|
A cybersecurity framework is a pre-built strategic plan—like NIST CSF, CIS Controls, or ISO 27001—that gives all businesses a proven roadmap to manage risk. Instead of risking a DIY security posture that might leave huge gaps, these standards give a common language that helps IT, HR, and legal teams communicate clearly. |
Cybersecurity frameworks are the blueprints for your digital defense.
Without one, you’re just guessing—and guessing leads to mistakes. Instead of just playing whack-a-mole with the latest threat, a framework gives you a repeatable game plan to keep your assets safe.
For scaling businesses with lean IT teams, these frameworks turn a chaotic to-do list into a prioritized roadmap. They help you prove to leadership and customers that you take data seriously. By using a standard like NIST or CIS, you’re reinforcing a security posture that keeps your business running.
Keep reading to learn more about common cybersecurity frameworks and which is best for your organization.
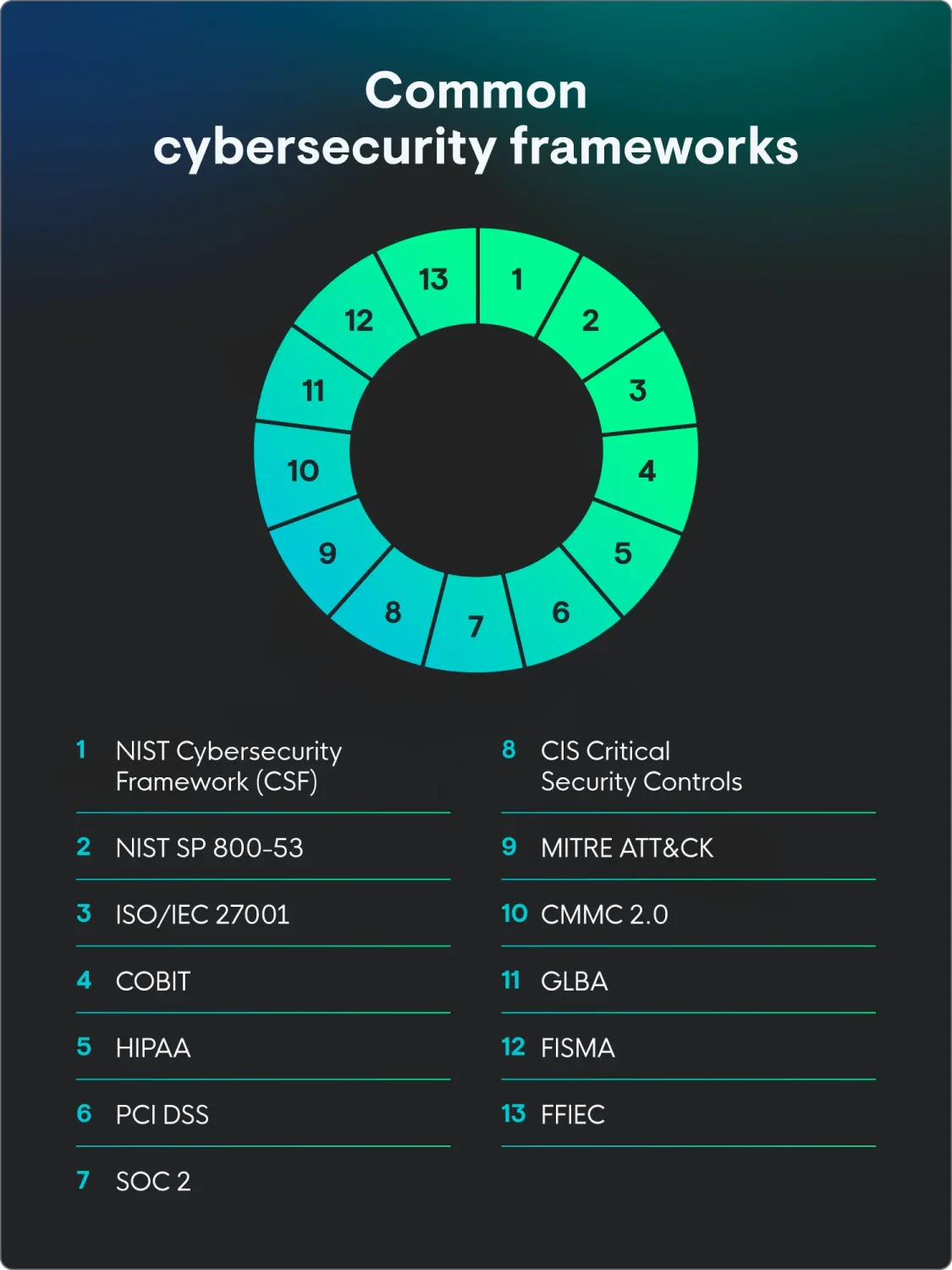
The 13 top cybersecurity frameworks
The top cybersecurity and regulatory frameworks offer guidance on cyber hygiene, steps for maintaining confidentiality, and more. The table below breaks down what each of these cybersecurity framework examples does and who it’s built for, helping you spot which ones align with your business goals or legal requirements.
