Since our founding in 2015, Huntress has been leading the charge in Managed Detection and Response (MDR), helping customers and managed security providers (MSPs) worldwide stay one step ahead of hackers. But what’s our secret weapon? Put simply, we put the “R” in MDR.
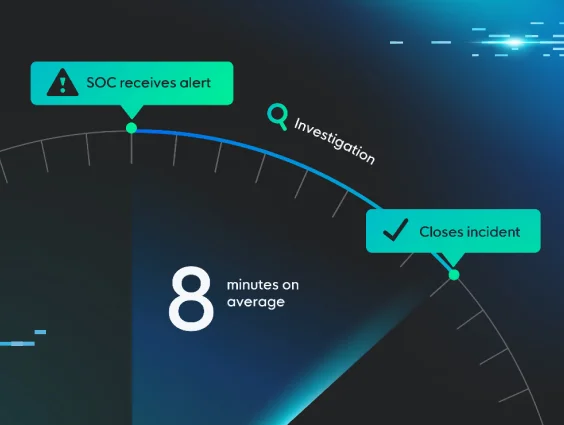
When you need us most, Huntress responds. Our suite of response capabilities—Host Isolation, Active Remediation, and Guided Cleanup and Recovery—is all about speed and effectiveness when facing threats. Many vendors forget that, bombarding their customers with endless alerts that only play into the hands of threat actors. In incident response, every second counts—both in kicking attackers out of your environment and in saving precious time from your packed schedule.
Before we dive into the breadth of our response capabilities and how we've meticulously tailored them to align with the incident response lifecycle, let's explore why quick response times are critical.
Time Decides the Victor
"Lost time is never found again."
- Benjamin Franklin
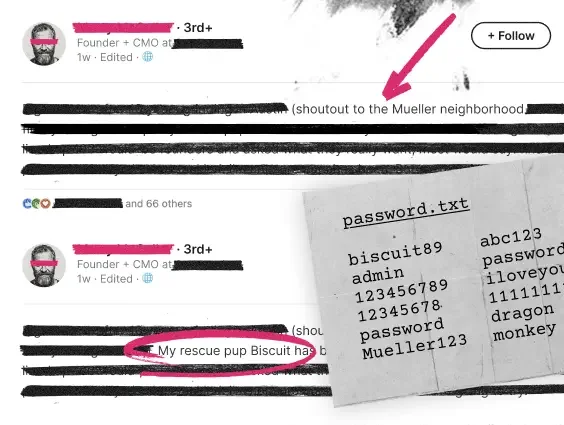
In the ongoing battle against attackers, one thing remains true: time decides the victor. Let’s face it, on a long enough timeline, hackers will break through your defenses. Why? Your attack surface is more vulnerable than ever due to shifts in meeting diverse business demands, all while security resources remain limited. Meanwhile, attackers operate with blazing speed and precision, creating a recipe for an inevitable breach.
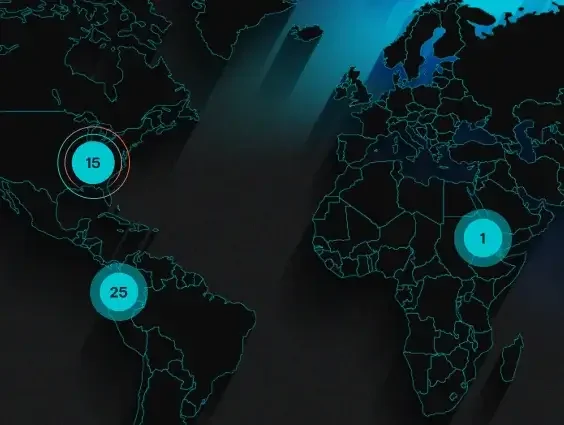
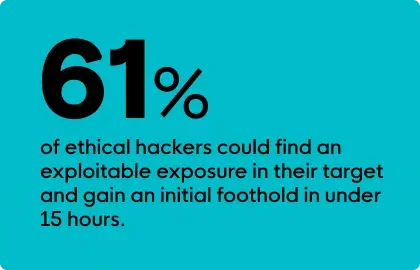
Consider this recent study by the SANS Institute. They asked ethical hackers (the good ones) how quickly they could find an exploitable exposure in their target and gain an initial foothold. The results were astounding—61% of these ethical hackers indicated they could accomplish this feat in under 15 hours.
