In 2026, the endpoint security issues facing businesses look way different from malware campaigns of a decade ago. Endpoints, identities, and cloud workloads now overlap, and traditional antivirus or perimeter-only defenses can’t keep up with fast-moving threats.
Threat actors are using methods like living-off-the-land (LotL) attacks to quietly sneak into your environment. To keep up, you have to evolve your security strategy and plan for incidents before they happen.
Here are 10 endpoint security trends shaping 2026 and what they mean for your business.
1. Watch as the AI race speeds up
Trend: As AI-powered endpoint tools become more advanced, organizations have new security and ethics risks. The focus in 2026 is on balancing autonomy with control, so AI decisions don’t go unchecked.
AI used to be a nice-to-have feature. But now, it’s becoming more embedded in day-to-day security operations. Your endpoint security partner needs to be intentional about using the right AI systems.
This is especially true with agentic AI, or agents that analyze huge volumes of data and even automate parts of investigations.
These agents are only as strong as their training and guardrails, and they can miss novel threats or behave unpredictably if they’re attacked or misused. Attackers can also target the agents themselves as a non-human identity, trying to hijack:
-
API keys
-
Tokens
-
Service accounts created for AI tools
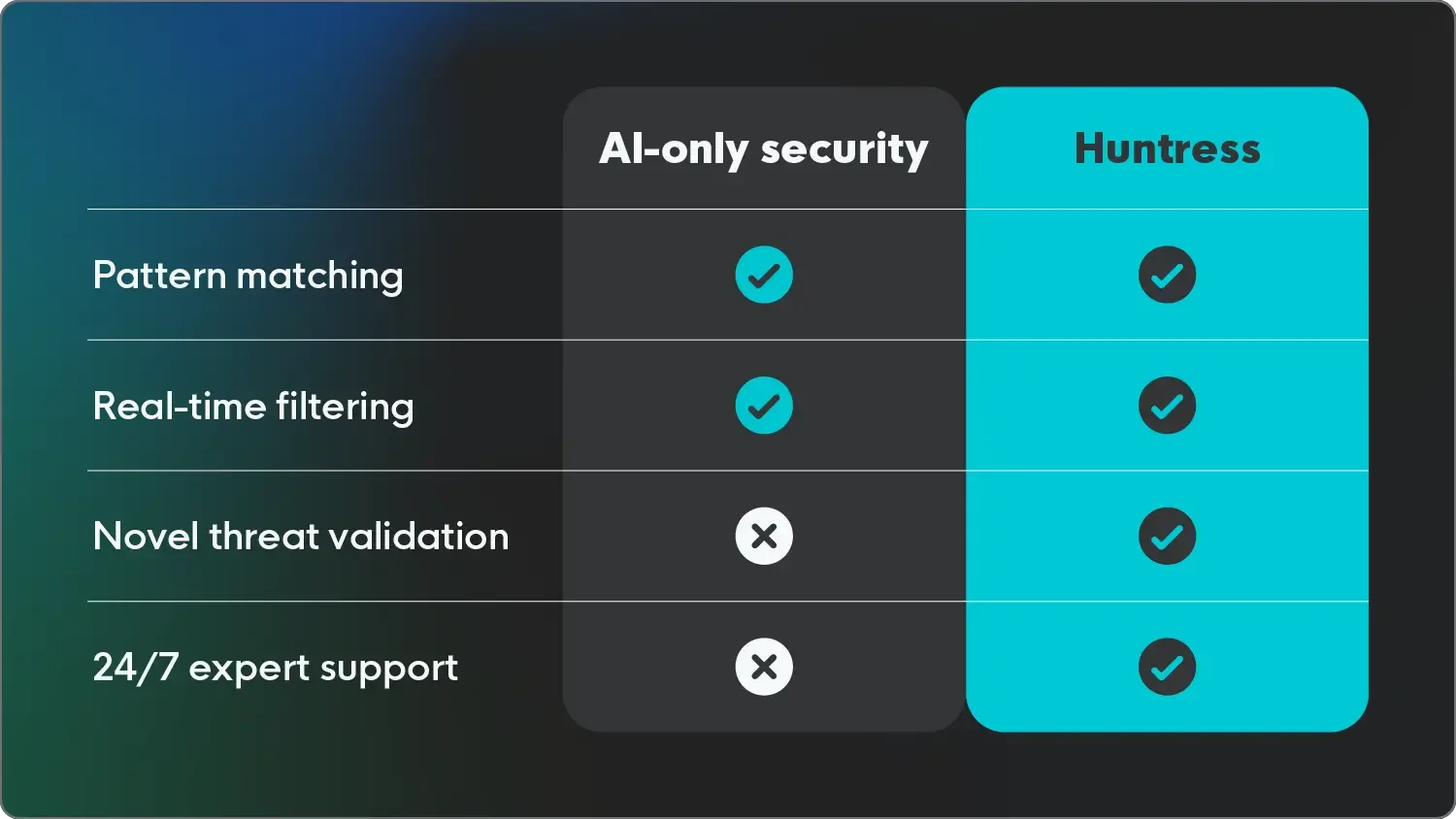
AI works best with human oversight rather than being the final decision-maker. That’s where Huntress shines, pairing AI-driven detections with 24/7 human security operations center (SOC) analysts who validate suspicious activity and step in before mistakes turn into breaches.
2. Keep an eye on ransomware’s shifting tactics
Trend: Ransomware is evolving. Threat actors are moving from single-encryption events to multi-layered extortion, heightening business risk and public fallout.
Ransomware is still one of the biggest threats to endpoints, but the playbook has changed. Many groups now use double or triple extortion, combining data theft, encryption, and public pressure to force higher payouts.
These multi-front attacks mean every minute counts. After gaining a foothold, attackers might quickly harvest credentials and threaten disclosure long before deploying encryption.
With so much at stake, fast detection is critical. Strong endpoint visibility and strong ransomware protection, paired with managed endpoint detection and response, reduce dwell time and stop an incident before it spirals into downtime or data exposure.
3. Get your incident response plan in shape
Trend: Security is about preparation just as much as prevention. Without a tested IR plan, even small attacks can spin out into chaos.
Plenty of businesses have security measures, but not nearly enough have a clear, tested incident response (IR) plan. In fact, in Verizon’s 2025 Data Breach Investigations Report, they discovered only 55% of companies have a fully documented IR plan. And IBM’s Cost of a Data Breach Report 2025 revealed that just 30% regularly test those plans.
When an attack hits and no one’s sure who does what, it’s easy to lose precious time just figuring out the basics. Details like who to call and how to communicate with leadership or customers can quickly slip through the cracks without a defined plan.
A solid IR plan outlines:
-
Roles
-
Decision paths
-
Contact trees
It also includes playbooks for common scenarios like ransomware and suspicious remote access.
The right partner for managed endpoint detection and response (EDR) can support that plan with real-world expertise, the way Huntress can. That experience includes 24/7 monitoring and clear guidance for your team as they move from detection to clean-up.
4. Be aware of EDR to XDR platform consolidation
Trend: Blending security layers under one roof can enhance visibility, but not if complexity muddies the waters.
As digital environments become more complex, many security teams are looking beyond standalone EDR to extended detection and response (XDR), which pulls in signals from endpoints, email, identities, and cloud workloads.
The idea is to correlate events across these layers so you can spot patterns that might not stand out when each system is viewed in isolation.
Consolidation, though, shouldn’t come at the expense of clarity. This broader view can introduce tool fatigue for smaller teams unless it comes from an all-in-one solution.
|
What XDR Can Help You Do |
Where Teams Still Get Tripped Up |
|
Correlate events across endpoints, email, identity, and cloud |
Overloading small teams with more data than they can review |
|
Spot multi-stage attacks that span multiple systems |
Relying on complex dashboards without clear guidance |
|
Reduce blind spots between separate security tools |
Assuming a single point of visibility equals full coverage |
|
Simplify licensing and vendor relationships |
Neglecting core risks like compromised endpoints and phished credentials |
The majority of successful attacks still start with a handful of familiar paths:
-
Compromised endpoints
-
Phished credentials
-
Malicious email
The Huntress Managed Security Platform focuses on securing these primary threat vectors. In return, you get deeper visibility where attackers are most likely to strike, without drowning in a bloated toolset you don’t have time to manage.
5. Focus on identity-first security and zero-trust architecture
Trend: Perimeters have dissolved, and identities are the new battleground. Securing logins and access credentials is now central to protecting every endpoint.
With so many apps in the cloud, identity has become the real perimeter. The best phishing protection guards identities to keep them out of the wrong hands.
Threat actors often find it easier to steal or phish credentials than to exploit a local vulnerability. Then, they use those stolen accounts to blend in with normal activity. That’s why identity-first security and zero trust architecture (ZTA) are now central to modern security strategies.
ZTA doesn’t grant long-lived trust. It assumes every session could be risky and leans on continuous verification, like repeatedly checking on:
-
Device health
-
User behavior
-
Usage context
Managed identity threat detection and response (ITDR) builds on that by watching for post-compromise behavior, like unusual logins and multi-factor authentication (MFA) fatigue.
When ITDR works alongside EDR, your team can spot both the compromised laptop and the compromised account it’s impersonating. It strengthens detection across every layer of your environment and closes the gaps attackers rely on.
6. Treat your supply chain as a major initial access risk
Trend: Attackers are exploiting trusted vendors, turning supply chains into backdoors for compromise.
