We resolve thousands of alerts every single month in our Security Operations Center (SOC). And, sure, we could throw out fancy numbers, but what does that really solve? Big numbers tend to blur the lines until they’re just more noise.
If you don’t work inside a SOC, you rarely get to see the meat and potatoes of what actually happens during a cyberattack. You see the news headline after the fact, but you don't get glimpses into the panic, the investigation, or, more importantly, the save.
But we’re here to change that. This is the story of how a local business almost lost everything through one of the most routinely targeted footholds on the internet: a public-facing VPN.
You’ll see how a combination of technology and human expertise builds security resilience in unexpected places.
Key takeaways:
-
Small businesses, not just big corporations, are key targets for ransomware. Attackers are focused on profit above all else, even if that means targeting organizations that play critical roles in local economies and supply chains.
-
A single vulnerable entry point can lead to a full-blown ransomware attack. In this case, a compromised VPN without multi-factor authentication (MFA) triggered tactics like stolen credentials, lateral movement, and attempts to disable security tools. Extra security layers, like MFA and monitoring remote access, can stop attackers before they do major damage.
-
While detection tools spotted shady activity, human analysis made the final call to isolate a network and kick out an attacker.
-
You don’t need an enterprise-sized budget to defend against enterprise-level threats. What matters is the right combination of visibility, expertise, and a clear response plan.
The target: More than just a small business
Let’s set the scene.
The victim of this attack is a small US-based construction manufacturing company that plays a critical role in its local supply chain.
Companies like this aren’t the massive Fortune 500 tech giants that make daily headlines. But they are the businesses that keep many towns alive. They’re often the lifeblood of their local economy. When businesses like this go down, it’s not just their employees who suffer. It’s every downstream project waiting for its output and products. It’s the local vendors, partners, and even nearby food joints that rely on their business.
When businesses like this get hit with ransomware and shut down for a week (or forever), real people risk losing their livelihoods.
How did the attackers get in?
Every cyberattack starts with an exposed vulnerability, whether it’s a software bug or a human at a keyboard. And while there are a thousand ways to break into an organization, there are only a handful of ways to move around once you’re inside.
