Introduction
Threat actors are not slowing down. We’ve seen how initial access through VPNs, RDP, and web app abuse is allowing attackers to land on endpoints faster and with little friction. Once they’ve landed, they quickly apply their tradecraft—getting situational awareness about the endpoint, downloading and executing their preferred tools, establishing persistence, elevating privileges, and working to achieve their objectives.
Key takeaways
Threat actors can move faster than endpoint detection and response (EDR) tools when attacking endpoints, like ‘land and encrypt’ ransomware.
Creating friction while threat actors are employing their tradecraft and deploying tools buys time for defenders to investigate and respond.
Huntress Managed EDR solves the attack speed versus detection gap with the Attack Disruption Engine.
The challenge
There are threat actors that are purposely moving very fast these days, taking advantage of gaps in how EDR tools work, like the time between collecting endpoint telemetry and machine and human analysis.
In 2025, the Huntress Security Operations Center (SOC) and threat hunters saw endpoint attacks, like ransomware, where the attacker knew it was a race between being detected and deploying their payload—the "land and encrypt" approach. These types of ransomware attacks happen in under 15 minutes! Our SOC analysts have even detected ransomware attacks that took less than five minutes.
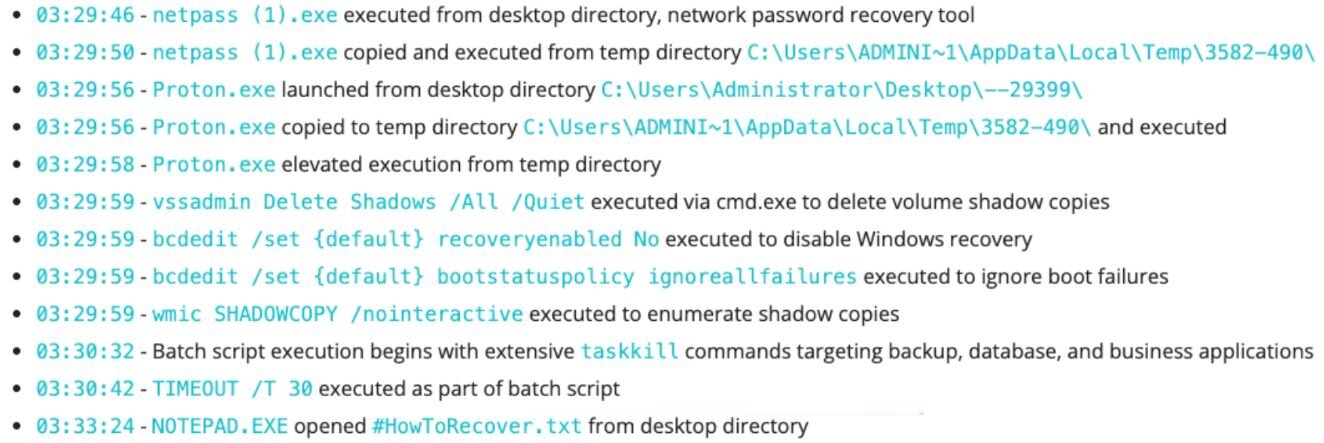
Figure 1: Timeline of events where Proton ransomware was deployed
Enter Attack Disruption
We’re excited to announce the Attack Disruption Engine in Managed EDR. Its development is an example of the threat expertise Huntress brings to our customers and how Huntress builds with a purpose in mind, not just chasing features for the sake of adding more features. The concept started with our Windows EDR Product Researcher, Jonathan Johnson (if you saw October 2025 The Product Lab, this is the micro engine he mentioned).
