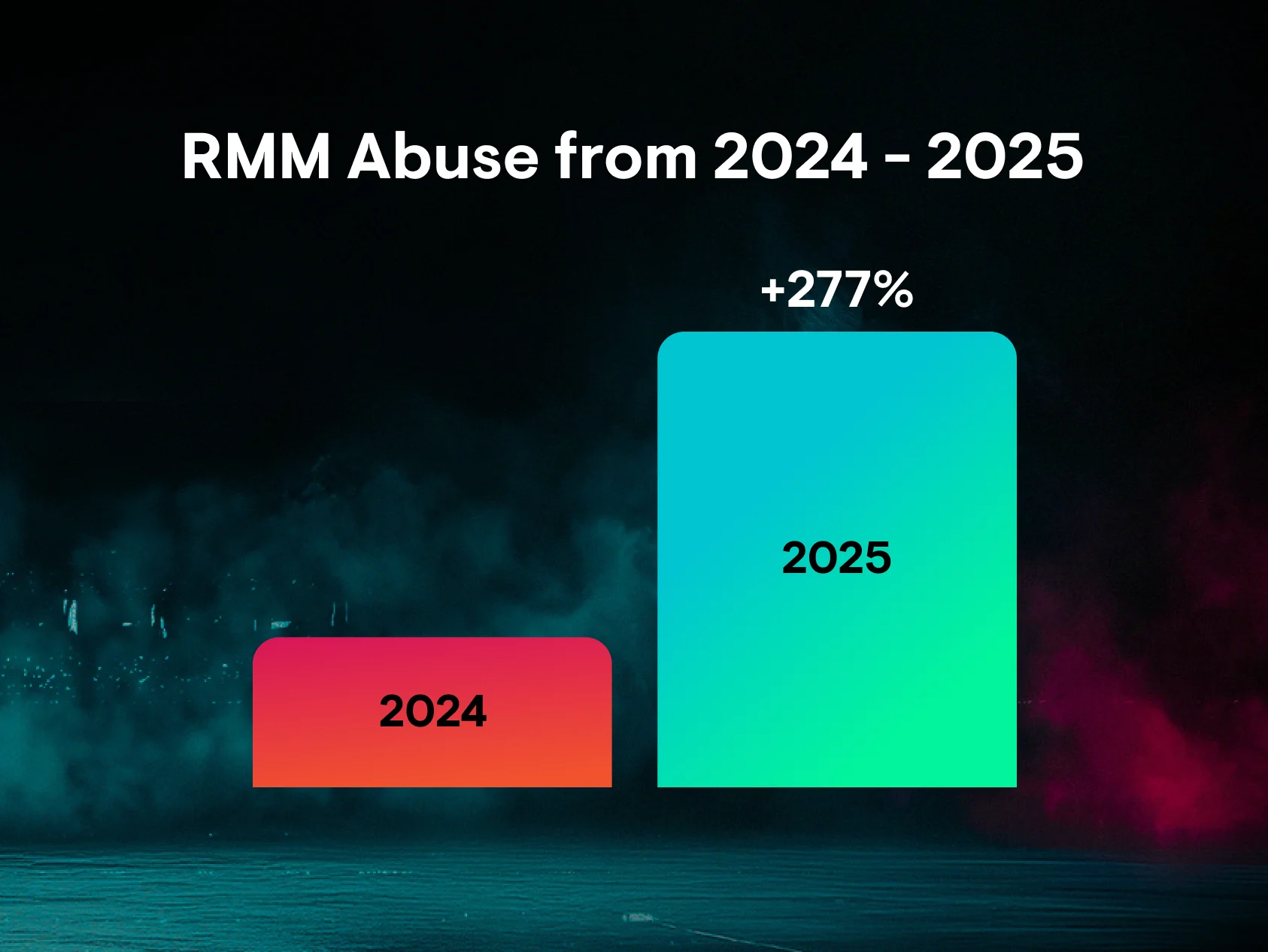
Cybercrime is booming, and it’s cashing in on your trusted tools and software. That’s the reality of Remote Monitoring and Management (RMM) abuse. And why the Huntress 2026 Cyber Threat Report reported a mind-blowing 277% jump in RMM abuse in 2025.