Whether you need a technical to-do list or a high-level strategy for the boardroom, you can use this comparison to find your starting point:
|
Framework or regulatory framework |
Best for |
Core functions |
|
Organizations of all sizes looking for flexibility |
|
|
Federal agencies, government contractors, organizations with strict compliance requirements |
|
|
Scaling businesses |
|
|
Small IT teams |
|
|
Core-market companies |
|
|
Healthcare providers |
|
|
Businesses that handle credit card data |
|
|
SaaS companies, cloud service providers |
|
|
Security teams, security analysts |
|
|
Businesses in the Defense Industrial Base |
|
|
Financial institutions |
|
|
Federal agencies |
|
|
Banks, credit unions, financial services companies |
|
1. NIST Cybersecurity Framework (CSF)
Best for: Organizations of all sizes looking for a flexible, high-level gold standard to build and measure their entire security program
The NIST CSF is the heavy-hitter cybersecurity framework, but it doesn't feel like a dense government manual. It gives us a common language to talk about risk. Recently updated to version 2.0, it makes sure everyone—from the IT or security team to the boardroom—is on the same page.
It’s built around six core functions that help you manage the lifecycle of a security event:
-
Govern: Set the rules and strategy for the business.
-
Identify: Know what assets and risks you actually have.
-
Protect: Keep the bad actors out.
-
Detect: Spot them quickly if they get in.
-
Respond: Kick them out and limit the damage.
Get back to business as usual.
What makes NIST CSF great for scaling businesses is that it isn’t a pass/fail test. You use it to see where you are today and decide where you need to be. Huntress Managed ISPM, ESPM, and SAT map directly to these functions—especially Identify and Protect, while Managed EDR, ITDR, and SIEM connect to Detect and Respond. This helps you prove your security isn't just a collection of tools, but a cohesive strategy.
2. NIST SP 800-53
Best for: Federal agencies, government contractors, or any organization that needs a comprehensive, granular catalog of specific security controls to meet strict compliance requirements
If the NIST CSF is the high-level strategy, NIST SP 800-53 is the thick book of tactical instructions. It’s a comprehensive catalog of over 1,000 security and privacy controls designed to protect federal information systems. While it was built for the government, any scaling business can use it to find specific, technical instructions for securing their environment.
The framework is organized into 20 control families that span from access control to incident response. Because it’s so detailed, most organizations don't use every single control. Instead, they choose a baseline—low, moderate, or high impact—based on the type of data they handle.
Implementing 800-53 can feel overwhelming for a lean operation, but it’s the backbone for major certifications like FedRAMP and FISMA. Using a managed approach to operationalize these controls helps you check the boxes without getting buried in the technical weeds. It’s about taking those 1,000+ options and focusing on the ones that actually move the needle for your security posture.
3. ISO/IEC 27001
Best for: Scaling businesses looking to prove their security maturity to global partners and speed up sales cycles through international certification
ISO 27001 is the global language of trust. It’s a management system (the ISMS) that proves your business takes security seriously. For lean teams, this is key to passing vendor security reviews without having to fill out a hundred different spreadsheets for every new client.
The framework is built on three core pillars: Confidentiality, Integrity, and Availability. It forces you to look at your business through a risk-based lens, meaning you only implement the controls that actually matter to your specific operations. It’s less about doing everything and more about doing the right things and documenting them.
Getting certified involves a two-stage audit that checks your paperwork and your actual practice. Huntress helps you operationalize this by providing the evidence auditors love to see—like Managed Security Awareness Training records and proof of active endpoint monitoring. It turns a scary audit into a repeatable process that helps you win bigger deals.
