Compliance can often feel like traffic laws. Street signs, speed limits, and signals aren’t just cute roadside decorations. They help ensure safe travel and the smooth flow of traffic. It’s the same deal for compliance regulations. They’re like the guardrails that ensure businesses, users, and systems that help everyone stay in their lanes and prevent accidents like cyberattacks. If you blow past a stop sign, you risk a penalty from the authorities, or worse yet, a total wreck. And similarly, if you blow past compliance, you run the risk of breaches and significant financial losses.
Same Challenges, Different Playbooks
Often, “compliance” is one of those buzzwords that everyone, everywhere knows—whether you're in New York, London, or Sydney. No matter where you are, compliance rules tend to have a few things in common, but each region throws in its own quirky set of requirements. If you’ve ever opened up your compliance guidelines, you know the struggle. It’s like trying to herd a bunch of cats—except these cats are holding legal documents and keep changing their minds every five minutes.
In this blog, we’ll review the compliance mandates for defense contractors in the US as well as a variety of industries across the UK and Australia. And we’ll review how security information and event management (SIEM) solutions can help individuals and organizations across the globe strengthen their cybersecurity and remain compliant.
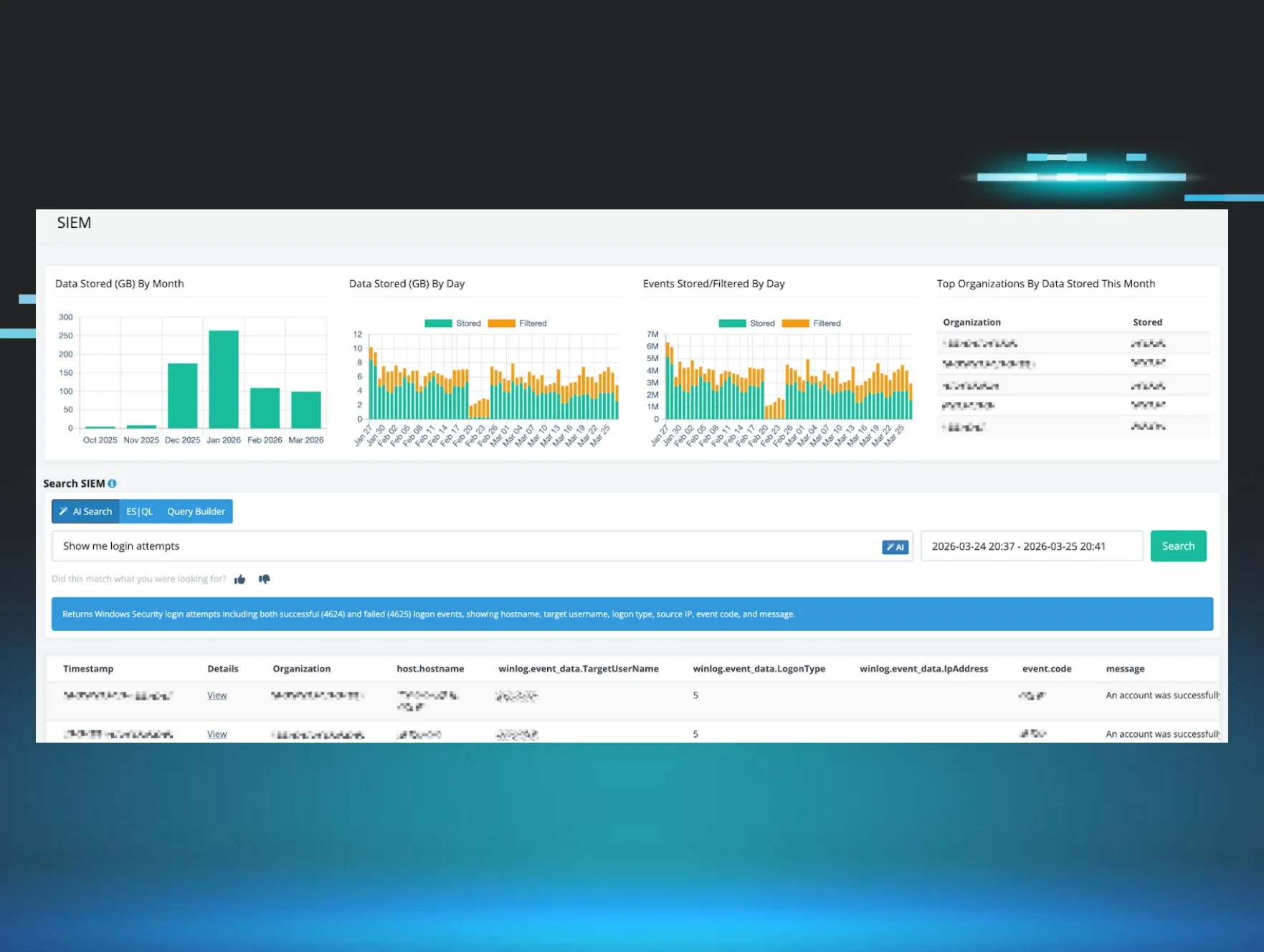
While we’ve discussed SIEM in depth in other blogs (like Unlocking SIEM: The Role of Smart Filtering and Chaos to Clarity: How our Community Helped Transform SIEM), let’s quickly review the purpose and benefits of this solution. A SIEM is like an all-seeing cybersecurity eye that can ingest loads of data, turn it into searchable information, and translate it all into comprehensible reports. What SIEM does best is:
- Consolidate data from disparate sources
- Detect indicators and patterns of compromise quickly
- Provide rapidly searchable data and reports for compliance needs

CMMC: Like Ft. Knox for Classified Data
The Cybersecurity Maturity Model Certification (CMMC) is the "bouncer" for sensitive information in the defense world, keeping it safe from troublemakers. Suppose you're a contractor working with the United States Department of Defense (DoD), the CMMC helps ensure you're following some pretty strict rules around data security—think log collection, threat detection, and rapid response. There are three stages—Foundational, Advanced, and Expert—and each one ramps up the defense, building layers of protection that make it harder for cyber threats to crash the party. The type and classification of data handled by contractors will determine which level of CMMC you’ll be required to meet.

