The Stryker incident of March 2026 wasn't just another headline to skim during your morning coffee. As someone who spends my time helping leaders navigate the fallout of digital disasters, I can tell you, this is a watershed moment.
For years, we’ve discussed ransomware as the "final boss" of corporate risk. Stryker has shown us that there’s something faster, more permanent, and far more difficult to recover from: the Weaponized Remote Wipe.
First, what is Stryker?
Stryker is a $25 billion medical technology giant with over 56,000 employees across 60+ countries. They’re the backbone of modern healthcare, providing everything from surgical robotics to defibrillators.
When a company of this scale goes dark, it isn't just an "IT problem." It’s a patient safety crisis. If hospitals can’t receive surgical pins or replacement parts, surgeries are postponed. This incident sits at the volatile intersection of cybersecurity, global logistics, and real-world human health.
The attack: When your shield becomes a sword
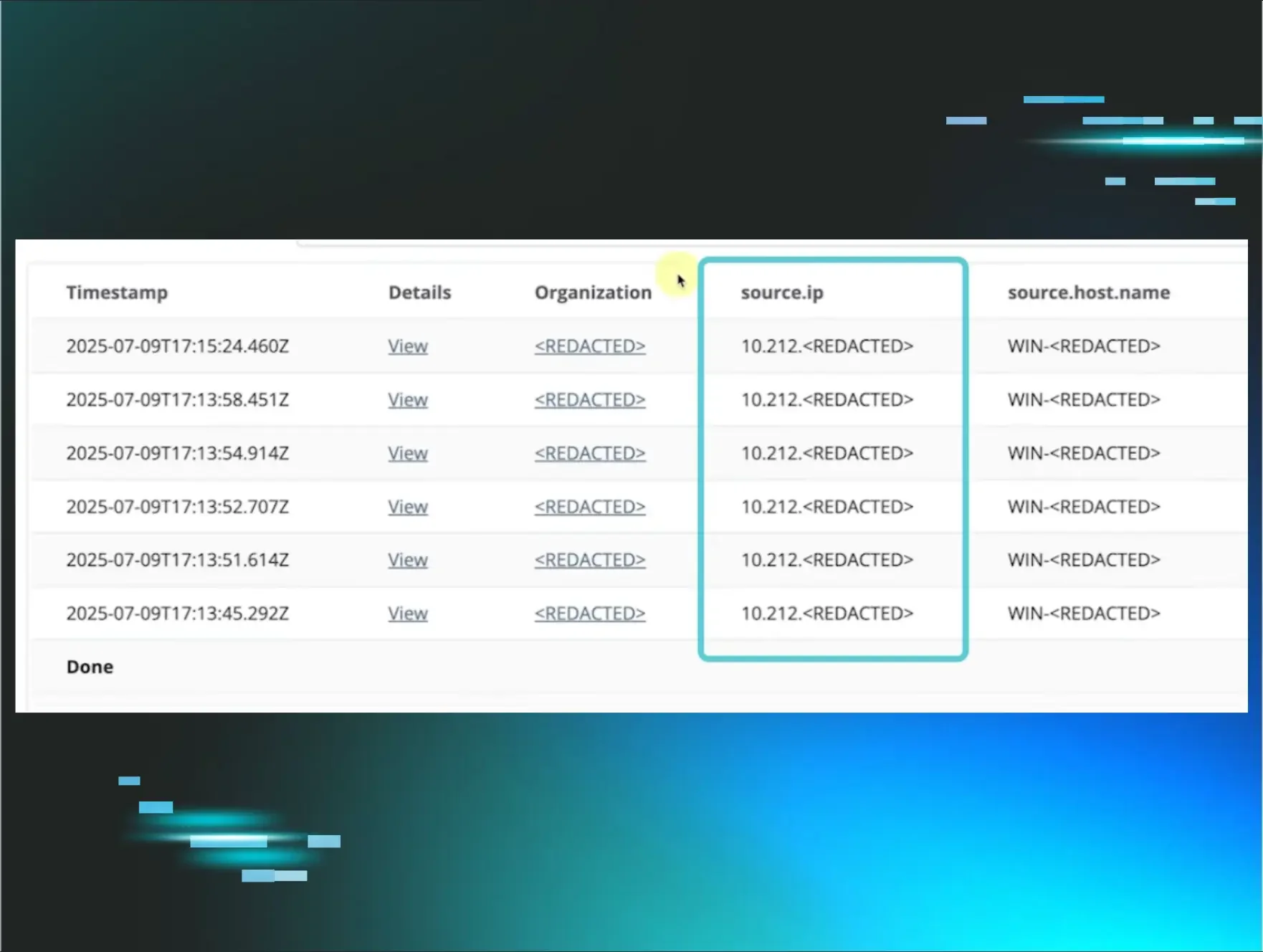
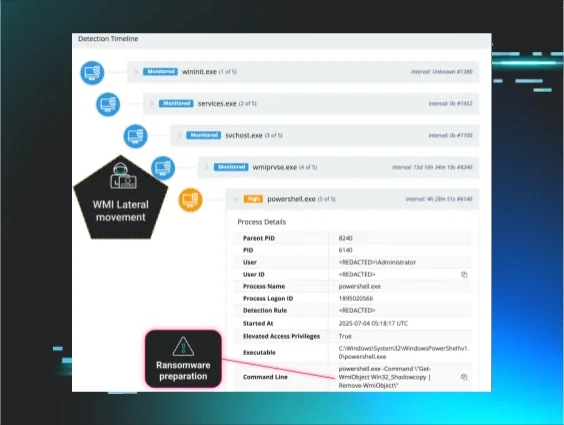
