More tools. Healthy budgets. Hard-working teams. And yet, security is still falling behind. The problem isn’t a lack of effort. It’s that many security programs were designed for a threat landscape that doesn’t exist anymore. The defender’s playbook hasn't kept up, and the gap is showing.
To put hard numbers behind it, Huntress surveyed 1,050 internal IT and security professionals across North America and the UK. The findings shaped our latest report, How to Build a Resilient Security Team for 2030.
We wanted the unfiltered truth about modern cybersecurity. We asked where teams feel prepared, where they don't, and what's getting in the way.
What we found should change the way you think about building a resilient security team for the future.
Key takeaways
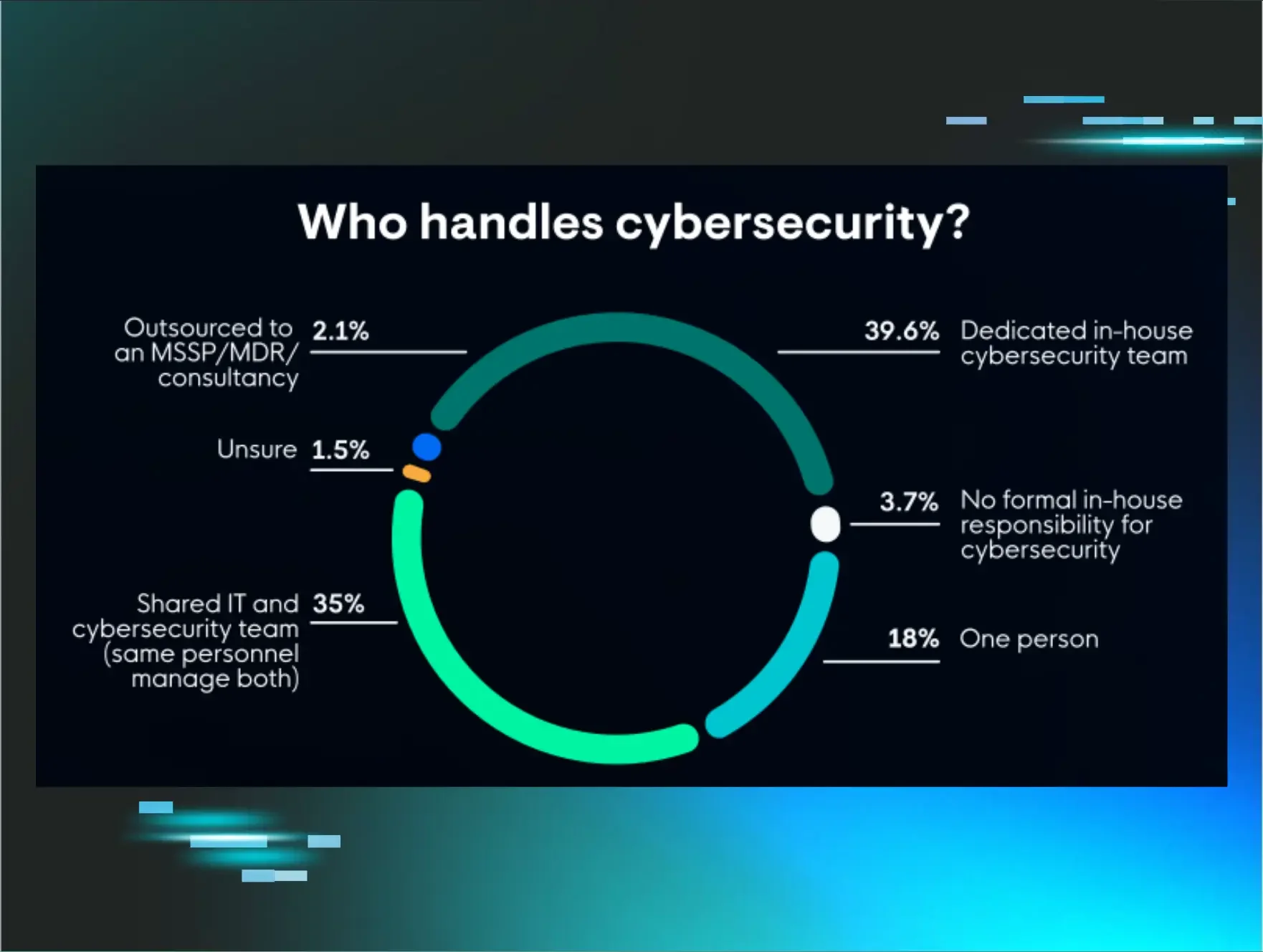
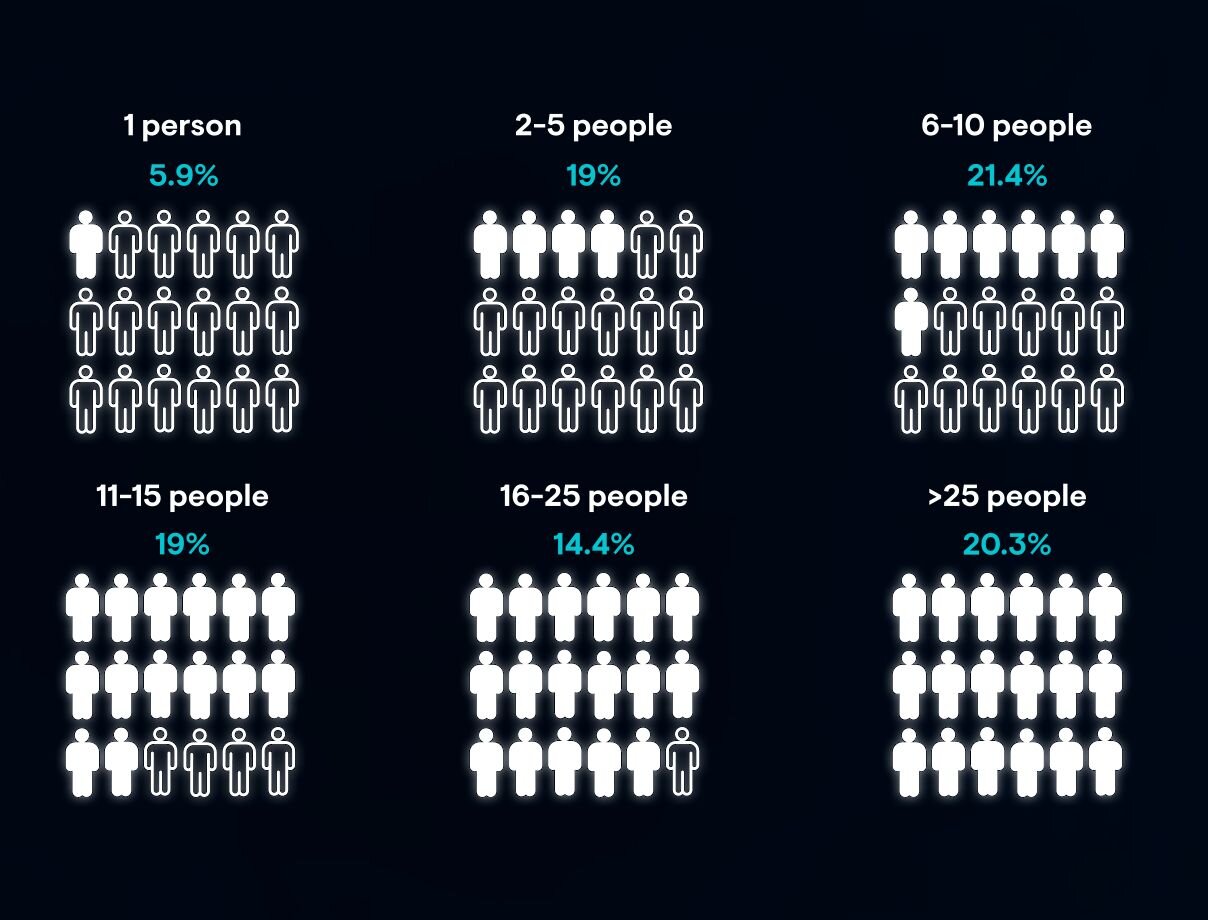
Most security teams are small. The majority of surveyed teams surveyed are between six and 15 people, with nearly one in five organizations relying on a single person to handle all cybersecurity responsibilities. These teams aren't failing because of a lack of effort. They're operating with programs designed for a different era against threats that have fundamentally changed.