Key takeaways
-
RMM tools are essential for IT operations but increasingly weaponized by attackers, who exploit legitimate, pre-installed remote management software for interactive, hands-on-keyboard (HOK) access
-
RMM abuse is a leading cybercrime tactic because attackers gain persistent, stealthy access while evading security detection, since trusted RMM binaries don’t appear malicious
-
RMM compromises often start with phishing or social engineering, where users are tricked into installing a malicious RMM agent
-
Approved RMM tools are abused by attackers, so organizations need to shift from trusting software presence to verifying behavior. This means defining a normal activity baseline, watching for anomalies, and keeping up with tool fingerprinting to quickly spot unauthorized or unusual remote access activity.
-
People are a critical defense layer. Security awareness training (SAT), mindful IT reviews, and a “see something, say something” culture help catch suspicious behavior before it turns into ransomware or data exfiltration
Hear from our security pros on the current state of RMM abuse:
The RMM reality check
RMM tools are the lifeblood of modern IT administration. They’re how security pros patch systems, troubleshoot issues, and manage networks from anywhere in the world. But this powerful utility has a dark side. When a security team’s own shield becomes the entry point for an attacker, the game changes entirely. It’s not just about cybercriminals dropping external malware anymore. It’s the mayhem they bring to the trusted tools already sitting on your endpoints. And cybercriminals don’t play by anyone’s rules but their own.
The perfect disguise for adversaries
RMM abuse has become one of the most widespread threats in the cybercrime ecosystem, and for good reason. It’s an ideal path of least resistance for attackers to gain access and persist in business environments. Attackers have realized that using pre-installed, legitimate software to launch attacks is more effective than trying to push custom malware past a firewall or endpoint detection and response (EDR). RMMs are interactive, HOK access, so attackers hide in the noise of daily operations.