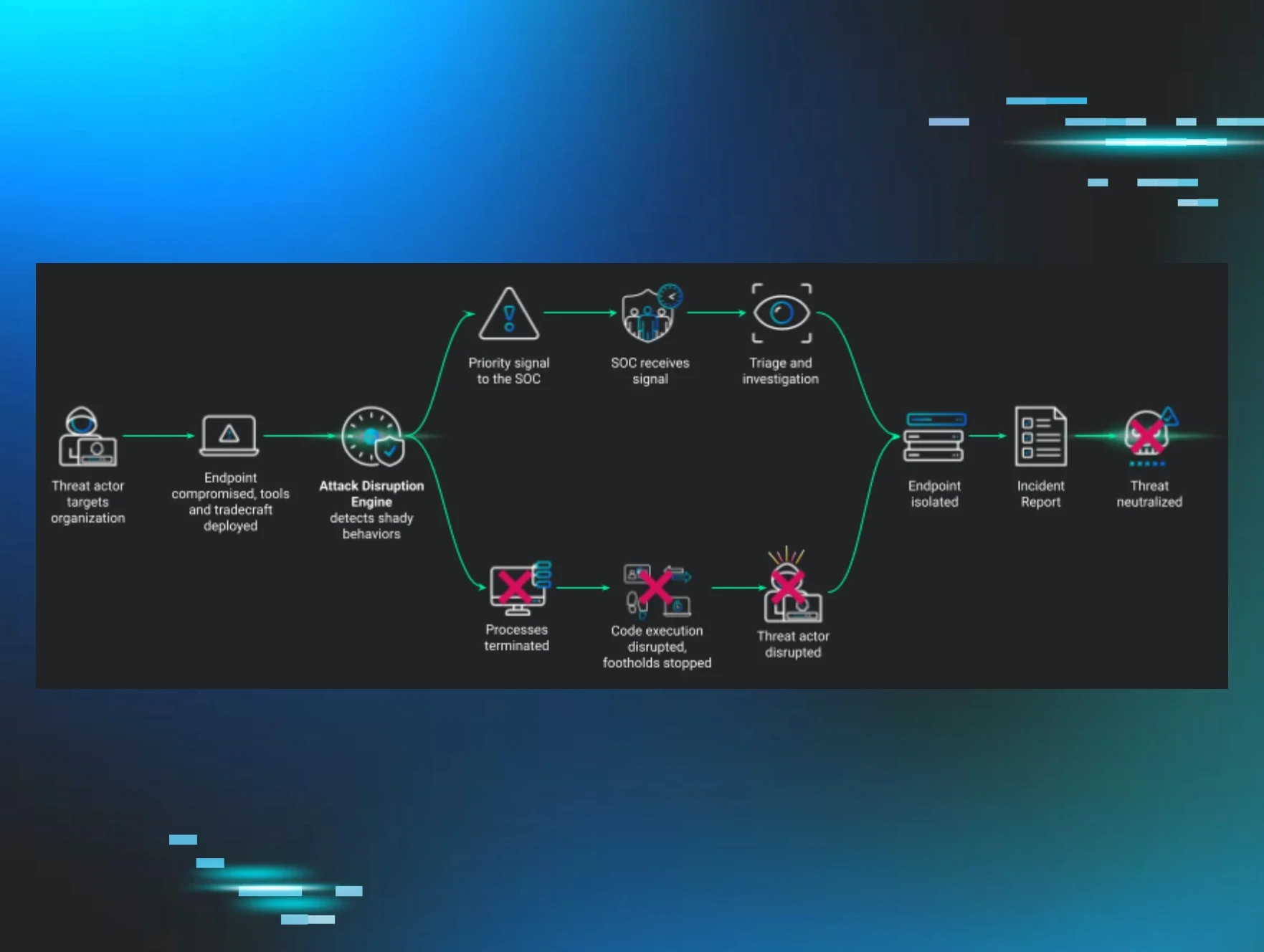
How Attack Disruption works
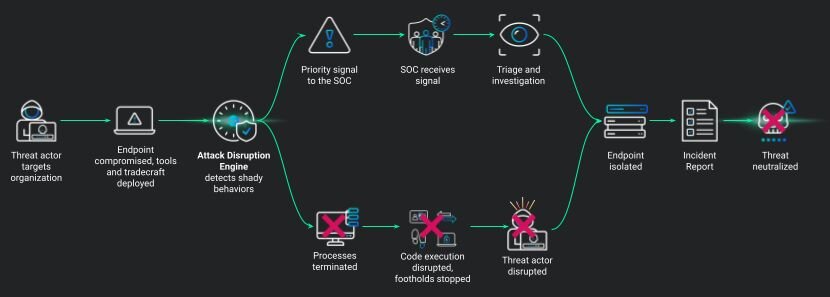
The Engine is integrated into our EDR agent, running locally on the endpoint, so it reduces the gap between telemetry collection, delivery, and analysis. We built the Engine to adhere to our Managed EDR tenants—it must be lightweight, does not impact endpoint performance and the user experience, it needs to catch really shady activity, and adapt as hacker tradecraft and tooling evolves.
