Learn more about Trumbull Tech and Huntress Managed ITDR helped an Accountant avoid financial ruin.
The little things we put off—or don’t do at all—can become the very things that break us. The danger isn’t the task itself. It’s the false sense of security you get from letting it slide. Reused passwords, delayed updates, unverified links, unprotected endpoints, and so on. Most days, nothing happens. But one day, something will.

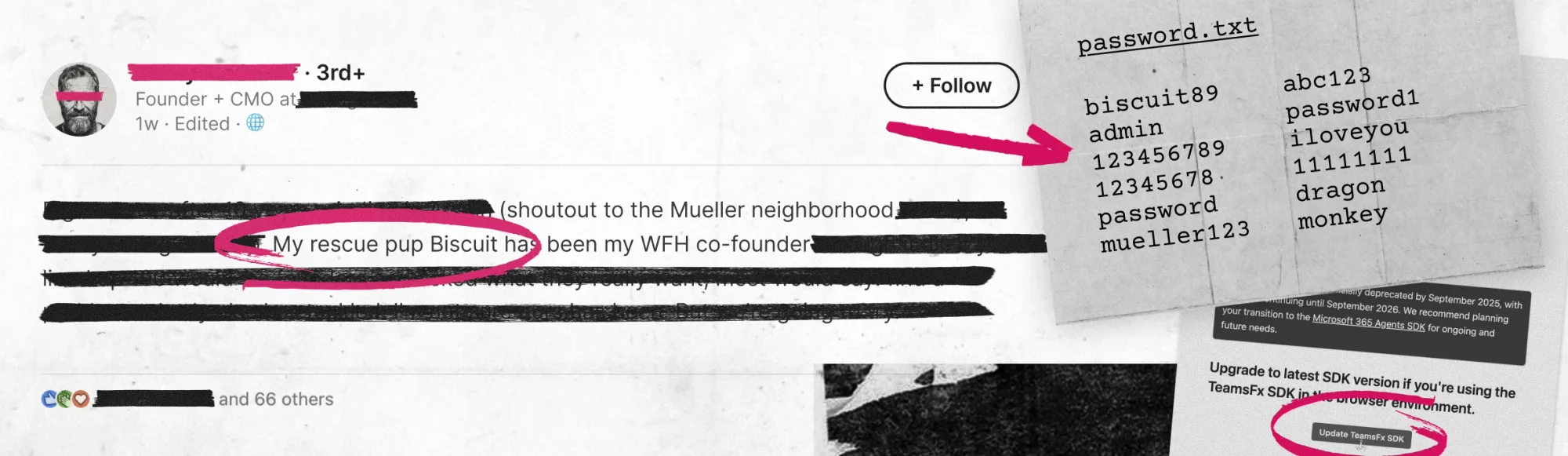
What you share on social tells attackers more than you think.
Join Huntress Principal Product Researcher Truman Kain and digital safety educator Caitlin Sarian (aka “Cybersecurity Girl”) for the latest edition of _declassified. They’ll reveal how attackers use your profile as intel and show you how to make yourself harder to target—with special guest Jai Minton, Senior Manager, Detection Engineering & Threat Hunting, joining the APAC session.
May 20, 2026 | 12:00pm EST | 5:00pm BST (US/EMEA)
21 May 2026 @ 10am AET | 12pm NZST (APAC)

Learn more about Trumbull Tech and Huntress Managed ITDR helped an Accountant avoid financial ruin.
This ebook breaks down what modern credential theft means for your business.
Phishing has been around forever, but it’s not slowing down. It’s just getting sneakier.


Attackers refined their playbooks in 2025, prioritizing stealth over speed. The frustrating part is how often outcomes still come down to fundamentals that didn’t get handled in time. The Huntress 2026 Cyber Threat Report breaks down what changed, what stayed familiar, and what we’re seeing most.
Increase in RMM abuse
Of malware loader activity involved ClickFix & fake CAPTCHAs
Were added to the average time-to-ransom (TTR)

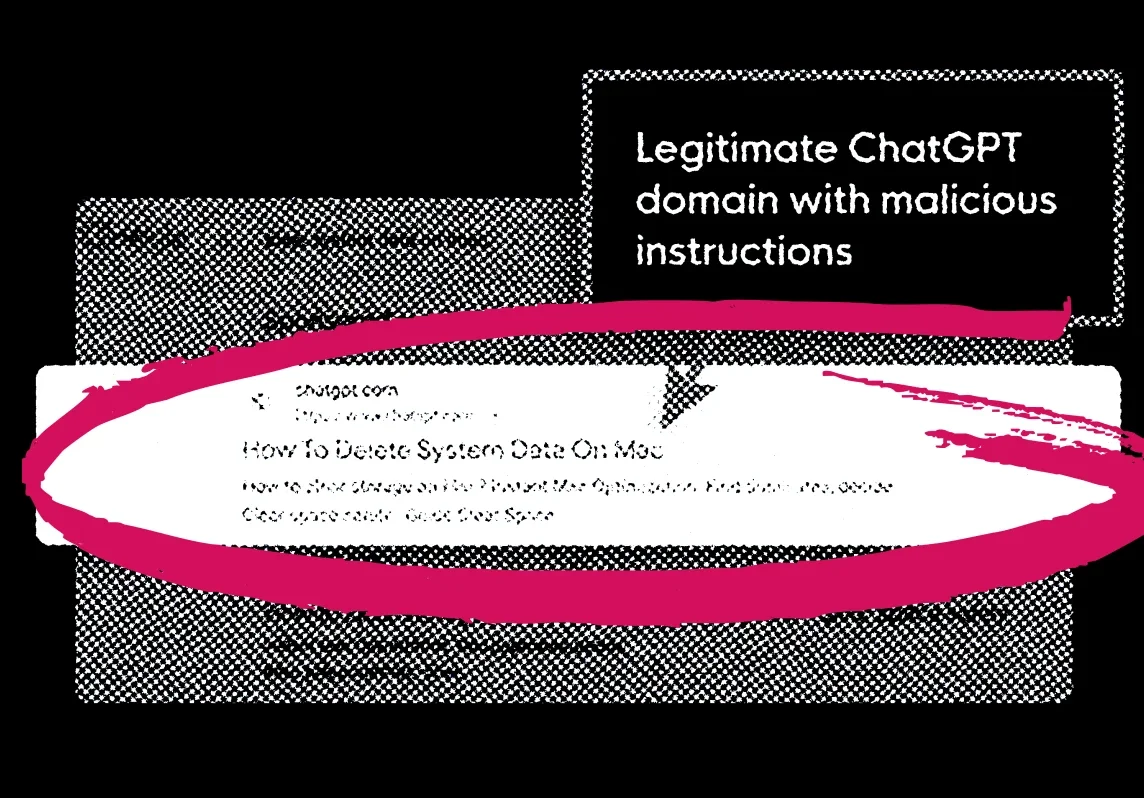
PHISHING
Attackers fine tune lures to match your day-to-day, and AI helps polish the details. E-sign requests, invoices, and login prompts are now indistinguishable from routine communication. That’s why the goal is resilience: catch it faster and limit the fallout when something slips through.


Hackers don't need much to phish you — a familiar logo, a sense of urgency, and a distraction on a Friday afternoon is all it can take to hand over your credentials without a second thought.

At the heart of this story lies a critical partnership that became the decisive barrier between restoring normal operations and total chaos.
No matter the scam, Huntress has your back 24/7 to shut down phishing scams early to protect your reputation and give you peace of mind.

STOLEN ACCESS
Attackers use ill-gotten passwords or session data (cookies or tokens) to pretend they’re legit users. It often starts with phishing or infostealers, though they can steal access in other ways, too. The risk grows when that access isn’t detected quickly and the attacker has time to escalate privileges, move laterally, and persist.


If a threat actor launches a ransomware, extortion, or identity theft attack, the odds are that infostealers—and the credentials they’ve compromised—are behind it.
At its core, credential theft is the unauthorized acquisition of login credentials such as usernames, passwords, or session tokens by a malicious threat actor.
Download to learn how Huntress shuts down infostealer threats in minutes, helping you protect your identity attack surface.

BUILDING RESILIENCY
Resilience means spotting trouble early, containing it quickly, and bouncing back fast. This is easier when your incident response and posture management run in a coordinated workflow, and when your insurance coverage aligns with your security controls. And when identity and endpoint signals are correlated in one place, you can prioritize the alerts that matter and act quickly.


Huntress surveyed 1,050 internal IT and security professionals across North America and the UK to find out where teams actually stand — not where vendor decks say they should be.

This guide explains what cyber insurance is, what it typically covers, and who benefits most from its protection.

We're thrilled to announce the expansion of the Huntress Agentic Security Platform with two new proactive offerings.

YOUR 24/7 TEAM
When everyday security basics slip, attackers move fast. That’s where the Huntress Adversary Tactics and the 24/7 Security Operations Center come in. These experts track real-world tradecraft, stop threats around the clock, and shut down the kinds of mistakes attackers love to exploit.


HUNTRESS PRODUCTS
The Huntress security platform is built, owned, and operated entirely by our team from first signal through remediation. Predictable pricing with no noise, just meaningful alerts.












Huntress Managed EDR doesn't just watch your endpoints—it’s a complete solution. From the second a threat appears until it’s eliminated, we handle everything. You get 24/7 continuous protection, detection, and response that disrupts and remediates threats.
Identity Threat Detection and Response (ITDR)
Finds and stops identity-based threats in Microsoft 365 and Google Workspace—because identity is the new endpoint, and attackers know it. Huntress Managed ITDR is designed to detect, respond to, and resolve critical identity-based threats like account takeovers, business email compromise, unauthorized logins, and more.
Huntress Managed SIEM takes away the complexity and overhead usually associated with traditional SIEMs, giving you everything you need and nothing you don’t. 24/7 threat response and strengthened compliance, fully managed by SOC experts, at a predictable price.
Engaging, expert-backed, personalized training content built on real-world threat intelligence and created by Emmy® Award-winning animators to reduce human risk and build a strong security culture.
Most hackers don’t "break in"—they just take advantage of messy settings, bad defaults, and accounts with too much access. Huntress Managed Identity Security Posture Management (ISPM) continuously audits and enforces configurations, policies, and permissions in Microsoft 365 so those easy attack paths are never open in the first place.
Huntress Endpoint Security Posture Management is proactive security that hardens endpoints to defend against attacks like ransomware and infostealers, and prevent breaches. Get broad endpoint visibility and control over configurations, applications, vulnerabilities, and more in one location and a single solution.


Discover how Huntress can help you spot trouble early and respond fast, so small issues don’t turn into major incidents. Book a demo to see it for yourself.