Modern security teams carry a constant mix of pressure. They are balancing risk, cost, visibility, and response while trying to build a stack they can actually rely on.
There is no shortage of tools promising stronger protection, cleaner visibility, and tighter control across the environment. Choosing the right mix for your organization’s risk profile and budget is where the real challenge begins. A dependable security stack still matters. It helps protect customer data, support compliance efforts, and keep identities, endpoints, and systems from becoming easy targets.
The bigger conversation is resilience.
Resilience lives in the technology and in the team using it. A resilient security stack helps teams find threats early, limit damage, and reduce operational drag. It supports the way real security teams work when the pressure is on.
When a stack creates too much noise, too many handoffs, or too much uncertainty around the next step, it slows the people who need to move fast.
That is why the strongest security programs pair the right stack with a team that can stay clear-headed, make decisions quickly, and respond with confidence when prevention falls short.
What is a security stack, and why does it need to be resilient?
A security stack should help your team spot threats sooner, respond faster, and keep operations moving when attackers slip through.
A security stack is the mix of software, tools, technologies, and processes that work together to defend an organization from cyber threats. It is the foundation that helps protect sensitive data, critical systems, and users through layers of visibility, detection, control, and response.
A reliable stack is built with purpose. It should help detect threats early, reduce downtime during incidents, and limit the kind of inefficiencies that drain time and focus. That matters even more now because attackers often avoid loud break-ins. They use valid credentials, abuse sessions, and blend into everyday behavior. A resilient stack has to support speed, visibility, and response across that reality.
The dangers of overloading your security stack
More tools can create more friction when they add noise, overlap, and complexity to your team’s day.
Expanding your security stack without a clear purpose can weaken your program instead of strengthening it. More tools can mean more dashboards, more duplicate alerts, and more context-switching for teams that already have plenty to manage.
Picture an analyst bouncing between products that are all describing the same suspicious activity in slightly different ways. That kind of clutter slows response, drains attention, and gives attackers more time to move.
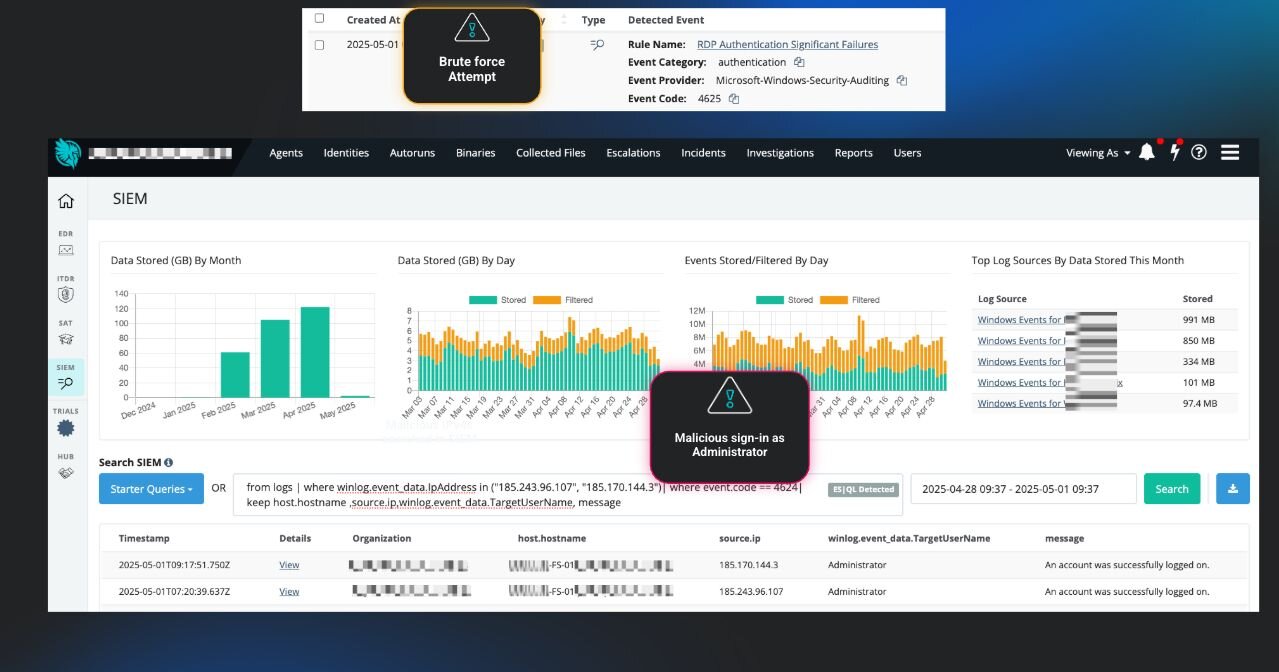
The survey data backs that up. Huntress found that 64.1% of teams say at least 25% of their alerts are noise, and 24.8% say more than half of their alerts fall into the “meaningless-noise” category. That kind of overload makes it harder to spot what matters, validate what is real, and move with confidence.
