Warren Bennis, a leading expert on leadership, once made a profound statement regarding trust:
"Trust is the lubrication that makes it possible for organizations to work."
Clearly, Mr. Bennis didn't work in cybersecurity. 😬
In fact, being too trusting of activity happening in your IT or managed environments is downright dangerous.
Recent cyberattacks prove that a breach or exploit can cost a business far more than money. Reputation and credibility are often permanently tarnished as fingers are pointed following an attack. In the long run, it's easier (and less expensive) to scrutinize, question, and verify the validity of everything happening in your network.
There's a name for that approach to cybersecurity: Zero Trust.
What Is Zero Trust Security?
The National Security Agency (NSA) has a pretty intricate definition of Zero Trust:
"Zero Trust is a security model, a set of system design principles, and a coordinated cybersecurity and system management strategy based on an acknowledgment that threats exist both inside and outside traditional network boundaries."
The Agency goes on to emphasize the elimination of implicit trust in this model:
"The Zero Trust security model eliminates implicit trust in any one element, node, or service and instead requires continuous verification of the operational picture via real-time information fed from multiple sources to determine access and other system responses."
In simpler terms, the Zero Trust Security Model disregards implicit trust and reverses the philosophy of trust, then verify. In the Zero Trust Security Model, trust must be earned across all people and devices, whether they're internal or external to a network.
Why Zero Trust?
At first glance, it may seem like Zero Trust is almost too mindful of threats. No user or device inherits implicit trust. Why all the extra concern?
There are quite a few good reasons to adopt a Zero Trust approach to security.
1. Cybercrime is expensive
Not being cautious enough is far more expensive than being overly cautious.
Cybercrime is predicted to cost the world $10.5 trillion annually by 2025—representing what will be the third-largest economy in the world. Threat actors are experts at finding their way into secure environments—it's what they do. It makes it that much easier for them when all they have to do is gain entry into an environment to garner immediate trust network-wide.
2. Today's remote workforce demands it
Another reason to adopt a Zero Trust mindset is to keep up with the demand from today's largely remote or on-the-go workforce.
In years past, cybersecurity looked completely different from how it looks today. Companies contained their network of systems within corporate data centers, and employees largely accessed these systems by logging into a secure network on-site. It's just not like that anymore.
Nowadays, many organizations rely on a mixture of on-premises and cloud-based systems to house their applications, which are then accessed by employees and other stakeholders—sometimes from different locations across the globe. Now, it's more the exception than the rule when a cybersecurity specialist can walk across the hall to make sure a failed log-in attempt was only an accident by an authorized user and not something—or someone—more malicious.