Before we cover how Managed SIEM helps with CMMC compliance, we’ll break down some of the key differences to keep an eye out for between CMMC and regular US-based non-DoD compliance requirements.
Scope and Focus
CMMC is specifically designed for organizations working with the DoD and its contractors. The primary goal is to protect Controlled Unclassified Information (CUI) and ensure that defense contractors meet rigorous cybersecurity standards to safeguard national security. Regular, non DoD-based frameworks apply to a broader range of industries and organizations, focusing on data privacy, financial security, healthcare regulations, or other sectors. For example, the Health Information Portability and Accountability Act (HIPAA) addresses healthcare information privacy in the US, and the Payment Card Industry Data Security Standard (PCI-DSS) deals with payment card data security.
Regulatory Environment and Penalties
Non-compliance with CMMC can lead to two outcomes: loss of DoD contracts and reputational damage in the defense industry, both of which are disastrous to a defense organization. Due to the potential outcome of non-compliance, contractors must pass and maintain adherence to CMMC certifications to continue to work with the DoD. For non-DoD frameworks, the consequences can vary depending on which compliance mandates they fall under. HIPAA non-compliance, for example, will result in financial penalties, loss of reputation and clientele, and potential downtime of medical services. While CMMC directly enforces the defense industry, non-DoD compliance impacts can vary and aren't always immediately felt.
Emphasis on Cybersecurity
Cybersecurity is the main driver for CMMC mandates. At its core, incident response, risk management, protection of sensitive data, and all-around cyber hygiene are the emphasis. Solutions like SIEM, and endpoint detection and response (EDR), as well as services like continuous security operations center (SOC) coverage and threat detection, should always serve as part of any CMMC defensive strategy. Non-DoD frameworks emphasize cybersecurity but will generally also cover other areas such as operational controls, user consent, and data privacy. Often, the focus is broader, covering areas that exist outside security best practices and are less stringent than CMMC requirements.