While Stryker hasn’t yet confirmed the exact technical specifics, the reported details suggest a "perfect storm." Attackers (linked to the pro-Iran group Handala) didn't need to bypass their firewall with complex malware. Instead, they reportedly bypassed the Identity Plane.
- The hijack: Attackers likely gained privileged access to Stryker’s Microsoft Intune/MDM environment, the very tool used to manage and secure their global fleet.
- The wipe: They issued a "Remote Wipe" command at an unprecedented scale. Reports suggest up to 200,000 devices from corporate laptops to employee-owned iPhones were factory reset in minutes.
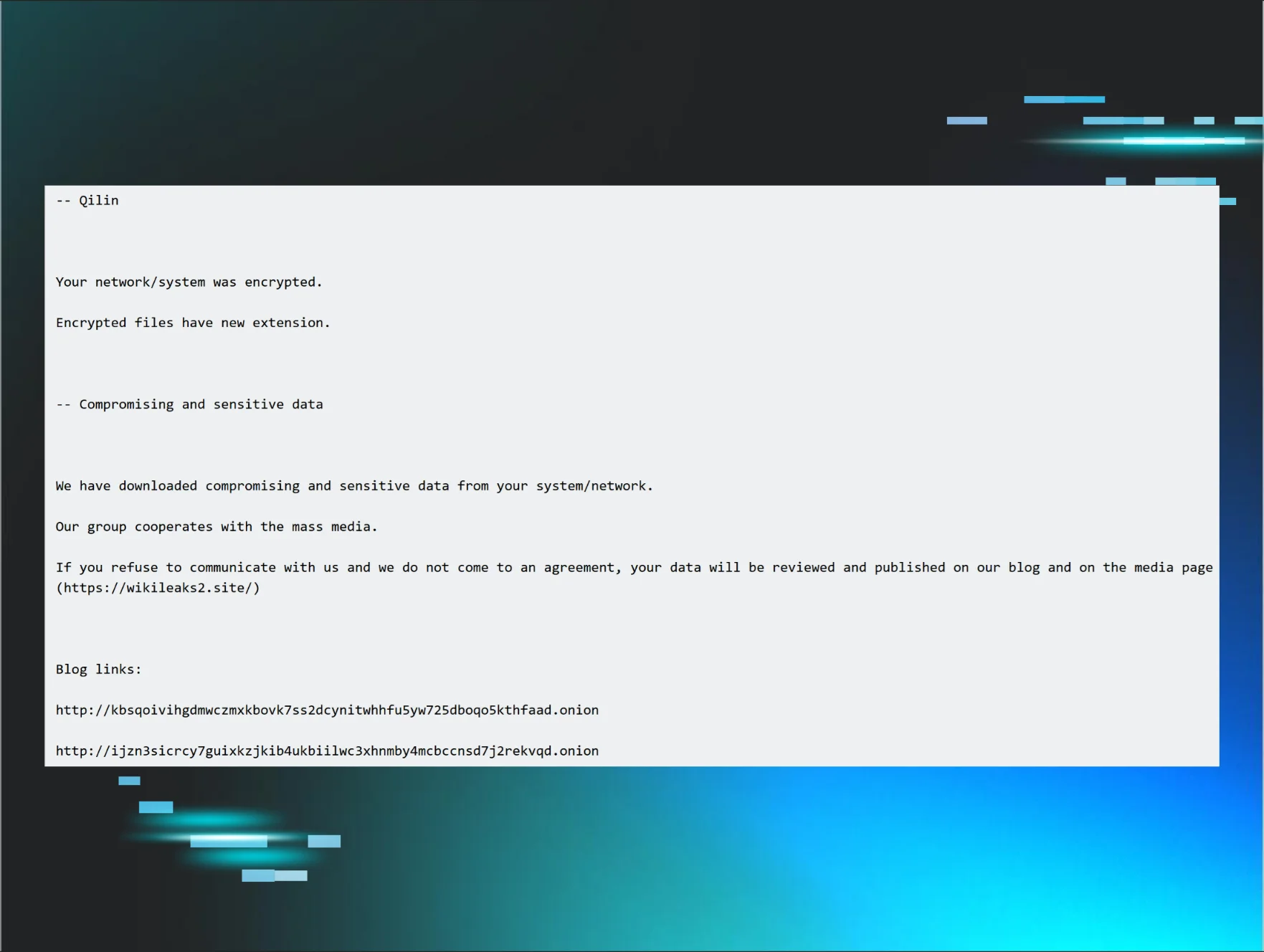
- The theft: While systems were being erased, the attackers claimed to have exfiltrated 50 terabytes of proprietary R&D, blueprints, and medical technology.
This is a structural failure of trust. The tools we treat as routine security measures were turned into a mass-destruction button.
Why this is significant
This is the first high-profile case where three forces aligned so visibly:
- Geopolitical "hybrid" warfare: This wasn't for a ransom. It was a retaliatory strike linked to Middle Eastern tensions. The UK’s National Cyber Security Centre (NCSC) has already warned that corporate networks are now collateral damage in international conflicts.
- Not a "restore" but a "rebuild": This isn't a ransomware recovery where you enter a key to decrypt. A factory reset means the data, apps, and settings are gone. You are now "bricked."
- The human toll: Because personal phones were enrolled in corporate MDM, employees reportedly lost years of personal photos and private messages. This creates an immediate, massive HR and legal liability.
The fallout: Customers, partners, and patients
The impact here is existential in the short term and reputational in the long term.
- Supply chain paralysis: The UK National Health Service (NHS) has already confirmed that Stryker is currently unable to receive orders. Everyday systems are down, millions in revenue are vanishing, and critical healthcare components remain stuck in warehouses.
- The recovery mountain: Stabilizing operations will take weeks. A full restoration of a 200,000-device fleet? That’s a three- to six-month journey. You cannot physically push that much data over the internet to every home office and hospital simultaneously without breaking the network.