3. It helps to identify shady wooden horses
Need another reason to be open-minded about Zero Trust? Let's talk about the Trojan War. (No, really.)
Though a tale from Greek mythology, the Trojan War gives us a pretty good example of why Zero Trust makes sense in today's cybersecurity landscape. The story goes that the Greeks used a wooden horse—a Trojan horse—to infiltrate the city of Troy to win the war. A number of soldiers hid inside the horse, and the horse was pulled into Troy to mark what the Trojans believed was their victory—that is, until the Greek soldiers snuck out of the horse and destroyed the city of Troy.
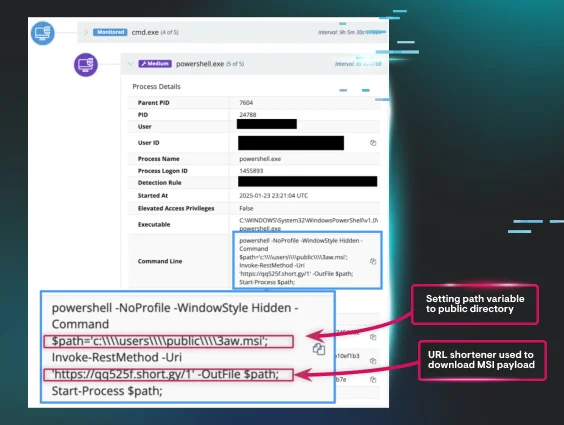
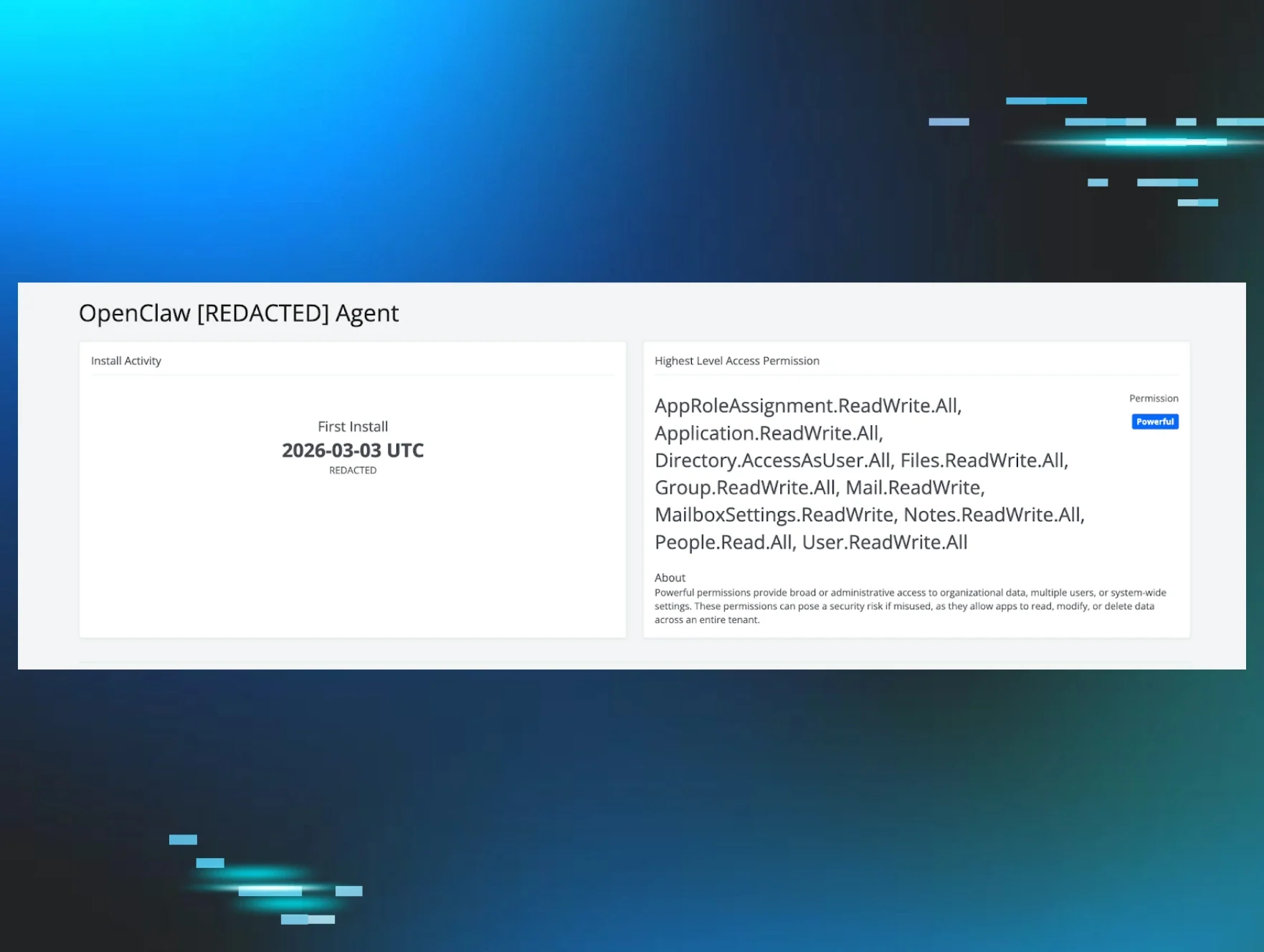
Similarly, your network receives many "wooden horses" over time in the form of application updates, vendor updates, and other items that typically scream business as usual. You don't want threat actors to hop out of one of those wooden horses and wreak havoc on your environment when you're not looking.
Without a Zero Trust mindset, your team would fully trust these updates and not think anything of them—and that's exactly how the mass exploitation of on-prem Microsoft Exchange servers happened in March 2021. Few people without a Zero Trust mindset figured they'd need to double-check an update from Microsoft—a generally trusted security vendor. As a result, the updates went through, and boom—their servers were compromised.
A Zero Trust approach, on the other hand, would have required careful verification of the updates after they were installed, checking system and network functionality against recorded baseline measurements. The exploit could have been caught much earlier with a Zero Trust mindset—and much of the damage could have potentially been mitigated.
Legacy security vs. Zero Trust: a comparison
Aspect | Legacy Security | Zero Trust Security |
Trust Model | Implicit trust once inside the network perimeter | No implicit trust; continuous verification required |
Network Perimeter | Strong perimeter defense; weak internal controls | No assumed safe zone; all access points secured |
Access Control | Broad access once authenticated | Least-privilege access; granular permissions |
Verification | One-time authentication at entry | Continuous authentication and authorization |
Threat Assumption | Threats come from outside the network | Threats exist both inside and outside the network |
Monitoring | Limited internal traffic monitoring | Comprehensive logging and inspection of all traffic |
Real-world benefits of implementing Zero Trust
Organizations across industries have seen tangible benefits from adopting Zero Trust principles:
Financial Services: A major bank implemented Zero Trust architecture and reduced security incidents by 60% within the first year. By requiring continuous verification for all users and devices, they caught insider threats that would have gone unnoticed under their legacy security model.