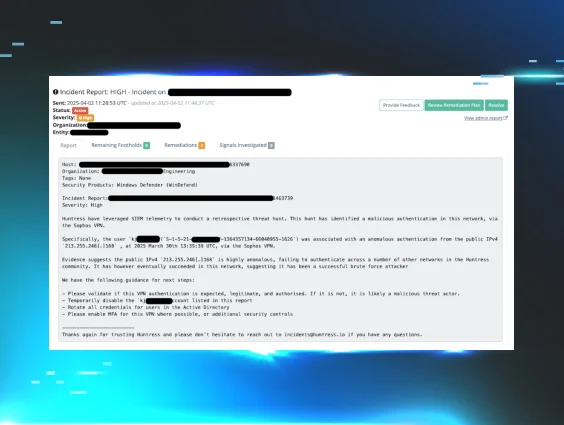
Huntress Managed SIEM deals directly with CMMC Level 2 compliance mandates. Within this framework, SIEM covers key areas such as threat detection, incident handling, log review, data correlation, malicious code detection, and identification of unauthorized use. Leveraging Managed SIEM helps assist with the above points specifically addressing risk, protection of data, and continuous coverage.
NIS 2: Guarding the UK’s Crown Jewels of Cybersecurity
In the EU, Network and Information Systems (NIS), or NIS 2, has been making waves in the compliance world. As of 2023, the new regulation, called the NIS 2 Directive, is all about boosting cybersecurity in industries that are critical to everyday life. It’s an upgrade to the original NIS Directive, with stricter rules for organizations to protect their networks and systems from cyberattacks, keep things running smoothly, and respond faster during an incident. NIS 2 applies to public and private companies that provide essential services or are part of critical infrastructure, so it's not just big corporations—it covers organizations of all sizes.
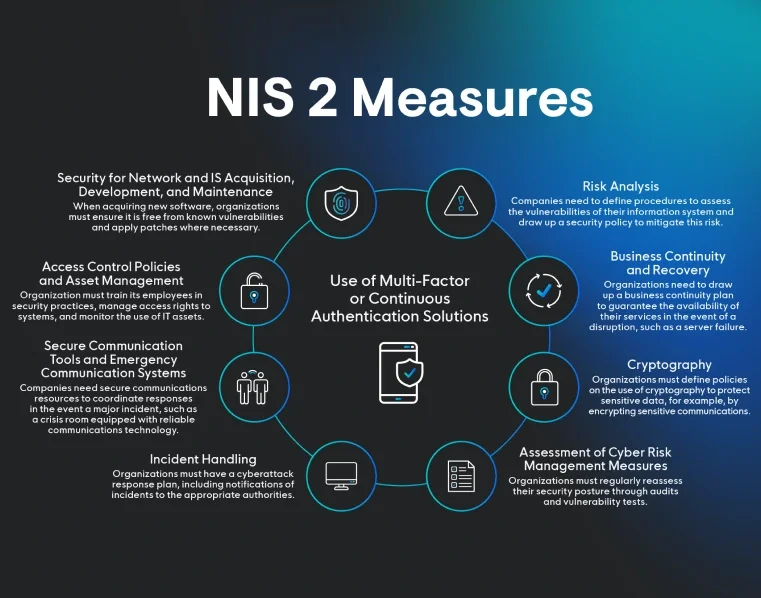
We’ll start by covering some of NIS 2's key components and how they impact organizations operating in the UK.
Focus and Purpose
Since Brexit, the UK isn’t directly governed by the EU's regulations anymore, but it’s still keeping things in check by adopting NIS 2 in the form of its own NIS regulations. The UK’s version of NIS 2 focuses on boosting cybersecurity for critical infrastructure—things like energy, transport, finance, healthcare, and digital services. The UK government has made it clear that they’ll either keep or tighten cybersecurity rules based on NIS 2, so if your organization is in one of these key sectors, you’ll need to stay on top of strong incident detection, risk management, and overall cybersecurity resilience to fend off cyberattacks and potential penalties.
Certification and Compliance Requirements
Under NIS 2, UK-based organizations in critical sectors must follow cybersecurity best practices and regularly assess their risks. There’s no official certification for compliance, but you’ll need to show you’re meeting the standards through self-assessments, cybersecurity audits, and regular reporting. If you don’t play by the rules, UK authorities can hit you with fines or other penalties. The National Cyber Security Centre (NCSC) and other agencies are the ones who can enforce these actions, so it’s important to stay on top of those cybersecurity requirements. After all, nobody wants to end up with a hefty fine or sanctions.
