In a rare encounter, we found ourselves directly interacting with a cybercriminal that took us down a dark web rabbit hole. But before we dive in, here's where this story stands.
The Latest Scoop as of February 10, 2020
The Huntress team recently learned that a person allegedly tied to the w0zniak account has been arrested in Atlanta. We received this information shortly after we released our blog and here are a few key updates:
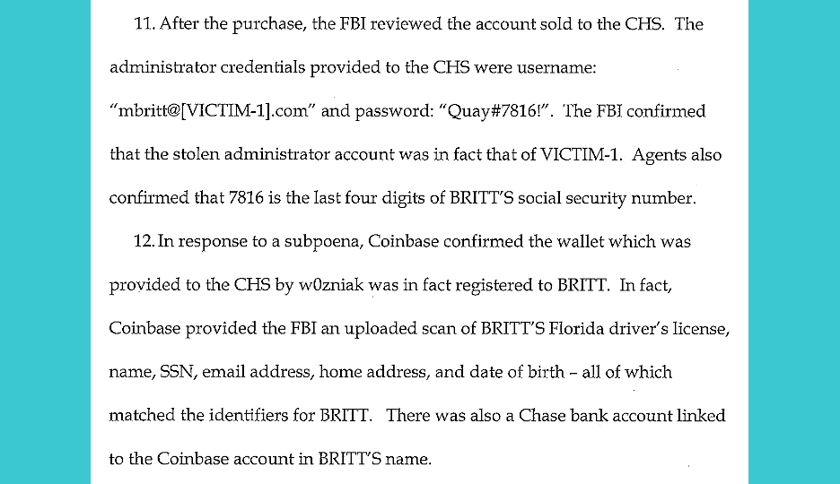
Insider threat: w0zniak was a disgruntled ex-employee of the MSP
Based on the criminal complaint affidavit, w0zniak is likely the Torum handle belonging to Marquavious Britt, who worked for our victim MSP until he was “terminated for failure to complete tasks assigned to him.”
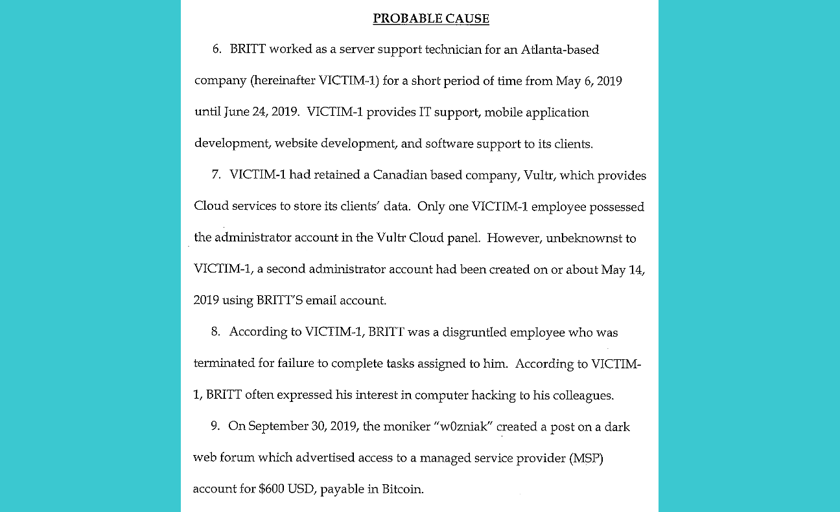