RMM tools are designed to provide continuous remote access. But when an attacker compromises these tools, they inherit that persistence. Suddenly, they can automate tasks, move laterally across the network, execute commands, and even drop ransomware, all while appearing to be a helpful IT administrator. The Huntress 2026 Cyber Threat Report findings show that over 50% of cases following suspicious Atera RMM activity are directly linked to ransomware attacks.
Here’s why this creates a massive headache for defenders. Security products are tuned to spot known bad signatures, like ransomware or remote access trojans (RATs). But a valid RMM binary isn’t a red flag, so it often slips past security detections in the name of business continuity.
How RMM compromises play out
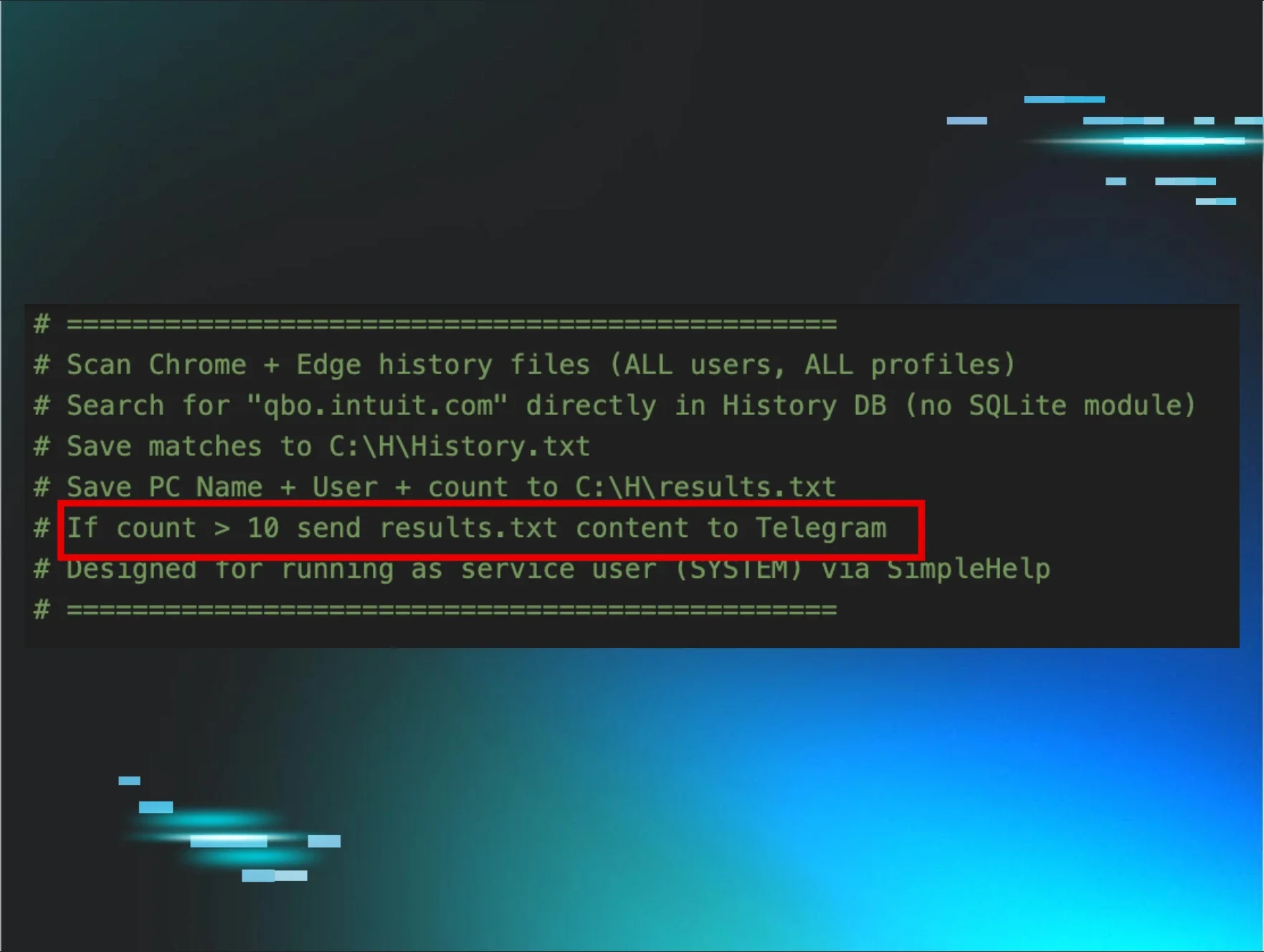
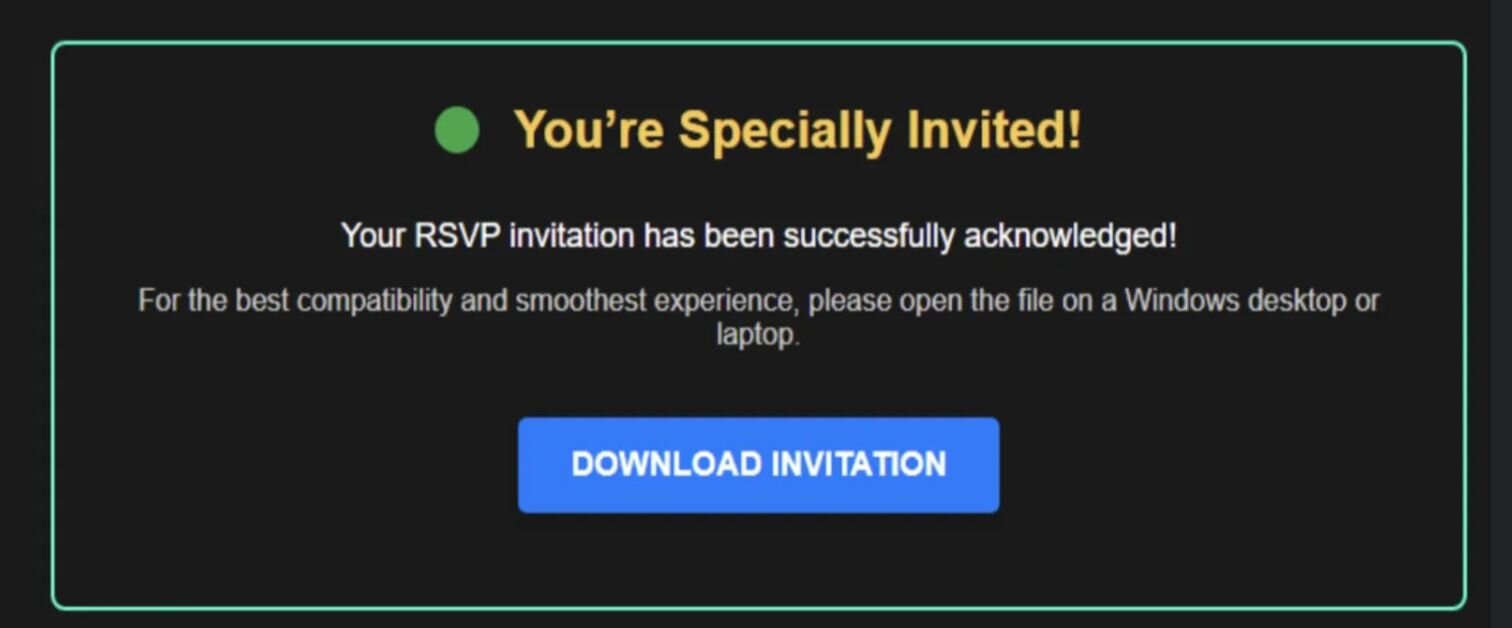
It often begins with sneaky social engineering and phishing scams. Users receive an email that looks authentic: think DocuSign request, a party invitation, or a Dropbox link. It then prompts them to click a link