Scope of Security Controls
NIS 2 lays out broad cybersecurity rules for organizations in critical sectors, focusing on things like risk management, incident reporting, and making sure network systems stay resilient. While it’s all about protecting vital infrastructure, it’s not specifically targeting defense-related info. Instead, it’s more about making sure organizations do things like conduct risk assessments, meet basic cybersecurity standards, and have systems in place for detecting and responding to incidents. If something major happens, UK-based organizations are required to report significant cyber incidents to national authorities like the NCSC, usually within 24 to 72 hours, depending on how serious it is. This is aimed at improving the UK’s overall defense against cyber threats and keeping the country’s infrastructure secure.
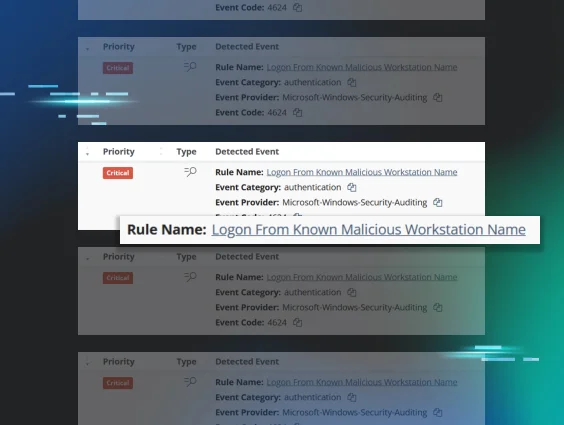
SIEM is a key tool for hitting the main goals of NIS 2 compliance. It can help UK-based organizations stay on top of things by continuously monitoring for incidents, detecting and responding to threats, managing logs, and handling all the necessary reporting. Essentially, it makes it easier to spot and deal with risks, keep track of everything for compliance, and stay organized when it comes to regulatory requirements. So, if you’re looking to meet NIS 2 standards, Managed SIEM is your friend.
Essential Eight: Cybersecurity That’s More Reliable than a Sydney Tram
The Essential 8 is a set of key cybersecurity practices recommended by the Australian Cyber Security Centre (ACSC) to help organizations protect themselves from cyber threats. It’s not a formal certification, but think of it as a solid foundation from which to build your security. By implementing these eight controls, you’ll greatly reduce the risk of things like malware, ransomware, and data breaches, keeping your systems and data secure. It’s a straightforward, no-fuss way to strengthen your defenses without becoming a cybersecurity expert overnight. Simple steps that go a long way—kind of like putting on your seatbelt before a drive to Bondi Beach!
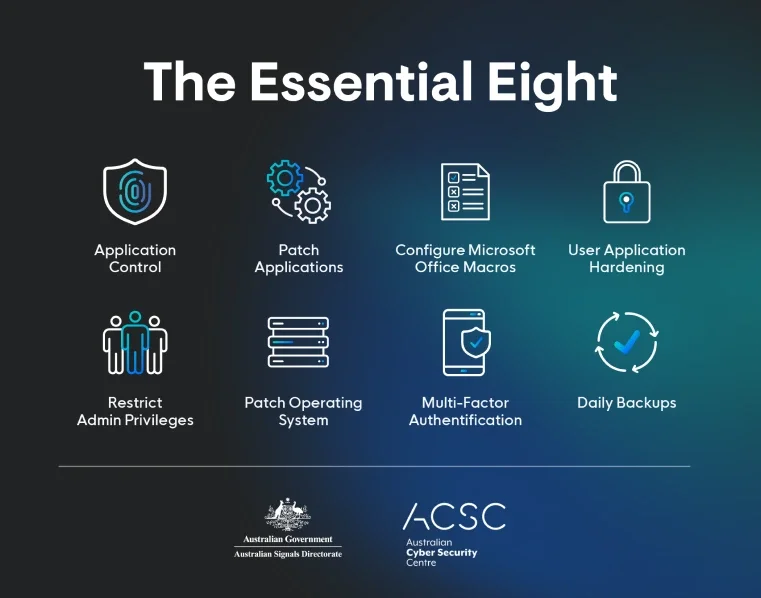
As implied by the name, Essential 8 covers eight specific controls:
- Application Whitelisting
- Patch Applications
- Configure Microsoft Office Macros
- User Application Hardening
- Restrict Administrative Privileges
- Patch Operating Systems
- Multi-factor Authentication (MFA)
- Daily Backup of Important Data
To gain a better understanding of these controls, we’ll break down areas in which they apply and how they came about.