The strongest stacks sit in the sweet spot between strong coverage and day-to-day usability. They give teams the visibility they need without burying them in extra work.
A resilient security stack needs a resilient security team
Technology can surface the signal. Resilience depends on the people, workflows, and ownership that turn visibility into action.
This is the part many organizations miss.
You can have endpoint protection, identity controls, logging, and the usual security building blocks in place. The whole system still starts to wobble when nobody is sure which signals matter most, who owns the next decision, or how the response should unfold when something suspicious appears.
Resilience comes down to how teams operate.
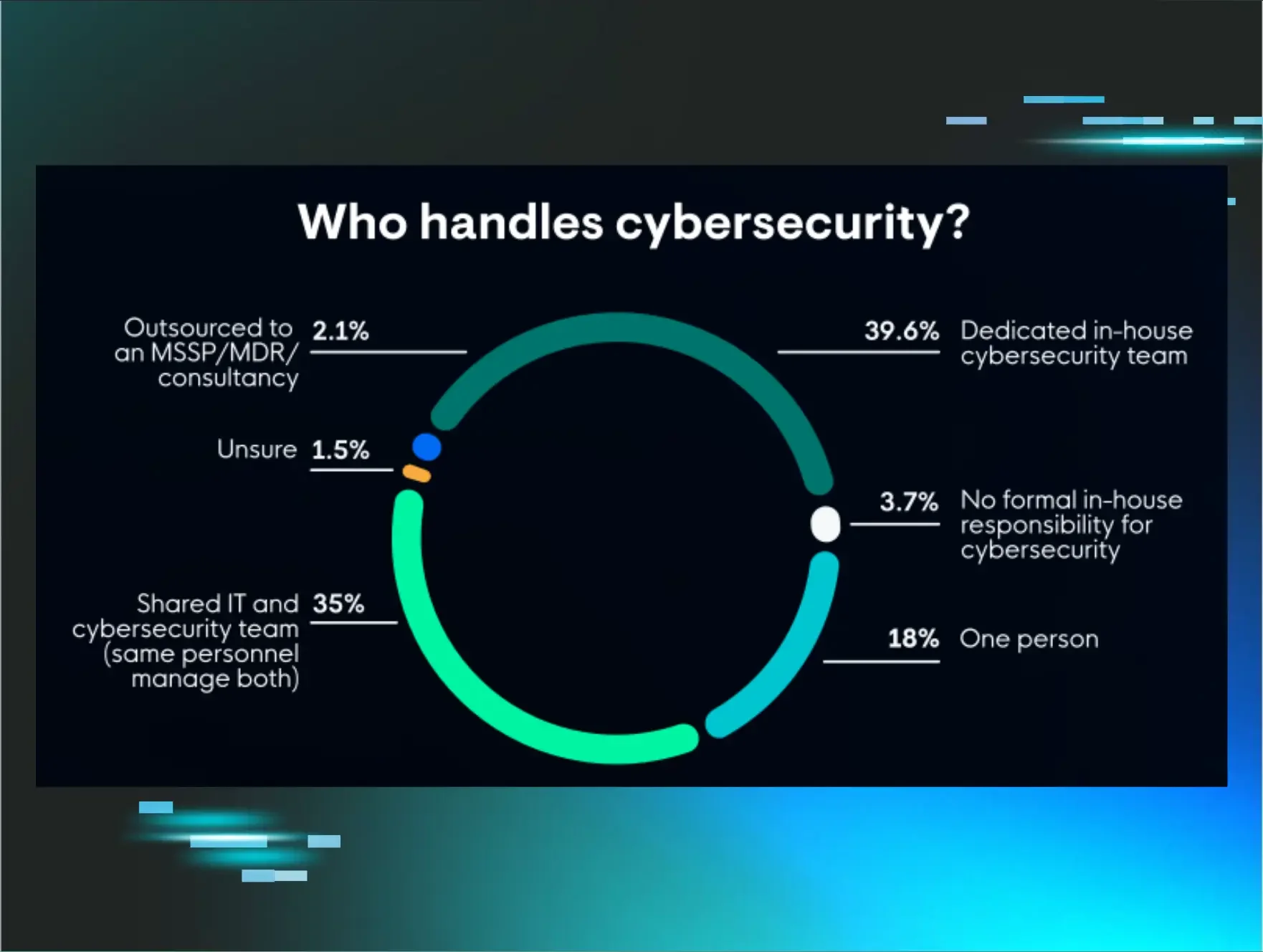
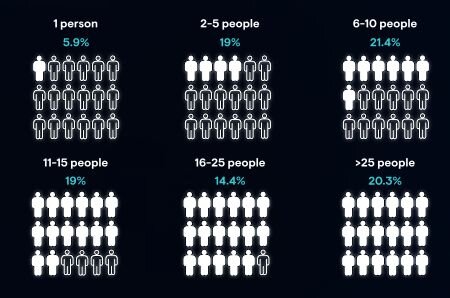
Many organizations are working with lean internal teams, shared IT and security responsibilities, or one person carrying cybersecurity for the business. Huntress survey data shows the most common team sizes fall between six and 10 people at 21.4% and 11 to 15 people at 19%. Only 39.6% report having a dedicated in-house cybersecurity team, 35% say IT and security responsibilities are shared, and 18% say cybersecurity is handled by a single person. In that kind of environment, clarity matters as much as coverage. A resilient team knows where to focus, how to prioritize, and what to do next.
