In 2025 and beyond, major employers have plans to implement a return-to-office policy, leading to many employees looking for new roles. But why are some employers reneging on promises of fully remote work? What factors led to their decision to force employees to return to the office?
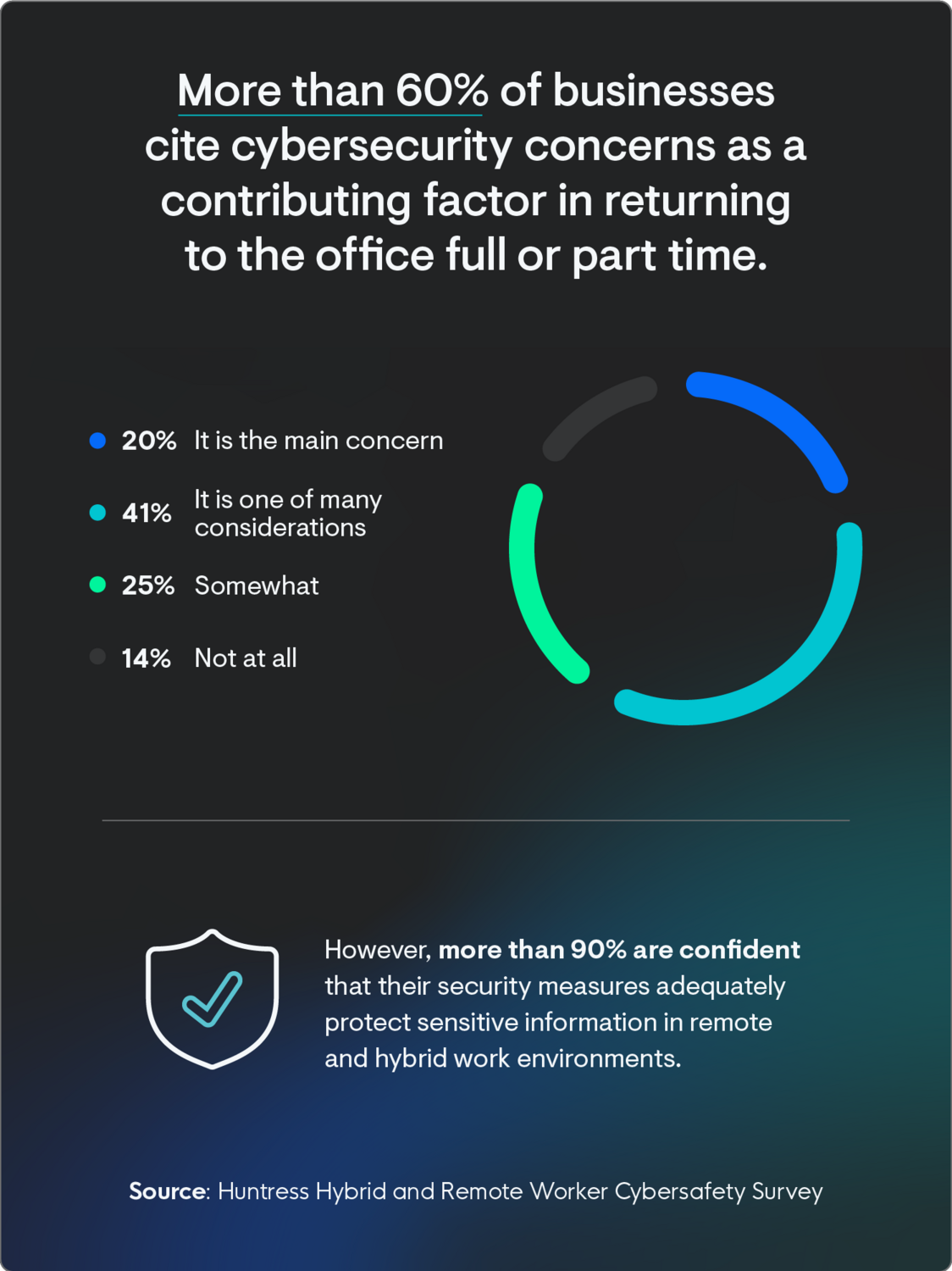
According to new data from a December 2024 survey of more than 200 IT professionals conducted by Huntress, 61% of businesses' cyber safety concerns over remote and hybrid workers played a role in their decision to return to the office to some extent. But this doesn’t have to—and shouldn’t—be the case.