The software and service providers your business relies on can become stepping stones for attackers.
High-profile incidents like the Kaseya supply chain attack show how compromising one vendor can give broad access to hundreds or thousands of downstream environments. That risk has only amplified with automation and remote tooling, making these relationships even more attractive to bad actors.
Protecting your endpoints now means monitoring how connected systems behave, which includes:
-
Locking down remote management tools
-
Enforcing least privilege for third-party access
-
Pairing vulnerability management with continuous monitoring
This is all to ensure unusual behavior from a trusted vendor doesn’t slip by. Even if you can’t control every partner’s security posture, you can watch how tools behave on your endpoints and be ready to contain abuse quickly.
|
Quick Checks for Vendor-Related Endpoint Risk |
|
7. Ride the wave of posture management
Trend: Misconfigurations are still the easiest way for attackers to get in. Fixing small mistakes prevents big breaches.
Endpoint security posture management helps find and fix these configuration issues at scale. These tools also keep an eye out for drift as settings change over time.
For many businesses, tying this to dedicated Microsoft 365 security monitoring is key. They need to watch for risky settings and data access patterns that might indicate someone is abusing those misconfigurations
Misconfigurations in Microsoft 365 and other cloud services and productivity platforms are a quiet but consistent source of breaches. Attackers are more than happy to walk through open doors left by occurrences like:
-
Over-permissive sharing
-
Weak access rules
-
Ineffective legacy protocols
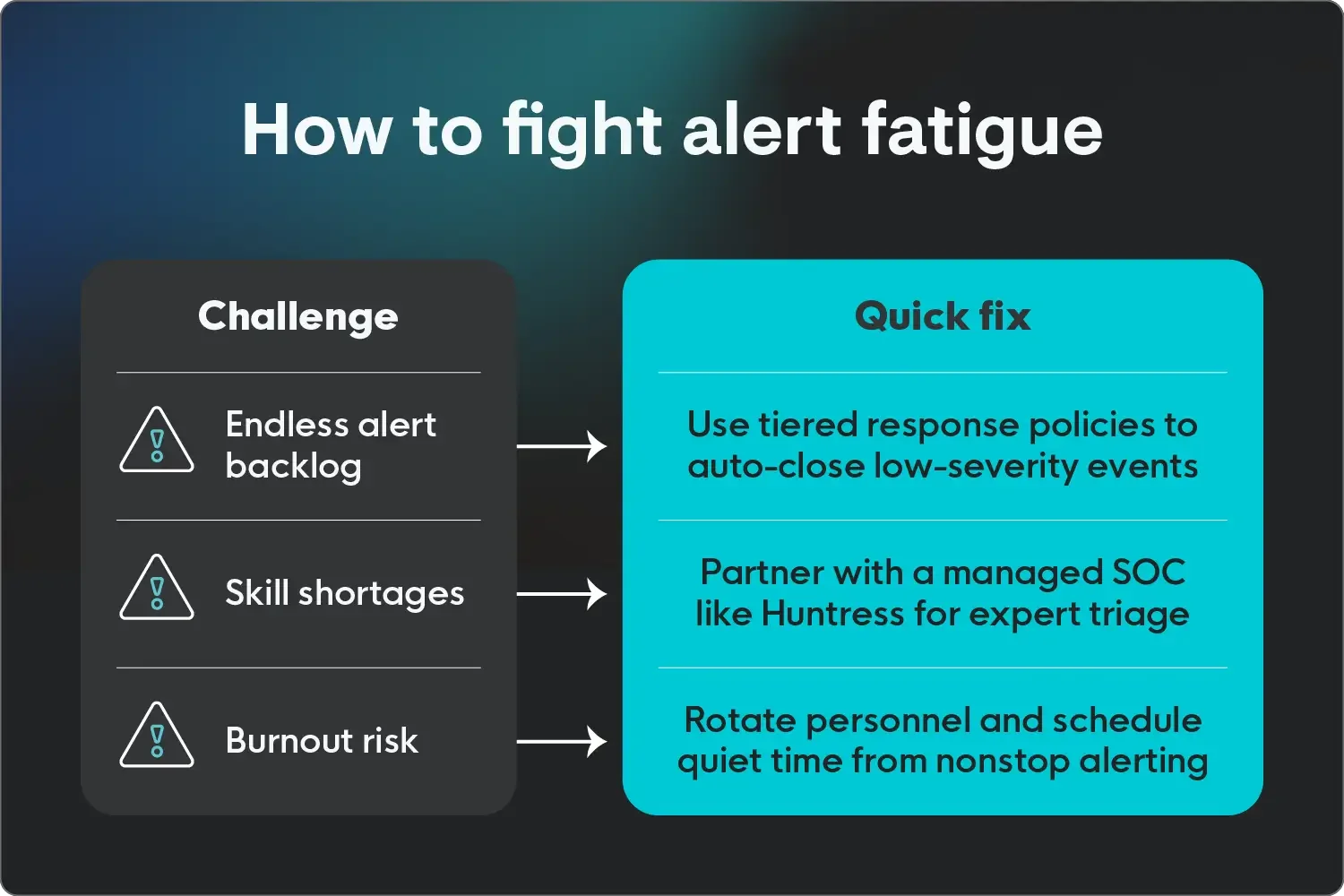
8. Prevent alert fatigue and close skill gaps
Trend: Even the best tools fail if security teams drown in alerts or lack the time to respond effectively.