What’s especially interesting is the Vultr account sold by w0zniak belonged to Marquavious Britt and included the last four of Britt’s SSN in the password. Additionally, the Coinbase account that received payment for the MSP access was registered to Britt’s name, SSN, address, and date of birth. Sounds like:
- w0zniak didn’t have the greatest online OPSEC
- MSPs need to closely audit admin accounts after employees depart
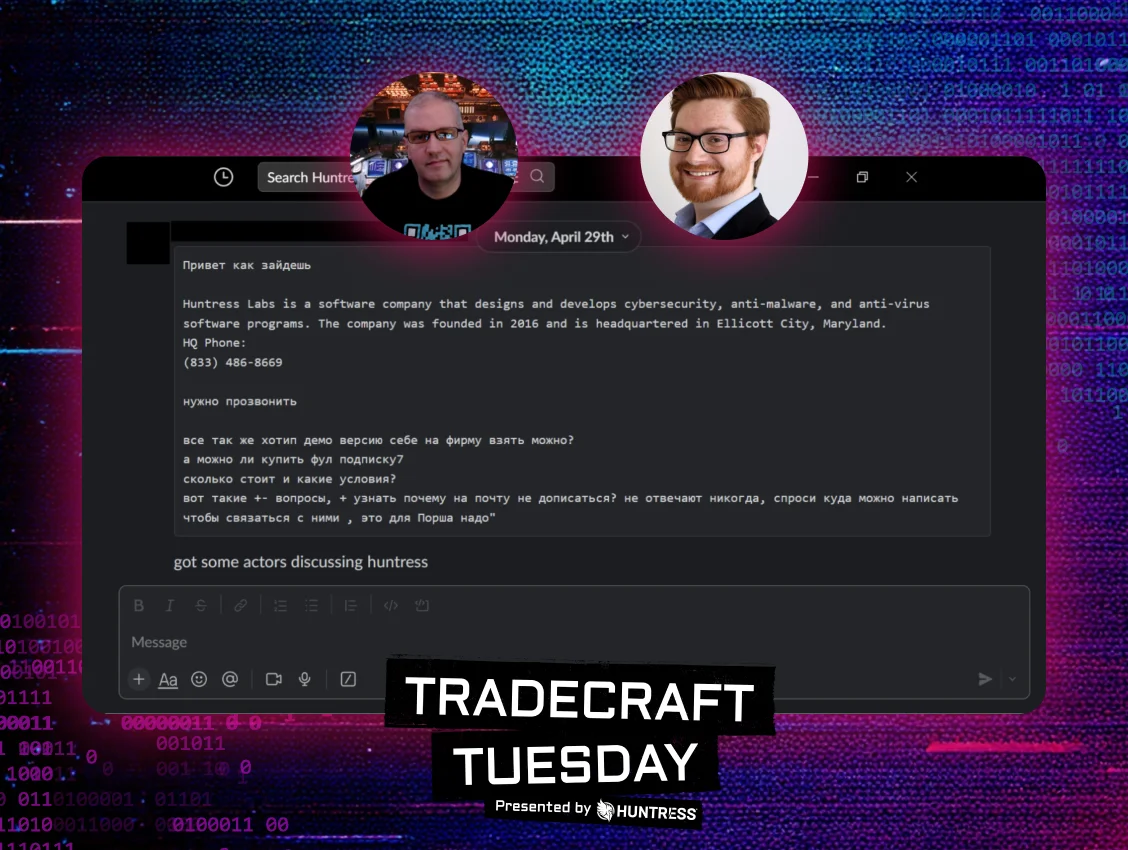
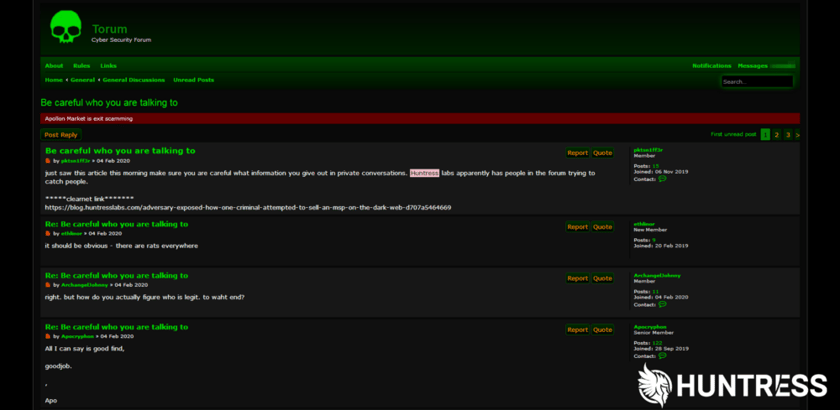
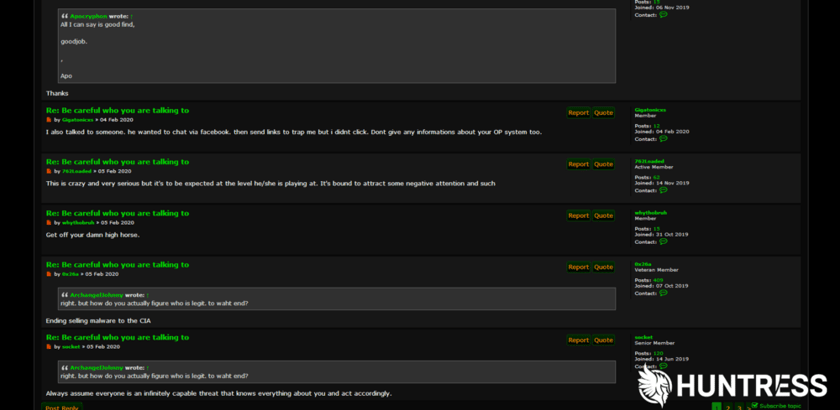
Some Dark Web hackers are not super thrilled with our effort
Since our story was published, we’ve seen hackers warn each other about who they talk to and what they see. They are on high alert, knowing their shady deeds are being watched.
