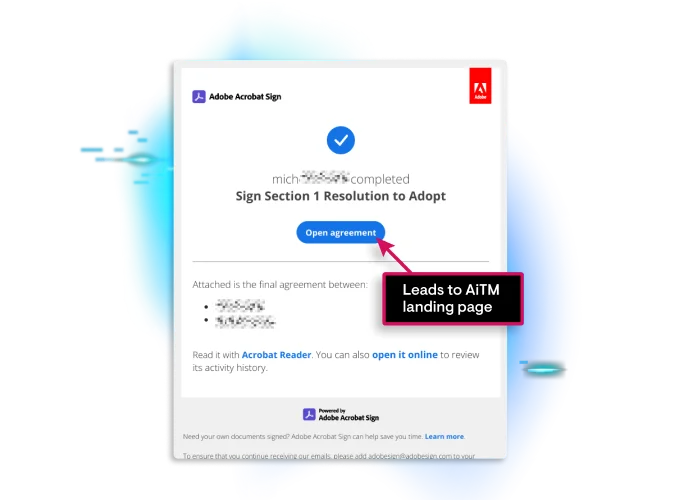
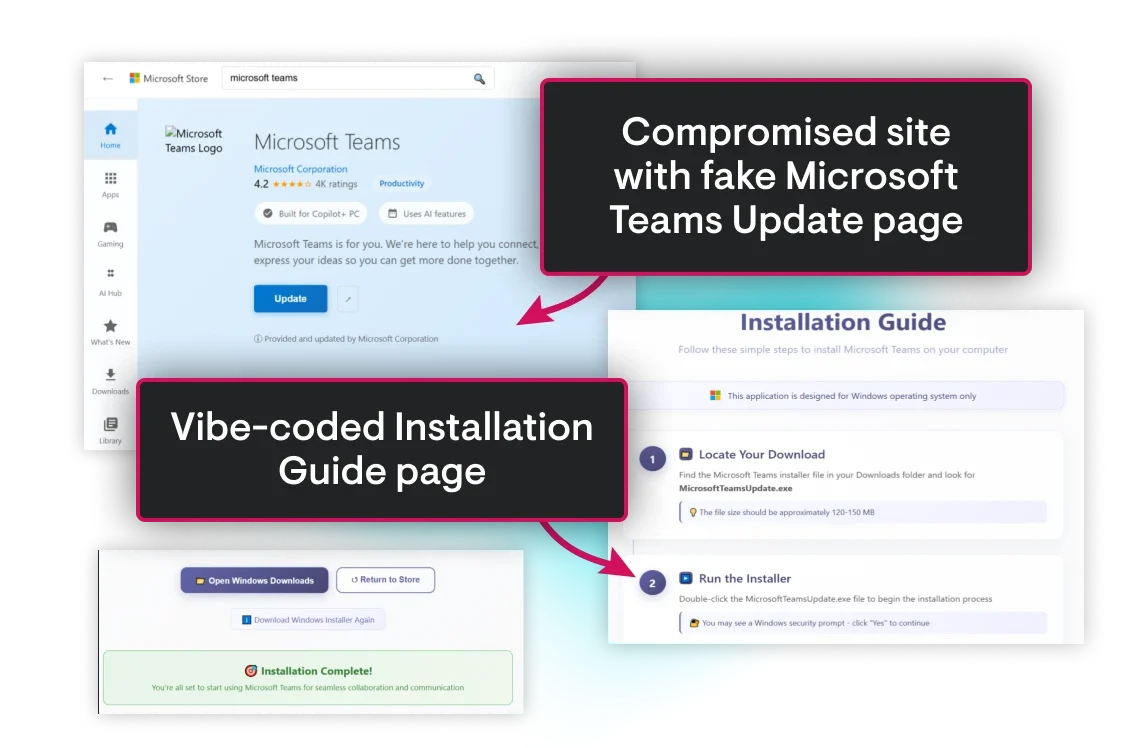
Phishing has been around for a long time and is always evolving. Old tactics like malicious links and classic social engineering are still used to trick people into revealing information. However, new methods are becoming more common and effective. These include tactics like ClickFix and FileFix attacks (which trick users into running malicious code), QR code phishing (Quishing), and call-back scams.
While phishing is mostly done through email, it also comes in other forms like SMS phishing (Smishing) and phone-based voice phishing (Vishing).