In this case, it all started with a VPN compromise, an attacker technique our SOC sees way too often.
If you’ve worked in corporate America, you know the drill. You use a VPN to remotely log into your work network. But here’s a scary realization: nearly half of the environments we protect don't use Two-Factor Authentication (2FA) on their VPNs. This means they’re leaving the front door unlocked for attackers to stroll in whenever they want.
In this case, our SOC was initially tipped off when the customer’s Managed Endpoint Detection and Response (EDR) started firing off warning signs for potentially shady activity. As our hunt quickly unfolded, the attack path and initial entry point became clear:
-
Entry: The attacker logged in via VPN
-
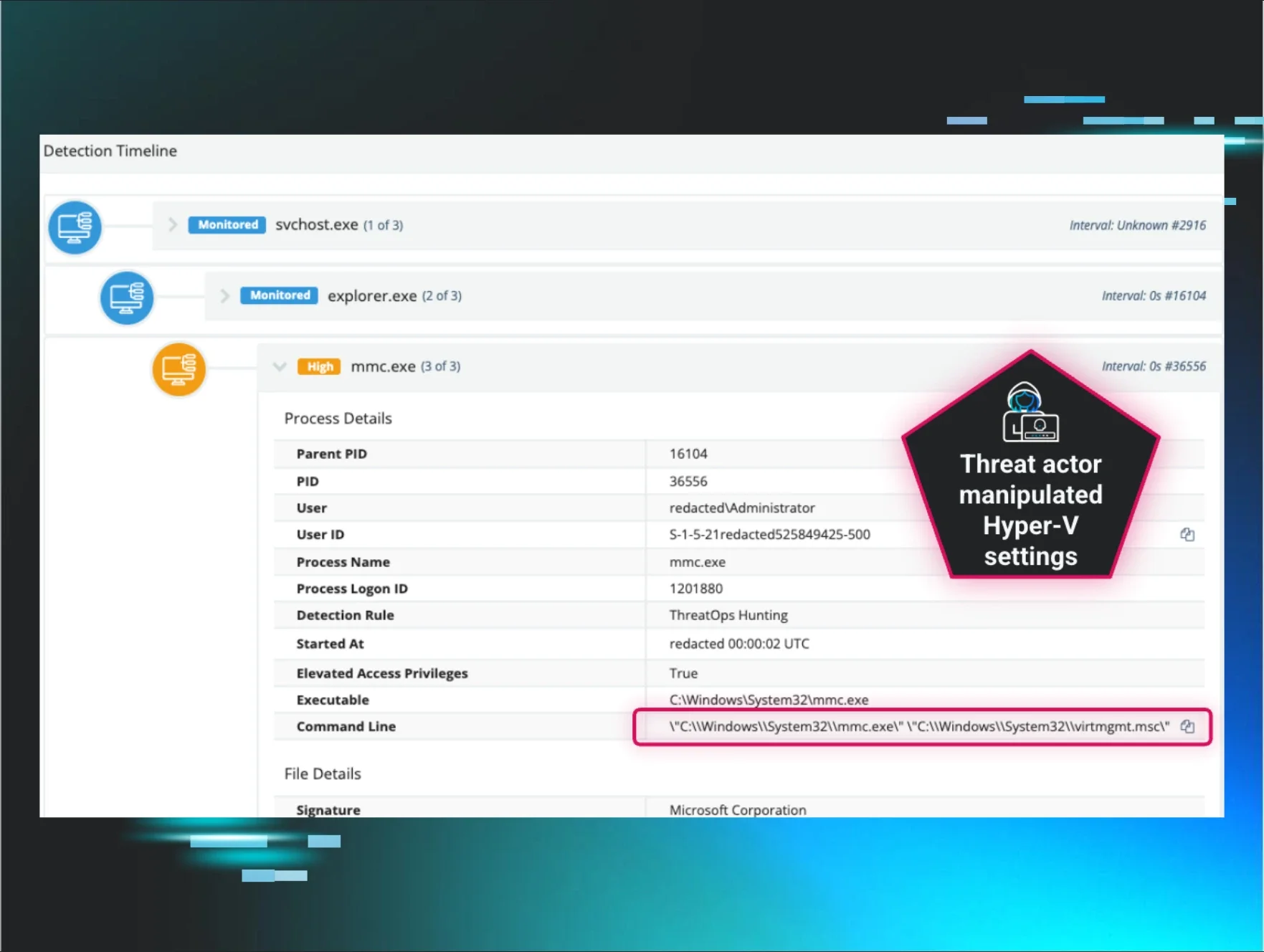
Reconnaissance: Used Remote Desktop Protocol (RDP) to look around the network, hoping to find administrator credentials, aka keys to the kingdom
-
Credential theft: Moved laterally to a server and dumped credentials, stealing usernames and passwords
-
Sabotage: Now that admin access was achieved, the attacker tried to disable Microsoft Defender and kill the Huntress agent.
While the attacker tried to disable our software, their attempt ultimately failed.
The response: People + technology
Software is great. It makes our lives easier and more secure in countless ways. But during critical cyber emergencies, it doesn’t make judgment calls, reassure victims, or investigate threat activity. That’s where the human element kicks in.
This save wasn't just about an algorithm. It’s about the people in our SOC who saved a small business from getting wrecked by ransomware.
1. Triage
These are the security pros on the other side of the keyboard when an alert goes off at 3:00am.
When the signals started rolling in, our SOC analysts didn't just forward an automated email. They investigated, pulled forensic data, and built a timeline that led to a critical decision—isolate the network. With just a few clicks, this business was cut off from the internet. The attackers, who were midway through their operation, suddenly lost their connection to the victim’s environment. They were locked out and shut down.
2. Support
Enter our SOC Support team. This job isn't just about the technical details. It’s also about humans working with humans to solve real-time security challenges.
Imagine you’re the IT manager for this small business. Your network just went dark. You legitimately start to panic. Worst-case scenarios are running through your head: getting fired, losing the company’s sensitive data, or not being able to recover at all.
SOC Support was on the phone with the customer, offering reassurance and explaining what was actually happening. This is crucial in helping victims pivot from panic to action under extremely stressful scenarios.