Healthcare: A regional healthcare system adopted Zero Trust to protect patient data across multiple facilities. They achieved HIPAA compliance more easily and prevented unauthorized access to electronic health records, even when credentials were compromised in a phishing attack.
Manufacturing: A global manufacturer implemented Zero Trust to secure their operational technology (OT) environments. When ransomware infiltrated their corporate network, the strict access controls prevented it from spreading to production systems, avoiding costly downtime.
Government: A federal agency transitioned to Zero Trust architecture to support remote work during the pandemic. They maintained security while enabling employees to access sensitive systems from home, without the vulnerabilities of traditional VPN solutions.
Getting started with Zero Trust security
Zero trust is as much of a mindset as it is architecture. To implement the Zero Trust Security Model, you have to fully embrace the mindset that nothing is safe until it's proven to be safe and to err on the side of assuming compromise.
Operationally, the Zero Trust Security Model requires the following:
Define mission outcomes, including the organization's critical data, assets, applications, and services (DAAS)
Design from within, meaning to begin with protecting the DAAS and then securing the paths to access them
Create access control policies to the DAAS to give required access to the people and applications that need it to perform their respective duties
Inspect and log all traffic to monitor activity across endpoints and flag anything suspicious
Frequently asked questions about zero trust
What is Zero Trust?
Zero Trust is a security model that eliminates implicit trust in any user, device, or network location. Instead of assuming everything inside a network is safe, Zero Trust requires continuous verification of every access request, regardless of where it originates. Think of it as "never trust, always verify."
How do you implement Zero Trust?
Implementing Zero Trust involves several key steps:
Identify your critical assets: Determine what data, applications, and services need the most protection
Map data flows: Understand how information moves through your organization
Architect your network: Design micro-segments around your critical assets
Create access policies: Implement least-privilege access controls based on user identity, device health, and context
Monitor continuously: Deploy logging and analytics to detect anomalies in real-time
Automate responses: Use automation to respond quickly to potential threats
Start small with your most critical assets and expand gradually. Zero Trust is a journey, not a destination.
Why is Zero Trust important?
Zero Trust is critical because traditional perimeter-based security no longer works in today's environment. With cloud computing, remote work, and mobile devices, there's no longer a clear "inside" and "outside" to your network. Cybercriminals have become sophisticated at breaching perimeters, and once inside, they can move laterally across systems.
Zero Trust protects against both external attacks and insider threats by assuming that compromise is inevitable and building defenses accordingly. It's not about being paranoid—it's about being prepared.
What is NOT a principle of Zero Trust security?
Implicit trust based on network location is NOT a principle of Zero Trust security. In legacy security models, users and devices inside the corporate network were automatically trusted. Zero Trust explicitly rejects this assumption.
Other concepts that are NOT Zero Trust principles include:
Trusting all internal traffic by default
One-time authentication provides permanent access
Assuming users with valid credentials have good intentions
Treating all users equally, regardless of risk factors
How do you build a Zero Trust network?
Building a Zero Trust network requires a strategic approach:
Step 1: Assess your current state
Inventory all assets, users, and data flows
Identify gaps in your current security posture
Understand your organization's risk tolerance
Step 2: Establish identity and access management (IAM)
Implement multi-factor authentication (MFA) for all users
Deploy single sign-on (SSO) solutions
Create role-based access controls (RBAC)
Step 3: Implement micro-segmentation
Divide your network into small, isolated segments
Apply strict access controls between segments
Limit lateral movement capabilities
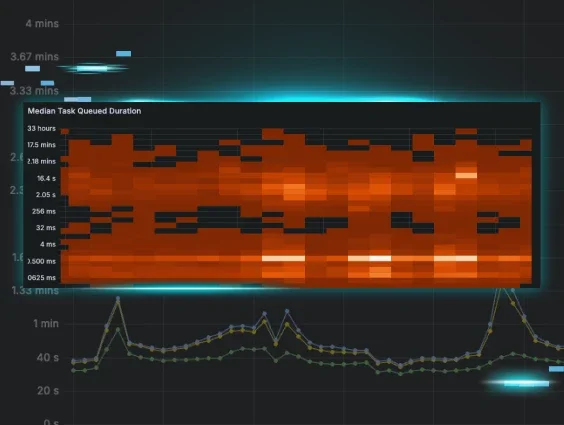
Step 4: Enable continuous monitoring
Deploy security information and event management (SIEM) tools
Implement endpoint detection and response (EDR) solutions
Establish baseline behavior to detect anomalies
Step 5: Enforce device security
Ensure all devices meet security standards before granting access
Monitor device health continuously
Isolate or block non-compliant devices
Step 6: Apply data protection
Classify data based on sensitivity
Encrypt data at rest and in transit
Implement data loss prevention (DLP) controls
Remember: building a Zero Trust network is an iterative process that requires ongoing refinement and adjustment.
Want to learn more?
Ready to dive deeper into Zero Trust? We recommend these resources: