Throughout 2024, politics has been top of mind for a significant portion of the world’s population. By December, over two dozen countries will have held elections, and scammers have been taking full advantage of this political climate. In the US, where voter engagement is particularly high, politically driven fraud is on the rise. Con artists are impersonating candidates and parties to trick voters into donating money to fake campaigns. We encourage you to get to know the different types of scams out there and learn how to identify them so you don’t fall victim to these traps.
What are Political Donation Scams?
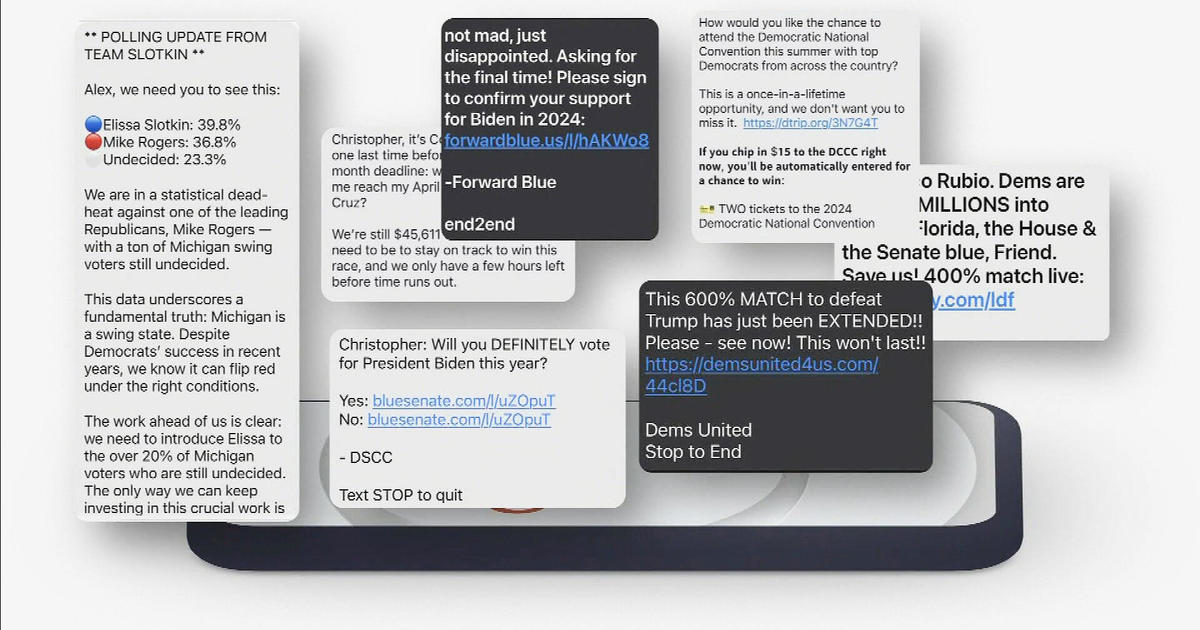
Political donation scams occur when someone pretends to represent a political party or candidate and solicits donations, usually through robocalls, emails, or social media. Scammers often already have access to your voting history and contact details, making their requests look legitimate. Their goal is simple—steal your money. If you’re not careful, scammers can trick you through fake websites or payment methods like wire transfers, gift cards, or apps like Venmo or Zelle.
Common Tactics Used by Scammers
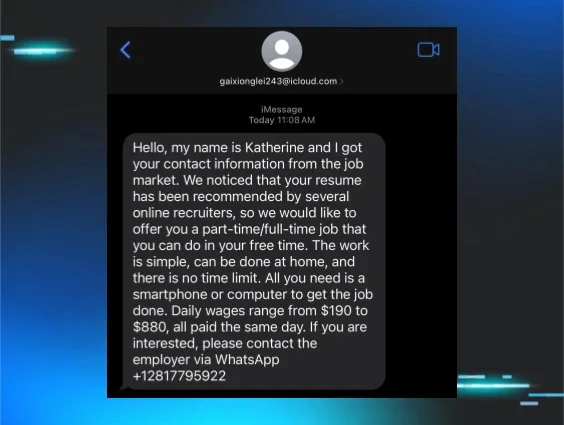
Robocalls and Text Messages
Robocalls and text messages are frequent tools used to solicit fraudulent donations. You might receive a recorded message that sounds like your candidate urging you to donate—but it’s fake. The provided donation link will take you to a fraudulent site. These methods exploit voters’ trust and familiarity with political outreach.
Deepfakes and Voice Cloning
Scammers are now using deepfake videos and voice cloning technology to make their schemes more convincing. They can clone the voice of a politician, using it in calls to make their message appear authentic. During the 2024 New Hampshire primary, there was a documented attempt to use voice cloning to influence voters.
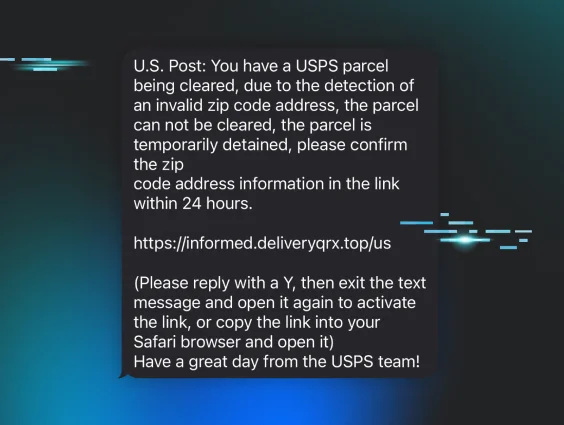
Fake Websites and Payment Methods
Scammers create websites that look identical to official campaign sites to collect donations. These sites can be tricky to differentiate from the real ones, and payments through wire transfers, gift cards, or apps like Venmo or Zelle are nearly impossible to recover once sent.
Address Registration Scams
Another tactic involves pretending to assist with voter registration. Scammers will ask for your personal information, which they then use to commit identity theft. Be wary of unsolicited offers to "help" register or update your information.
Fake Surveys and Polls
Scammers use fake surveys and polls to collect personal information, sometimes offering rewards to get you to participate. However, these surveys often require payment information, which is used for fraudulent purposes. If you decide to participate in a poll or survey, do NOT give out any personally identifiable information (PII) like your name, contact information, social security number, or date of birth. And certainly don’t give any payment information or “just pay for shipping” to “claim your reward.”
How You Can Avoid Political Scams
These scams can be convincing, but there are steps you can take to protect yourself:
- Ignore unsolicited messages: If you didn’t ask for it, don’t engage with it.
- Verify donation links: Go directly to the candidate’s official website or call their office.
- Use a credit card for any political donation: This offers extra protection and dispute options if you get scammed.
Look Out for Red Flags
Scammers rely on urgency to push you into performing an action. They’ll frame their requests as urgent, claiming the immediate need to secure your vote or protect democracy. Slow down, take a deep breath, and verify before making any donations or sharing personal information.
Conclusion
Election season is a prime time for scams, but staying informed and cautious will reduce your risk of becoming a victim. Don’t engage with unsolicited messages, verify the sources of donation links, and never share personal details with unverified contacts. If you suspect a scam, report it to the authorities and always rely on verified channels when engaging in the political process.