Back when I worked in the division of student affairs, I came across an unsettling report from our university’s police department. One of my students (let’s call them ‘Jamie’) became a victim of a long and convoluted scam where a hacker pretended to be from the IRS.
It involved phishing, vishing, Apple gift cards, Uber, a statehouse, a university police department, and… me. The total damage? Jamie was out $10,000 in the form of five, untraceable $2,000 gift cards.
How did Jamie fall victim to this phishing gift card scam?
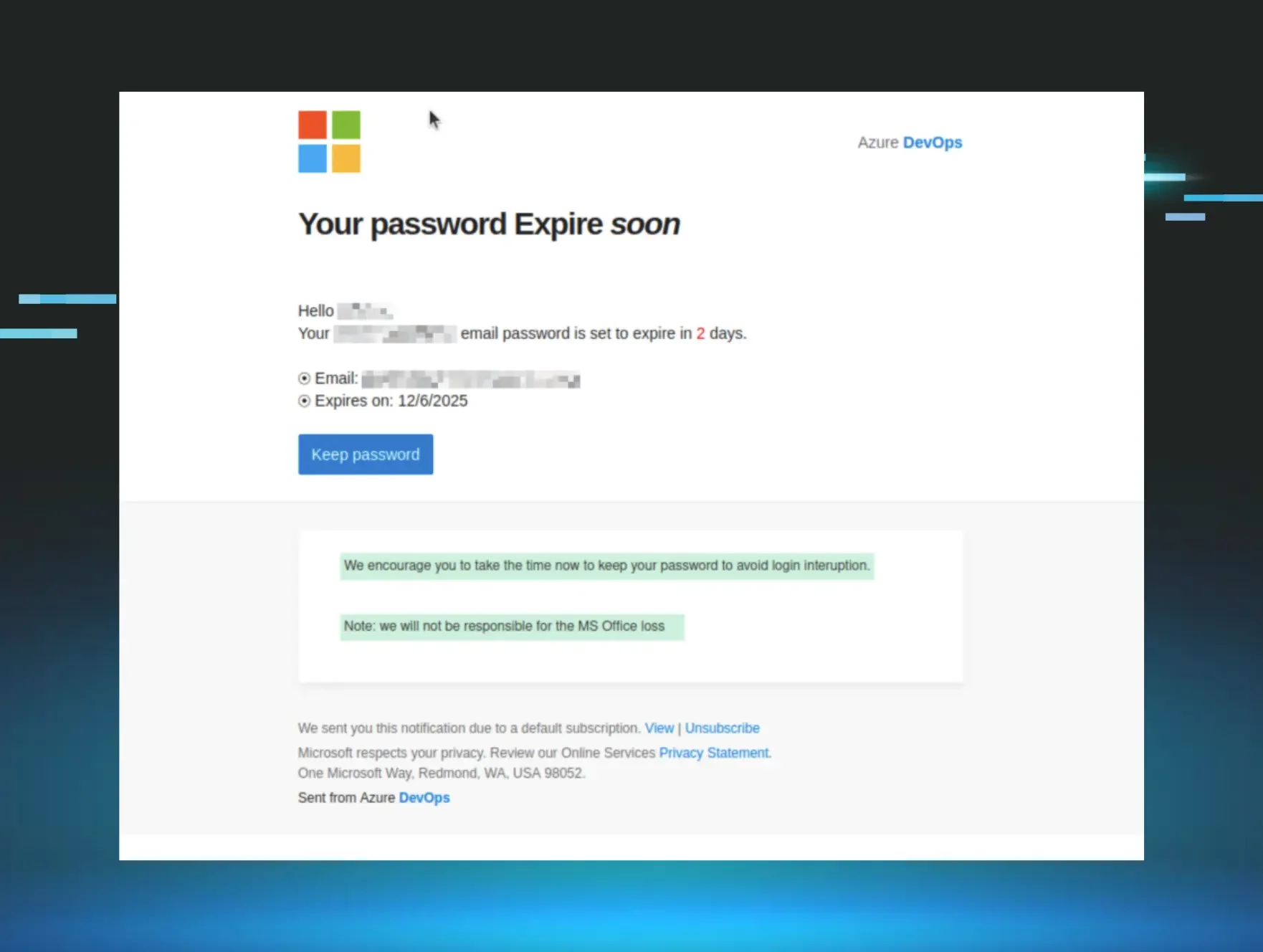
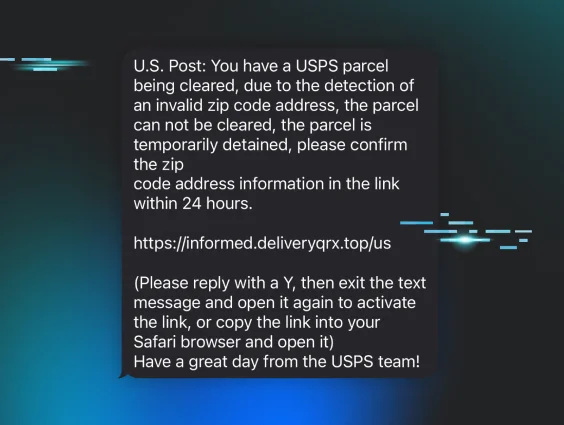
It all began with an email Jamie received with the following subject: “IRS URGENT: IMMEDIATE ACTION REQUIRED”
Jamie read “the Internal Revenue Service” was threatening legal action and arrest against them unless they acted quickly to resolve the matter.