Focus and Purpose
The Essential 8, created by the ACSC, is mainly for organizations in Australia, especially those in industries where strong cybersecurity is a must. It’s a set of basic yet powerful security measures designed to help businesses improve their cybersecurity. The focus is practical, proven controls that can be easily implemented to protect against common threats like malware, ransomware, and data breaches. Think of it as a checklist to boost your cybersecurity hygiene and cover the essentials needed to defend against a wide range of cyber risks.
Cybersecurity Controls and Risk Management
The Essential 8 lays out a set of clear, actionable steps that are straightforward and practical to put into place. These controls mostly focus on prevention—things like application whitelisting, regular patching, and backups—helping to improve overall security hygiene across your organization. While it emphasizes the importance of daily backups and using MFA to avoid data loss, it doesn’t dive deep into incident response or reporting. The main goal is to prevent issues before they happen and catch any problems early on.
Penalties and Enforcement
Following Essential 8 isn’t required by law, but the ACSC strongly recommends it for organizations looking to boost their security. However, the Australian government mandates all non-corporate Commonwealth entities to adopt Essential 8 Level 2 mitigations to achieve a managing maturity rating. There’s no official certification, but organizations can do self-assessments or even opt for external audits to see how closely they align with the guidelines. While there aren’t any legal penalties for not following Essential 8, businesses that skip these steps may leave themselves open to cyberattacks, which could lead to reputational damage or financial losses. The ACSC prefers encouraging adoption with helpful guidance rather than enforcing strict rules.
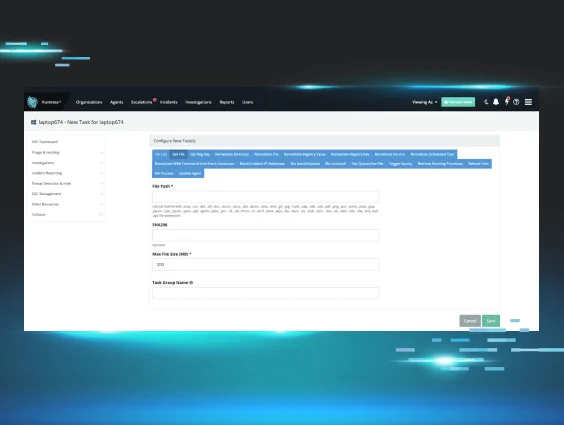
A SIEM solution can be a really helpful tool when it comes to supporting several of the Essential 8 controls, even if it doesn't directly address some of the Essential 8 controls. Here’s how it can assist:
- Application Whitelisting: It can detect when unauthorized apps are running.
- Microsoft Office Macro Settings: It keeps an eye on macro execution and flags any suspicious behavior.
- User Application Hardening: It spots risky user behaviors in applications and potential security gaps.
- Restricting Administrative Privileges: It monitors and alerts you to any unusual activity by privileged users.
- MFA: It watches for any authentication anomalies or attempts to bypass MFA.
- Daily Backup of Important Data: It checks backup logs and alerts you if something goes wrong or if there’s unusual access.
While the SIEM doesn’t directly handle all of the controls, it plays a key role in monitoring, detecting, and alerting you on how well those controls are working, helping to spot vulnerabilities or misconfigurations before they become bigger issues.
Complex Mandates, SIEMple Solutions
Compliance can be quite a challenge. Understanding the ins and outs of the regulations and how they can apply to the various geographical locations is half the battle. Managed SIEM is designed to help assist you with getting the rest of the way there. Whether you’re new to these regulations or a seasoned pro, Huntress Managed SIEM will help be your compliance anchor regardless of what ocean you may be closest to.
Dive deeper into the complexities of compliance mandates and cyber insurance, and see how SIEM can simplify your needs—watch our on-demand webinar, Decoding Compliance and Cyber Insurance: From Mandates to Clarity.