4. CIS Critical Security Controls
Best for: Small IT teams that want a prioritized roadmap to stop the most common and damaging cyberattacks
If you’re feeling overwhelmed by giant lists of rules, the CIS Critical Security Controls (CIS18) are your best friend. They are a prioritized list of 18 actions based on real-world data from actual attacks. The goal is simple: do the most important things first to get the biggest boost in security for your effort.
The controls are broken down into three Implementation Groups (IGs). Most scaling businesses start with IG1—often called essential cyber hygiene. It’s a foundational set of 56 safeguards that every business should have in place, regardless of its size. It covers the basics like keeping an inventory of your hardware and software, managing passwords, and keeping your systems updated.
What makes the CIS controls so powerful is how well they map to Huntress Managed ISPM. We help you automate the heavy lifting for many of these controls — Managed EDR surfaces open ports and suspicious processes, while Managed ISPM hardens identity configurations to enforce access hygiene. Instead of a manual checklist, you get a managed way to stay on top of the basics, so your lean operation can stay ahead of the curve.
5. COBIT
Best for: Core-market companies that need to align their IT goals with their overall business strategy and governance
COBIT (Control Objectives for Information and Related Technologies) is the bridge between the IT department and the executive suite. It’s both a technical security guide and a framework for IT governance. It helps you make sure your technology investments actually support your business goals and that you’re managing risk in a way that aligns with those goals.
The framework is built on five key principles that focus on meeting stakeholder needs and covering the business from end to end. It helps lean operations move away from fixing things as they break and toward a more mature model where IT is a driver of growth. It’s about making sure your team is doing the right work for the right reasons.
Using COBIT helps you create a clear structure for decision-making and accountability. When you use Huntress to manage your security posture, you’re checking a major COBIT box by ensuring your technical controls are monitored and measurable. It turns complex IT tasks into clear business outcomes that show the value of your team.
6. HIPAA
Best for: Healthcare providers, dental practices, and anyone who handles protected health information (PHI)
HIPAA (the Health Insurance Portability and Accountability Act) is unique because it’s a legal requirement, not a choice. For growing businesses in the healthcare space, the Security Rule part of HIPAA is the part that really matters. It mandates that you protect the confidentiality, integrity, and availability of all electronic PHI (ePHI) with specific administrative, physical, and technical safeguards.
Unlike some frameworks that give you a strict list of tools, HIPAA is scalable. This means the law expects you to implement security measures that make sense for your size and specific needs. However, you still have to prove you’ve done a formal risk analysis and that you're actively monitoring for threats. If you can't show your work, the fines can be steep—even if you haven't had a breach.
Huntress Managed ISPM is a lifesaver for HIPAA compliance because it helps you tackle the technical safeguards without the manual headache. By enforcing strong multi-factor authentication (MFA) policies, monitoring for unauthorized access, and keeping a clean record of identity configurations, we give you the audit-ready reports you need. It turns HIPAA from a looming legal threat into a manageable part of your daily operations.
7. PCI DSS
Best for: Any business that processes, stores, or transmits credit card data—from a single-market retail shop to a global ecommerce leader
If you accept credit cards, you must comply with the Payment Card Industry Data Security Standard (PCI DSS). It’s a set of 12 requirements designed to make sure cardholder data stays safe from threats. The latest version, 4.0, focuses even more on continuous security. Failing to stay compliant can lead to heavy fines or losing your ability to process payments entirely.
The framework covers everything from how you build your network (like using firewalls) to how you manage passwords and track who accesses your data. For scaling businesses, the goal is to keep your cardholder data environment as small as possible. The less surface area you have to protect, the easier it is to manage.
Huntress helps you meet these requirements by handling the technical heavy lifting, like monitoring for unauthorized access and ensuring your endpoints are hardened. Instead of spending your week manually checking logs, you get the proof you need that your systems are protected. It’s about staying compliant so you can keep the revenue flowing without the extra stress.
8. SOC 2
Best for: SaaS companies and cloud service providers that need to prove to their customers—and their customers' auditors—that they are handling data securely
If you’re a scaling business in the tech space, SOC 2 (System and Organization Controls 2) is almost certainly on your radar. It’s an auditing procedure designed by the Association of International Certified Public Accountants (AICPA) that focuses on five Trust Services Criteria:
-
Security
-
Availability
-
Processing Integrity
-
Confidentiality
-
Privacy
SOC 2 requires you to prove that you’ve actually been following your own security policies over time. There are two versions you’ll hear about: Type 1 and Type 2.
-
A Type 1 report is a snapshot: It says your controls look good on paper today.
-
A Type 2 report is the real deal: It covers a period of time (usually 6–12 months) to show that your controls actually worked in the real world.
For lean IT teams, a SOC 2 report is a massive competitive advantage because it tells high-value clients they can trust you with their data. Huntress gives you the continuous monitoring, MFA enforcement, and incident response documentation that SOC 2 auditors look for.
9. MITRE ATT&CK
Best for: Security teams and analysts who need to understand how attackers actually behave so they can proactively hunt for threats and test their own defenses
MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) is like a playbook for how the bad actors operate. It’s a living, breathing knowledge base of real-world attacker behaviors. For a lean IT team, this framework is the ultimate map for understanding how a breach progresses—from the first phishing email to the final data theft.
The framework is organized into Tactics (the attacker's goal, such as “Initial Access”) and Techniques (how they achieve that goal, such as “Phishing”). By looking at the MITRE ATT&CK Matrix, you can see exactly where your security has blind spots. It shifts your focus from just looking for bad files to looking for bad behavior, which is how you catch sophisticated attackers who know how to hide.
10. CMMC 2.0
Best for: Any business in the Defense Industrial Base (DIB)—from aerospace manufacturers to IT providers—that wants to win or keep contracts with the Department of Defense (DoD)
The Cybersecurity Maturity Model Certification (CMMC) 2.0 is the DoD’s way of making sure everyone in their supply chain is actually doing the work to protect sensitive info. If you handle Federal Contract Information (FCI) or Controlled Unclassified Information (CUI), this framework is a requirement to bid on new contracts.
It’s built to stop threat actors from getting their hands on sensitive military or defense data through a partner's less-secure network. CMMC 2.0 keeps it simple by using three levels of maturity:
-
Level 1 (Foundational): Focused on basic cyber hygiene with 15 safeguards
-
Level 2 (Advanced): Aligns with NIST SP 800-171 and includes 110 practices to protect CUI
-
Level 3 (Expert): For the most sensitive programs, requiring 24+ specialized controls
For scaling businesses, the jump to Level 2 can feel like a lot because it requires proof of a hardened security posture. Huntress Managed EDR and Managed ISPM take the pain out of this by helping you meet many of those controls.
11. GLBA
Best for: Financial institutions—including non-traditional ones like mortgage brokers, tax preparers, and auto dealers—that handle sensitive consumer financial data
The Gramm-Leach-Bliley Act (GLBA) isn't just for big banks. If your business is involved in financial activities, you’re on the hook. The core of this for IT teams is the Safeguards Rule, which was recently updated with much stricter requirements. It mandates that you protect nonpublic personal information (NPI) through a formal, written information security program.
To stay compliant, you have to do more than just install a firewall. The rule requires specific technical hurdles, such as MFA for anyone accessing customer data, mandatory encryption of data at rest and in transit, and annual penetration testing or continuous monitoring. You also need to appoint a qualified individual to oversee the whole thing and report to your leadership.
12. FISMA
Best for: Federal agencies and any private-sector contractor, subcontractor, or grant recipient that supports federal programs or handles government data
The Federal Information Security Modernization Act (FISMA) is the law of the land for anyone doing business with the US government. It mandates that agencies and their partners build, document, and maintain a rock-solid information security program.
The goal is to protect federal data from unauthorized access, use, or disruption. FISMA relies heavily on the NIST RMF. To stay compliant, you have to follow a strict cycle:
-
Inventory: List every system and interface you use.
-
Categorize: Label your data as low, moderate, or high risk based on its importance.
-
Control: Implement the specific security recipes found in NIST SP 800-53.
-
Monitor: Watch your systems 24/7 to catch and report incidents as they happen.
At its heart, FISMA is about accountability. You have to prove you’re managing risk, not just hoping for the best. Huntress Managed EDR and Managed ISPM give you the continuous monitoring piece that FISMA requires, providing the automated detection and human-led analysis needed to protect federal data without a massive, in-house SOC.