Budget isn't always the core problem. Nearly three-quarters of respondents rate their IT budget as at least adequate, and more than a quarter allocate 16–20% of that budget to security. The financial resources exist. What's missing is clarity around what matters most and who owns the next decision.
Alert noise steals the time your team needs most. Speed of detection and response is the top measure of success, but nearly two-thirds of teams report that at least 25% of their alerts are just noise. Every false positive is time an attacker spends moving deeper into your environment. Auditing your alert quality is key to better security.
Resilience is about decisions under pressure, not just tools on a shelf. The teams that come out ahead aren't necessarily the ones with the biggest budgets or the most headcount. They’ve clarified ownership before an incident, designed systems that catch human error, rather than assume it won't happen, and made the deliberate shift from "prevention only" to resilient operations.
The teams behind the data
Before we get into the findings, it helps to understand who we're talking about.
Most of the teams in this survey are small. The most common team sizes fall between six and 10 people (21.4%) and 11–15 people (19%). Only 39.6% of respondents have a dedicated in-house cybersecurity team. Another 35% say IT and security responsibilities are shared among the same people, and 18% say cybersecurity is handled by a single person.
These aren't teams with unlimited resources and a 24/7 Security Operations Center (SOC). These are people doing the best they can with what they have. And they’re doing it well, in many cases.
Budget isn't the core issue, either. Nearly three-quarters of respondents (72.3%) rate their IT budget as at least adequate, and more than a quarter allocate 16–20% of their IT budget to cybersecurity. The resources exist, so why do outcomes still lag?
The real problem is that security programs are built for yesterday's threats
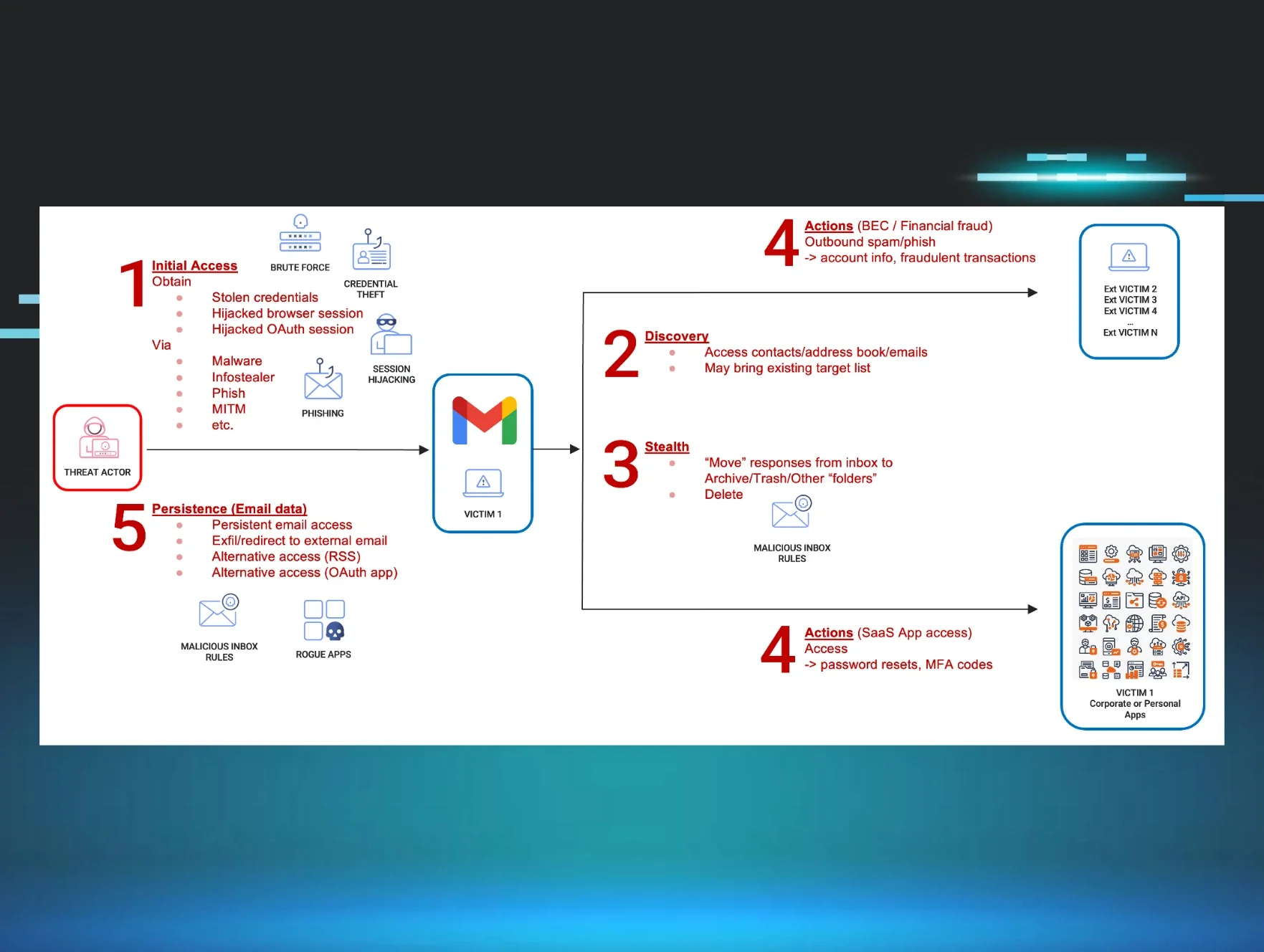
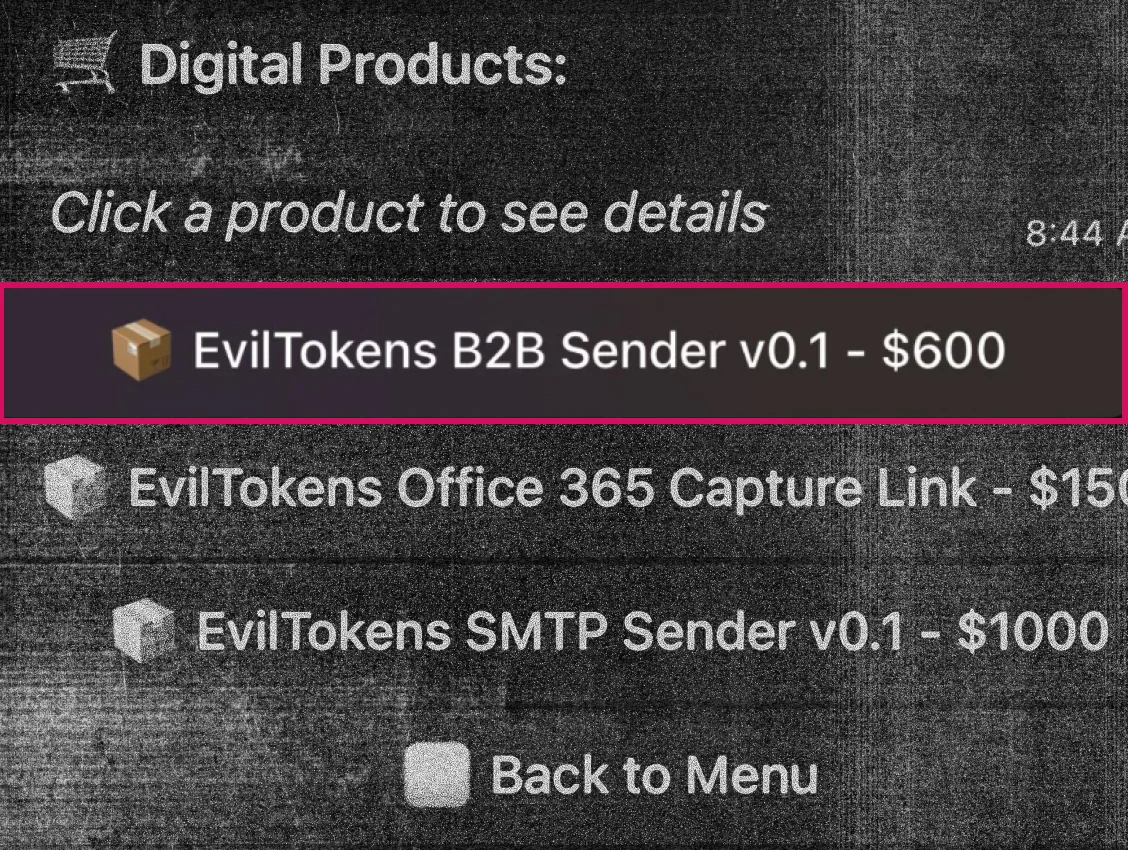
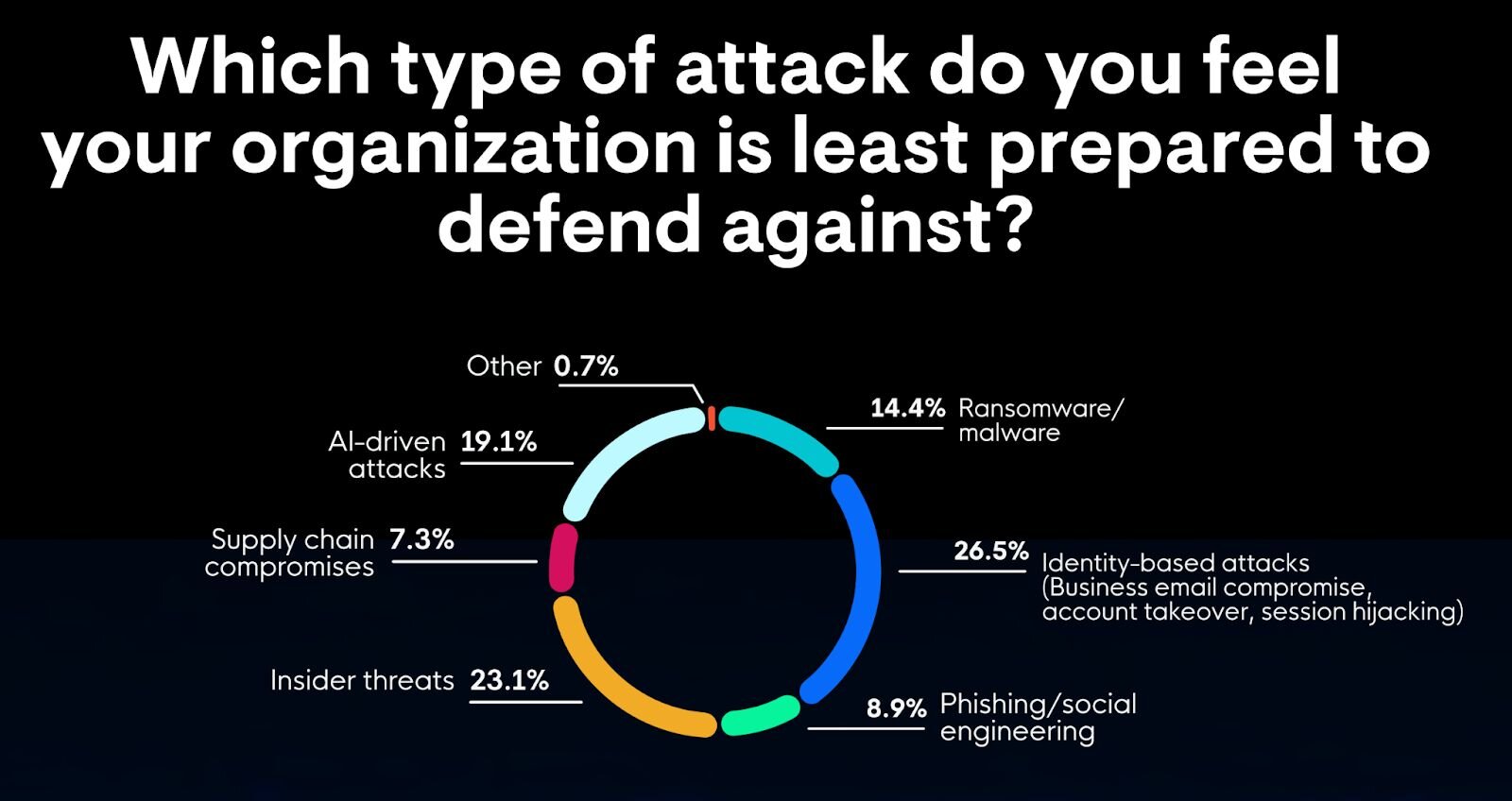
As the business world becomes increasingly digital, IT and security teams face a rapidly shifting threat landscape. To manage this, many organizations have invested in solutions that rely on tools layered over time. What’s troubling, though, is that many of these security programs were designed with yesterday's threats in mind. They were built to detect malware and other traditional endpoint attacks, rather than spot access abuse or unauthorized use of identities.