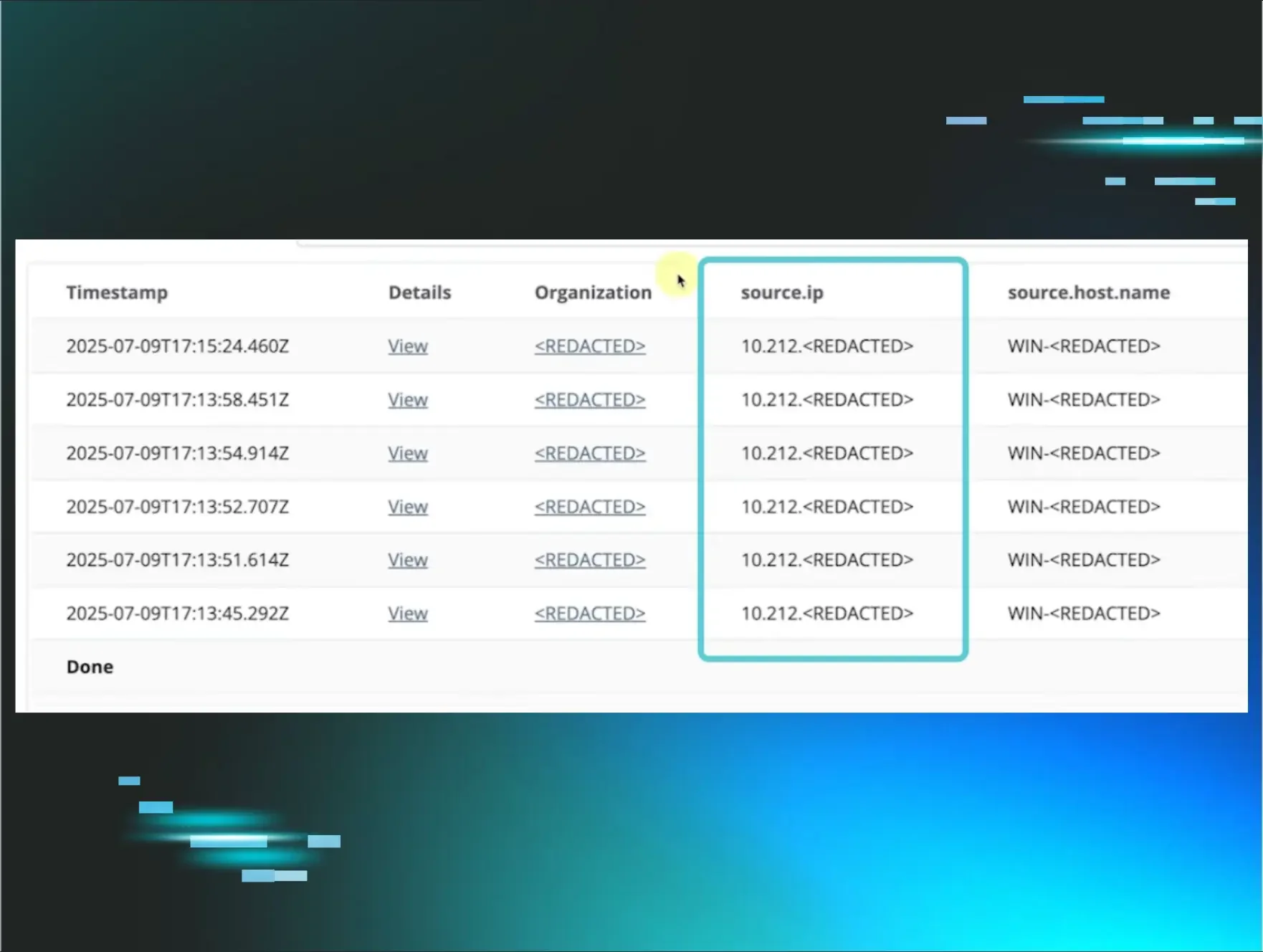
And because we suspected a VPN breach, the SOC Support team requested the customer's VPN logs. You can't fix a hole if you don't know where it is, right?
3. Deep dive
This is where our Tactical Response team comes in. They’re looking for the smoking gun to get the customer safely back online now.
After reviewing the VPN logs, Tactical Response confirmed the initial access culprit: VPN compromise.
To regain control of their environment, Tactical Response recommended the following initial steps:
-
Disable compromised accounts
-
Turn on 2FA
Within just a few hours, a situation that could’ve been a business-ending ransomware event was resolved. We kicked the bad guys out, patched the holes, and the supply chain kept moving in this local community.
Learn more about VPN compromises and how Huntress Managed Security Event and Information (SIEM) spots them early in the attack chain:
Why this matters: The cybersecurity poverty line
We all know the massive security vendors who are fighting the good fight for the Fortune 500, and this is undoubtedly crucial work.
But who’s watching over the endpoints and identities of the local dentist, the law firm, or the manufacturing plant down the street? The hard truth is that they’re often unprotected and just as vulnerable to cyberattacks. They’re hovering below the “cybersecurity poverty line,” with million-dollar security teams and solutions far out of reach.
Attackers are opportunists, if nothing else. And they know these businesses are easy targets.
Spoiler(!): You don't need a NASA-sized budget to stop a sophisticated cyberattack. Instead, you need the right product (to detect the threat), the right people (to investigate and respond), and the right process (to wrangle the chaos).
What you can do
If you’re running a small business or managing IT for one, take a hard look at your defenses.
-
Do you have 2FA on your VPN? (Seriously, go check right now.)
-
Do you know if RDP is exposed to the internet?
-
Do you have access to a team that can review alerts, or is it just a piece of software running in the background?
-
Do you have a practical, rehearsed plan when things go wrong?
-
Need help getting started with your security journey? We’ve got you covered here.
Special shout-out to Jose Oregon, Security Operations Analyst, Jake Vicini, Senior SOC Support Specialist, and Anton Ovrutsky, Principal Tactical Response Analyst, for supporting this incident!