Passwords are part of life these days. The average person probably has hundreds of them—and they’re all unique, right? RIGHT?!
So how are you expected to keep track of them all? Well, you could write all your passwords down in a file, save it to your desktop, and be sure to name it “My Passwords” for safekeeping.
While that may seem like a joke (and please, NEVER do that), our experience tells us that some users actually do this. They will save plaintext passwords to their desktops as an easy way to keep track of their credentials. Part of that is because they don’t have the proper security awareness training to understand the risk that this exposes them to, but there are others who know that they shouldn’t do this but ignore that advice anyway.
We know this happens. We’ve seen this happen. But what the curious minds of the Huntress Product team were most interested to know is how often this happens. Turns out, it’s way more common than we thought.
Files with Exposed Passwords: How Prevalent Are They?
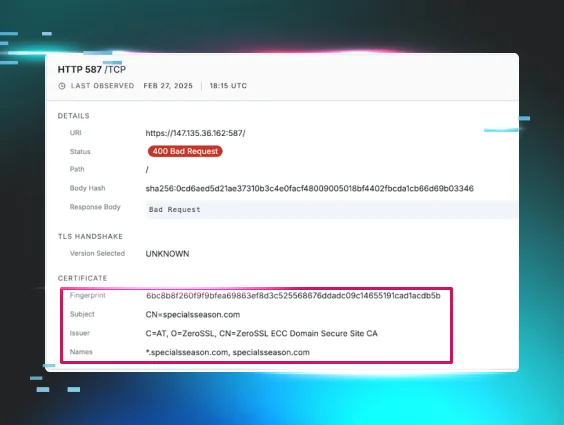
In early October, Huntress responded to an incident where multiple unsecured password files were present that may have been accessed by adversaries. After responding to this incident, it got us wondering: how many other instances of plaintext documents (think Notes app, Word docs, Excel files, etc.) across our managed endpoints could potentially contain exposed passwords?
So, our team decided to conduct an assessment of our managed endpoints to detect any files that we believe contain stored plaintext passwords (note: Huntress does not download or scan the file contents). The assessment was run across over 4,000 partner accounts, amounting to over 2 million total endpoints. Most of the analyzed endpoints were from small to medium-sized businesses.
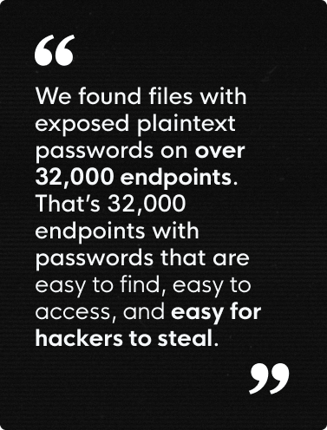
We were somewhat shocked by the high rates of exposed plaintext passwords we found. Here’s what we uncovered:
- Approximately 1.6% of all endpoints contained an exposed plaintext password file
- Over 200 partners had exposed password files on 5% or more of their total endpoints
- Over 100 partners had more than 50 endpoints with exposed password files
To put this into perspective, this means that we found files with exposed plaintext passwords on over 32,000 endpoints. That’s 32,000 endpoints with passwords that are easy to find, easy to access, and easy for hackers to steal. This poses a huge danger because these unencrypted files essentially contain the keys to things like business emails, bank information, sensitive user data, business-critical software log-ins, and the list goes on. And having this information out in the open is the ideal low-hanging fruit adversaries are after.
How To Protect Against Stolen Credentials
While security practitioners may well understand good cyber hygiene, there is a massive gap in education for users at small and medium-sized businesses. This presents an unfortunate opportunity for hackers to find low-hanging fruit to exploit.
Fortunately, there are simple steps you can take to reduce the risk of exposed passwords and account takeover.
- Give your users access to an encrypted password manager
- Deploy multi-factor authentication (MFA) wherever possible
- Build a security awareness training program
- Monitor your environment for evidence of account takeover
While 100% protection is never possible in cybersecurity, this combination of tools and tactics will make it significantly tougher for hackers to gain access to your accounts.
With security awareness training, you can empower users to identify and prevent attacks like phishing, social engineering, and business email compromise at the source, while password managers and MFA add additional layers of security and protection to end users' passwords and accounts. If an adversary ever does gain access, having a tool to monitor your environment will allow you to identify and stop malicious behaviors before they can do any damage.
Huntress Can Help
With the prevalence of potentially exposed passwords that we found through our initial scan, it was clear to us that we should make this a permanently available product feature for our partners. So, we have now baked this feature into our Huntress Managed EDR offering.
Partners and customers leveraging Huntress Managed EDR will be opted-in to “Credential Reports” to receive alerts any time the Huntress Platform detects a file that may contain exposed passwords. All accounts will be opted into this feature by default on 11/8 unless they opt out in Account Settings. Information on the feature and how to opt out (not recommended) can be found here.
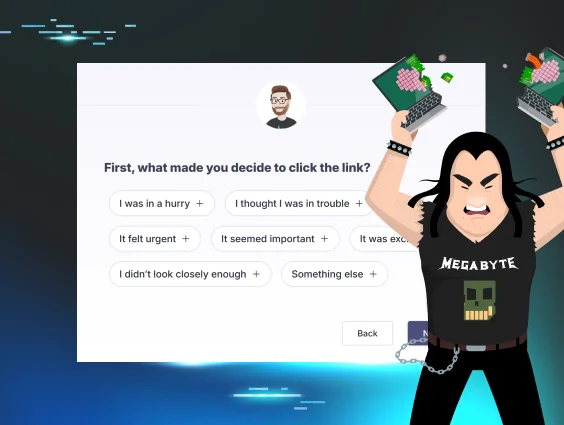
Huntress Security Awareness Training offers effective and engaging learning modules to help you educate your end users on cyber hygiene best practices (i.e., password management) and how to identify red flags like phishing scams and social engineering.
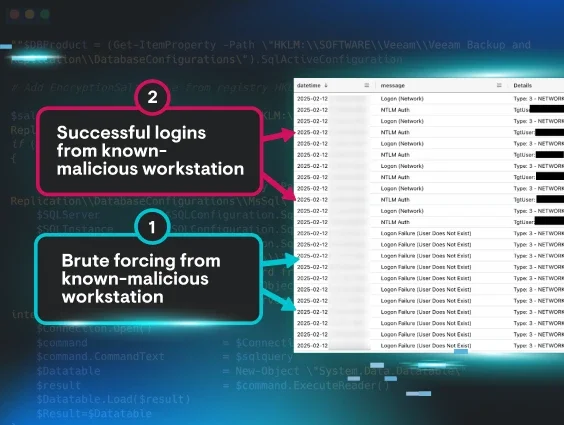
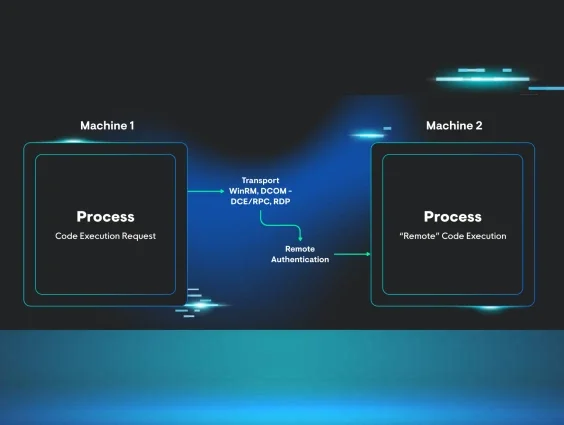
When attackers steal credentials, one of the most common ways they use them is by reusing them to conduct business email compromise (BEC). With Huntress Managed ITDR, you can have peace of mind knowing that a 24/7 SOC of security experts is monitoring your Microsoft 365 environments for BEC and other account takeover threats.
Huntress Managed SAT
Password Simulation
Technical controls only go so far. See how Huntress SAT closes the human side of the password problem with a free simulation preview.
Start for Free Today
Want to see if you have any exposed passwords in your environment? Take Huntress Managed EDR (with the Credential Reports feature) for a test drive and experience the power of endpoint protection, detection, and response backed by our team of human security experts.