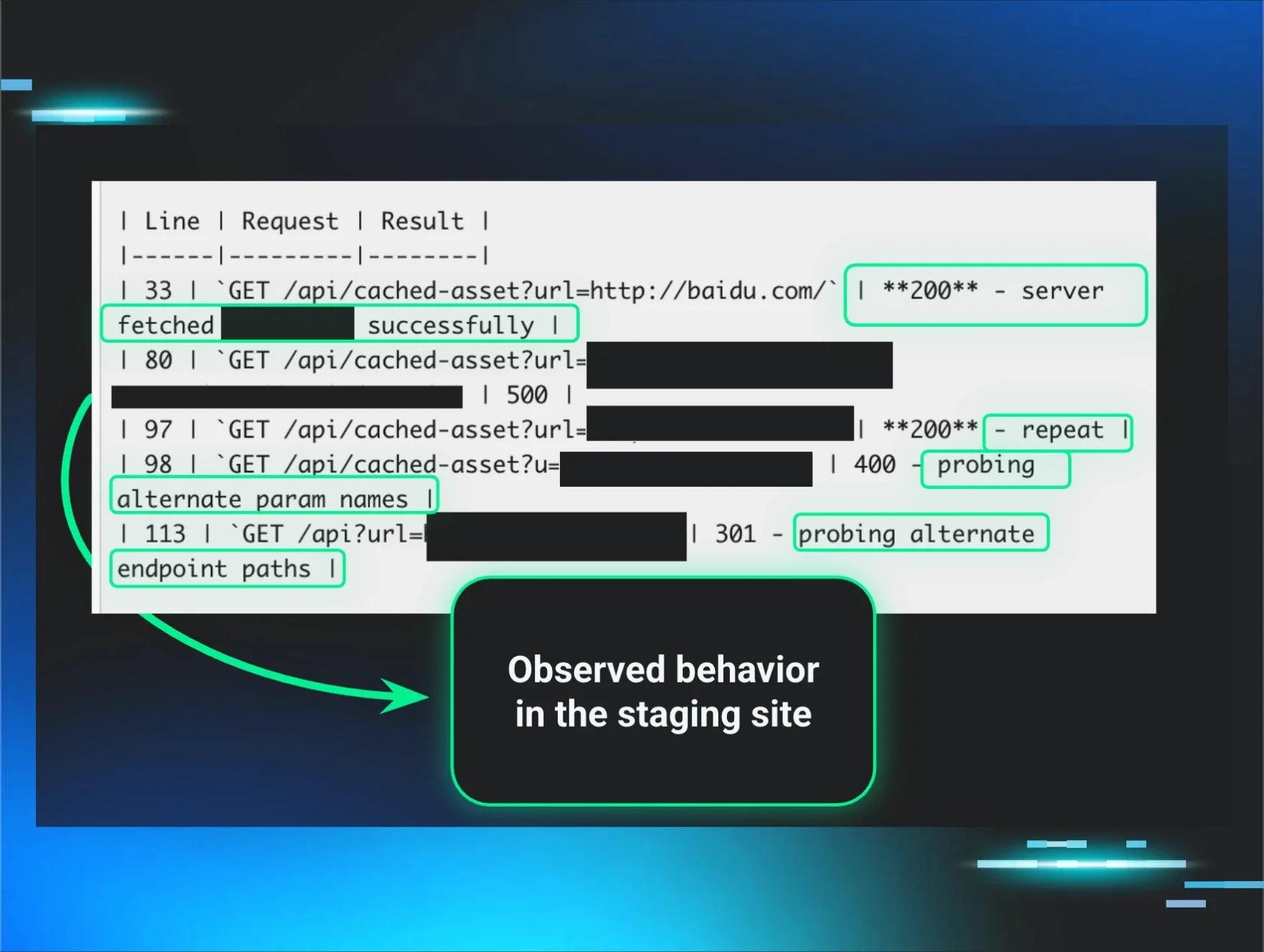
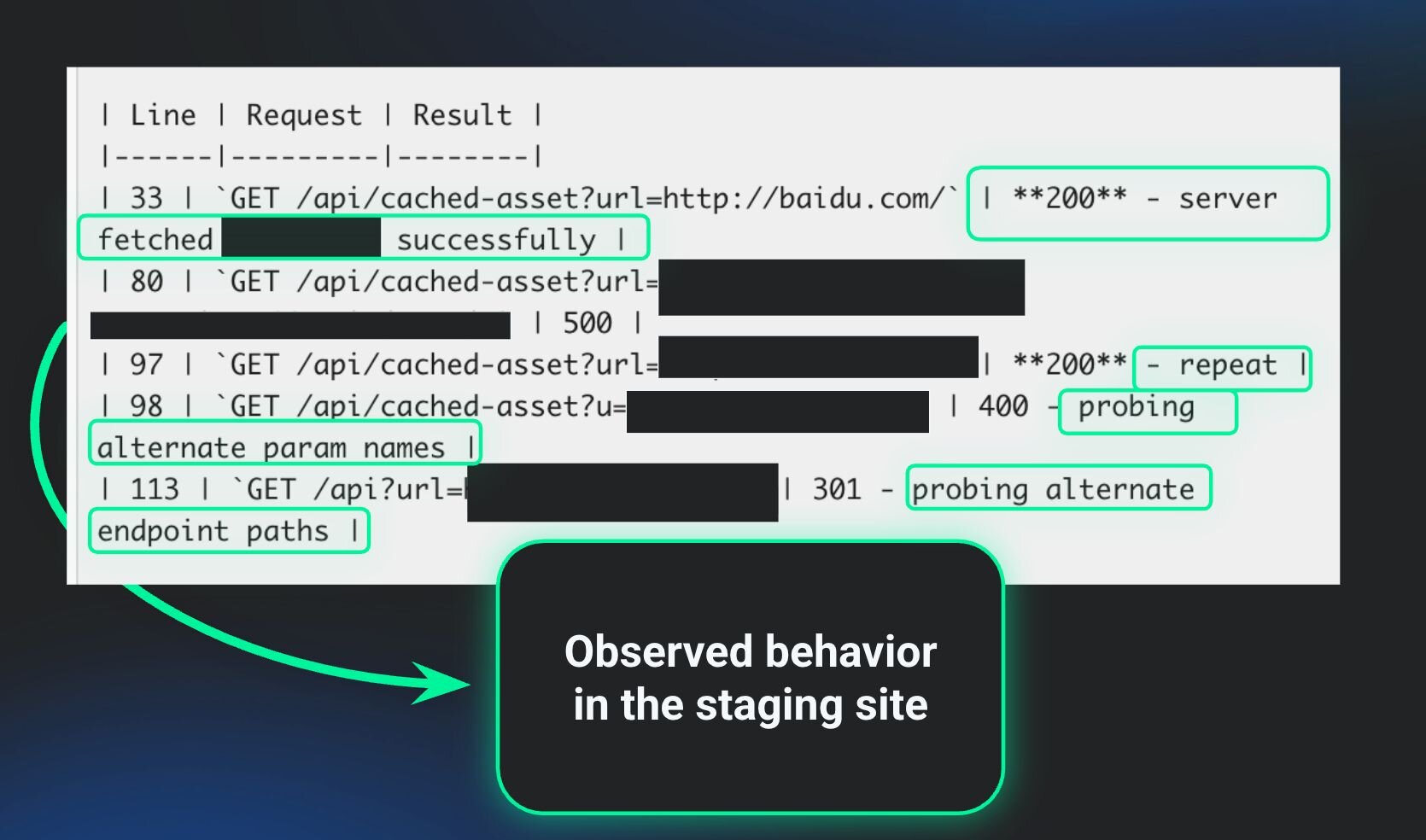
A third-party security researcher recently found a vulnerability in our staging environment.
That’s not a fun sentence to write, even when the person finding it is part of a “bug bounty” program and operating with permission. Still, moments like this are useful tests. They reveal whether your security posture works the way you think it does.
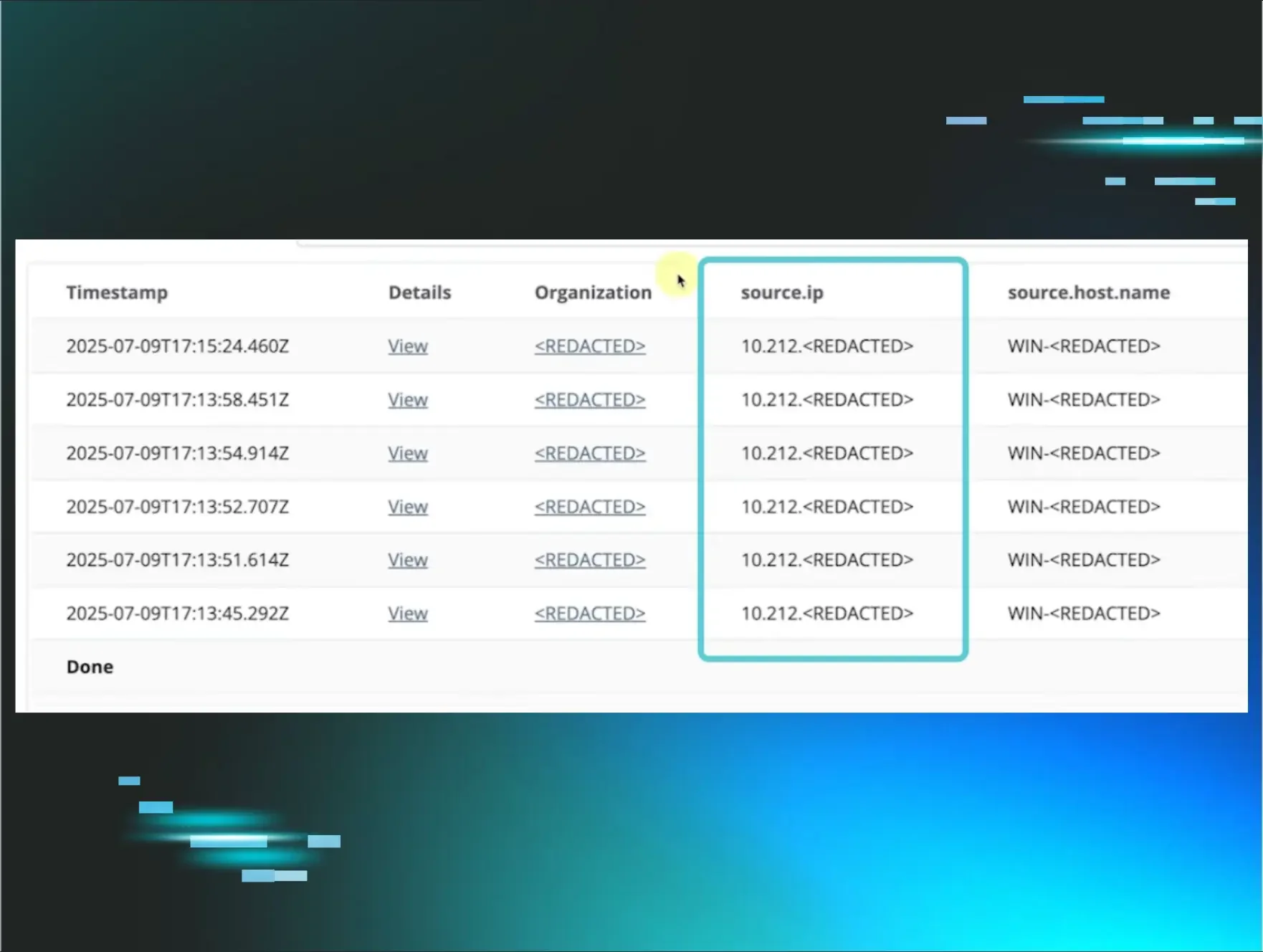
In our case, it did. Our team was alerted to the issue and fixed it within minutes. In fact, the vulnerability was remediated before the researcher could even send us the report. Better yet, there was no customer impact, no material compromise, and no messy cleanup afterward.
Even so, the experience was a good reminder of something plenty of businesses still underestimate: attackers aren’t only focused on the systems you care about most. They look for the places you treat as secondary, and staging environments often fall into that category.
Most companies deliberately spend less on protecting staging. Since it’s not production, it doesn’t always get its fair share of budget, scrutiny, or monitoring. Over time, that creates something closer to a Petri dish than a workspace, growing wild with weaker oversight, older components, stale integrations, or access paths that made sense in a bygone era and were never revisited.