A few patterns show up again and again:
They optimize for speed. Visibility becomes useful when it helps teams make decisions and act quickly. Strong teams know how to separate real signal from background noise.
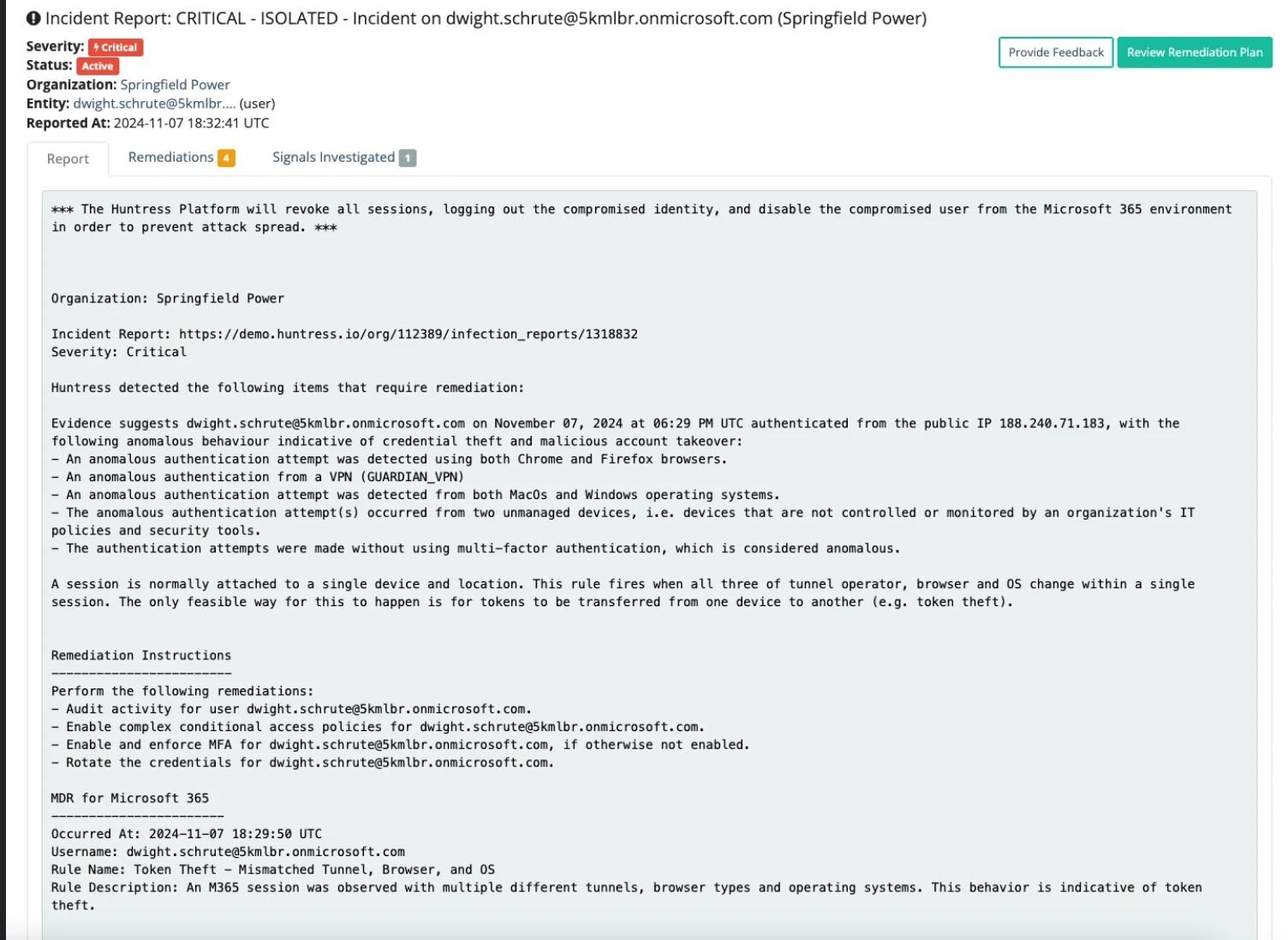
They treat identity as foundational. Modern attackers often log in through stolen credentials, hijacked sessions, or abused SaaS access. Teams need visibility into behavior, misuse, and suspicious access patterns.
They build systems that support humans. Security programs work better when workflows, tools, and controls account for the way people actually operate under pressure.
They use AI to reduce cognitive load. Nearly half of respondents, 46.9%, say AI is a critical part of their strategy. Its clearest value shows up in threat detection, automated response, and faster analysis that helps teams cut through noise.
They prioritize ownership. Clear accountability keeps investigations moving and helps teams respond decisively when something goes wrong.
Roles may scale with the size of the business. Ownership still has to be clear. That is what turns a collection of tools into a security system a team can trust.
Once that foundation is in place, the next question is what the stack should actually do for the team using it. The right tools should help people spot risk earlier, focus on what matters, and respond without piling on more noise or complexity. That starts with a few core layers that strengthen visibility, support faster decisions, and make the security program more resilient day to day.
Think like an attacker
Understanding how attackers see your environment can help you close the gaps they are most likely to exploit.
Attackers look for openings, weak points, and opportunities to move with the least resistance. That could be an unpatched vulnerability, an exposed identity, a weak SaaS permission model, or a poorly secured server. Looking at your environment through that lens helps you build a stack that can detect, contain, and disrupt malicious activity earlier in the attack path.
Where to start:
Use offensive security exercises such as penetration testing, red teaming, or purple teaming to see your infrastructure from an attacker’s point of view
Pull in real-world tradecraft insights so your defenses reflect how attackers actually operate
Early threat detection and response
The earlier you catch suspicious behavior, the better your chances of limiting the damage.
Early threat detection should be a core part of any resilient security stack. Fast detection creates more room to investigate, contain, and respond before attackers reach sensitive systems, identities, or data.
Detection also needs a clear response path. Teams need to know who owns the investigation, who takes action, and how the handoff works when alerts fire.
Where to start:
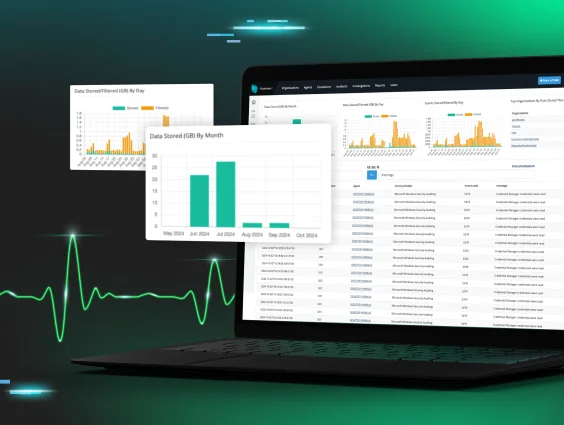
Use Security Information and Event Management (SIEM) and detection workflows that surface suspicious activity early
Make ownership of the investigation and response clear before an incident starts
Identity and access management
Identity has become one of the most important places to watch because attackers increasingly rely on valid access to blend in.
Strong identity protection is a core part of any successful security stack. IAM platforms like Okta or Microsoft Entra ID still play an important role, and modern threats have pushed the conversation well beyond multi-factor authentication (MFA) and SSO alone. Attackers increasingly target sessions, tokens, SaaS permissions, and cloud identities because those paths can look legitimate at first glance.
That pressure shows up clearly in the survey results. Identity-based attacks are the threat category teams feel least prepared to defend against at 26.5%. At the same time, 32.1% say they do not have Managed Identity Threat Detection and Response (ITDR) and believe it would increase their confidence in stopping an incident. Teams need visibility into identity misuse, unusual behavior, and suspicious access patterns before valid access turns into business impact.
Where to start:
Strengthen IAM foundations across authentication and access controls
Add visibility with ITDR for identity abuse, suspicious behavior, and session-based threats
Visibility across assets and endpoints
Visibility across assets and endpoints gives teams a clearer picture of what needs protection and where attackers may try to land.
You can’t protect systems you can’t see. Unmanaged devices, shadow IT, and visibility gaps create openings that attackers know how to exploit. Endpoint coverage matters for the same reason. Endpoints are where attackers often establish footholds, escalate privileges, persist, and reach for sensitive data.
Strong visibility helps teams find problems sooner and respond before activity spreads. It also helps security teams confirm that the controls they expect to be running are actually in place across the environment.
Where to start:
Continuously monitor your asset inventory, so your team knows what exists and what needs protection
Validate that endpoint coverage matches the environment your business is actually running
Use Managed Endpoint Detection and Response (EDR) to investigate suspicious behavior, contain activity quickly, and shorten the path from detection to response
Zero trust, but not by itself
Zero trust helps reduce exposure, and it works best as one layer in a broader defensive system.
Zero trust still plays an important role in limiting access and reducing lateral movement. It helps security teams shrink the paths attackers can use once they gain access. That matters, especially when attackers are operating with legitimate tools, trusted applications, and valid accounts.
Teams still need identity visibility, endpoint detection, and a response model that holds up when suspicious activity slips through. Zero trust works best when it supports a larger system built around visibility, detection, and action.
Where to start:
Apply zero trust principles to reduce unnecessary permissions across your organization
Support those controls with identity visibility, endpoint detection, and a response plan your team can execute
Resilient security programs win the long game
Long-term resilience comes from pairing the right defenses with a team that can make sense of the signal and act when it matters.
A resilient security stack gives teams the visibility, context, and coverage they need to respond under pressure. A resilient security program makes those capabilities usable in the real world. It gives people clearer ownership, cleaner handoffs, and better ways to move when something looks off.
That is where resilience starts to feel real. The stack supports the team. The team makes the stack useful. Together, they create a security program that can hold up when attackers find an opening.
Strong stack. Strong team. Real security resilience.