“The concern is understandable. Traditional security programs were designed by building the biggest walls. Remote workers exist outside of that — which can bring challenges,” says Chris Henderson, Senior Director of Threat Operations at Huntress. “Here at Huntress, we protect ourselves with the same technology we utilize to protect our clients. We monitor our identities for anomalous behaviors and have a robust EDR — all patrolled by our team of expert analysts.”
In fact, the same survey showed that 90% of cybersecurity professionals are confident about their organization’s ability to protect sensitive information in remote and hybrid work scenarios.
With high rates of formal security awareness training happening, as well as other measures like multifactor authentication and encrypted password managers, IT professionals agree there’s little cause for concern or business interruption when working remotely.
Let’s take a deeper look into remote work and its impact on cybersecurity—both real and perceived—so you have best practices for your employees to stay cyber-secure, no matter where they’re signing in from.
Key Takeaways
- 61% of workplaces cite “cybersecurity concerns” as a contributing factor to returning to the office full- or part-time.
- More than 90% of cybersecurity professionals are confident in their organization's ability to protect sensitive data in remote and hybrid environments.
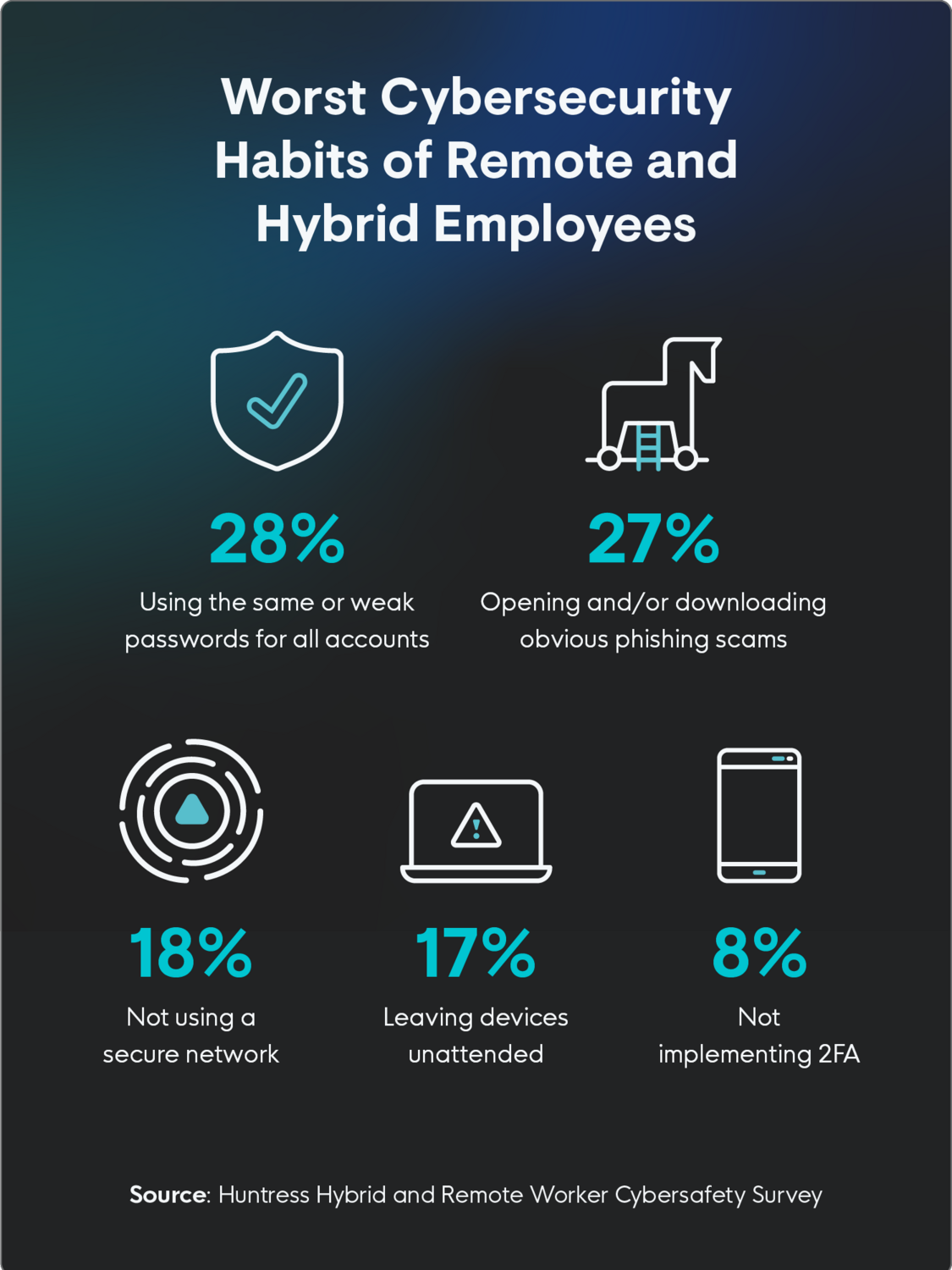
- 28% of cybersecurity professionals say password usage is the biggest weakness of remote or hybrid employees.
Cybersecurity Is a Consideration in Enforcing Return-to-Office Policies
More than 3 out of 5 cybersecurity professionals (61%) noted that concerns around cybersecurity and employees following remote work security best practices were, to some extent, part of their organizations’ decision to return to the office either full- or part-time. Of those, only 20% said it was a deciding factor, while 41% said it was one of many considerations.
