Every intrusion that we comb over here at Huntress is different in its own way. Although there are definitely discernible patterns when it comes to intrusions, us analysts are often left guessing as to threat actors' intentions and motivations.
Sometimes, a case breaks established patterns and reveals itself as more interesting, or, at least, worthy of a closer look.
This blog will cover an example of one such case—one that began with a simple brute force attack and led to the unraveling of infrastructure and tradecraft that we suspect as being linked to a larger ransomware ecosystem, particularly initial access brokers.
Attack narrative
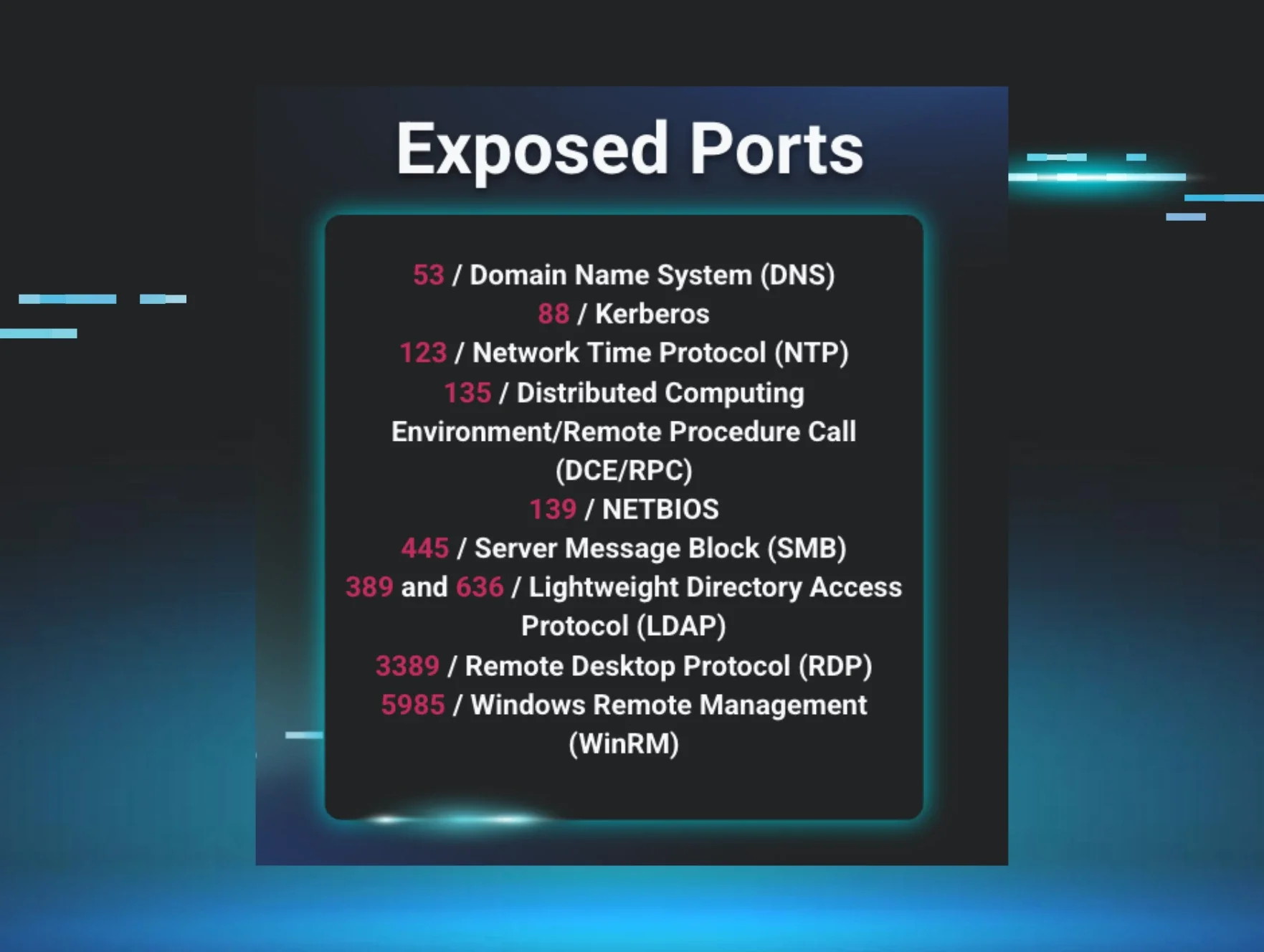
In this case, a network was exposing a Remote Desktop (RDP) server to the broader internet. We’ve talked about the dangers of this dynamic through different webinars, blogs, and social media posts, yet often businesses have no choice but to expose RDP for a myriad of reasons.