Now this is where many of us might say “Wait, the IRS cannot arrest me. This is a scam.” But Jamie was a first-year college student, whose parents had always filed taxes on their behalf. Let’s face it: parents handling their dependents’ taxes is rather common for college students.
The body of the email instructed Jamie to click on a hyperlink and begin filling out a webform. The email went on to read that once the form was completed, they should expect a phone call from an IRS agent to close the case.
Jamie received the phone call shortly after submitting the form, and it was “an IRS agent” on the other line. Cough, cough, scammer.
The scammer said they needed to collect more information–which amounted to Jamie revealing their current location and current address–and that Jamie had an outstanding debt owed to the IRS. The scammer explained Jamie could pay $20,000 via money order, or they can pay $10,000 in the form of Apple gift cards as ‘the IRS has an agreement in place with Apple’ where they cover overdue taxes in exchange for credit because it is a U.S. company.
…more lies…more lies…
Also, the scammer instructed Jamie to stay on the phone the entire time and said:
1. Take an Uber to the nearby Apple store [10 minutes from campus]
2. Purchase five, $2,000 Apple gift cards
3. Take an Uber to the statehouse downtown [40 minutes away]
Jamie followed the scammer’s instructions, purchased $10,000 in gift cards from the Apple store, and while in the Uber on the way to the statehouse, the scammer told Jamie to put the phone on speaker, begin reciting the gift card numbers, and scratching off the pin on the back of each card.

Now remember, the Uber driver did not hear any of this conversation until Jamie turned the phone on speaker.
The Uber driver felt as though something bizarre was happening, then asked Jamie a few questions about why they were headed to the statehouse, probed with a few more questions, then told Jamie he thought they were being scammed. When the scammer heard this [the phone was still on speaker] the scammer ended the call.
The Uber driver kindly canceled the fare and returned to campus, and Jamie contacted the university police department. The responding officer contacted Apple to see if they could freeze the gift cards, to which Apple said the funds had already been spent.
That was it.
How was this bizarre and vile phishing scam so successful?
It wasn’t until I later sat down with Jamie that I learned the full context of this scam [read on to see our conversation]. But when I read the police report, I thought to myself: “How could a college student be so susceptible to such an elaborate scam?”
I had heard of scams where people end up going to a landing page and typing in personal and bank account information, but never anything like this one.
This scammer was successful because they created an environment of urgency, and made the first action in the scam so incredibly easy. They designed a low floor to engage Jamie, and placed Jamie in the driver’s seat as well.
Step 1: Get Jamie to click on a link. Pretty easy.
Step 2: Get Jamie to enter in some personal information. Also easy.
Once the scammer got Jamie on the phone, Jamie was hooked then tricked into seeing the issue through.
The aftermath & response
Once university police forwarded the case to student affairs, it became a closed case; there was nothing the police department could do. When I followed up with the reporting officer, he shared the extreme likelihood the assailant was in a region outside of the United States. When I asked why he seemed so convinced, his reply shocked me. The officer explained that the university police department sees a number of these scams where students are specifically targeted, and their hands are tied when they investigate and learn the IP address pings outside of the country.
So what could I do to help Jamie? Frankly, there wasn’t much I could do. They lost the $10,000, there was no way to getting that back. I asked Jamie what was on their mind and we unpacked how this happened. This is what Jamie shared:
“Well, I am kind of embarrassed, because I hear about those ‘Nigerian Prince’ scams all the time and laugh, thinking to myself how gullible someone must be to fall for something like that. But when I really think about my situation, I felt like it was a really important emergency. And felt like I needed to address it. And the first step was something easy, I just had to click the link and type in some of my information on a website. And after that, everything just felt required because I already began the process of ‘resolving’ the situation.”
It felt unreal to hear the full story, the full sequence of events in hindsight; from the web form to a phone call, to the Apple Store, to reciting the numbers and scratching of pins codes on the back of the gift cards–just unreal.
So what can you do to prevent a gift card scam from happening?
We all know those helicopter parents still see their college students as kids. Professionals in higher education acknowledge students as young adults, and it takes a village to help students develop competence and independence. Anyone can be a target of a cyber attack, even CEOs in the cybersecurity industry.
Young adults are a prime target for IRS phishing scams. It is rather unlikely that college students of today file their own taxes, usually due to parents typically filing on their behalf [lucky them]. So what happens when a scary email from an unwieldy and ubiquitous organization tells them they must take immediate action? Well, if you’ve made it this far, you know the result.
So where does this story leave us? Are we to let these students fail forward by falling victim to phishing scams? Or can we proactively educate them to defend themselves against hackers?
Even individuals who laugh at the absurdity of Nigerian princes can fall victim to scams when it feels so real, it’s the reason why so many people are impacted by phishing scams.