Here’s a breakdown of survey respondents' current work arrangements:
- 43% of organizations are hybrid, working both in-office and from home
- 29% are completely in-person/in-office full-time
- 21% have plans to or are considering enforcing a return-to-office policy
- 7% are completely remote
Most Cybersecurity Professionals Are Confident in Their Security Measures
While most noted that cybersecurity is a concern, the majority (51%) are “confident” that their organization's data security measures are adequate to protect sensitive information in remote and hybrid work scenarios. In comparison, 42% are at least “somewhat confident” in their company’s data security measures.
While cybersecurity concerns influenced the return-to-office (RTO) decisions of many organizations, more than 90% of cybersecurity professionals are confident in their organization's ability to protect sensitive data from loss in remote and hybrid environments.
This discrepancy suggests a possible gap in understanding or communication regarding the actual strength of cybersecurity within these organizations versus the perceived threat remote and hybrid employees pose.
“While cybersecurity is one of many possible contributing factors leading to RTO decisions, it’s also possible that it’s one of the factors that is being used simply to justify a return to office when in reality there is no true threat perceived,” Henderson says.
Despite Concerns, IT Professionals Report That the Shift to WFH Positively Impacted Overall Cybersecurity Posture
Despite some organizational concerns around remote work, cybersecurity professionals are optimistic about its impact on their cybersecurity health.
More than 3 out of 5 (64%) respondents felt that the shift to remote and hybrid work had a positive impact on their ability to predict and prevent cybersecurity incidents, while 30% were neutral, and only 6% reported a negative impact.
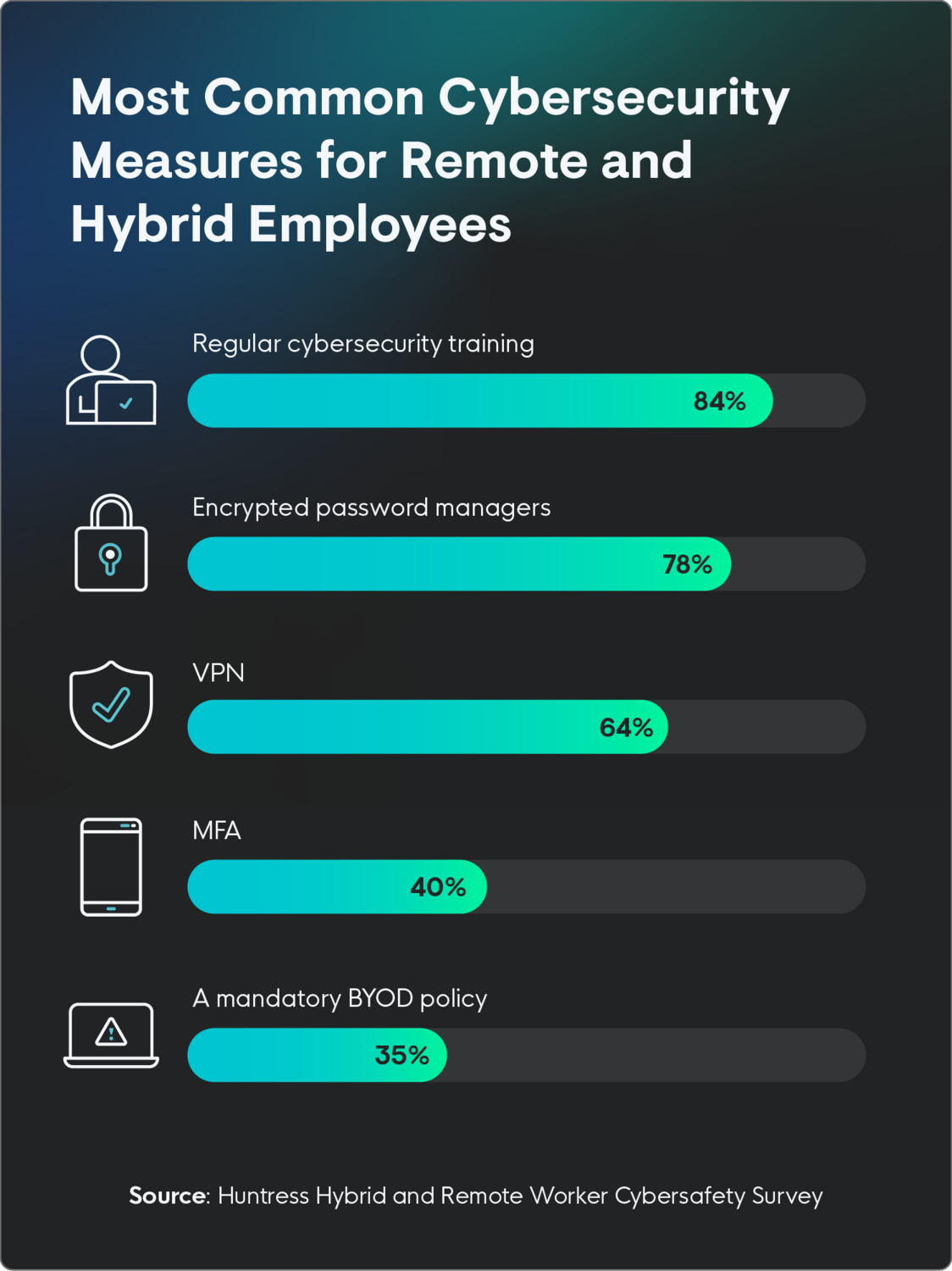
The most commonly implemented cybersecurity policies for remote and hybrid employees are regular cybersecurity training (84%), encrypted password managers (78%), and virtual private networks, or VPNs (64%)
But here’s where things get interesting: less than half of respondents (39%) utilized multifactor authentication (MFA)—leaving the door wide open for threat actors.