- Regulatory hammer: With 50TB of potentially sensitive data breached, Stryker faces global regulatory scrutiny under certain regulations, which could trigger fines of up to 4% of global turnover.
Five concrete steps to take now
These are actions you can start on immediately, regardless of your size or sector.
1. Treat your management platforms as crown jewels
Anything that can deploy software, push configurations, or wipe devices must be protected like a high‑value asset.
-
Lock down Intune / MDM / RMM / EDR consoles / cloud admin portals
-
Use phishing‑resistant MFA (FIDO2 security keys) for all highly privileged identities; SMS and basic app‑based MFA aren’t enough against session hijacking and state‑aligned actors
-
Enforce strict role separation:
-
Separate day‑to‑day admins from “break glass” or destructive roles
-
Avoid shared admin accounts
2. Put brakes on destructive actions
Assume that any single account can be compromised. Your job is to make it hard for one compromised credential to destroy the environment.
For Intune and similar platforms:
-
Enable Multi‑Admin Approval (MAA) or equivalent:
-
Require a second independent approver for high‑impact actions (e.g., wiping more than N devices)
-
Set thresholds so “no single person can delete the company.”
-
Monitor and alert on:
-
Bulk wipes, mass profile changes, or large‑scale policy rollouts
-
Creation of new high‑privilege roles or service principals
3. Fix your BYOD and MDM story
The Stryker case reportedly involved personal phones being wiped because they were enrolled as fully managed devices. That’s a huge HR, privacy, and legal risk.
-
Audit your BYOD and Intune/MDM profiles right now
-
Where are you enforcing full‑device control on personally owned phones?
-
What consent notice or policy did users actually see?
-
Where possible, move to Mobile Application Management (MAM):
-
Manage work apps and data only
-
Preserve the ability to wipe corporate data without factory‑resetting personal content
4. Build and practice an out‑of‑band comms plan
Don’t wait for the day when your primary tenant is offline to discover you have no way to coordinate a response.
At a minimum:
-
Create a small, trusted comms group for your IR leaders:
-
Signal or WhatsApp group
-
Personal email distribution list
-
Store personal contact details for key responders outside corporate IT (e.g., printed, or in a separate password manager not tied to the primary SSO)
-
Run a 30‑minute drill:
-
Simulate “Microsoft 365 is down”
-
Force the team to re‑establish comms via the out‑of‑band channel
-
Capture gaps and fix them
5. Practice “day zero” restore at a realistic scale
Most organizations have tested restoring a database or a single application. Very few have rehearsed rebuilding an entire fleet.
Borrow from the scale of the Stryker incident:
-
Design a “Day Zero” exercise where you assume:
-
Your primary management platform is untrusted
-
Several thousand devices are wiped or need to be re‑imaged
-
Work through:
-
How you would stage and throttle re‑provisioning (you can’t realistically have 200,000 machines all pulling images at once)
-
Which sites and roles get priority
-
How you’ll re‑establish trust in identities, devices, and backups
-
Pay special attention to your backup management consoles:
-
If they live in the same identity or MDM ecosystem as the devices, you may be forced into slow, offline recovery modes
Closing thoughts
The Stryker incident is a watershed moment because it brings together:
-
Geopolitical pressure
-
Identity and management‑plane compromise
-
Real‑world impact on healthcare supply chains and patient safety
You don’t need to be a $10B med‑tech giant to learn from it. If you operate any centralized admin console—as an enterprise, MSP, or vendor—this is a preview of what can happen when those tools are turned against you.
Use this as a forcing function to:
-
Re‑evaluate your management plane protections
-
Strengthen BYOD and MDM hygiene
-
Practice how you’ll talk and operate when your primary platforms are dark
When the crisis hits, it won't be a clever PowerPoint that saves your organization. It’ll be the boring, well-rehearsed basics you choose to implement today.
You can follow live updates from Stryker here.