Security tools can generate an overwhelming amount of data. It’s common for small or mid-sized teams to see thousands of alerts per day across EDR, email security, identity platforms, and cloud services. With a lean staff, this can lead to alert fatigue. People either tune out the noise or burn out trying to keep up.
A human-led 24/7 managed SOC like Huntress can make that data workable.
Instead of expecting your team to triage every event, you can count on security experts to investigate alerts, confirm or dismiss threats, contain and remediate threats, and provide guidance to bolster defenses when something is actually wrong.
That support closes skill gaps, reduces time-to-response, and lets your in-house team focus on projects that move the business forward instead of living in alert queues.
9. Look for stealthy living off the land (LotL) attacks
Trend: Attackers are hiding in plain sight, using your own tools to evade detection.
More attackers are skipping traditional endpoint security threats like malware and turning to LotL techniques like living off the land binaries, or LOLBins. They’re using built-in tools like PowerShell, Windows Management Instrumentation (WMI), and command-line utilities to do their dirty work.
Because these tools are part of normal Windows environments, their activity can blend in easily if you’re only watching for known malicious files or signatures.
Detecting LotL activity takes endpoint visibility plus context from a human who knows what normal looks like for your environment. That might mean actions like:
-
Flagging an unusual PowerShell script launched by a user who rarely uses the command line
-
Spotting a lateral movement tool running from a workstation that has no business doing remote admin work
These are subtle clues, but they often surface well before data is encrypted or exfiltrated. Download our LOLBins Attack Playbook to learn how to spot these attacks and shut them down.
10. Tighten security on all your IoT and OT devices
Trend: IoT and OT devices are expanding the attack surface faster than security can keep pace.
Think about smart cameras, printers, sensors, badge readers, and industrial controllers. They're all part of the endpoint landscape these days, even if they aren't running standard security agents. And your business needs endpoint protection across all of your endpoints, not just the obvious ones.
A lot of these IoT and OT devices don't have strong security built in, or they ship with insecure default settings that people rarely bother to change.
Instead of trying to run endpoint agents everywhere, isolate these devices with network segmentation so these systems have limited access to critical assets and can’t freely talk to everything else. Then, monitor the systems they communicate with using managed EDR.
That way, in IoT cybersecurity instances, you still see the lateral movement and can respond before real damage is done.
Overcome endpoint security challenges today and tomorrow with Huntress
To get better endpoint security, it’s helpful to remember the clear patterns in these trends. The businesses that stay ahead combine practical tools and processes with trusted partners who can help them respond when something slips through.
Huntress gives you fully managed EDR backed by AI-assisted 24/7 SOC analysts who understand how threat actors think and what their activity looks like in real environments.
If you’re ready to dig deeper, check out the Huntress resources in our EDR Guide to learn more about Huntress Managed EDR and how it helps you contain threats around the clock.
FAQ
What risks and threats does endpoint security protect against?
Endpoint security helps protect against:
-
Ransomware
-
Infostealers
-
Malicious scripts
-
Unauthorized remote access
-
Other threats that can lead to data loss or business disruption
It also helps you spot lateral movement and suspicious behavior before attackers reach high-value systems.
What are the primary types of endpoint security?
Common endpoint security layers include:
-
Antivirus
-
EDR
-
Host-based firewalls
-
Device control
-
Application control
-
Vulnerability management
-
Managed detection and response service
Many businesses also pair these with identity-focused tools like ITDR and security awareness training for a more complete picture of risk.
How is endpoint security different from antivirus software?
Antivirus focuses mainly on detecting and blocking known malware, often using signatures or simple heuristics.
Endpoint cybersecurity covers a wider range of protections, including behavioral monitoring, incident investigation, response actions, and long-term visibility into what’s happening on each device.
How does endpoint detection and response fit into endpoint security?
EDR is a core part of modern endpoint security because it continuously monitors endpoints, records activity, and helps detect suspicious behavior that traditional tools miss.
A managed service like Huntress Managed EDR gives you 24/7 experts who can investigate threats and guide response when something goes wrong. Talk to Huntress today to see how we can help you defend all of your endpoints.