Identity-based attacks, like business email compromise (BEC), account takeover, and session hijacking, are what teams feel least prepared to defend against (26.5%), according to the survey data.
Jenko Hwong, Principal Product Researcher of Identity Threat Detection and Response (ITDR) at Huntress says:
“Identity used to be about passwords and MFA. In the cloud, it’s sessions, tokens, and apps—and that’s where most teams are behind.”
What makes this more alarming is that while speed of detection and response is the top measure of security program success, nearly two-thirds of teams (64.1%) report that at least 25% of their alerts are just noise, leaving businesses vulnerable to emerging identity threats. While security teams are buried in false positives and low-priority signals, attackers get the one thing they need most: time.
Real-world incident: Identity threats in action
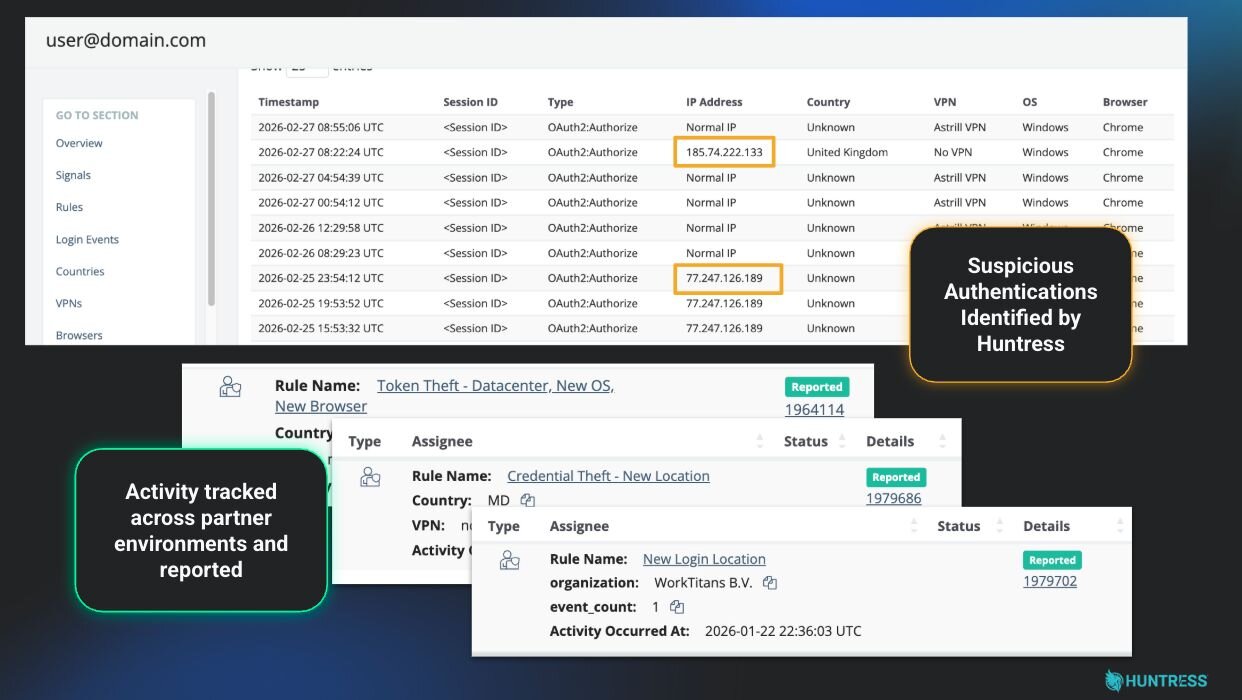
Here's what this looks like in practice. We recently detected an identity compromise coming from a suspicious, newly seen data center location. Our SOC jumped on this threat right away and disabled the compromised account before any damage could spread. But here's where human judgment made all the difference: the team didn't stop there.