or download a file to view a document. But they aren't actually opening an invite or an invoice. They’re installing an RMM agent that connects directly to the attacker. The attacker has immediate access to your environment as soon as the agent installs.
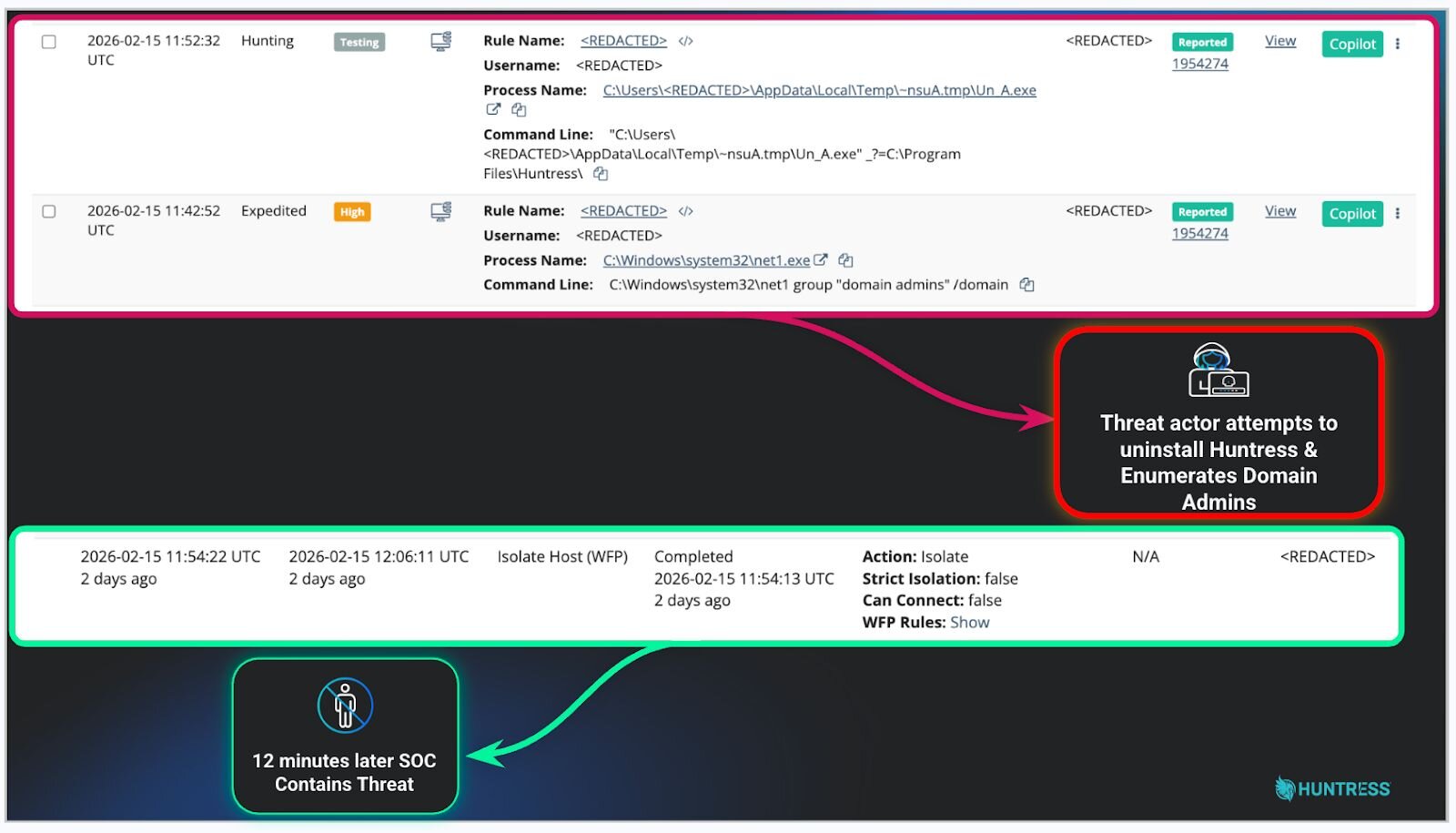
In other cases, like this one from our Security Operations Center (SOC), a threat actor used stolen RMM credentials to gain initial access to a partner’s environment. Luckily, our SOC contained the threat about 12 minutes after the threat actor executed the first command, and then stepped up to help the partner further manage the incident.
But the bottom line in this case is that the partner’s approved RMM software was abused, leading to a fast-moving intrusion that involved running enumeration commands and attempting defense evasion by disabling the Huntress agent. Since the credentials belonged to an IT support technician, the threat actor would have gained access to all environments managed by the managed service provider (MSP) if the threat hadn’t been contained within minutes.
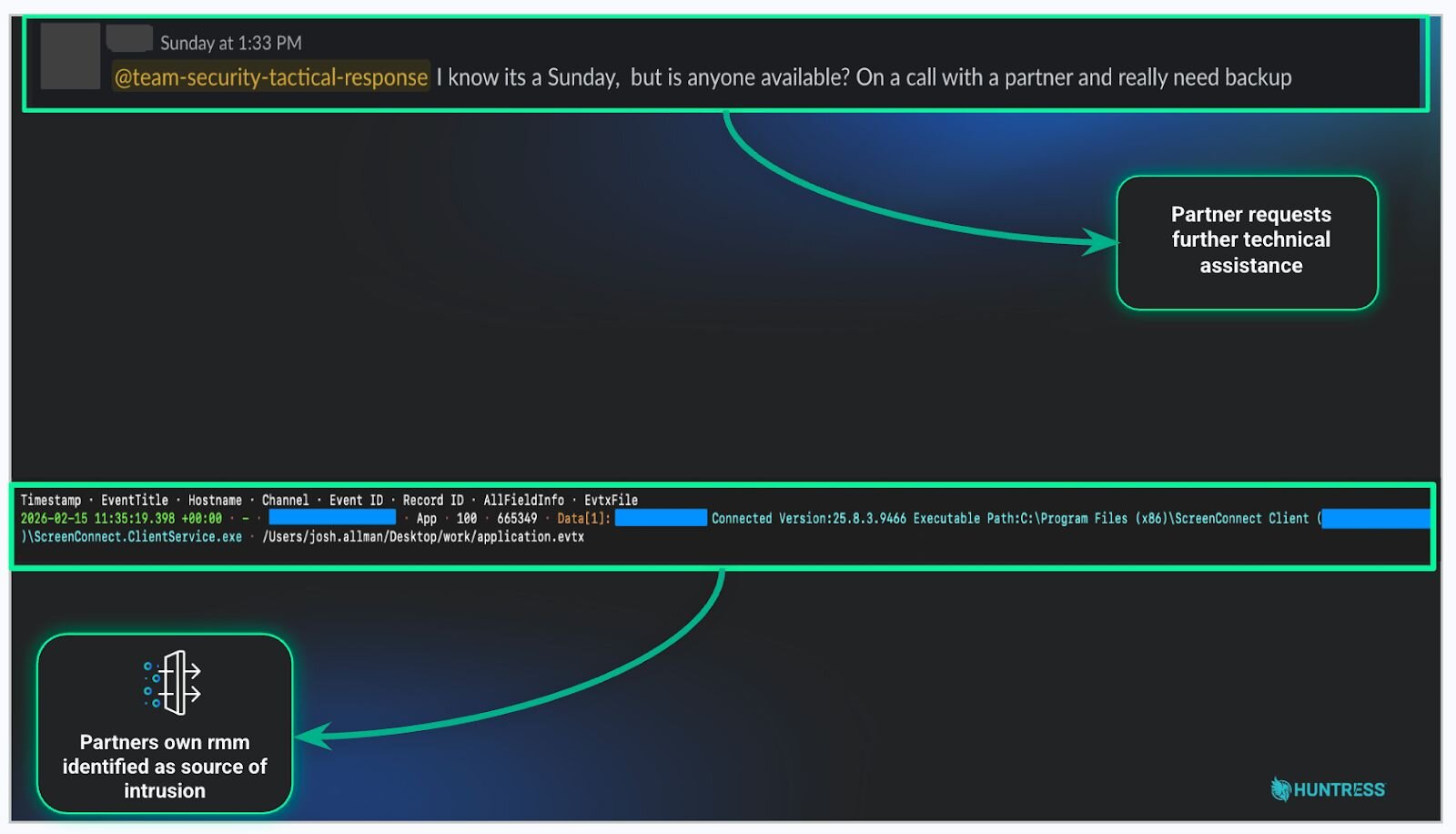
In supply chain attacks like the example above, the stakes are even higher. When attackers compromise an RMM solution used by an MSP, they gain direct, interactive access to every single customer managed by that MSP.