Multifactor authentication is key to thwarting attackers, but like any security tool, it has inherent weaknesses. SIM Jacking will circumvent any SMS based MFA, One Time Passwords can be intercepted. Once strong MFA methods are deployed, “The next most important thing to consider is how long an authenticated identity is allowed to stay authorized to use a system before having to re-assert their authentication,” Henderson says. “Authentication sessions should be short enough to thwart a potential session theft but not so short to hamper productivity.”
The Majority of Workplaces Conduct Cybersecurity Training Quarterly, at Minimum
Nearly 2 in 5 (39%) organizations conduct cybersecurity training every quarter. This cadence aligns with remote work best practices, which suggest completing cybersecurity training at least every six months.
As for the rest of the respondents, 23% complete training every six months, while 23% do it monthly. But it’s not all good news… 10% have training once a year or less, and 5% do not have a formal cybersecurity training schedule in place at all.
Because today’s threats are so advanced and evolve quickly, your organization must take a proactive approach to cybersecurity to stay safe.
Weak Passwords Are the Biggest Internal Threat to Cybersecurity
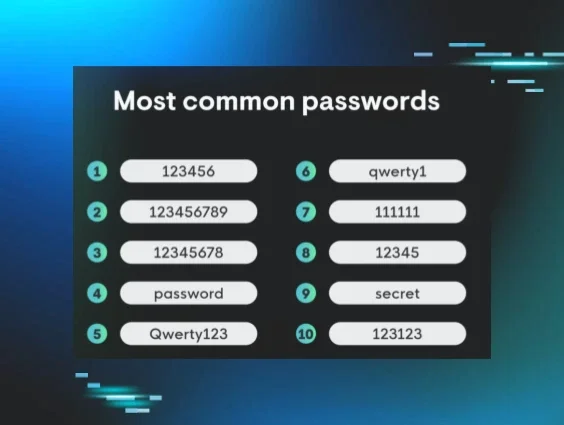
When asked about their employees' worst habits, the most commonly selected answer was exposed passwords, specifically using the same or weak passwords for everything. This answer was followed closely by opening and/or downloading obvious phishing scams and not using a secure network.
Respondents rated the top outside threats to cybersecurity in remote work environments as:
- Phishing attacks and social engineering
- Data loss or breaches
- Unauthorized access to sensitive data
It’s worth noting that these findings represent common threats in both remote and in-person work environments for many workplaces, not just remote and/or hybrid environments. The results underscore the importance of ongoing cybersecurity training and education for all employees, regardless of their work location.
By making all employees aware of common threats and security best practices, organizations can empower their workforce to act as the first line of defense against cyberattacks and minimize the risk of data breaches in remote work environments.
Nearly One-Third of Cybersecurity Professionals Believe Employees’ Security Awareness Needs Improvement
Nearly a third of respondents (32%) believe overall cybersecurity awareness among employees needs improvement, while 46% rate them as “meeting expectations”. Conversely, 22% said that employees exceeded expectations.
Organizations must encourage employees to follow remote work security best practices, participate in regular training, use secure networks, and practice good password hygiene.
Doing this not only limits cybersecurity threats to the organization, but also empowers employees to take responsibility for their own cybersecurity, at work and at home.
Learn more about Huntress’s Managed Security Awareness Training.

5 Remote Work Cybersecurity Best Practices
Building a successful remote or hybrid work strategy requires focusing on best practices from industry expert reports. By incorporating some or all of these guidelines into daily operations, organizations can become more productive, improve employee well-being, and strengthen their overall security—win/win!
1. Implement Regular Cybersecurity Training
Cybersecurity training is an essential investment for any organization, regardless of size. Educating employees on security best practices gives them the power to become the first line of defense against cyber threats. Regular training makes security consciousness a part of your culture, where employees are actively involved in protecting sensitive data and minimizing the risk of cyberattacks.
Effective cybersecurity training covers a range of topics tailored to the organization's specific needs, but key areas should always include:
- Password best practices: Encourage employees to use strong, unique passwords for each account and avoid password reuse.
