Hackers often rely on email to be their delivery vehicle for malware. They develop a weaponized URL or attachment before delivering it via email to their unlucky targets. Email has become a hacker favorite in recent years because it is cheap and easy to use—and unfortunately, hackers know that users have a tendency to click on links and attachments.
But how do these phishing emails continue to get through traditional security layers, and what can defenders do to stop them? To help answer these questions, we brought in some experts.
Q&A with Our Experts
To provide some insider insight on the current state of email-based threats, we called upon Sébastien Goutal, Chief Science Officer at Vade, and John Hammond, Senior Security Researcher at Huntress.
You can also hear from Sébastien and John in their recent webinar, The Ransomware Lifecycle: From Email to Infection.
2020 drastically changed the way the world did business. In what ways did we see that trend translate to the world of cybercrime?
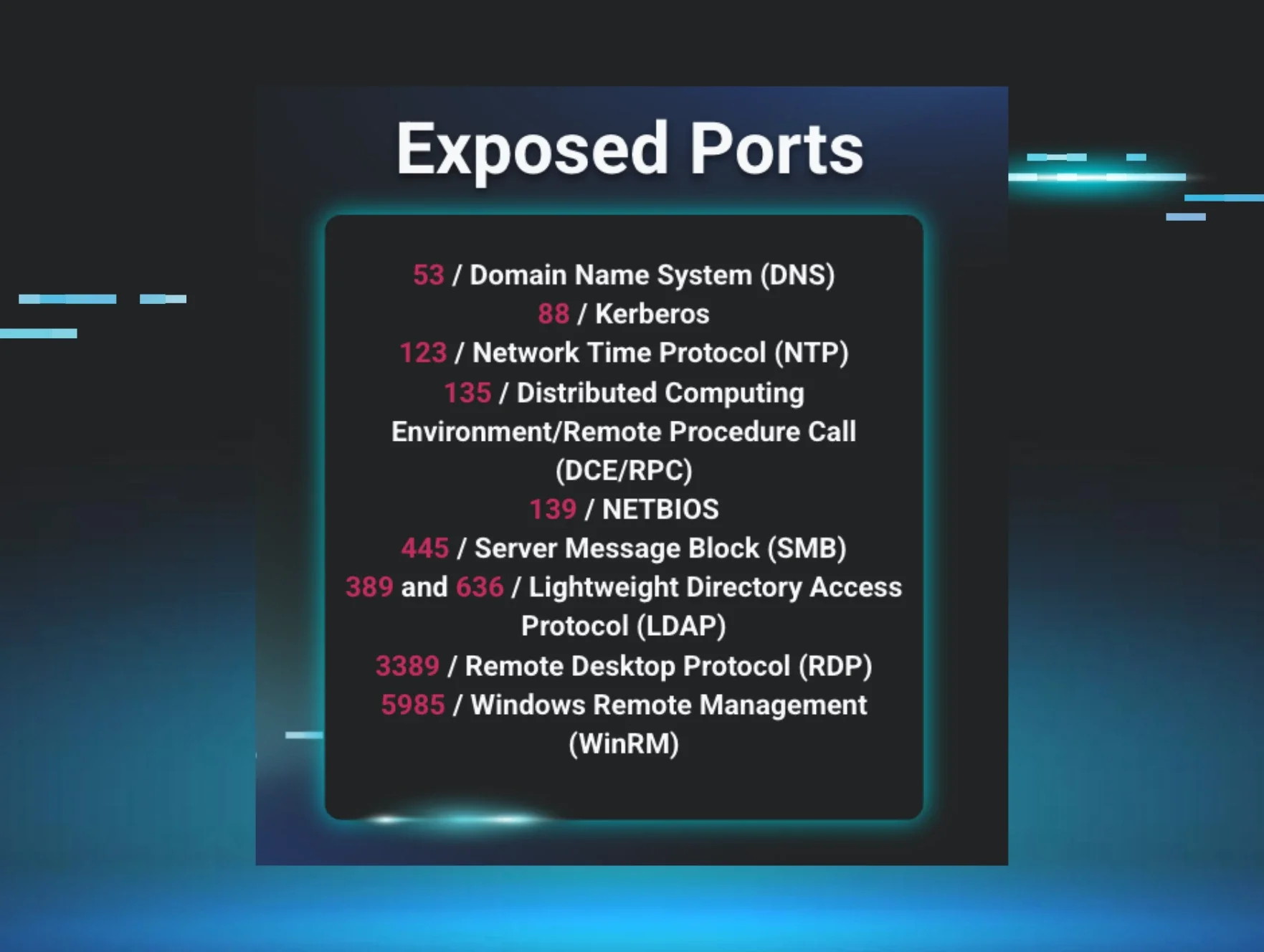
John Hammond (JH): “There is no question that with the pandemic and the recent year, the face of cybersecurity completely changed. In a frantic and knee-jerk reaction, businesses and organizations had to shift to a work-from-home model with personnel teleworking and operating fully remotely. Not only were employees no longer behind the castle walls, companies needed to rapidly deploy a solution for team members to access internal infrastructure and applications from their own homes.