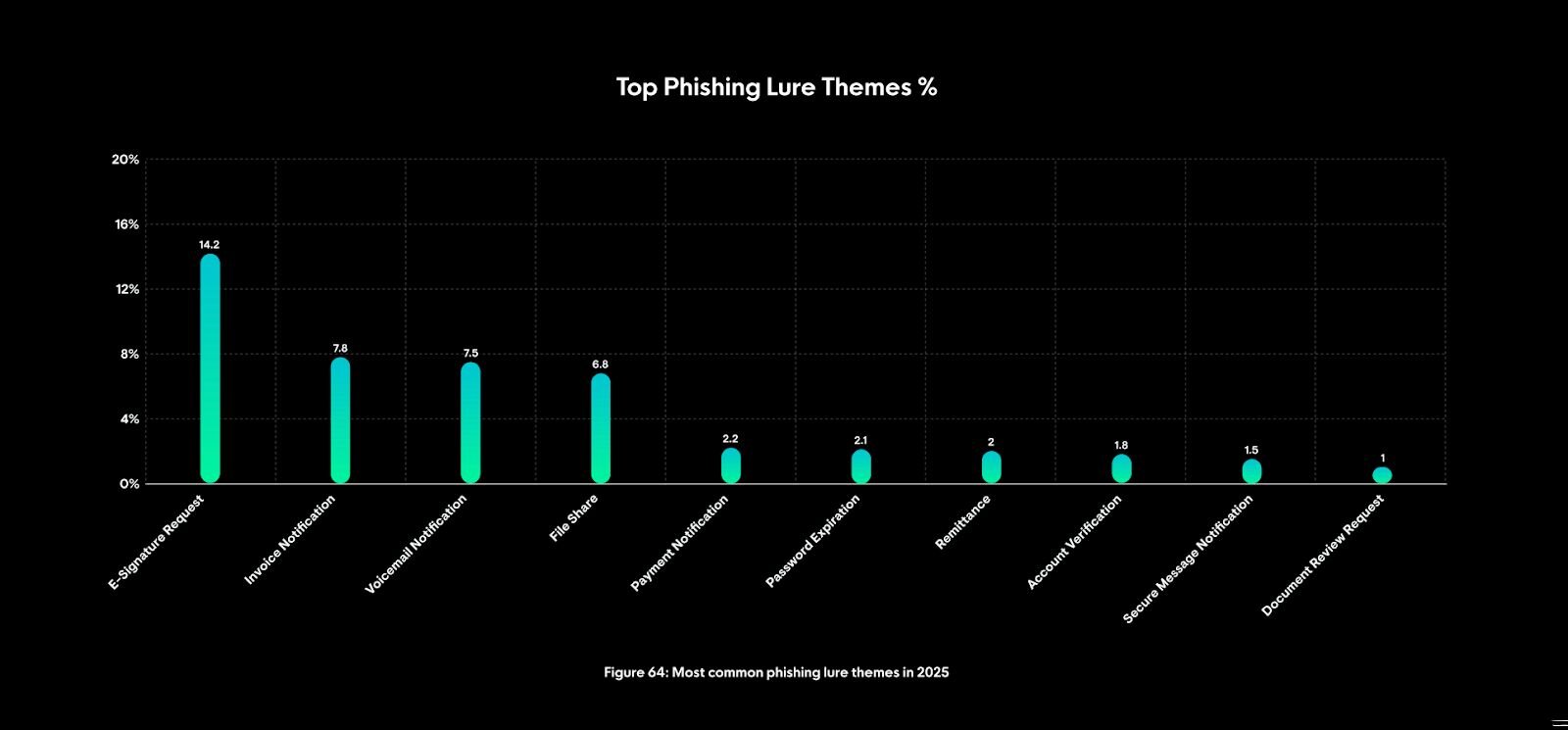
In 2025, these common email messages doubled as the most common phishing bait, so pause before you click:
-
E-signature request (14.2%)
-
Invoice notification (7.8%)
-
Voicemail notification (7.5%)
-
File share (6.8%)
Figure 4: Most common phishing lure themes in 2025
Legit tools. Bad intentions.
Too often, businesses make this common security mistake: if a tool is approved, every instance of it is automatically trusted.
But let’s consider a scenario where a remote employee uses an RMM to access their laptop from home. An administrator sees the traffic and assumes, "Normal activity."
But this assumption can be risky. Just because the RMM traffic is expected doesn’t mean this specific session isn’t an adversary hiding in plain sight. Attackers bank on that complacency. They know IT teams are conditioned to expect these tools in the environment.
Defending against this requires a shift in mindset. The presence of approved software isn’t proof of security. When strange timing, users, or behavior shows up, the activity warrants a second look, even if the tool itself is authorized.