But it gets worse. The timeframe for achieving their objectives accelerates once they break into the environment. In fact, an end-to-end attack can be accomplished in under 25 hours by 57% of attackers. It’s important to note that these are attackers operating within ethical boundaries. What about the ones we face in the real world where corruption thrives?
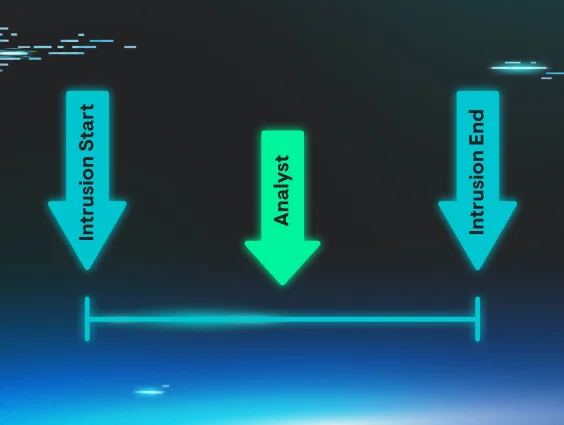
This is where MDR, a solution designed to minimize threat actor dwell time, comes into play. MDR acknowledges that attackers will inevitably break through preventative measures. The key is to stop them before they can achieve their objectives. Once again, time is the deciding factor.
Shifting the Time Advantage in Your Favor
So, what does Huntress bring to the table? Response where it’s needed most.
Let's walk through the incident response lifecycle and how Huntress’ approach makes time work for you, not against you.
| How Huntress Helps | |
|---|---|
| Identifying and Assessing the Threat | You can’t tackle what you can’t hunt. Fortunately, our track record does the talking—a whopping 98.5% customer satisfaction rate! We’re exceptional at spotting threats. Our secret sauce? Purpose-built detections, outstanding threat investigators, and a false positive rate of less than 1%. Translation: when we find a threat, it’s not a maybe—we take action. Whether it’s a sneaky advanced persistent threat (APT) or a mischievous lateral movement, we’ve got it covered. |
| Containing the Threat | Ok, we've spotted the threat—what's next? Every second counts at this critical juncture. When we detect a threat, we're on it—24/7, every day of the year. But here's where we stand out: unlike many MDR providers who depend solely on automated systems that might mistakenly isolate critical operations, our approach at Huntress includes a crucial human element. Our dedicated Security Operations Center (SOC) staff personally handles threat isolation. This prevents any further spread within your network and avoids the disruptions that automated systems can cause. Our precise, human-guided containment measures buy precious time to assess the situation and decide on the next steps. |
| Active Remediations to Eradicate the Threat | We don’t stop at containment. Unlike many MDR providers that contain a threat and throw an alert over the wall, we take it further. We empower you with choices. You can pre-authorize our SOC to automatically execute remediation actions on your behalf. This approach optimizes for speed and convenience. Not only does this reduce the attacker's timeline, but it also decreases the likelihood that you’ll have to get out of bed, interrupt your vacation, or skip out on dinner when we detect suspicious activity. Time matters outside of work, too! Or maybe you want to play it safe initially—no worries. Our “click-to-approve” feature lets you review each case individually and then respond with a touch of a button. Trust isn’t built overnight, but our track record—backed by that impressive <1% false="" positive="" rate—speaks="" volumes.="" as="" we="" work="" together,="" you’ll="" see="" firsthand="" how="" our="" active="" remediations="" swiftly="" neutralize="" threats.="" gain="" confidence="" in="" approach="" and="" will="" want="" to="" leave="" the="" for="" us="" handle.<="" td=""> |
| Recovering and Restoring Operations | While containing and eradicating threats is crucial, our commitment doesn’t end there. We recognize that helping organizations clean up and recover is equally vital. Here’s how we go the extra mile:
|
| Learning from the Incident | We’re not just about response, we’re all about learning from the trenches. With millions of endpoints under our watchful eye, we observe a fascinating array of novel, innovative attacks. But here’s the kicker: once we spot them, we don’t just pat ourselves on the back. We roll up our sleeves and create protective measures that benefit everyone. We can do this because we own our own technology and can adjust it on the fly. So, while the bad guys get crafty, we’re busy making sure our clients stay one step ahead. |
Visualizing the Outcomes
While all of this may seem a bit complex, it’s not. Attackers have traditionally had the time advantage, but with Huntress, we make the advantage yours. Let's take a simplified look at how we keep you protected when it matters most.
| Threat Containment | Active Remediation | Guided Cleanup & Recovery | |
|---|---|---|---|
| What we do | We provide around-the-clock intervention to prevent the spread of the attack on your behalf. This crucial action allows you the opportunity to review our reports and give your approval for our automated remediation measures to fully eliminate the threat. | We provide you with the flexibility to permit Huntress to execute remediation actions that remove identified threats from the technology under our care. Should you prefer not to authorize remediations in advance, you retain the option to utilize our “click-to-approve” feature. | After successfully containing and removing the threat from the technology under our care, we offer further detailed recommendations to assist in clearing any remnants of the threat actor and strengthening any weaknesses in security measures. |
| The Outcome | Quickly stop the spread | Eliminate the threat | Return to normal/more resilient state |
| Actions We Take |
Endpoint Detection and Response (EDR): Host isolation
|
|
|
Beware of the Pretenders: Not All “R” is Created Equal

Unfortunately, the MDR vendor landscape is like navigating a treacherous maze.
On one hand, you’ve got providers making outlandish claims — promising to neutralize attackers in seconds. But here’s the catch: it's a facade for a barrage of alerts that leave you drowning in a haystack while the needles (i.e., critical threats) remain hidden.
Then, there’s the other side of the coin. Some MDR provider organizations seem to have a foggy understanding of what that “R” in MDR stands for. Yes, it’s “Managed Detection and Response.” But some vendors tout “MDR + Remediation” as if it’s a groundbreaking revelation.
The truth is separating fact from fiction when it comes to response is hard. However, we’ve made it easy. When considering MDR providers to protect the future of your organization, make sure you get clear answers to the following questions, as they may just save you when time is on the line.
1. Can the provider detect elusive threats with confidence?
- It’s crucial to assess the provider’s ability to detect a range of threats, including sophisticated threats. Look for a high degree of confidence in their conclusions, minimizing false positives.
- Ask about their detection techniques, in-house threat intelligence capabilities, and how they handle false positives.
2. Can the provider take action to stop threats?
- Detection alone isn’t enough. Ensure the provider can take swift action to prevent threats from spreading.
- Ask about their response capabilities, including containment and isolation techniques.
3. Does the provider offer flexibility in threat eradication?
- Flexibility matters. Can you choose how and when actions are initiated? Some threats require immediate action, while others may need a more strategic approach.
- Inquire about threat eradication methods and whether they align with your organization’s needs.
4. Can the provider assist in cleanup and recovery?
- After an incident, effective cleanup and recovery are essential. Look for providers who not only contain threats but have experts on hand to also help fortify your security posture.
- Ask about their post-incident recommendations and support.
5. Is the provider continuously improving?
- Threat landscapes evolve, so your MDR provider should too. Are they learning over time and enhancing their detections?
- Inquire about their research, development, and commitment to staying ahead of emerging threats.
Remember, MDR isn’t just about buzzwords or fancy acronyms. It’s about having a partner who can navigate the incident response lifecycle effectively and give you that critical time advantage. With Huntress, our mission is to make sure we act before potential impact.