Needless to say, this shook up the security landscape. Phishing and ransomware ran rampant, remote access trojans and cryptocurrency miners increased and cybercrime was at an all-time high. The sudden shift to remote work came with bandaid solutions, bad practices and more vulnerabilities than ever before—which are all factors that hackers continue to exploit today.”
Sébastien Goutal (SG): “Hackers are always ready to pounce on the first opportunity to attack. The sudden transition to remote work resulting from the COVID pandemic was, to hackers, simply too good to be true. They pounced immediately. At Vade, we saw an almost immediate uptick in phishing attacks—a 167% increase from March 2020 to April 2020.”
Were these trends a symptom of businesses’ or employees’ lack of preparedness, or were social engineering tricks becoming more sophisticated or exploitative of our situation?
SG: “It was a combination of both. COVID caught everyone by surprise. Many businesses that would have never considered going remote suddenly found themselves a fully remote company, totally unprepared for what was to come. Hackers then used social engineering to tap into weaknesses both in infrastructure and in humans. The phishing surge in April included COVID-themed emails that played on our fears about the virus, from emails impersonating the World Health Organization to local health authorities. Even employees who had received user awareness training were vulnerable to these messages due to the nature of the situation.”
JH: “Threat actors work smarter, not harder. Deception, deceit and decoys are a hacker’s game, and it is certain that attacks are becoming more sophisticated. While businesses and employees leave themselves in a vulnerable position, the capabilities and prowess of the bad guys are ever-growing. It is a synthesis of both perspectives: we were unprepared for this onslaught, hackers took advantage of our situation, and they continue to improve their tradecraft.”
What is it about email? Why is it a top delivery method for ransomware?
SG: “Email is the main communication tool for businesses, so it’s not surprising that it’s widely used to deliver ransomware. The ransomware is, however, very rarely delivered directly via email—it is usually the email body or one of its attachments that contain a link to the ransomware.”
JH: “Email is a prime target due to its nature—there is no other technology that lets a threat actor mass-deploy malware to so many victims, often without restraint. Email addresses can be easily discovered and validated to ensure it is a legitimate address. Plus, end users are trained with a sort of muscle memory to click through emails—meaning bad actors can be confident that if they cast a wide enough net, certainly one or more unsuspecting targets will open the email or click its links.”
How does ransomware evade detection or being flagged by security tools that defend the perimeter?
SG: “Many techniques are used to confuse defensive layers. For example, the download and installation of the ransomware may be performed by JavaScript or VBA code in PDF or Office attachments. The malicious code is often unique, obfuscated and sometimes encrypted—to render fingerprint and static code analysis-based technologies useless. Sites hosting the malicious files also use cloaking evasion techniques so that malicious content cannot be detected by URL scanners and web crawlers. Cloaking techniques range from HTTP User-Agent header filtering to only delivering the malicious content to IP addresses based in a specific country.”
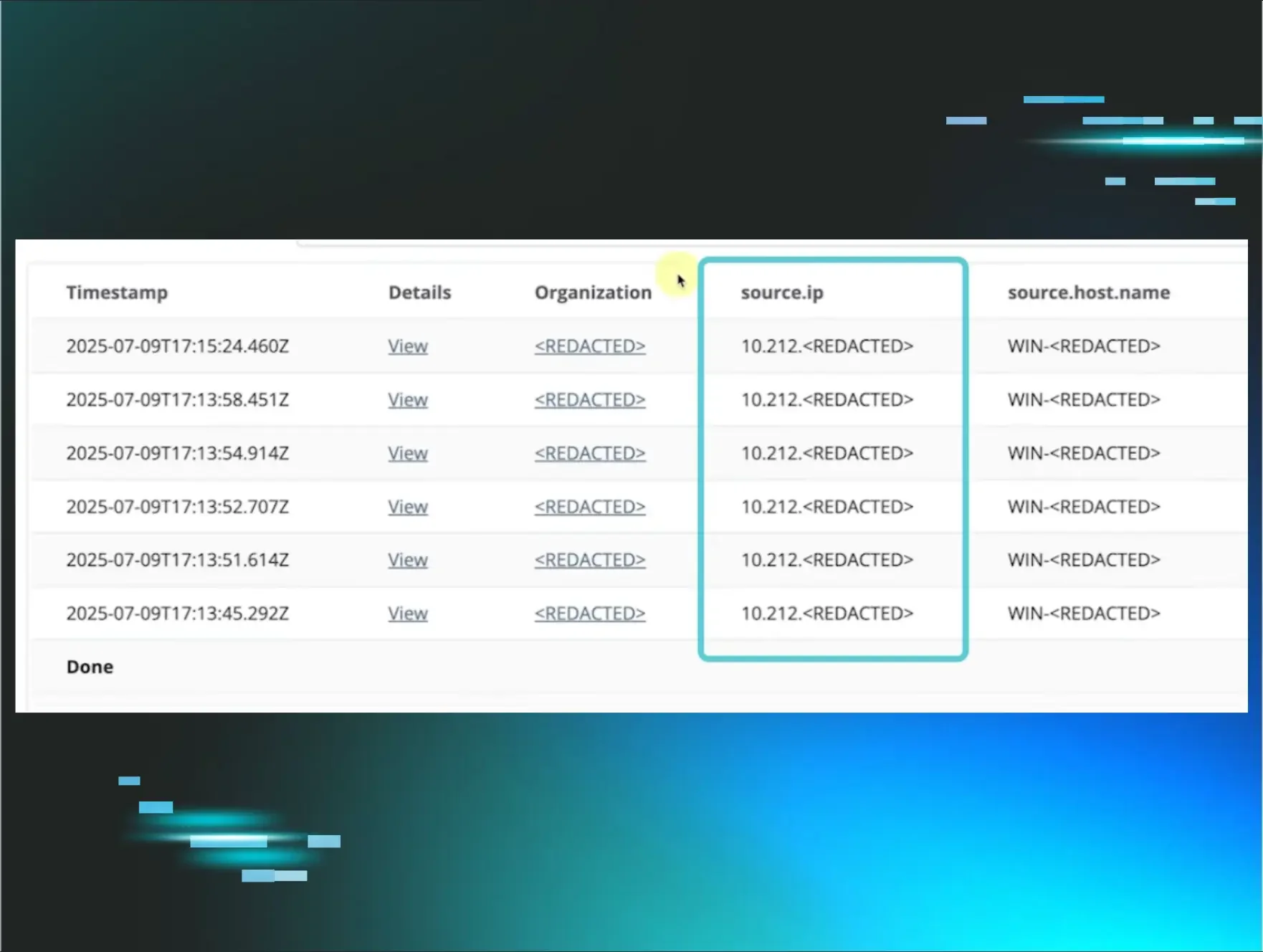
JH: “At its core, ransomware is like any malware—it has to be staged in payloads or layers that can help it go undetected from automated security mechanisms. Oftentimes, malware uses living-off-the-land techniques to abuse tools and utilities inherently native to the victim’s operating system. Even then, they weaponize fileless malware techniques to reside solely in memory and leave behind as few fingerprints as possible. Until it is time for ransomware to ‘detonate,’ threat actors might lurk and live undetected in networks just waiting until go-time.”
What are some new developments we’re seeing in ransomware, phishing or other email-based attacks?
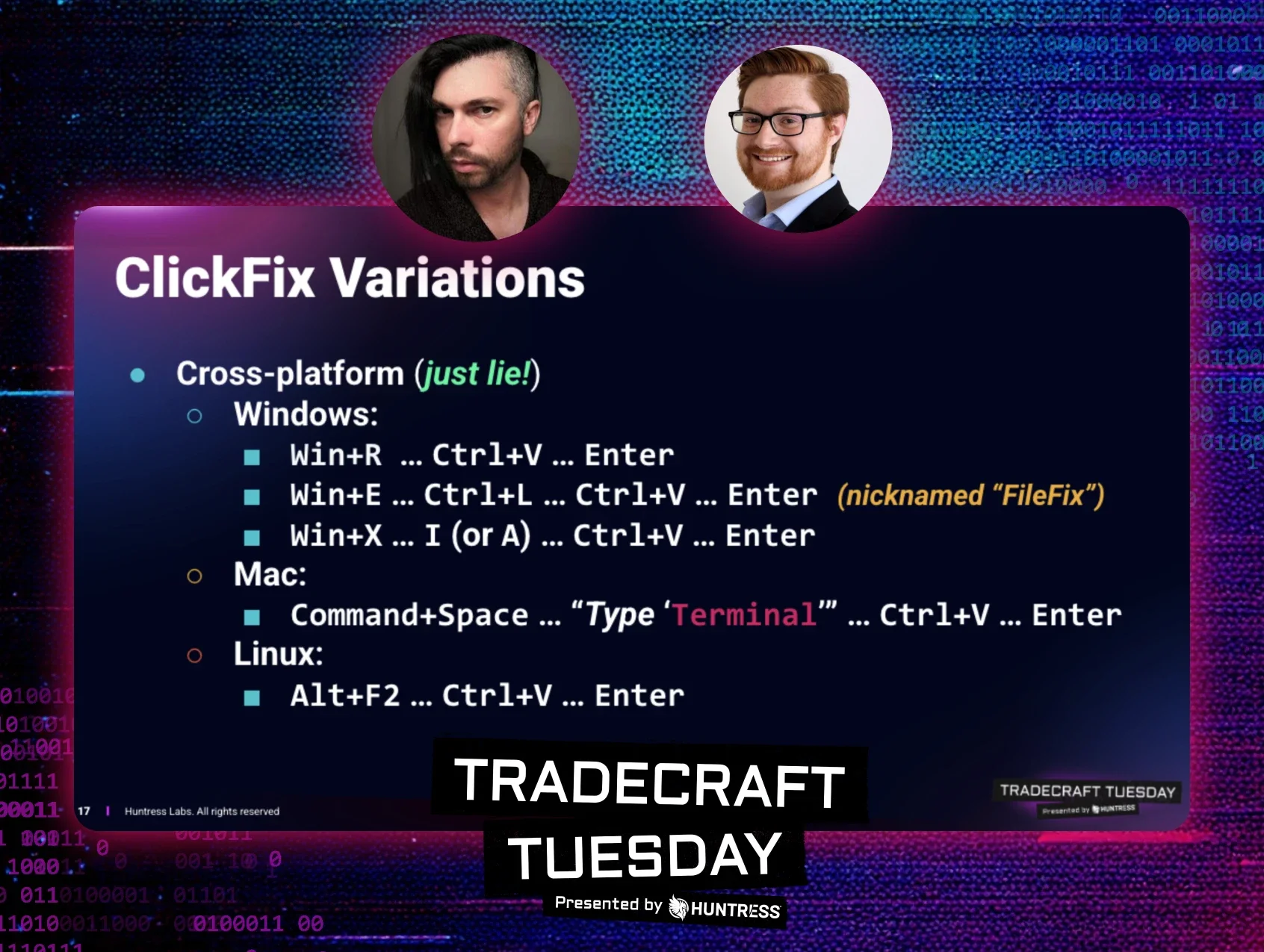
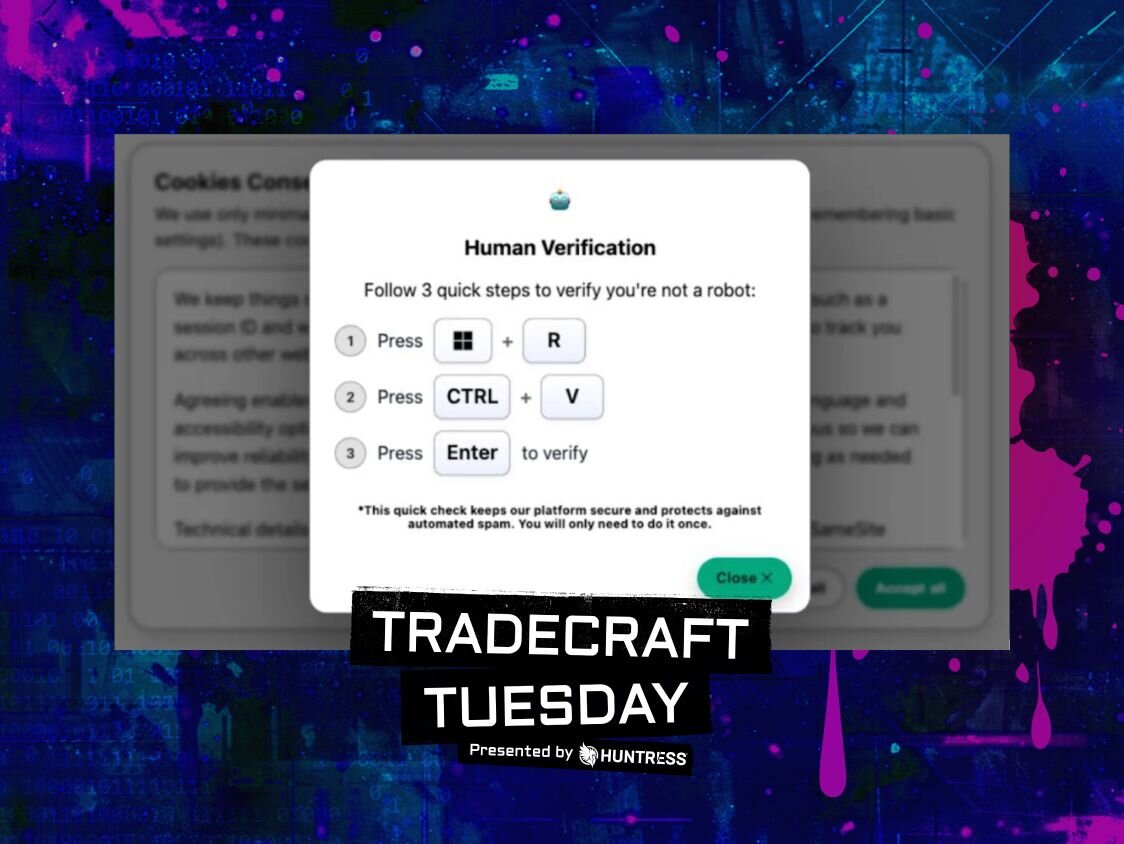
JH: “Some clever techniques that hackers are using these days are better obscuring phishing links, or taking advantage of a different vulnerability in a legitimate website to use as part of their attack chain.