In this instance, our Security Operations Center (SOC) received an alert for some domain enumeration and got to work.
Brute force
Although intrusions are often written about in a linear fashion, neatly mapped to frameworks like ATT&CK, the reality is that analysts often receive signals for intrusions that are normally found in the “middle” of a threat actor's kill chain. This means that once a signal is received, we have to work both backward and forward in time to find both the source of the intrusion as well as any go-forward attack paths.
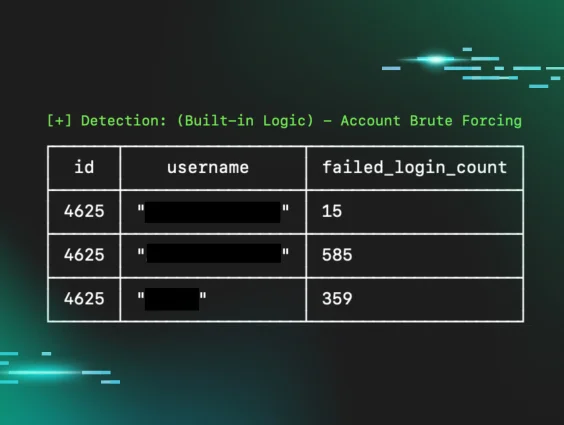
In this case, upon investigation of the Windows event logs for the affected hosts, we discovered that the RDP service was being brute forced.
Although brute forcing is considered a “bread and butter” type attack technique, investigation of brute force attacks, particularly in networks with default logging configurations, can get a little tricky. Often, recorded login attempts fill up the log channels with security-relevant telemetry being overwritten or discarded. Adding to this dynamic are various service accounts for inventory or vulnerability scanning tooling that often generates failed logins to various services.
Here, the relevant telemetry was thankfully available, and a successful brute force attack was discovered. Although a multitude of accounts were targeted via this brute force attack, only one account was successfully compromised.
Using this compromised account as a pivot point, we discovered that the account had been compromised from multiple IP addresses. This dynamic is at least somewhat atypical or nonstandard for what we'd expect to see in most intrusions. Upon further review of the timestamps of the successful logins, evidence suggested that this compromise was not from multiple threat actors, but from one threat actor utilizing infrastructure that allowed compromise from various servers.
Figure 1: Initial SOC incident report showing brute forcing from multiple IP addresses
The successful brute force of the exposed RDP server meant that the threat actor now had access to the victim's network. Once this access was established, the threat actor proceeded to enumerate the domain, including various groups and domain configurations.
Figure 2: Image showing domain enumeration commands
When these enumeration signals were investigated by the SOC and determined to be malicious, network-wide isolation was issued to prevent further lateral movement within the network.