Security will always be a cat and mouse game, but that game doesn’t have to be checkers. Playing chess probably starts with an offensive approach to defense.
If Britt is responsible, w0zniak is a man
While we wrote this blog, we definitely had fun imagining our hacker as a woman. It was an interesting thought exercise that challenged us to remove our preconceived notions. However, not everyone agreed with our decision.
At the end of the day, we are just relieved to see one more criminal is receiving their day in court. MSPs are increasingly vulnerable to hackers on the Dark Web. This blog was just another example of our commitment to protecting MSPs to keep them safe.
• • •
Original Post from February 4, 2020
Think about all the things you can buy and do on the dark web.
Most of what you see on the dark web stems from the fact that it is powered by anonymity. While there is certainly an argument for freedom of expression that drives part of the dark web, most of what we see and hear are nefarious activities of hacktivists and a growing organized cybercrime underworld. But we often hear about the events after their criminal activity has already run its course.
In a rare encounter, we found ourselves directly interacting with one of these cybercriminals. Read on to see how our very own Kyle Hanslovan, Chris Bisnett, and John Ferrell took a deep dive into the dark web with a first-hand encounter with an attacker.
The Sale of the Day
Back in October, Datto identified a threat actor through their routine dark web monitoring practices. This cybercriminal, known by her Torum handle as “w0zniak”, was seen selling access to an MSP’s VPS control panel on the dark web for $600 BTC.
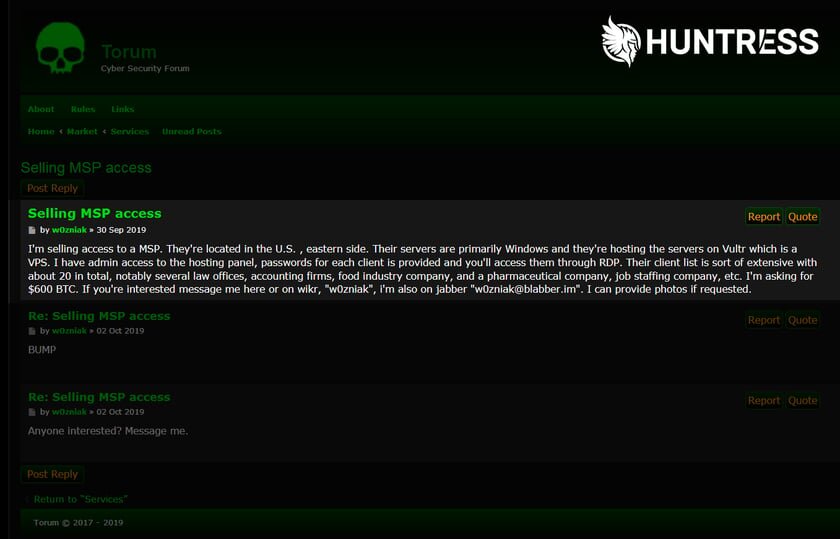
“I’m selling access to a MSP. They’re located in the U.S. , eastern side…… I’m asking for $600 BTC. If you’re interested message me here or on wikr… i’m also on jabber. […] I can provide photos if requested.”
We’re looking at a businesswoman at work. She’s laying out her terms — establishing price, contact information, and evidence to build trust. But what type of businesswoman is she? What are her motivations? Is it all about just a quick payout, or is there more to her plans?