A great example of this was the open-redirect vulnerability previously found in the Department of Health of Human Services website. While the website itself is served with secure HTTPS and a valid certificate and ends in an official .gov domain, bad actors could take advantage of a login redirect vulnerability to forward unknowing victims to a pre-crafted malicious site. And even hovering over the link as we are all trained to do, an innocent user might think they are going to a valid and legitimate website.”
SG: “Regarding the delivery of the ransomware, we are seeing that images are increasingly used to instruct the victim to disable certain security features—such as clicking on the Enable Content button to enable macros in Microsoft 365. The goal for any cybercriminal is to make detection harder as we need to use Computer Vision to extract relevant visual features—such as the text and the logos of the impersonated brands. Computer Vision is slow, costly and difficult to scale—cybercriminals know that.”
In your opinion, what are the most common causes that lead to successful ransomware attacks?
SG: “Cybercriminals rely on social engineering techniques to trick their victims. For example, business email compromise (BEC) attacks will usually impersonate a C-level executive of the targeted organization to trick the victims. It is also very common that targeted attacks convey a sense of urgency and exploit people’s fear. These malicious emails are crafted so that the victim has an emotional reaction—as opposed to a rational assessment of the email—to get their victim to take action and increase their chances of success.”
JH: “We often discuss what I consider to be the boring, basic and boilerplate best practices for cybersecurity hygiene. Things like ‘use complex passwords, enable MFA everywhere, patch your systems, don’t click on email links or plug in USB drives,’ etc. I resonate with individuals who say they already know all this—everyone has said that before, and everyone says it over and over again.
The reason the security industry keeps shouting about these fundamentals is because we still continuously see that the start of attack chains rely on these trivial weaknesses. Too often, threat actors gain access to a network by an outdated application, or reused and shared credentials, or by repeatedly taking advantage of human vulnerabilities (social engineering). Ransomware incidents require only one initial foothold, and unfortunately, that is all too easy to do because we keep overlooking the basics.”
What advice would you give defenders looking to mitigate email-based threats?
SG: “There is no 100%, bulletproof solution to security. It’s important that employees are evaluated periodically and trained in consequence to detect and report targeted threats. It is particularly important to focus on employees who have access to key assets such as bank accounts, HR data and contracts, as they are more likely to be targeted. Employees should play an active role and constitute a last line of defense within the organization.”
JH: “For email-based threats specifically, there absolutely has to be some form of automated prevention or data inspection in place. Granted, automated solutions are not a silver bullet or a magic wand, but they set the foundation and the number of potential attacks you see with that in place is significantly less than what you would see without. Email attachments should be scanned and vetted before they reach an end user’s inbox, external links should be analyzed if they are not from a whitelisted domain, messages that are just an image or have no text whatsoever should be blocked… there are a number of things that can be done prior to delivery.
If, for whatever reason, a nefarious email does enter an end user’s inbox, then we have to fall back to that weak ‘user education’ piece. Again, relying on the human element is a weak dependency, but at minimum end users should forward suspicious emails to their security department and never interact with the email if they have any doubt or hesitation.”
Learn More
Interested in learning more about the ransomware lifecycle and the role email plays in the attack chain? Watch our on-demand webinar, The Ransomware Lifecycle: From Email to Infection, to hear more insights from experts John Hammond and Sébastien Goutal.