Everyone has heard the saying that “time is money,” but there is one big difference between the two: you can’t make more time, so you need to spend the time you have wisely.
Now, this blog could go in a much more philosophical direction, but we’re not in the philosophy business. We’re in the business of improving the cybersecurity experience for small and medium-sized businesses, which is why we’ve rolled out a new way for you to save some more of that precious time: Auto-Remediation for low-severity incidents.
What Is Auto-Remediation for Low-Severity Incidents?
With Auto-Remediations, Huntress can automatically remediate low-severity threats like potentially unwanted programs (PUPs) or malware artifacts as soon as they are identified by our SOC. No further action is required from your team, which means you can save time by foregoing the approval process for low-severity incidents and remediate threats before they turn into a bigger problem.
Why Low-Severity Incidents?

Low-severity incidents are the most prevalent type of incidents we see across our managed endpoints. In fact, low-severity incidents take up over 60% of all incident reports sent out by Huntress. When you factor in that it takes an average of over 10 days from the time a low-severity incident is sent to it being approved and remediated by our customers (even with our Assisted Remediation feature), that's a significant amount of time that could be spent on other aspects of your business, not to mention less time wasted taking care of these incidents before they turn into something more critical.
While catching these low-severity incidents before they can become something more serious is always a good thing, the time it takes to remediate them can be seen as a nuisance to already time-strapped security teams. Nonetheless, it is still proper cyber-hygiene to remediate these incidents in a timely fashion, which is what led to the creation of our Auto-Remediations feature.
By opting into Auto-Remediations, you can reduce the overall amount of time it takes for you to resolve incidents by over 90%. In turn, you’ll bolster your security posture by having these incidents remediated as soon as they’re identified by our 24/7 SOC.
How Does It Work?
Historically, the process for remediating low-severity incidents was through our Assisted Remediation feature. This entailed the Huntress SOC identifying incidents like PUPs or malware artifacts, and then sending you the remediation steps for your approval. Once the remediation steps were reviewed, they could be approved through the click of a button that then kicks off the remediation.
This is a fairly painless process, but it still requires that you take the time to review the steps and give approval.

All the while, those unwanted programs (however low-level they may be) are still sitting on the endpoint until the remediation has been run.
With Auto-Remediation, everything is still reviewed by our 24/7 SOC and you will still receive a full incident report, but you now have the option to give prior approval to remediate any incidents that fit the low severity criteria. This means you can have those pesky PUPs and malware artifact files remediated as soon as they’re identified, without spending any additional time on them.
What We’ve Seen So Far
We’ve had plenty of partners opt into Auto-Remediations already and their results are pretty telling.
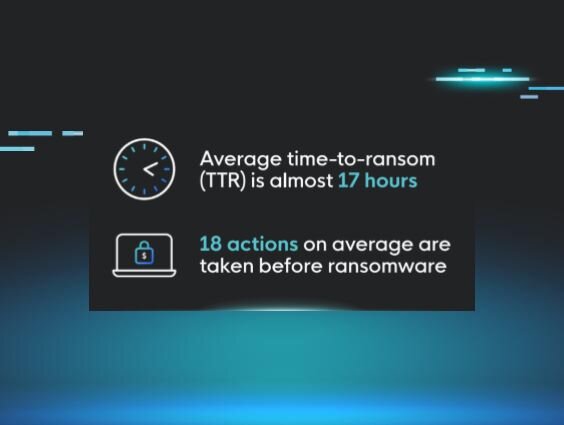
Before Auto-Remediations became available, the average time it took for an incident to be resolved after it was sent to a partner (across all levels of severity) was 10 days. With Auto-Remediation, we have seen that overall average drop to 19 hours. That is a staggering 92.5% reduction in the average time it takes to close an incident, which greatly reduces the risk of a low-severity incident turning into a more critical threat and is a significant amount of time that your team gets back in their day.

Why Opt Into Auto-Remediations?
If you find that you are spending more time than you’d like tending to low-severity incidents when you have other priorities that need your attention, then we recommend opting into Auto-Remediations.
At the end of the day, your time is worth what you spend it on, so why not focus on things that will help you see real value, and let Huntress handle the rest?
Take Managed EDR for a test drive and experience the power of endpoint protection, detection, and response backed by our team of human security experts.