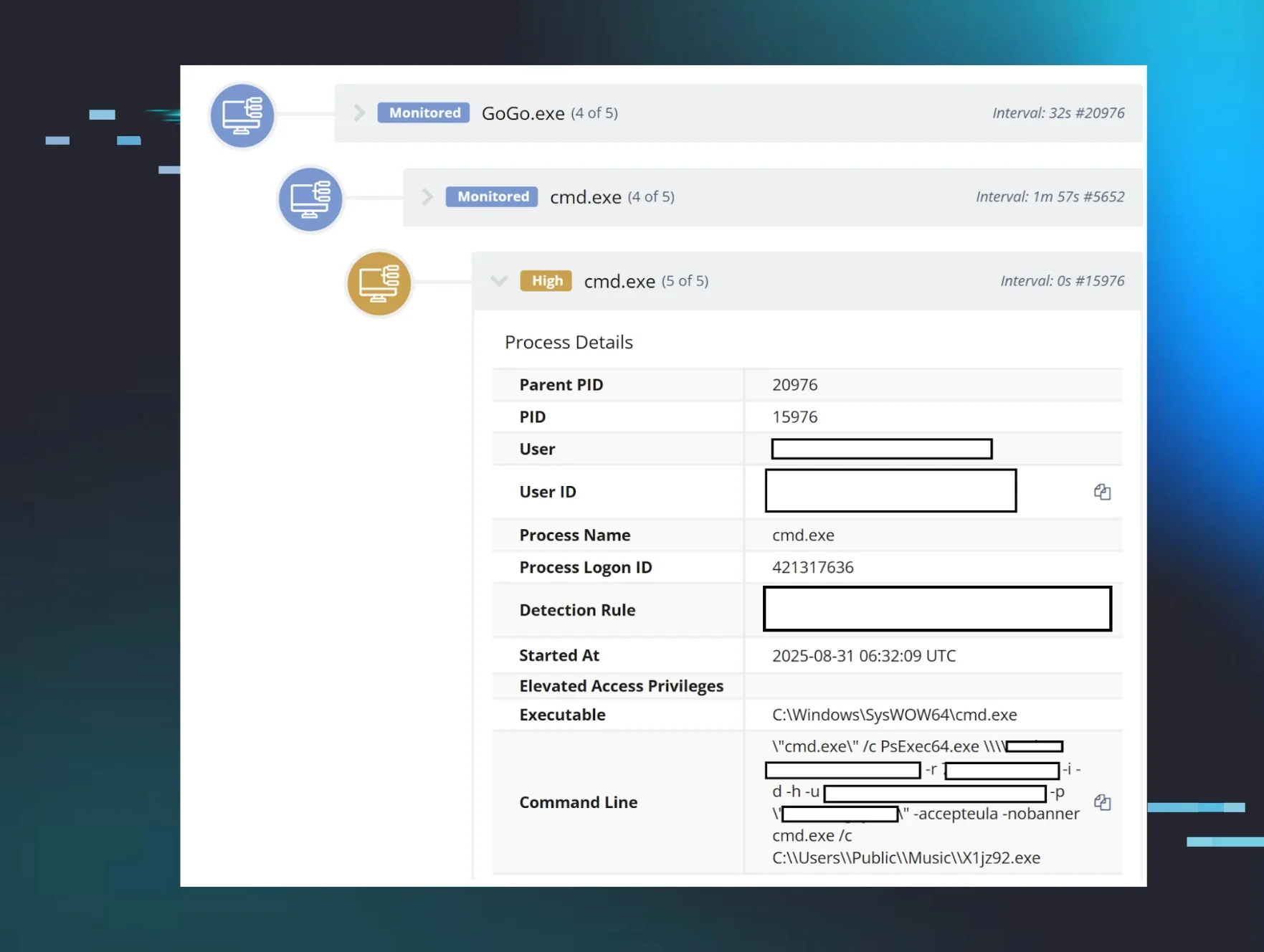
At first glance, this may seem like a straightforward incident: a successful brute force occurs, the threat actor lands in the network, and proceeds to enumerate said network prior to being discovered and shut down by the SOC. This time, however, upon reviewing other bits of telemetry after isolating the network, we discovered something particularly interesting and out of step with the normal threat actor activity patterns we observe.
