The Huntress SOC team continues to see new Emotet, Trickbot, and Qakbot malware outbreaks within networks — regardless of antivirus, anti-spam, or firewall solutions. As a result, we’ve become too familiar with the hurdles MSPs and IT departments face when attempting to contain these worms (sometimes taking months to remediate).
In this blog post, we’ll look at how these malware families (and attackers) abuse Windows’ Administrative Shares to propagate. We’ll also share battle-tested techniques you can leverage to quickly curb the spread and begin remediation.
Introduction to Administrative Shares
An often overlooked feature of Windows is the administrative shares. These shares, which are enabled by default, provide administrators and software the functionality to remotely manage hosts. Although most network shares are visible within Windows Explorer’s network view (browse to \\localhost), administrative shares are not displayed. This is the result of a feature that “hides” any share with a name ending with a “$”.
It should be noted that the word “hidden” is a bit of a misnomer. Only Windows hides these shares from being displayed. If you were to connect to these shares with a Unix/Linux/macOS SMB client, all “hidden shares” would be visible.
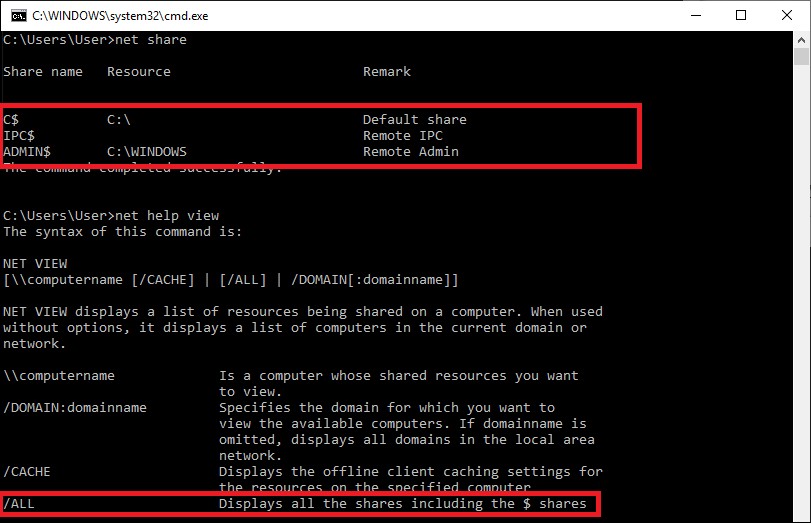
In fact, even Windows allows you to locally and remotely discover “hidden” shares using the net share and net view /all commands as shown in the image below:
Viewing admin shares on a Windows 10 host with a single partition and documentation on remote viewing.
Exploiting Administrative Shares
Accessing the administrative shares requires administrative privileges. While useful under normal operations, Windows' administrative shares can be problematic when there is malware or an attacker on the network as the shares can be leveraged for lateral movement.
Malware with worming capabilities, such as Emotet and Trickbot, will steal credentials and also use brute force to gain access to other systems on the network. Once the malware has obtained credentials, both Emotet and Trickbot use a technique similar to Microsoft’s PsExec tool to copy and execute malicious payloads on a remote victim host. This technique relies on the ability to access administrative shares.
For most networks, external access via the SMB protocol is blocked by the firewall. Within the internal network, however, SMB traffic is often unrestricted — allowing all hosts to communicate with each other. Consider the case where an administrator’s account was compromised (either stolen or brute-forced); if all the workstations have the same administrator credentials, the malware (or attacker) effectively has access to all the systems.
How You Can Reduce Your Risk
Someone (or something) with administrative privileges can wreak havoc on a single system. Through the malicious use of Windows Admin Shares, the result can be catastrophic if those administrative privileges grant access to multiple hosts.
Here are some simple steps you can take to minimize your risk of attackers exploiting Windows Administrative Shares:
- Randomize the local administrator password on hosts using tools such as Microsoft’s “Local Administrator Password Solution” (LAPS).
- Regularly audit accounts with administrative privileges and limit administrative access to only those users who require it. Keeping the number of administrative accounts low presents fewer “high-value” targets for attackers.
- On hosts that are not sharing resources with other systems (e.g., workstations), consider disabling administrative shares or enabling the local firewall to block access to the ports used for SMB.
Want to fight back against hackers?
Thousands of MSPs and IT practitioners rely on Huntress to find and stop the advanced attacks that evade their preventive security measures. You can get complete access to the Huntress Managed Security Platform with our free trial. Simply deploy our agent in minutes to an unlimited number of endpoints, set up a reporting integration into your ticketing system, and we’ll deliver step-by-step remediation procedures for each compromised host we discover.