The Attack Disruption Engine monitors endpoint activity in real-time, and when it sees anomalous attacker behavior, it immediately takes disruptive action:killing malicious processes, stopping malicious code execution, and preventing the threat actor from establishing footholds. Simultaneously, it generates an accelerated alert to our SOC to bring humans into the loop. Our goal was to slow down an attack and create friction for the attacker that, in the best case they give up and move on to another target, and where they keep persisting, gives our SOC time to jump in, triage, and respond.
Figure 2: How Attack Disruption works in Huntress Managed EDR
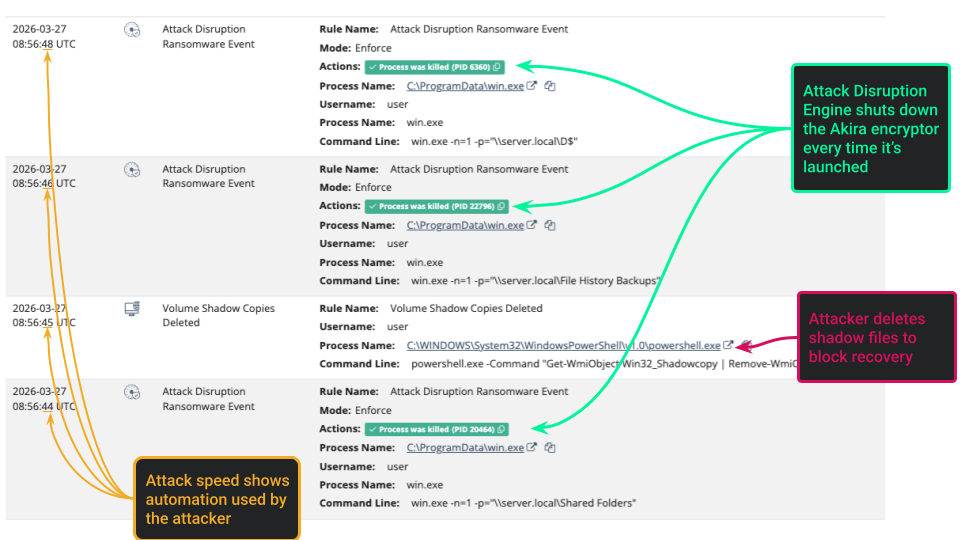