That’s part of what makes these environments attractive to attackers. A staging site, dev environment, old subdomain, or neglected web property can offer an easier way in than the systems you’ve locked down most aggressively. Once someone gets that initial foothold, they can start figuring out what’s connected, what’s exposed, and where they might be able to move next.
There’s a lesson here. Non-production environments can’t be treated like an afterthought. The name doesn’t matter nearly as much as the access, connectivity, and visibility around it. If a system is reachable and useful, it deserves attention, regardless of whether it sits in production or adjacent to it.
This is also a good reminder that no business should opt out of being tested, including cybersecurity companies. If your business is connected to valuable systems, somebody’s going to test your defenses. In the best case, it’ll be a skilled researcher working within the rules. In the worst case, however, it’ll be an adversary with patience and a habit of looking where others don’t.
There’s a line often misattributed to Abraham Lincoln:
“Give me six hours to chop down a tree, and I will spend the first four sharpening the axe.”
Whether he said it or not is irrelevant, but this quote still sticks. Attackers are persistent. The companies that respond well aren't the ones that get lucky, but they're the ones that do the unglamorous work before anything goes wrong.
It’s absolutely vital to treat security as an operational capability, not a pile of disconnected tools. You need visibility across your environment. You need to know what’s exposed. And you need people and processes that can move fast when something looks off.
It’s too bad many businesses aren’t set up that way. They may not be watching non-production environments closely, or they may not know what those environments connect to. Plus, they may not have the staff to investigate and remediate in minutes. That’s how a small issue becomes a larger one.
For us, this was reassuring. It reinforced something we already tell customers all the time: your attack surface is bigger than your production environment, and staging is part of that reality, whether you treat it that way or not.
If there are any practical takeaways here, they’re to:
-
Treat staging like part of your real environment, because attackers already do.
-
Review what non-production systems can access, not just what they’re called.
-
Keep monitoring and visibility consistent across the areas attackers are most likely to test.
-
Assume gaps will be found, and build the ability to see them and close them fast.
-
Build an incident response plan, and practice, practice, practice.
Entry points are everywhere, and your coverage needs to reflect that.