Mohammad "Red Bull" Muzahir believed he was heading to Laos for a legitimate IT job.
Originally covered in Andy Greenberg’s brave reporting for WIRED, Mohammad quickly found himself trapped, coerced into scamming vulnerable people out of their life savings.
What happened next exposed something far bigger than one man’s unfathomable ordeal: a vast, industrial-scale cybercrime network powered by human trafficking and forced labor.
Listen to Mohammad tell his story to understand the human cost behind enterprise-level cybercrime.
What are "pig butchering" scams?
Pig butchering scams are romance-based cryptocurrency fraud schemes where victims are "fattened up" with affection and trust, then "butchered" when scammers convince them to invest their life savings into fake cryptocurrency platforms.
As Greenberg notes, these scams have become the largest type of cybercrime in the world, stealing tens of billions of dollars annually.
But the story gets a lot darker: the scammers themselves are often victims, trapped in compounds across Southeast Asia, and forced to run shady fraud scams under threat of violence.
A borderless crisis of global proportions
The situation Mohammad was forced into wasn’t an isolated operation. It was an organized, corporate-like machine built to exploit people.
To illustrate the scale, the compound Mohammad “lived” in had roughly 100 people on the same floor. There were multiple floors in his building, multiple buildings in his compound, and multiple compounds in the Golden Triangle, the special economic zone in Southeast Asia, historically known for illicit activities and trafficking. Similar operations exist across Cambodia, Myanmar, and increasingly around the world.
Estimates suggest hundreds of thousands of people are trapped in these modern trafficking operations globally. The scale is staggering.
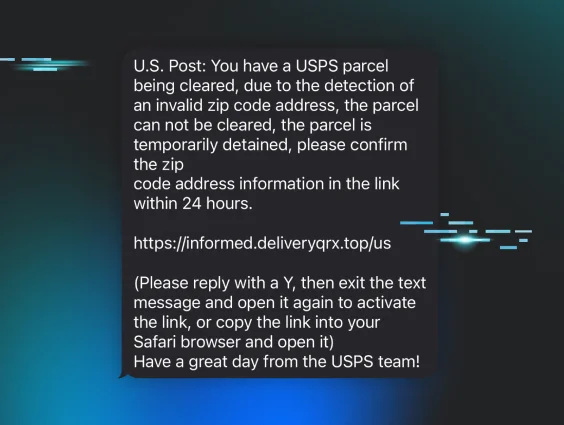
The deception playbook
Mohammad was forced to use the following psychological manipulation tactics against the victims.
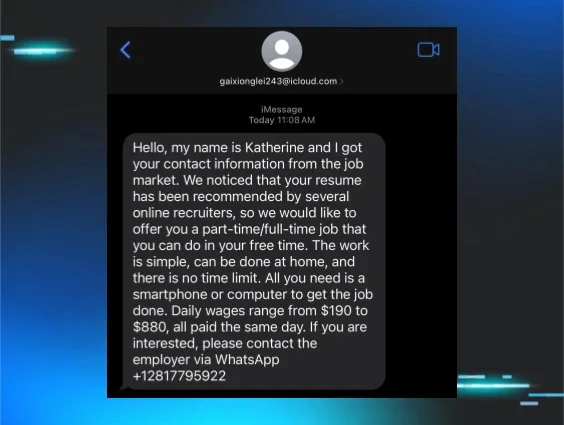
Building trust through routine
Scammers sent daily messages to create familiarity: “good morning” texts, breakfast photos, real-time selfies, and voice notes. These messages were designed to make scammers feel like a natural part of the victims' daily lives. Routine creates familiarity, and familiarity creates trust.
Creating emotional bonds
After trust with the victims was solidified, scammers shared dreams and future plans. They talked about financial freedom and building something together to make victims feel connected.
Pre-positioning
Before asking for money, scammers mentioned their own banking "problems" as a reverse psychology tactic. This encouraged victims to ignore warning signs, since a scammer likely wouldn’t be warning about scams.
