The first episode of our _declassified series might change the way you think about cybercrime forever…and we hope it does. Because, like special guest Jim Browning said, “If there are people willing to attack you, your systems, and your business, the best way to defend yourself is to understand how they do this, who they are, and how they’re working. If you understand all of that, you’re far better able to protect yourself.”
The underground economy you can’t ignore
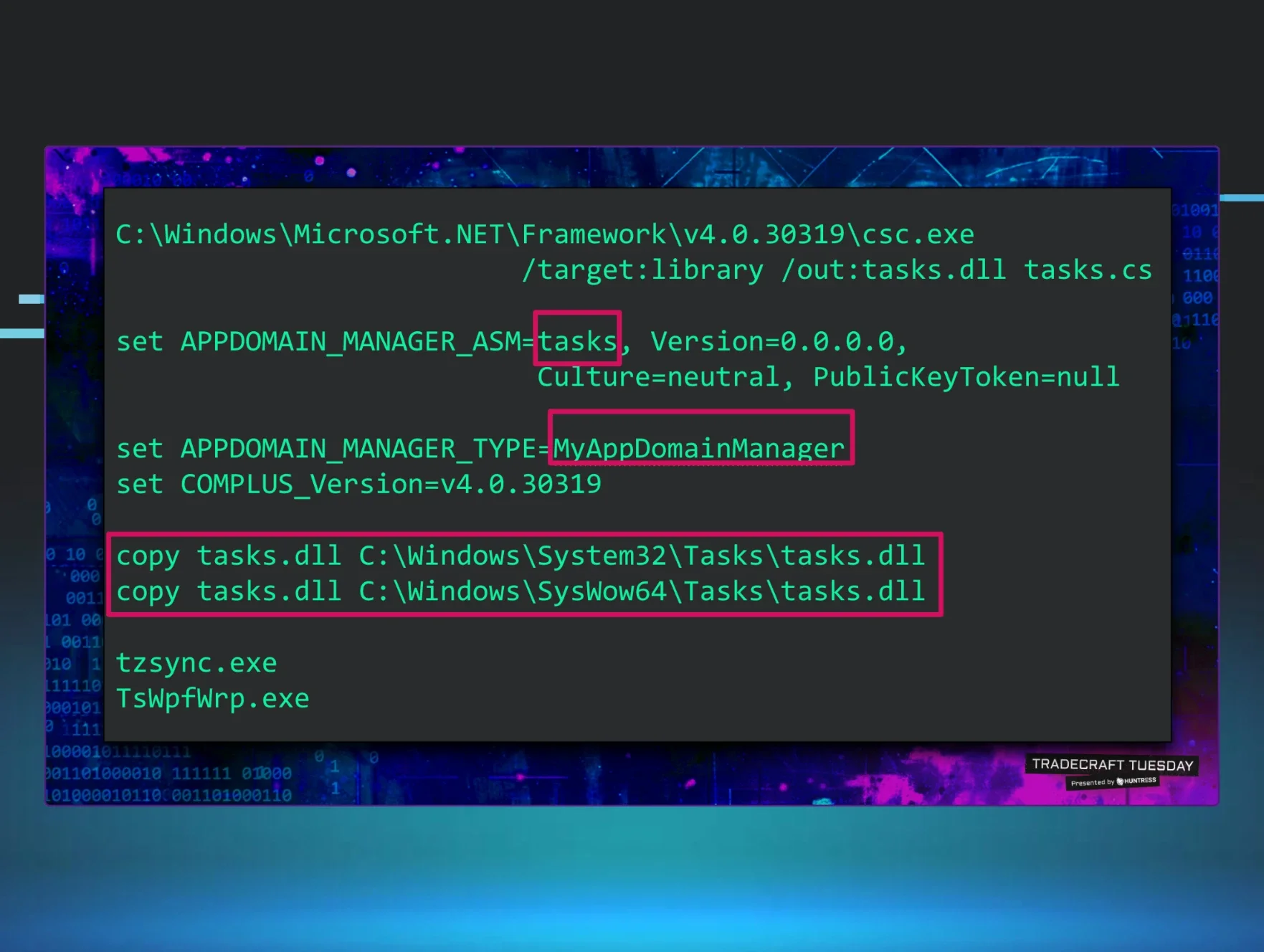
Let’s once and for all ditch the image of a lone hacker in a hoodie lurking in a basement. Cybercrime is a full-blown economy, with businesses, products, services, hierarchies, teams, and performance metrics. The people driving it are organized, methodical, and probably very rich. They’re all laser-focused on one goal: scamming for profit…at scale.
There’s no clear line between traditional cybercrime and scams. Ransomware, phishing, business email compromise (BEC), and fake tech support calls—it’s all part of the same underground economy. And the organizations behind it are your hidden competition.