Analysts used the suspicious hosting provider associated with the initial compromise to pivot across Huntress' ITDR telemetry, searching for other accounts that had authenticated from the same location. They found multiple additional compromised accounts, which were all identified, reported, and secured.
No malware. No exploit. Just a valid login from the wrong place, and a human-led, AI-centric SOC team that knew how to follow the thread. That's what identity threat detection and response looks like when it works.
Figure 3: An example of the Huntress SOC shutting down an identity threat
AI amplifies what lean teams can do
Intentionally deployed AI can change the equation for lean teams. Rather than a luxury reserved for enterprise organizations with massive headcounts, AI levels the playing field for smaller ones.
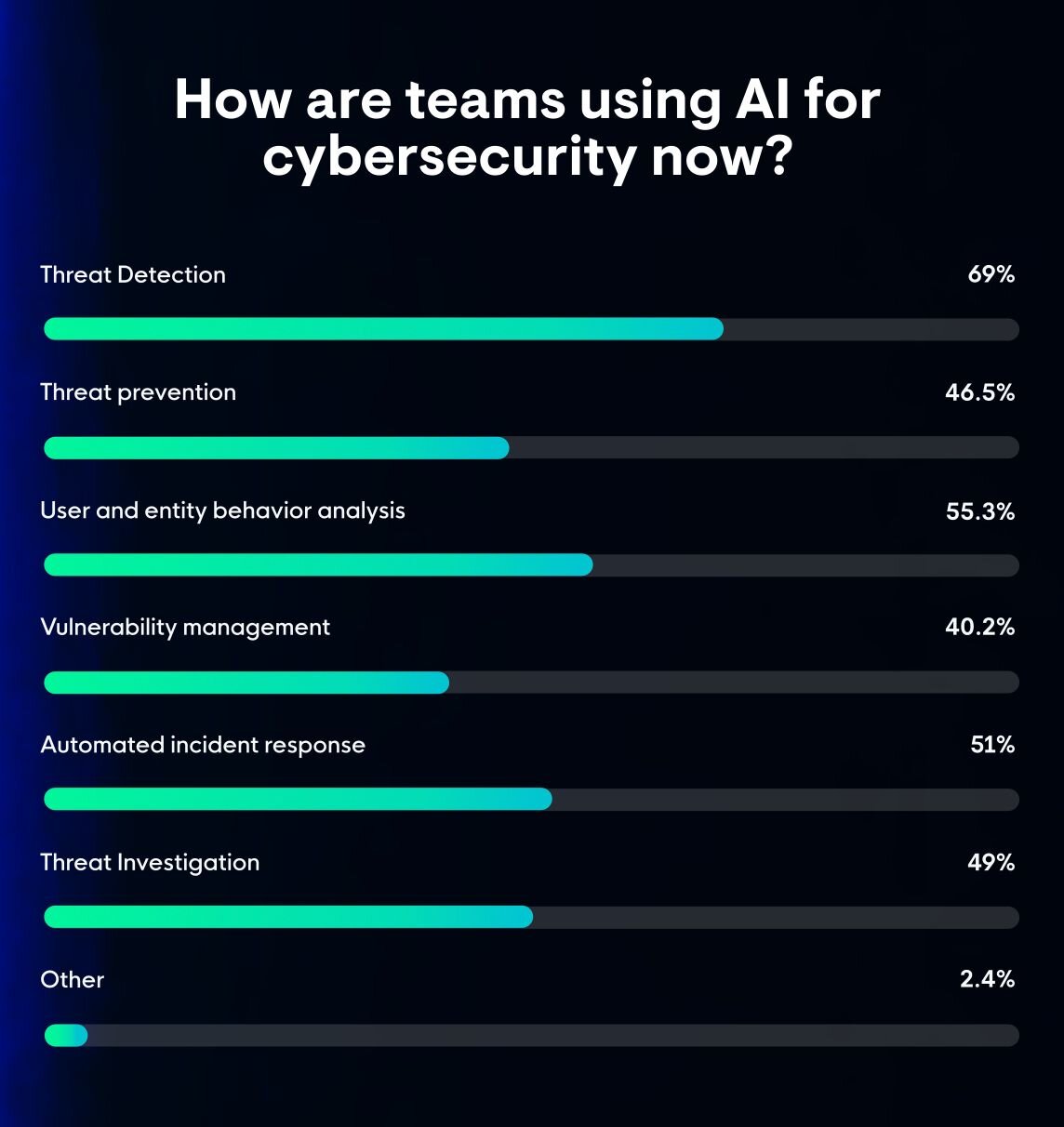
Nearly half of the professionals we surveyed (46.9%) rate AI as a critical part of their security strategy. And the way most teams use it says a lot. The top use cases are:
Threat detection (69%)
Analyzing user and entity behavior (55.3%)
Automated incident response (51%)
Threat investigation (49%)
In other words, teams are using AI to accelerate analysis, reduce noise, and shorten response time. For a six-person team carrying the security weight of a 500-person organization, AI can handle high-volume, repetitive work so that your analysts aren't burned out before the real threats show up.
Anna Pham, Senior Tactical Response Analyst at Huntress, states:
“AI saves people from burnout—but humans still have to verify what matters.”
Resilient teams purposefully design systems that bring AI and people together to reduce cognitive load, protect human judgment, and speed up the decisions that matter most. People are supported, not replaced, with the goal of making fewer decisions and better ones when it counts.
What can you do right now to build a resilient team?
The data points to a clear path forward, and it doesn't start with buying more technology. It starts with asking better questions.
Audit your alert quality. What percentage of your alerts actually lead to meaningful action? If more than a quarter of your time is spent on noise, your team is burning time and energy on signals that don't matter. That's time stolen from the threats that do.
Treat identity as a primary attack surface. Multi-factor authentication (MFA) and SSO are a starting point, not a finish line. Do you have visibility into session behavior, SaaS permissions, and token usage?
Clarify ownership before the next incident. When something goes wrong, does everyone know their role? If there's any ambiguity, that's the first thing to fix.
Design for humans, not perfection. When your systems fail, is it because people made mistakes or because the systems assumed they wouldn't? Even well-trained employees make mistakes under pressure. Build systems that catch those mistakes early, rather than ones that assume they won't happen.
Resilience is about more than just headcount or budget. It means your team has to be able to make decisions under pressure. The good news is that the shift from "prevention only" to "resilient operations" doesn't require a complete overhaul. It requires deliberate design and willingness to build for the threat landscape that actually exists today.
The teams that come out ahead will be the ones who made purposeful decisions before the next incident forced their hand.
If you’re ready to start building a more resilient security team, let Huntress help guide you. Download How to Build a Resilient Security Team for 2030.