Maintaining the illusion
Fake daily schedules made scammers seem like real people with busy lives. And the level of detail was staggering. If you mentioned food, you needed a photo. If you mentioned a car, you needed evidence. Supervisors trained workers to have answers for everything, creating identities so convincing that victims never suspected the elaborate machinery behind every message.
Tech advantages
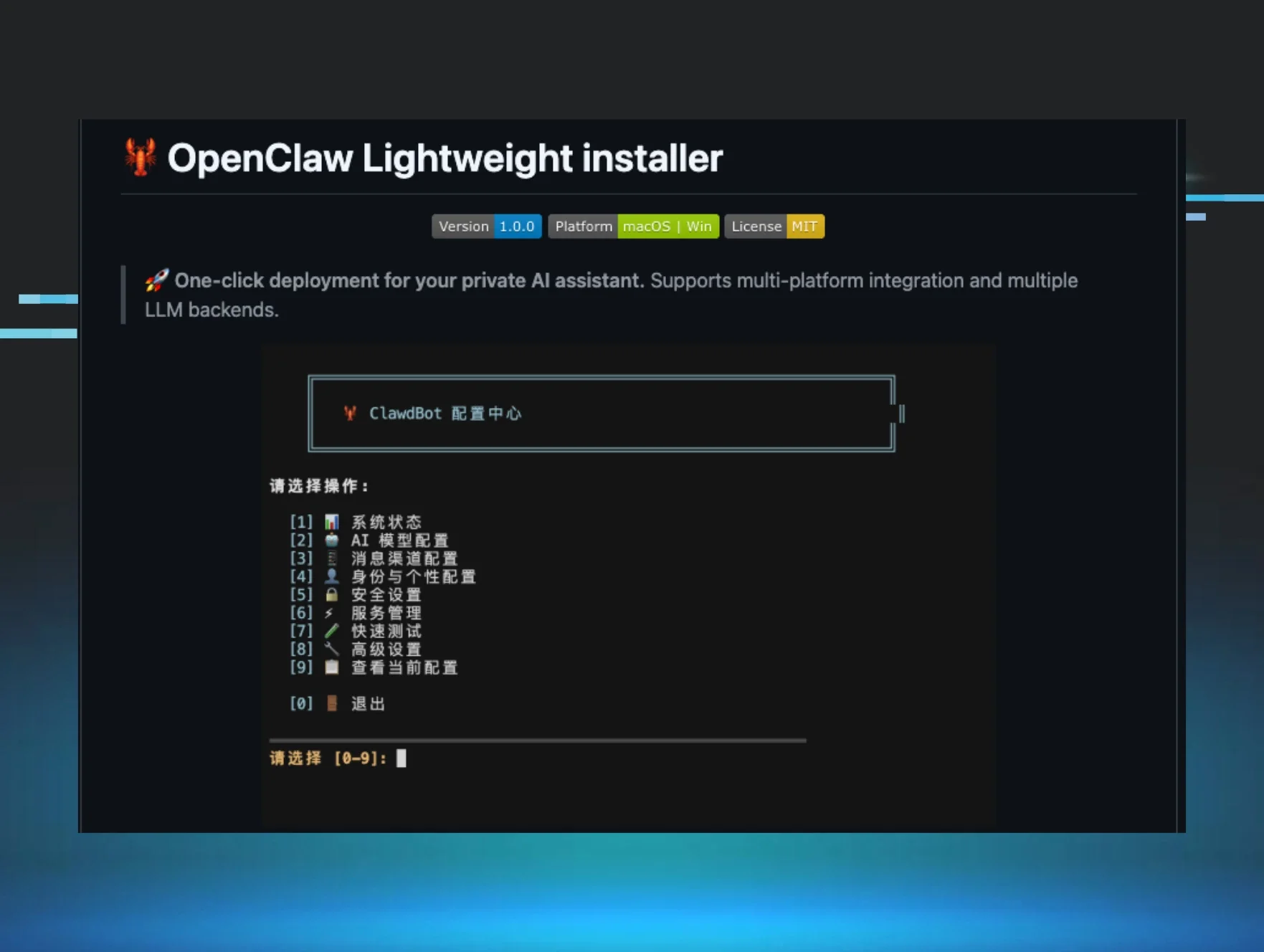
Large language models (LLMs) fueled conversations with victims, helping scammers fabricate endless conversations and build rapport. AI-generated images and deepfake technology also optimized fake personas.