Cybercrime scam centers exposed
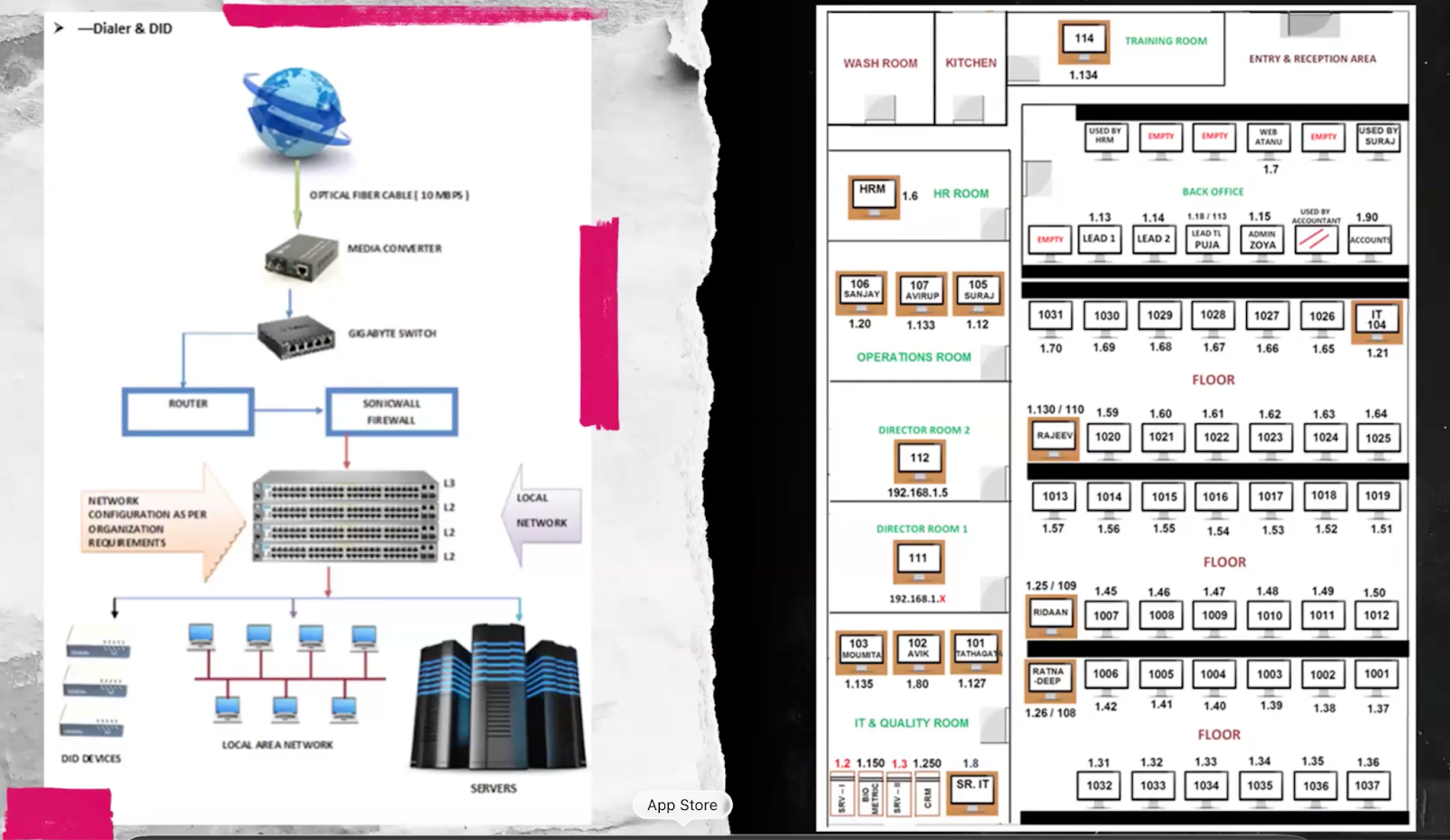
Picture a network diagram from a corporate office: training rooms, HR, operations, IT, and even a quality assurance room. Now swap the company name. This is exactly how cybercrime scam centers run. These aren’t chaotic setups—they’re engineered operations, often hiding behind legitimate businesses to drive profit and stay off the radar. In some cases, the people working the phones have been coerced or even trafficked into the cybercrime economy.
Hijacked CCTV footage captured the inner workings of their operations:
-
A fake travel agency in India is running a Microsoft tech support scam, pulling in over $3 million annually from fake virus pop-ups
-
Tech Harbor Services in Lahore, Pakistan, tricked victims with cell phone “discounts” and used promo codes to hijack accounts
-
DK Business Patron in Delhi: Amazon resellers by day, tech support scammers by night
-
A number-spoofing operation buying phone numbers just one digit off real banks, capturing misdialed calls to collect personal info, and enrolling victims in subscription scams
It gets even more hair-raising when you watch a scammer live on the phone with a victim. In Jim’s clip, someone posing as a Commonwealth Bank employee calls about a “suspicious transaction.” One listen is all it takes. This isn’t a random crime; it’s a business.