Wrecking Akira ransomware
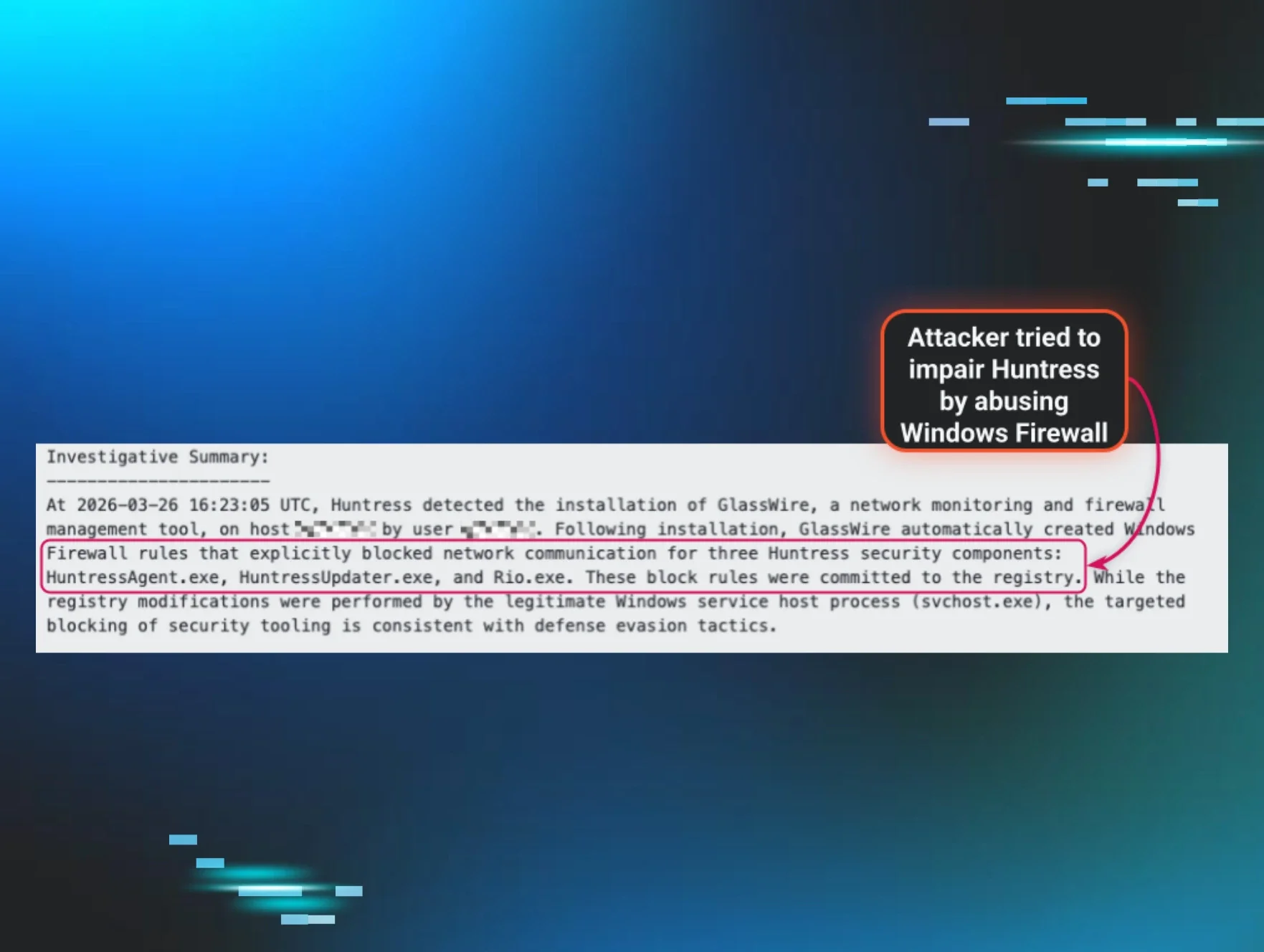
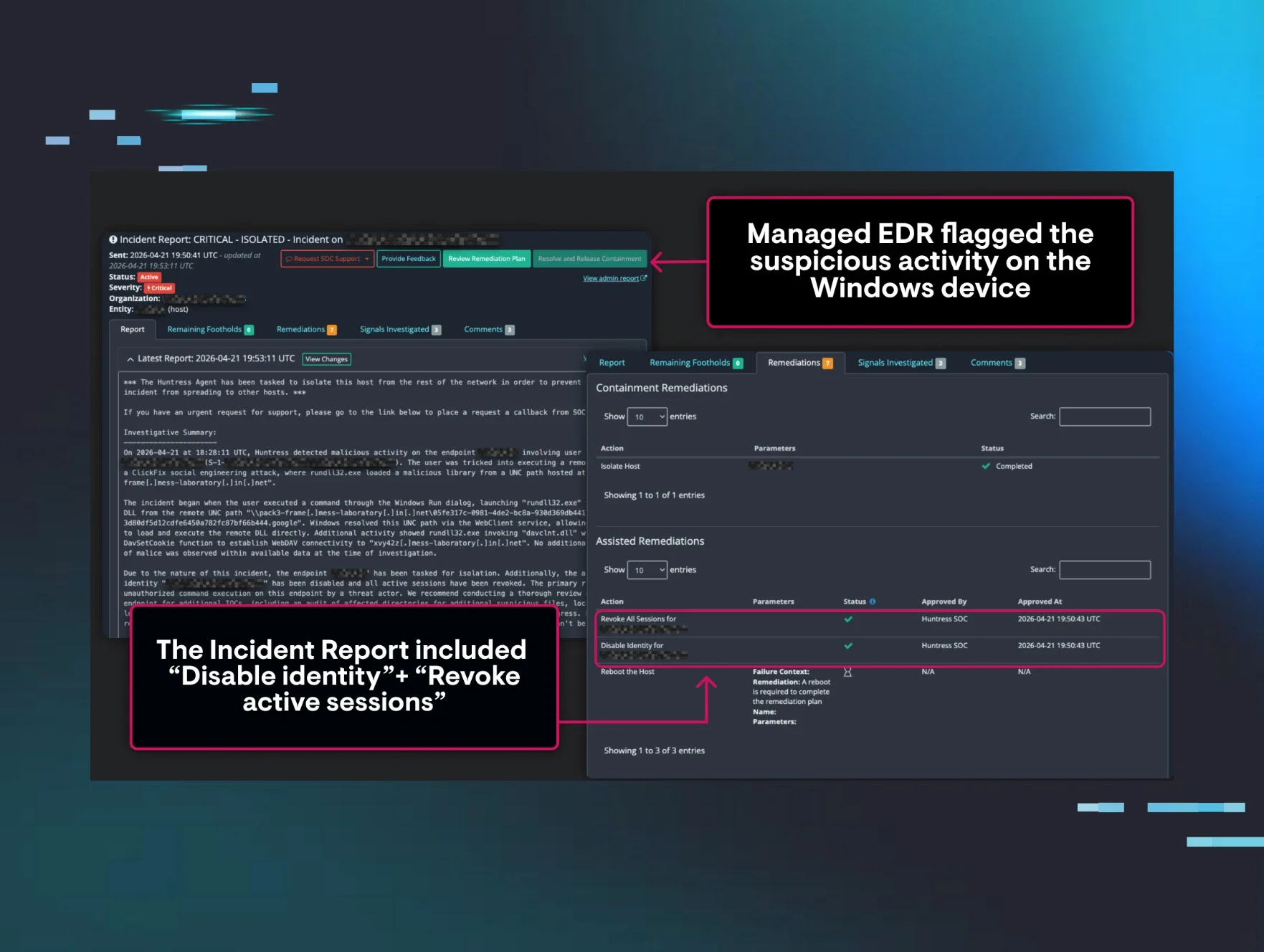
No organization is safe from ransomware attacks. Here’s a real-world example from the Huntress SOC where an adversary targeted a fire department’s IT systems! The attacker landed on an endpoint and launched an EDR killer to try to blind the SOC, which Microsoft Defender Antivirus detected and quarantined.
The attacker then moved on to scoping out remote shares to encrypt and built a target list. The adversary then launched the attack, deleting shadow copies, a common practice to prevent encrypted files from being recovered, and executing the Akira encryptor against the targets. The timestamps suggest that the attacker automated this portion of the attack to move as fast as possible before being detected. But the Managed EDR Attack Disruption Engine quickly detected the suspicious activity and killed the Akira encryptor process every time it was launched to encrypt a share, preventing any files from being encrypted and minimizing the impact to the organization.
The future of Attack Disruption
We've just started the journey with Managed EDR Attack Disruption. As our threat experts and SOC uncover new attacker tradecraft and tools, Attack Disruption will be there to make it hard on hackers.
Want to learn more about how Huntress bolsters your endpoint security and resilience? Reach out and book a demo today!