Define the baseline
How do you defend your environment when the threat looks strikingly similar to your admin tools? The first step is to define what "normal" looks like for your organization:
-
What’s the standard level of user activity?
-
Which users typically access which tools?
-
What time of day do these connections usually happen?
If you know your baseline, anomalies stand out fast. When a user in marketing suddenly runs command-line scripts via an RMM tool at 3am, you’ve got a problem. It doesn’t matter if the tool is approved because the behavior isn’t.
Dedicating resources to review these RMM usage patterns helps you catch sketchy deviations before they snowball into full-blown ransomware or data exfiltration. When tools like RustDesk or Atera are abused, ransomware damage can unfold in as little as an hour or two, according to the Huntress 2026 Cyber Threat Report.
Inventory everything: The power of fingerprinting
It’s not enough to know that you “use ScreenConnect.” You need an ongoing, detailed inventory of your attack surface. Dig into the details and create fingerprints of your digital ecosystem that answer questions like this:
-
What specific RMM tools are approved for our environment?
-
What are the approved executable hashes for these tools?
-
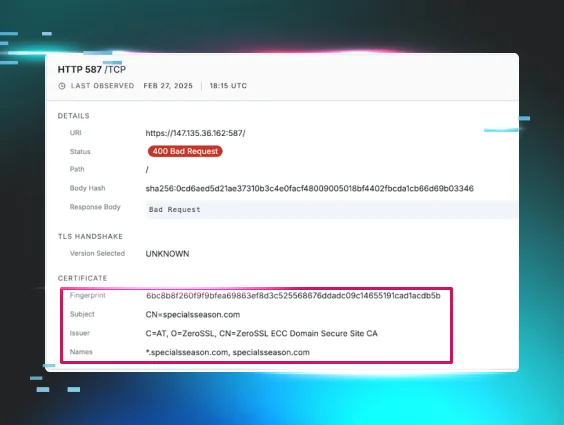
What URLs or IP addresses should these tools connect to?
By fingerprinting approved tools, you can set up alerts for anything that doesn't match. If a new RMM shows up and the hash doesn't match your allow list, or if it tries to connect to an unknown server, you know it needs to be checked out ASAP.
Treat every remote access tool like a potential intruder until verified. If you find a tool you didn't install, that’s not business as usual. Verify the configuration, check the logs, and confirm the connection endpoint for valid or malicious activity.
The human element: Your strongest line of defense
Your strongest line of defense? Your people. That matters more than ever with RMM abuse, where attackers exploit human trust for access and hide their attack path behind trusted software. Attackers count on human errors to unlock the front door, often through phishing or social engineering.
Spotting shady behavior early is what keeps a small red flag from turning into a full-blown breach. Managed Security Awareness Training (SAT) helps end users notice sly social engineering attempts that deliver malicious RMM payloads. Everyone deserves to know that a "party invite" doesn’t require administrative privileges to open.
Furthermore, encourage a culture of vigilance within your IT and security teams. If an analyst sees something weird, they should feel comfortable speaking up. "See something, say something" applies to network traffic just as much as it does to physical security. If your whole company is equipped to watch for outlier behavior, you close the gap between infection and detection.
Stopping RMM abuse requires teamwork
RMM abuse isn’t disappearing anytime soon. As long as these tools provide easy, powerful access and cash flow, attackers will use them.
Shutting down this trend will require collaboration between RMM vendors, cybersecurity companies, and (potentially) government agencies. We need to make it harder for attackers to abuse these tools anonymously. This could look like stronger vendor-side abuse detection, faster removal of malicious instances, and better intelligence sharing to identify rogue servers more quickly.
Until then, security teams have to step up their game. Your RMM is a powerful tool, but in the wrong hands, it’s your toughest competition.
Download the Huntress 2026 Cyber Threat Report or the TL;DR to better understand and stay ahead of RMM abuse in your own environment.