Something feels off
When threat actors land inside a network—either through an RDP intrusion like we’ve covered so far or through other means such as VPN compromise—they'll typically enumerate the network, gather credentials, and move laterally.
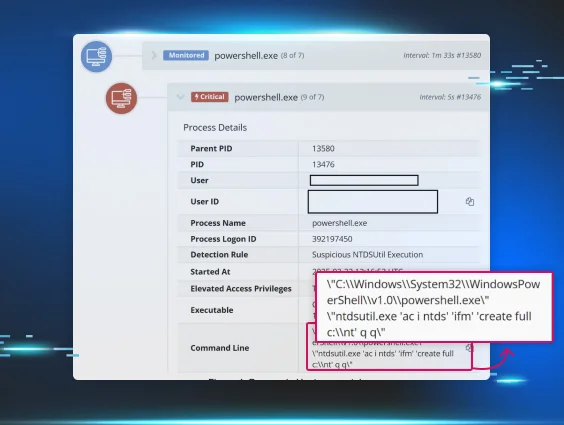
Typically, credential access in these scenarios consists of extracting credentials from the Windows LSASS process through tooling like Procdump or Mimikatz or credential access via registry dumping via something like Secretsdump. In some cases, we’ve also observed threat actors going after browser cookies.
We often don't observe threat actors going through file systems or file shares to look for credentials in files. In this intrusion, however, we observed just this.
Absent hard evidence, we can only offer educated speculation as to why this dynamic plays out the way it does. Our hypothesis is that most threat actors have a playbook that's followed. Extracting passwords from the registry or from LSASS can be performed in a playbook-type fashion, with commands and tooling differing little from environment to environment. This isn't the case for passwords in files, as these can be found in many places on the network. In addition, once credentials are extracted from the registry and from LSASS, we can surmise that these credentials are utilized in one way or another within the network, making them attractive to threat actors. In contrast, credentials found in files may be historical, old, or outdated, and they need manual testing to verify whether they actually grant access to a targeted resource.
In this particular instance, the threat actor chose a manual approach, using Notepad to open up text files that ostensibly contained credential materials:
Figure 3: Image showing process tree with notepad opening text files containing passwords
When we examined the jumplist artifacts from the affected host, we noticed even more threat actor activity linked to credentials in files.
Figure 4: Forensic evidence of threat actor looking through “password” themed files
This uncharacteristic tradecraft prompted a second and closer examination of the IP addresses associated with the brute force attack.
Unraveling the infrastructure
An initial look at the offending IP addresses resulted in some hits via Maltrail, which indicated that the IP in question was associated with Hive ransomware:
Figure 5: Image showing brute force IP addresses associated with Hive ransomware
Other reporting via CISA also links this particular IP address to BlackSuit.
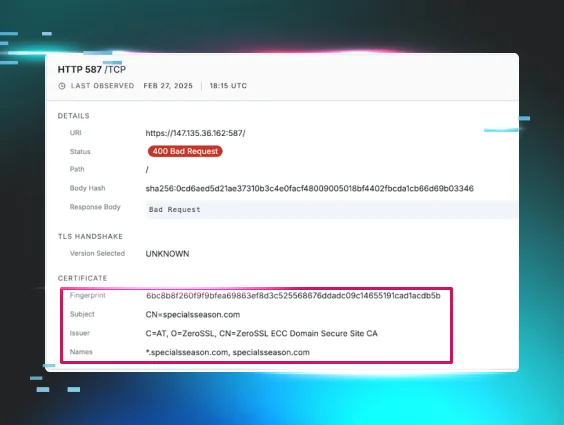
With this information now in our possession, we wanted to pivot from this data point and look for any interesting domain names. When examining the TLS certificates associated with the brute-forcing IP address, we discovered an interesting domain name of specialsseason[.]com:
Figure 6: Image showing certificate information for a malicious domain
Now that we had a domain name associated with the offending IP address, we pivoted to the TLS certificate fingerprint to see if we could identify further malicious infrastructure consisting of either IP addresses or domain names.