Of course, the primary goal was to identify and help the victimized member of our community. But as crazy curious cyber defenders, our secondary goal was to get a better understanding of who we were dealing with so we could “know our attacker”. It’s not every day where we have the opportunity to talk directly to a cybercriminal. This was our chance to learn more about her motivations and tactics.
Background
Let’s rewind for a second just to see how we got to this point.
We’ve always believed in the power of collaboration, and we certainly are not alone. Back in July 2019, our very own VP of ThreatOps, John Ferrell, and the CISO of Datto, Ryan Weeks, got together to brainstorm ways to better secure our communities. This conversation quickly expanded to both our Huntress ThreatOps team and Datto’s security team, resulting in the creation of a Slack channel to facilitate collaboration. Evolving into the very first grassroots MSP-ISAC, we had established an avenue for vendors in the MSP community to share what we’ve seen and collaborate together.
What all of our community members have learned through combined decades in security is that intel sharing is one of the best and most effective ways for all of us to stay ahead of the attackers.
This story is a perfect example of a team effort. And the biggest takeaway is working together allows us to not just find and resolve threats, but to identify new behavior patterns and methods of cybercriminals. In the end, this makes us all better at protecting ourselves and each other against a potentially new type of adversary.
Reconnaissance
Okay, enough with the high fives; let’s get back to the story.
Datto, one of the founding members of the MSP-ISAC, came across the Torum post shared above and showed it to the rest of the MSP-ISAC. Given our background in cyber operations at the NSA, seeing this perked up our ears motivating us to go all in to thwart this attacker.
We started doing some snooping, watched subsequent posts, and it became evident that our adversary is a person who is looking for ways to grow and develop her business. This next post makes it clear that she’s mastered how to compromise IT departments and managed service providers, but wants to build a team to help with encryption.
In fact, she turned down someone who offered to work with her because she wanted someone that is willing to work on a longer-term strategy. This is a person who is all about the ring on their finger, not just a one-time fling.

“Thanks for the offer but I’m looking more for a partner or partners who want to work long time and make money.”
Engaging Our Adversary
We knew it was imperative that we sound credible in order to get the attacker to talk. So we zipped up our black hoodies and threw ourselves into a tactical negotiation.
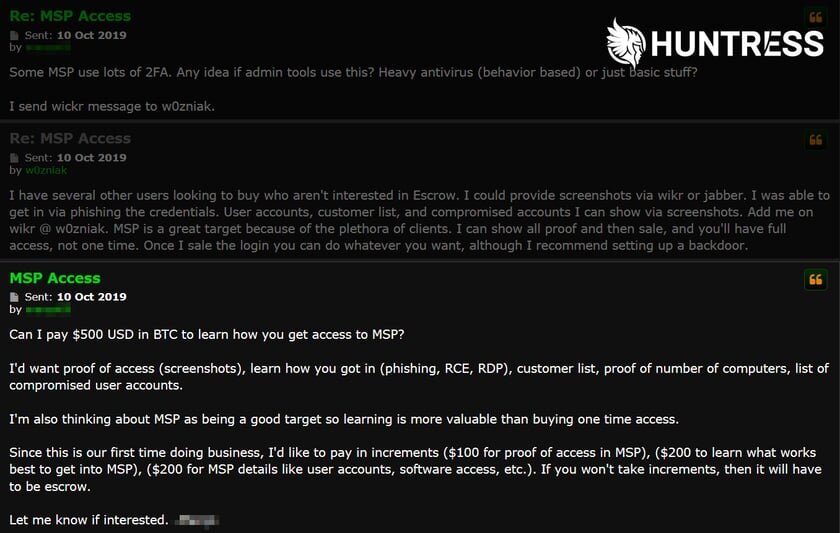
Our bogus offer:
- Proof of access with all the info upfront — We absolutely had no intention of paying, but was it still possible to extract clues that would lead us back to either our victim MSP or one of their clients without handing over a single dime?
- Down to $500 BTC, but we wanted to learn how to get access — not just get access by itself. Remember, our secondary goal is to actually understand more about our adversary.
- And lastly, the payment terms of the deal.
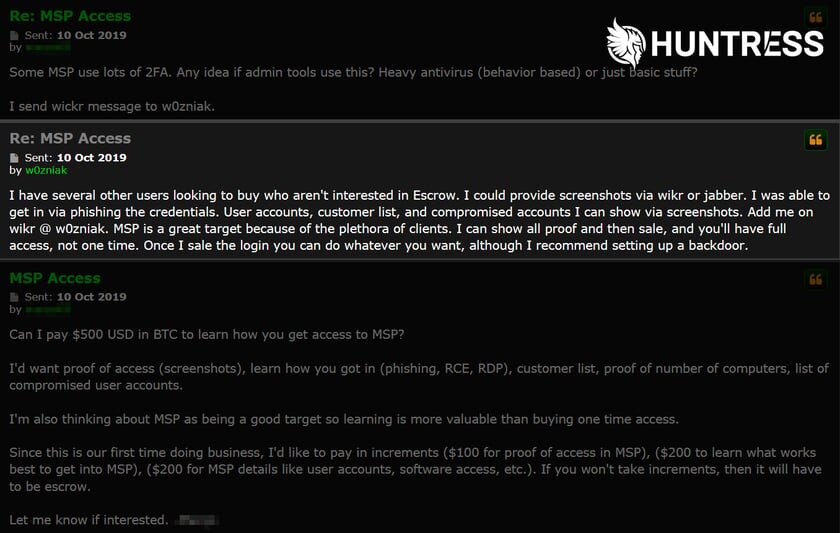
Success—she responded! And more importantly, we’re drawing her in to give us some important details.
“I was able to get in via phishing the credentials. User accounts, customer list, and compromised accounts I can show via screenshots…. MSP is a great target because of the plethora of clients.”
Private Conversations
It worked! We were DM’ing with her on Wickr, pretending to flush out the business arrangement. Our intention was to craft our responses convincingly so that she’d give us enough details to eventually identify the targeted MSP as soon as possible so they could start remediation.
She sent us a screenshot of what she had compromised. Wickr would have notified w0zniak if we took an “in-app” screenshot, so we resorted to the next best thing — a picture of our phone. 😉
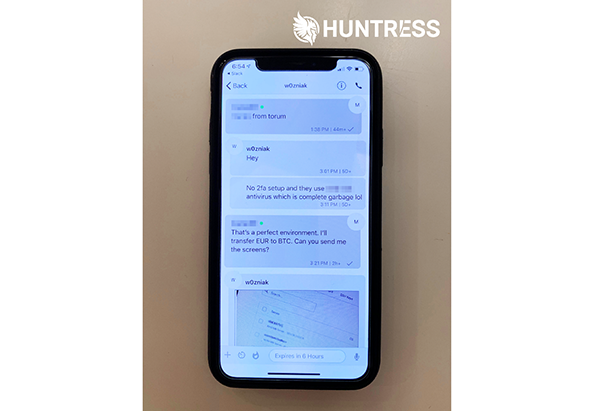
Another parlor trick? There is evidence that indicates many cybercriminals or sellers on the dark web won’t even sell their goods to US buyers. So to keep up with the facade, we said we’d “transfer EUR to BTC” to make it sound as though we were based out of the country. 😎
Finding and Helping Our Friends
We took a closer look at these screenshots and the first thing we saw were the names and IP addresses of servers being managed by this MSP.
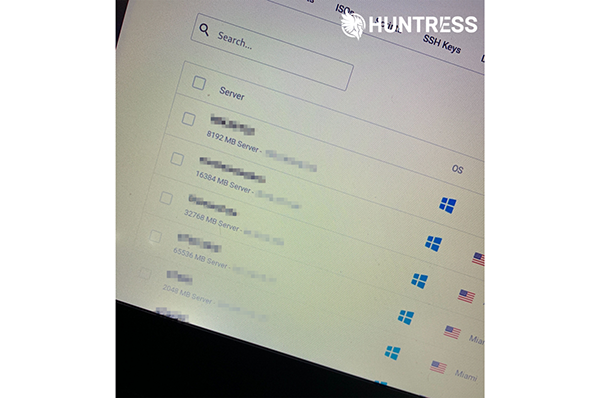
We started ‘dig’ging through DNS records and looking at WHOIS information to help us find domain registrations, AS numbers — anything that would help us trace back to the MSP or even one of their customers. Commonalities in all of this information started to emerge, giving us confidence that we had found the MSP we were looking for.
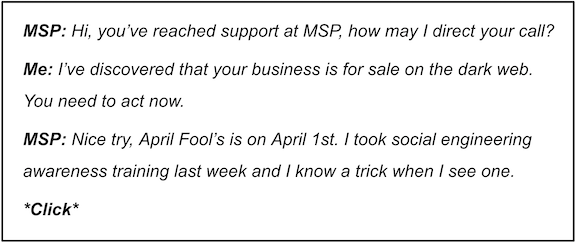
With the name of the victim MSP in hand, it was now time to get a hold of them. An email or phone call seemed like an obvious next step, but this turned out to be a much harder challenge than we had anticipated.
We imagined how this call would go down:
A Successful Partnership
So we sat there, heads in our hands, trying to figure out what we should do. We urgently needed to get a hold of this MSP. Eventually, FQDNs and registrars from our mountain of research started staring back at us until we finally realized — some hostnames actually contained names strongly hinting that our MSP was, in fact, a ConnectWise customer.
Using our ISAC community, we reached out for extra help. Through our community, we contacted John Ford, former CISO of ConnectWise, who helped us confirm that the MSP was indeed a ConnectWise partner. John used his business relationships to contact this MSP, passing along all the details of what we found so they could expel the hacker, protect their clients, and harden their internal network.
We couldn’t have been happier about the outcome. Reflecting on this story, it perfectly highlights how close collaboration and threat intel sharing, even between competitive vendors, can be used to go head-to-head against hackers. Putting our egos aside and succeeding at a common goal is something we can all be extremely proud of.
A Message From Our Hacker
The reality is, this story is already becoming part of a new normal. Since these events have happened, our attacker, w0zniak, has already struck again.
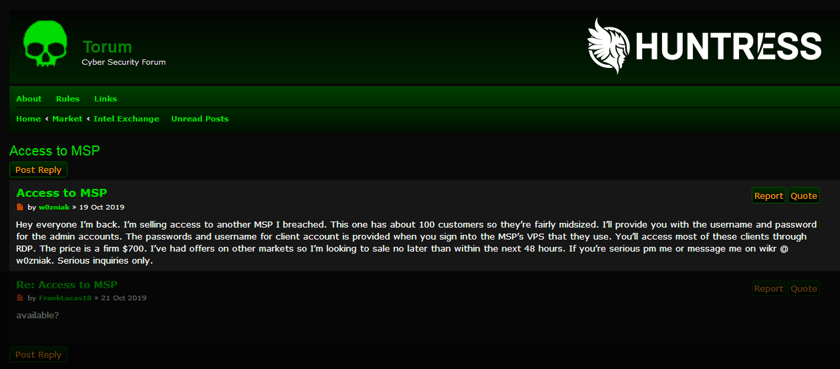
The truth is this follow-up message is not a surprise after seeing the original events. Attackers will continue discovering new victims, new markets, and new ways to succeed in their dirty business.
What we need to take away from this is confirmation of the essential defenses that we absolutely need to put in place in order to protect our networks and our users. We’ve heard the same story from vendors, security magazines, certification providers, etc: apply multi-factor authentication, do not expose RDP externally, watch out for phishing, the list goes on. But now, we are hearing it directly from our attacker.
I’ll provide you with the username and password for the admin accounts. The passwords and username for client account is provided … You’ll access most of these clients through RDP.
There is no better confirmation supporting these defenses than from the source.
Sharing is Caring
While we do our best to avoid them, we each have our own unique encounters with these attackers. And because we’re always seeing new attacker behavior, sharing these encounters is exceedingly important. It helps us stay together as a community to corroborate events, warn others of what we’ve seen, and enrich everyone.
As always, we will stand by our commitment to sharing what we see and find ways to improve our community. And as long as hackers keep hacking, we will always keep hunting.
Want to read more Huntress threat analysis? Check out these blogs:
- Bullseye: A Story of a Targeted Cyberattack
- Snakes on a Domain: An Analysis of a Python Malware Loader
- Discovering a Ransomware Remedy in the Wild
Editorial Note
Huntress purposefully personified this hacker as a business-savvy woman of (offensive) cybersecurity. The truth is, we actually don’t know the identity or gender of the attacker. We personified this hacker as a woman for the sheer fact that there’s not enough representation of women in the cybersecurity industry and that there are equally capable cybercriminals out there that are women.