13. FFIEC
Best for: Banks, credit unions, and financial services companies that need to meet the rigorous oversight standards of the Federal Financial Institutions Examination Council
The FFIEC isn’t just one rule—it’s a council of several federal agencies (like the FDIC and the Federal Reserve) that sets the bar for how financial institutions manage risk. Their Cybersecurity Assessment Tool (CAT) is the go-to for many scaling banks and credit unions to measure their maturity. It’s designed to help you see where your security stands today and what you need to do to hit the next level of protection.
The framework focuses on two main areas: Inherent Risk Profile and Cybersecurity Maturity. This helps you understand how much risk your specific business faces based on the services you offer, and then checks if your security controls are strong enough to handle it. It covers everything from protecting customer accounts to managing third-party vendors and responding to incidents.
How to choose the right framework for your team
With 13+ frameworks to pick from, you aren't expected to do all of them at once. Picking the right one is about finding the sweet spot where your security needs meet your business goals.
-
Industry-specific regulations: This is usually the must-do list. If you handle health data, HIPAA is your starting point. If you’re a defense contractor, CMMC 2.0 is non-negotiable. Start with the frameworks that keep you legal and licensed.
-
Customer and partner expectations: Sometimes the law doesn't care about your security, but your biggest customer does. If you’re a scaling SaaS business, you might find that you can't close deals without a SOC 2 report. Look at what your partners are asking for in their security questionnaires.
-
Available budget and team size: Be realistic about what your lean operation can handle. Some frameworks, like the CIS Critical Security Controls, are built for small IT teams and offer a high return on investment (ROI) without needing a massive budget.
-
Regional and state-specific laws: While many frameworks are national or global, state-level laws—like the CCPA in California or the SHIELD Act in New York—have specific rules for protecting data. Check in with your legal counsel or use resources like the International Association of Privacy Professionals (IAPP) to see which standards apply to your backyard.
-
Competitor standards: Research the standards your peers are using. Meeting or exceeding those industry benchmarks doesn't just help your security posture—it makes you the more attractive choice for risk-averse clients.
How to begin using a framework: 4 simple steps
Picking a framework is a big win, but the real magic happens when you actually put it to work. You don't need to overhaul your entire department overnight. The goal is to move from a reactive mode to a proactive, managed strategy that grows with your business.
-
Start with a gap analysis: Find where you stand by mapping existing strengths against the holes that need immediate attention. This helps you spend your budget and time where they’ll actually help the most.
-
Find quick wins with CIS Controls: Focus on high-impact, low-cost actions like MFA or inventory management to build early momentum. These essential hygiene tasks prove to your team that the framework is doable.
-
Secure leadership buy-in by talking business: Skip the jargon and frame security as a business enabler that helps close deals and protects your reputation. Show them how posture reinforces long-term growth.
-
Treat it as a cycle, not a project: Framework adoption is an ongoing process of improvement, not a one-and-done task. Stay agile with regular check-ins to make sure your security evolves alongside new threats.
Stay secure and compliant
Cybersecurity frameworks give the map, but you still have to drive the car. For lean IT and security teams, the goal isn't to collect as many certifications as possible—it’s to build a security posture that actually protects the business and helps it grow.
Whether you’re starting with the CIS Controls for some quick wins or diving into the deep end with NIST 800-53, the most important step is simply getting started.
Learn more about how Huntress is built to help you operationalize these frameworks without needing a massive team.
FAQ
What are the five NIST cybersecurity frameworks?
The current version of NIST has six core functions. The five original functions from version 1.1—Identify, Protect, Detect, Respond, and Recover—have now been updated to include a sixth: Govern.
Which is better, NIST or CIS?
Neither is “better” because the NIST and CIS serve different purposes. NIST CSF is a high-level strategic framework for managing overall risk, while CIS Controls are a prioritized, technical to-do list that tells you exactly which security settings to fix first.
Which cybersecurity framework is best?
The best framework is the one that fits your specific industry and team size. For most scaling businesses, starting with the CIS Controls for quick wins and moving toward NIST CSF for long-term strategy is the most effective path.
What are the key functions of the NIST cybersecurity frameworks?
The NIST CSF 2.0 uses six key functions: Govern, Identify, Protect, Detect, Respond, and Recover. These functions work together to create a continuous cycle that helps you manage and reduce your business’s security risk.