What didn’t work
Some scams fell apart when:
-
Victims brought friends or family into financial decisions
-
Someone reverse-image searched photos using Google Lens
-
Targets asked too many questions about platform switches
-
People refused to send the first payment
The entire system depended on three things: speed, secrecy, and the first payment. If any of these broke down, the scam stumbled.
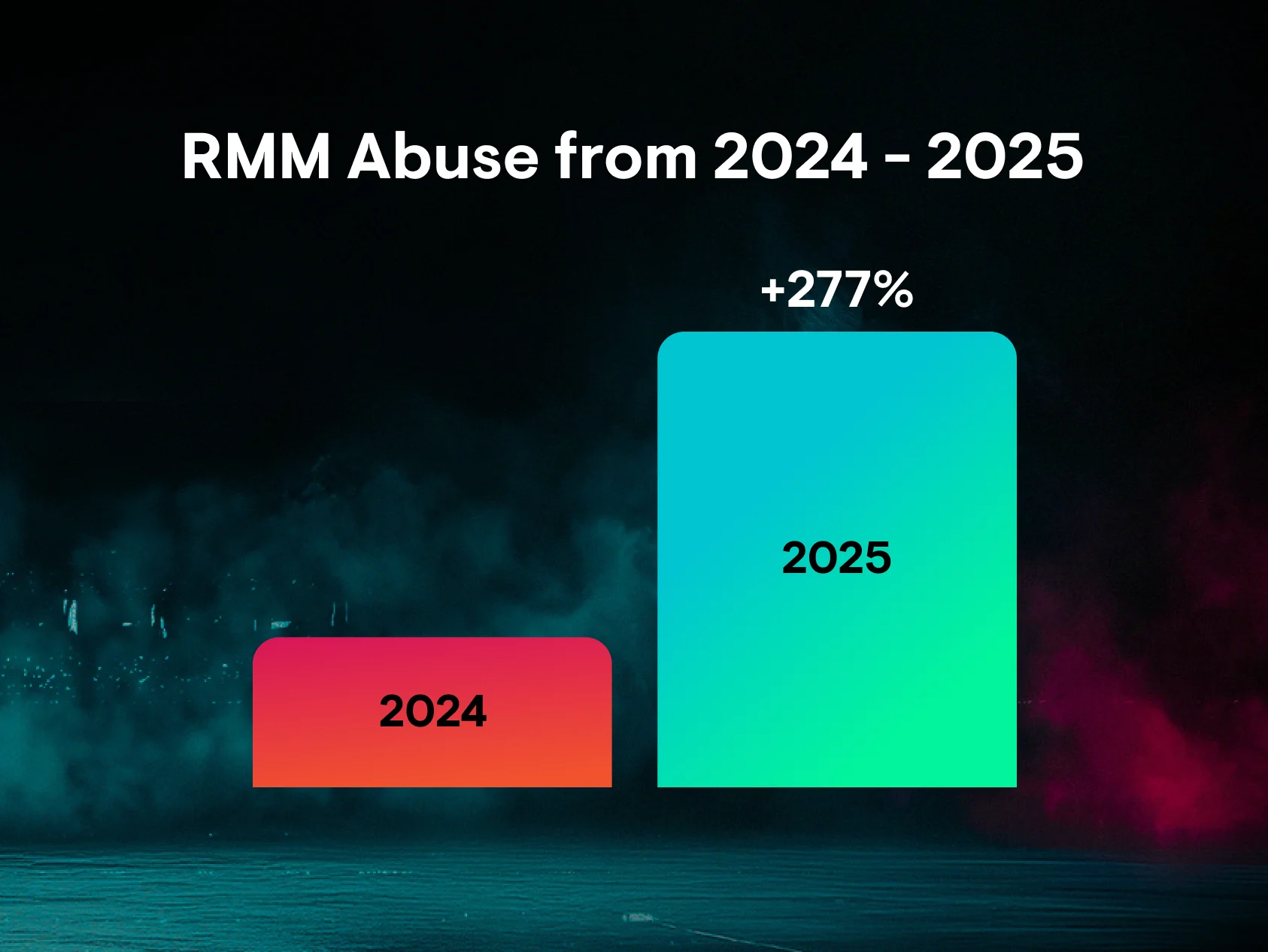
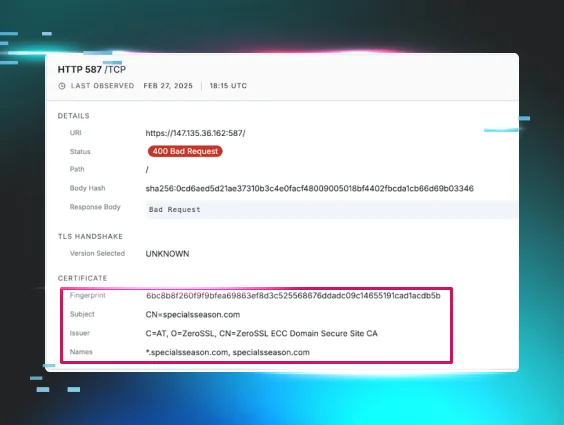
The infrastructure behind the scams
A complex web of infrastructure supports corporate-like cybercrime:
Communication networks: Encrypted messaging platforms for rapid, global coordination. Training materials, victim data, and operational instructions flow through these channels with zero friction.
Money movement: Cryptocurrency moves across borders instantaneously, without the delays and verifications of traditional banking
Support services: Black markets sell accounts, manage money-laundering systems, and harbor illegal transactions
How you can protect yourself, family, and friends
Mohammad's message is clear: these scams work because they target hope, loneliness, ambition, and financial pressure. Getting scammed can happen to anyone.
Here’s how you and your family can stay safe from online scammers:
-
Slow down. The entire system relies on speed. Take time to think through any financial decision involving someone you've only met online.
-
Break the secrecy. Talk to friends or family (or other trusted confidantes) before sending money. Emotional manipulation often slows down when you involve trusted people in decisions.
-
Never send that first payment. Escalation is easy once scammers get the first payment. That’s where the real danger begins.
-
Use reverse image searches. Run photos through Google Lens or other tools to check if they appear elsewhere online.
-
Ask questions. If someone wants you to switch communication platforms, ask why. If investment opportunities sound too good to be true, they probably are.
How you can help the greater cause
After hearing Mohammad's story, you might be asking yourself, “What can I do now?”
Here are a few meaningful next steps you can take to support survivors like Mohammad:
- Support trusted anti-trafficking organizations: Consider donating to vetted nonprofits that are actively helping trafficking victims escape, recover, and rebuild their lives.
- Nomi Network: dedicated to empowering survivors affected by trafficking and educating the public on the connection between scams and human exploitation
- Operation Shamrock: mission is to educate the public and mobilize law enforcement, business, and government action to disrupt the scam industry
- Transparentem: works to expose and prevent forced and coerced labor across global supply chains, not only in illicit industries, but within legitimate, everyday business operations.
- Help amplify accurate reporting: Andy Greenberg’s in‑depth reporting on Mohammad and these scam compounds has helped bring this story into the light. Sharing credible journalism like this is one way to increase pressure on the people and systems enabling these crimes.
- Educate and protect your own community: Share the on‑demand recording of this session with colleagues, friends, or family who might be targeted by similar scams, and talk openly about the red flags and patterns you heard described.
What does it take to break the machine?
It starts with awareness.
When more people understand how online threats actually work, the system starts to crumble. Not overnight, but gradually.
Security awareness training (SAT) is one way awareness spreads. When someone learns about online risks at work, that knowledge travels home. They share it with parents, children, and friends, widening the circle of people who can spot manipulation, verify opportunities, question urgency, and safeguard sensitive information.
Ultimately, the tide turns when exploitation isn’t just exposed, but stops being a cash flow for criminals.