This yielded surprising results, and we found multiple related IP addresses and domain names:
Figure 7: Image showing pivot from initial certificate fingerprint to other domains
When reviewing the IP addresses and their associated domain names, a pattern emerged. Each of the IPs resolved with the same naming convention: NL-<countrycode>.specialsseason[.]com
Below is a full listing of all the various country codes found associated with the TLS certificate of the IP address used in the original brute force attack:
Figure 8: Image showing Google search for specialsseason domain with an additional domain displayed
We can observe a fairly robust network that's geographically distributed. Also interesting to note here is multiple “Ru” / Russian codes as well as multiple US country codes.
Many of the IP addresses associated with the above country codes also contained various listening services on various ports. An examination of TLS certificates of these IPs presented an opportunity for a further pivot revealing yet another malicious domain name of 1vpns[.]com:
Figure 9: Image showing pivot from certificate fingerprint hash to additional domains
Interestingly, this domain name is very similar to the legitimate VPN site, but without the extra “s” after “1vpn”: https[:]//1vpn[.]org/
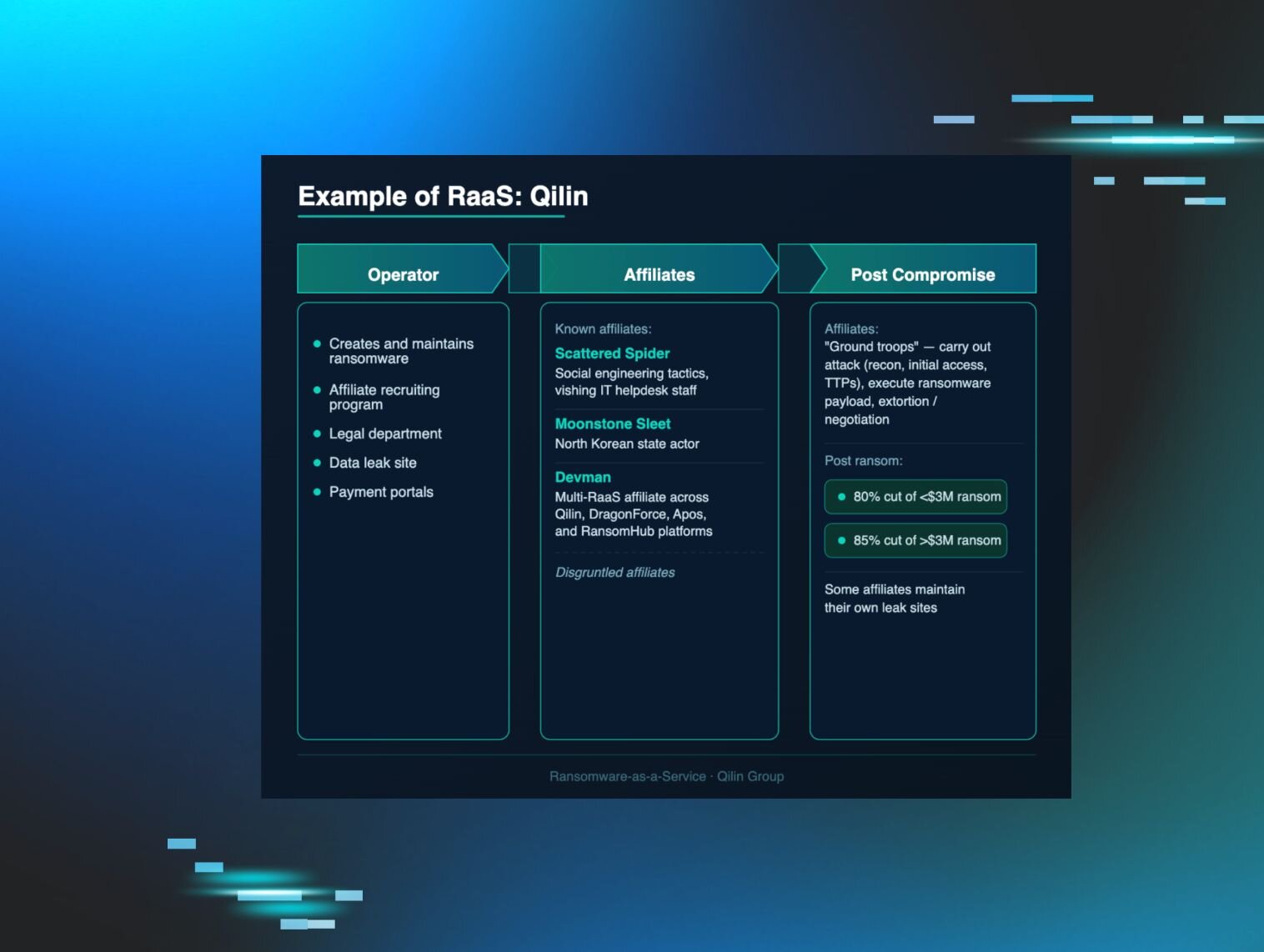
Some domain names mean nothing and are random but here we don't believe that to be the case. The term “Special season” also referred to as “big game hunting” has been a common phrase used to describe financially motivated threat groups, typically ransomware targeting high-value and or high-impact organizations.
Two public threat reports link the use of this VPN service to two separate ransomware groups—an additional service advertised 1jabber[.]com with a list of “funny”’ domains.
Figure 10: Image showing additional domains
Specifically focusing on the mention of nologs[.]club, whereas the VPN service FAQ also comments on the fact they keep 0 logs, which would make this an ideal service for any cybercriminal.
We often read about ransomware cases through a lens of techniques, tactics, procedures, and other abstract elements. We often hear terms like “initial access brokers” but often don't get an inside view into their operations, particularly through an infrastructure lens. In this case, we can see how these nefarious actors operate and can get a glimpse into their motivations as well as the kinds of elements that make up their ecosystem. A clear motivation to get as much credential material as possible is evident in this case. This case also demonstrates the need to sometimes go beyond traditional incident response, where a “zooming out” is required. Here, a “simple” brute force turned out to unravel an entire ecosystem and infrastructure for ransomware operators.
Most intrusions don't facilitate this kind of analysis either due to lack of telemetry or many other factors. This intrusion is different in that a tiny little thread of evidence led to an unraveling of a proverbial yarn of ransomware infrastructure. The evidence also provides insight into the behavior and objectives of these threat actors in a manner that's difficult to convey through static IOCs or TTPs.
Conclusion
Ransomware continues to disrupt businesses large and small alike. For many security professionals, a brute force is a “bread and butter” technique that's been covered and written about for many years. Many analysts may see a brute force attack and will move on with their day. At Huntress, however, we're always looking to “SOC and Awe,” constantly pulling on every and any investigative thread that we can get our fingers on.
In this case, what started out as a simple brute force attack turned out to unravel a rather large suspected ransomware-as-a-service ecosystem, specifically one that's suspected to be utilized by initial access brokers who facilitate this illicit dynamic.
Indicators of Compromise
|
IOC Type |
IOC |
|
IP Address |
64.190.113[.]159 |
|
IP Address |
147.135.36[.]162 |
|
Domain |
specialsseason[.]com |
|
Domain |
1vpns[.]com |
|
Certificate Fingerprint (SHA256) |
6bc8b8f260f9f9bfea69863ef8d3c525568676ddadc09c14655191cad1acdb5b |
|
Certificate Fingerprint (SHA-1) |
65899cd65dd753d2eef5463f120ae023e873e1bd |
|
Certificate Fingerprint (SHA-246) |
|