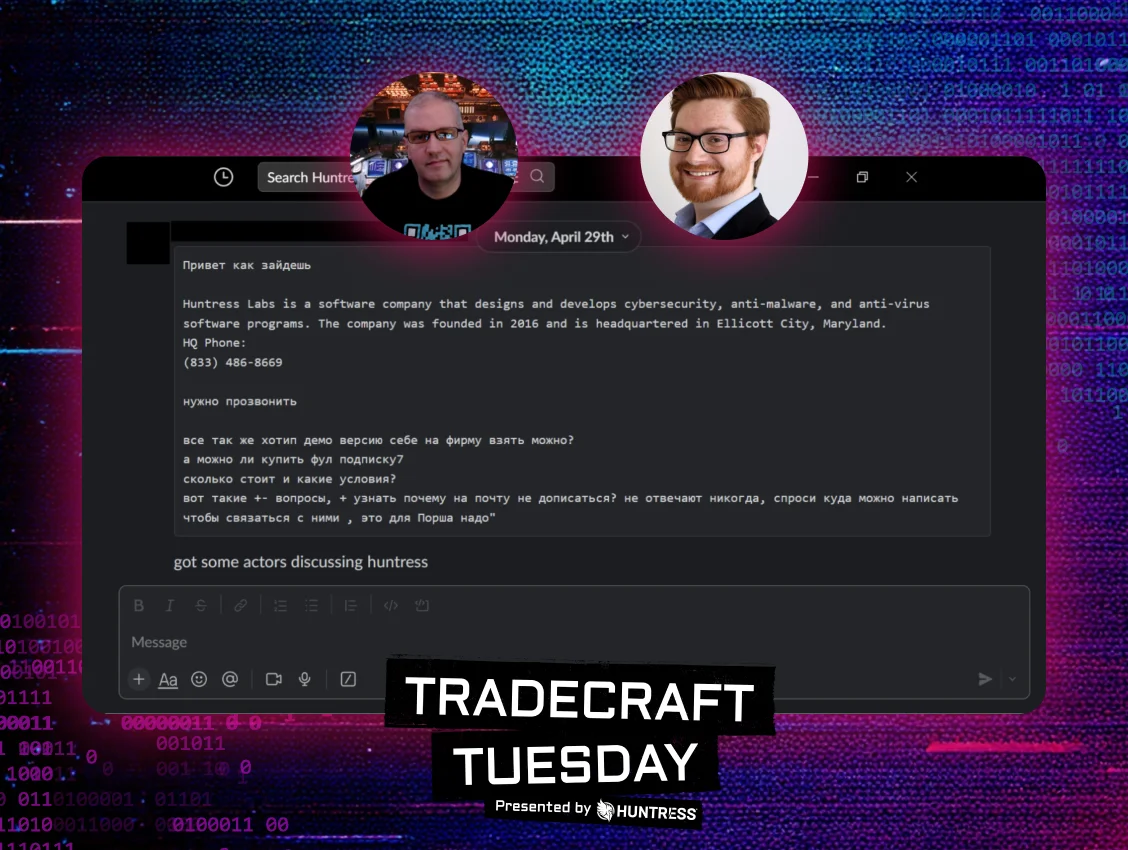
Scammers don’t just hack. They sell.
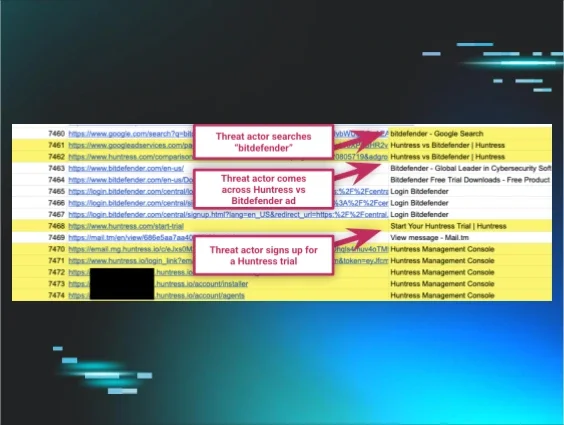
Sales operations revolve around the customer journey, even in cybercrime. Scammer agents in call centers split agents into roles. Some focus on conversion, convincing victims to send money, while others handle “retention,” reeling prior victims back in with promises to recover their losses.
If you’re still not convinced that cybercrime is an actual business, here’s a fun fact: One group Jim exposed has over 300 employees and pulled in over $20 million a year.
Embrace AI or get wrecked by it
Attackers were among the first adopters of generative AI, and they’re moving fast:
-
Fake AI-generated passports that look eerily similar to real ones
-
Deepfake Zoom calls with real-time face overlays that make scammers appear as someone else. If you’re worried about getting caught in a deepfake call, try this trick: ask them to hold up three fingers and see if the facial overlay holds up.
-
AI-powered robocalls are common, but for now, they have telltale signs like slight delays.
Jim says, “Fighting AI with AI is always a good thing.” Here are some ways that defenders are using AI to wreck cybercriminals:
-
Daisy, an AI persona from UK carrier O2, keeps scammers on the line as long as possible, wasting their time. Her line: “While they're busy talking to me, they can't be scamming you. And let's face it, I’ve got all the time in the world.”
-
For email scams, rescam.org lets you forward a scam email and keeps scammers occupied indefinitely.
Be part of the solution
Understanding these operations makes you more resilient. We need to approach defense with knowledge, not fear.
Ready to dive deeper into cybercrime? We’ve got you covered. Save your spot for the next episode of _declassified.