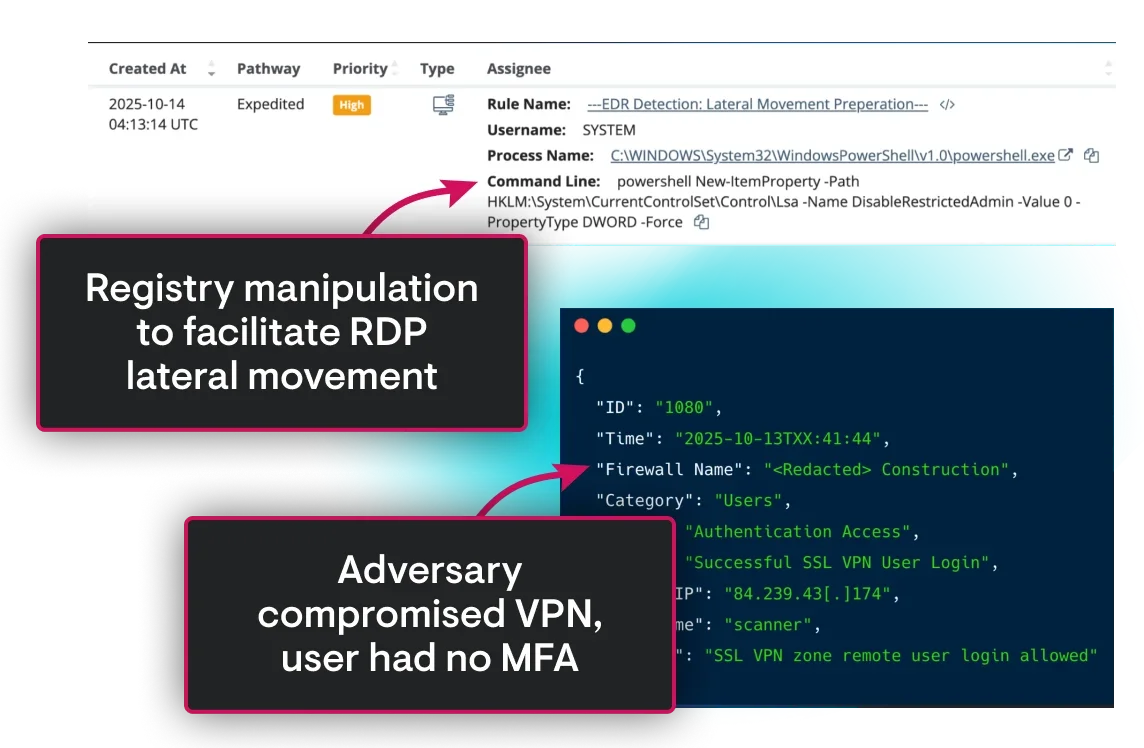
Protecting against phishing requires a defense-in-depth approach due to the increasing complexity of tactics threat actors are using against your users. Building awareness and educating employees to stop phishing is a great start, but it’s not the end-all-be-all. When all hackers need is one successful click to compromise your business, additional layers like Endpoint Detection and Response (EDR) and Identity Threat Detection and Response (ITDR) play a pivotal role in giving you the visibility to identify and shut down attacks that make it past your first line of defense:your employees.
Senior-level security experts are vital to providing the management and oversight necessary to action on the detections from EDR and ITDR, but these tools typically require specialized expertise.
Outsourcing to a SOC built specifically to manage these detections is a great way to gain security expertise without overextending your team.
Speed matters when it comes to stopping a phishing attack. The ideal state for your users to stop them in their inbox, before the attack even starts. But for successful phishing attacks, the faster an attack is detected, and the threat is contained—whether that’s shutting down VPN access, isolating a host or identity, or kicking threat actors out of your environment—the greater likelihood your business will minimize the impact of a phishing attack.
To protect against ransomware, you need a defense that covers all the tricks attackers use. This means stopping them from phishing users, exploiting system vulnerabilities to get into your network, accessing endpoints, and moving around once they're inside. It also means being ready to bounce back quickly if an attack does happen. This requires a well-documented,tested incident response plan and a solid, secure data backup strategy.
Attackers are using AI to build more effective phishing attacks at scale. IT and security teams can keep up with hackers and defend against phishing attacks by using AI to identify phishing emails faster, triage and prioritize alerts more quickly, and move at the speed phishing attacks are evolving.
Having a solid phishing incident response process is key—it needs to be tested, validated, and fine-tuned. A good security awareness training program is also a must, teaching users to spot and report suspicious emails quickly to help stop a breach as soon as possible.
Huntress stands out in preventing phishing attacks by giving you multiple layers of protection that work together to strengthen your security over time. Every new detection feeds into a feedback loop of information and intelligence, improving all layers of defense. Plus, you get the convenience of working with one trusted vendor who treats you like a security partner, not just another customer.
It all starts with preventive tools like Managed SATas well as Identity and Endpoint Security Posture Management to block phishing attempts before they even begin. If something does slip through, layers like Managed EDR, Managed ITDR, and Managed SIEM step in to detect and stop malicious activity.
Every incident our SOC handles becomes another piece of data that makes our training smarter and our detections sharper, creating a kind of "herd immunity" that benefits all Huntress customers.
We’re all about speed and quality. Huntress Managed SIEM gives you broad visibility across your security tools and IT environment, helping you spot threats before they can break into your network. With our human-led, AI-Centric SOC, you’ll get verified, actionable alerts in minutes, complete with context and steps to take action. Instead of overwhelming you with endless alerts, we give you a clear plan to quickly remove threats and keep attackers out.


See Huntress in action.
Our platform combines a suite of powerful managed detection and response tools for endpoints and Microsoft 365 identities, science-backed security awareness training, Managed SIEM, and the expertise of our 24/7 Security Operations Center (SOC).