- Phishing and social engineering: Employees should know how to identify and report suspicious emails and recognize common phishing tactics like urgent requests, unexpected attachments, and requests for sensitive information.
- Safe browsing and downloading: Everyone in your organization should know to avoid suspicious websites, download only from trusted sources, and be leery of unsolicited downloads.
- Data handling and privacy: Employees should understand data classification, handle sensitive information responsibly, and adhere to data privacy regulations.
- Mobile device security: All employees should secure their mobile devices with passcodes or biometrics, avoid public Wi-Fi for sensitive tasks, and regularly update their device software.
2. Limit Attack Surface With VPNs
By using a VPN, businesses can significantly reduce the risk of data breaches, protect sensitive information from unauthorized access, and comply with data privacy regulations. VPNs are great for remote workers who connect to the company network from various locations, often using unsecured public Wi-Fi networks.
VPNs can also help prevent malware infections and protect against phishing attacks. By filtering traffic and blocking access to malicious websites, VPNs create a safer browsing environment for employees. Additionally, when applying IP allow and block lists to restrict access to internal resources, a VPN allows a very narrow list to be implemented, keeping your attack surface smaller.
3. Require Multifactor Authentication
One of the key ways to improve security is with MFA. Even though less than half (40%) of respondents currently use multifactor authentication at their organization, it’s a simple and effective way to slow and prevent cyberattacks.
Multifactor authentication is particularly effective at deterring brute force attacks, where hackers gain access to a system by guessing credentials.Or a Credential Stuffing attack where hackers gain access by utilizing previously compromised credentials. With MFA enabled, even if the password is guessed correctly, hackers won't be able to enter the system without the second point of authorization, which will ping the user that someone has tried to access their system.
It’s important to note that not all MFA is created equally. SMS MFA is less effective and secure than a time-based one-time password (TOTP) or hardware tokens.
4. Use Encrypted Password Managers
Encrypted password managers generate and securely store strong, unique passwords for each account, removing the need to remember complex combinations or resort to weak, easily guessable passwords.
Password managers provide unique credentials for every site, limiting the impact a breach will make if one of your services has an incident. Considering poor passwords are one of the main concerns of cyber professionals, organizations should enforce the use of strong passwords across all accounts. Doing this can reduce the risk of unauthorized access and data breaches resulting from compromised credentials.
5. Create a Cybersecurity Policy Tailored to Remote Work
Every organization should have a cybersecurity policy. This is particularly important for workplaces with remote or hybrid employees, where endpoint security is ultimately both the IT and security team and the employees’ responsibility.
Your cybersecurity policy should include regular cybersecurity training, MFA, VPNs, and encrypted password managers, as well as guidance for incident reporting, data handling, and Wi-Fi security, among many additional considerations.
In the end, cybersecurity is equal parts the employer's and the employee's responsibility. Employers should give guidance and clear regulations to ensure cybersecurity, and employees should always follow those policies.
Support Cybersecurity No Matter Where Your Employees Work
“The security of remote teams is contingent upon the strength of the organization's security program and its adaptability to their specific environment,” Henderson says. “Equitable security is absolutely achievable by designing a program that acknowledges and addresses the realities of your workforce.”
By implementing reliable security measures, investing in employee training, and creating a strong security culture, all organizations can be cyber-secure, regardless of working location. Adhering to remote work security best practices is a must for protecting sensitive data, mitigating risks, and ensuring business continuity in today's dynamic work environment.
If you’re looking for a stress-free way to manage your remote employees' endpoints, read more about Huntress’ managed endpoint detection and response (EDR), featuring 24/7 support from our expert security team.
Methodology
The survey of 227 US IT professionals ages 18+ was conducted via Centiment Audience for Huntress between December 4 and 6, 2024. Participants were excluded if they had never worked at an organization that offers fully remote or hybrid work options to employees. Data is unweighted, and the margin of error is approximately +/-3% for the overall sample, which has a 95% confidence level.