Mastering the Art of Threat Hunting
To master an art form, your tools are just as important as your skills. But it’s not just about having those tools on hand—it’s about knowing when and how to use them. That know-how can be the difference between creating a masterpiece or a tired derivative.
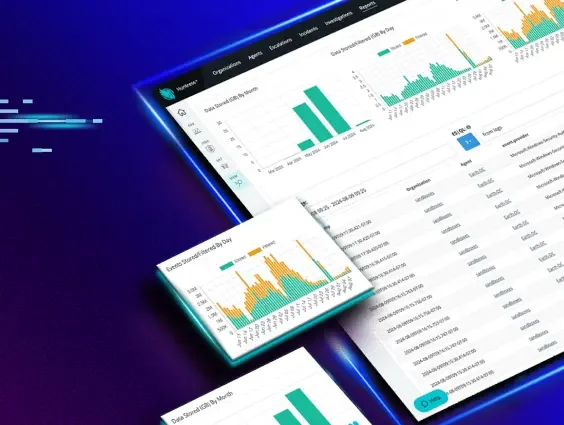
With that in mind, it’s safe to say threat hunting is more of an art than a science. While structured and methodical practices based on analysis and data are certainly there, the need for intuition, creativity, and understanding of the nuances has transformed the landscape. That’s where Security Information and Event Management (SIEM) comes into play. By gathering and analyzing critical data, SIEM takes the guesswork out of threat hunting and turns it into precision artistry.
Tools of the Trade Turning the Tide for Our Community
Like any art, using the right tool with the right skill is imperative, and SIEM is no exception. Even though Huntress Managed SIEM is new, the Huntress Security Operations Center (SOC) has been using this Early Access version to put pressure on threat actors. It's been especially useful for our SOC analysts, helping them pivot quickly from endpoint detection and response (EDR) alerts and investigations to dive deeper into the data the SIEM has already collected and neatly organized. It's proving to be our secret weapon in tracking down more information and staying one step ahead.
While we’re putting the finishing touches on threat detection for Managed SIEM, our SOC has already used it to protect our partners and customers. Here are three examples of how Huntress Managed SIEM, along with our SOC, has helped turn the tide in defense of our community.
The Hostname’s Most Wanted
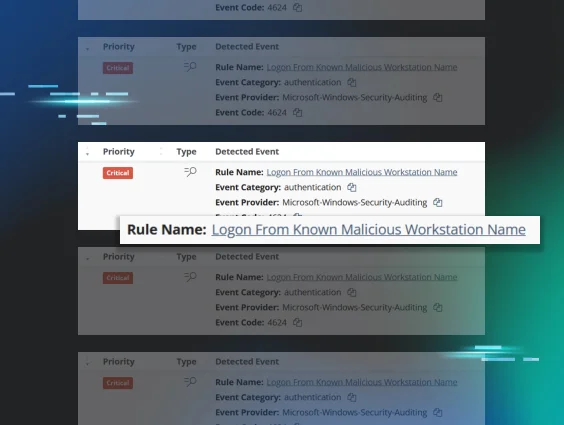
The Huntress SOC collects indicators of compromise (IOCs) from previously seen intrusions, which can include known malicious IP addresses, hostnames, and adversarial tooling used for specific tradecraft or in association with specific adversary groups. Huntress can construct robust early detection signals using the collected information, and with SIEM, leverage this data during investigations.
Utilizing a robust malicious hostname database, Managed SIEM enables analysts to cross-analyze against previous cases and evict threat actors at the first signs of compromise. In the real-world scenario below, Managed SIEM was alerted to the interaction of host “DESKTOP-NT7KVK5” within a partner’s environment. This hostname was previously observed in two prior intrusions.
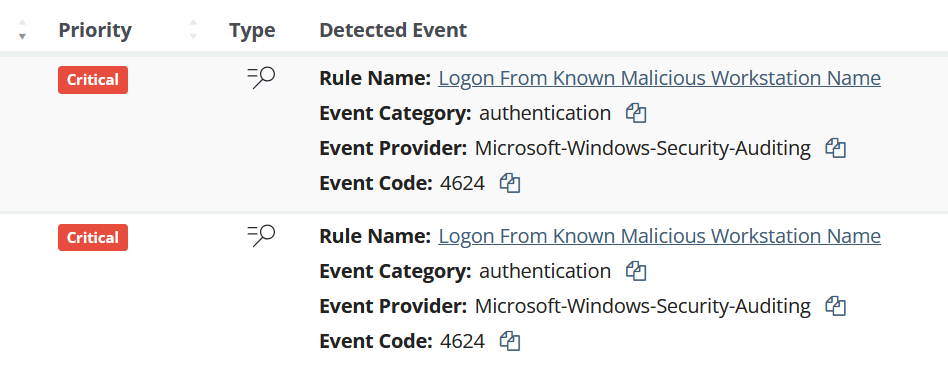
Further analysis noted that due to increased visibility in the partner environment, initial adversarial access was through the organization’s FortiGate gateway appliance (unfortunately, this wasn't connected with Managed SIEM at the time). However, the ability to rapidly analyze interactions within the environment at scale revealed numerous legitimate authentications through this IP address, a pattern often observed in gateway appliances and VPNs.
Due to Managed SIEM’s tracking capabilities, this environment was isolated at the first signs of compromise. Further analysis and parsing of organizational firewall logs revealed not one, but two, compromised VPN accounts, extending back in time before Huntress’ integration into the FortiGate firewall.
This level of remediation following a security event is only possible through the use of Managed SIEM. Individual layers of the environment can be examined for IOCs holistically, giving the Huntress SOC a clearer strategy of defense toward partner environments in response to security incidents.
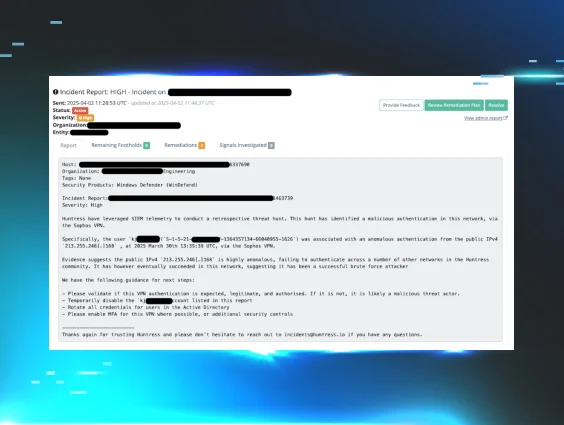
Brute Force Loses to Smart Defense
Often, practitioners overlook the unintended exposure of services within their environments. But with Managed SIEM, we've seen how powerful it can be in spotting system and service misconfigurations. It helps catch vulnerabilities that might otherwise go unnoticed—vulnerabilities that attackers could easily target.
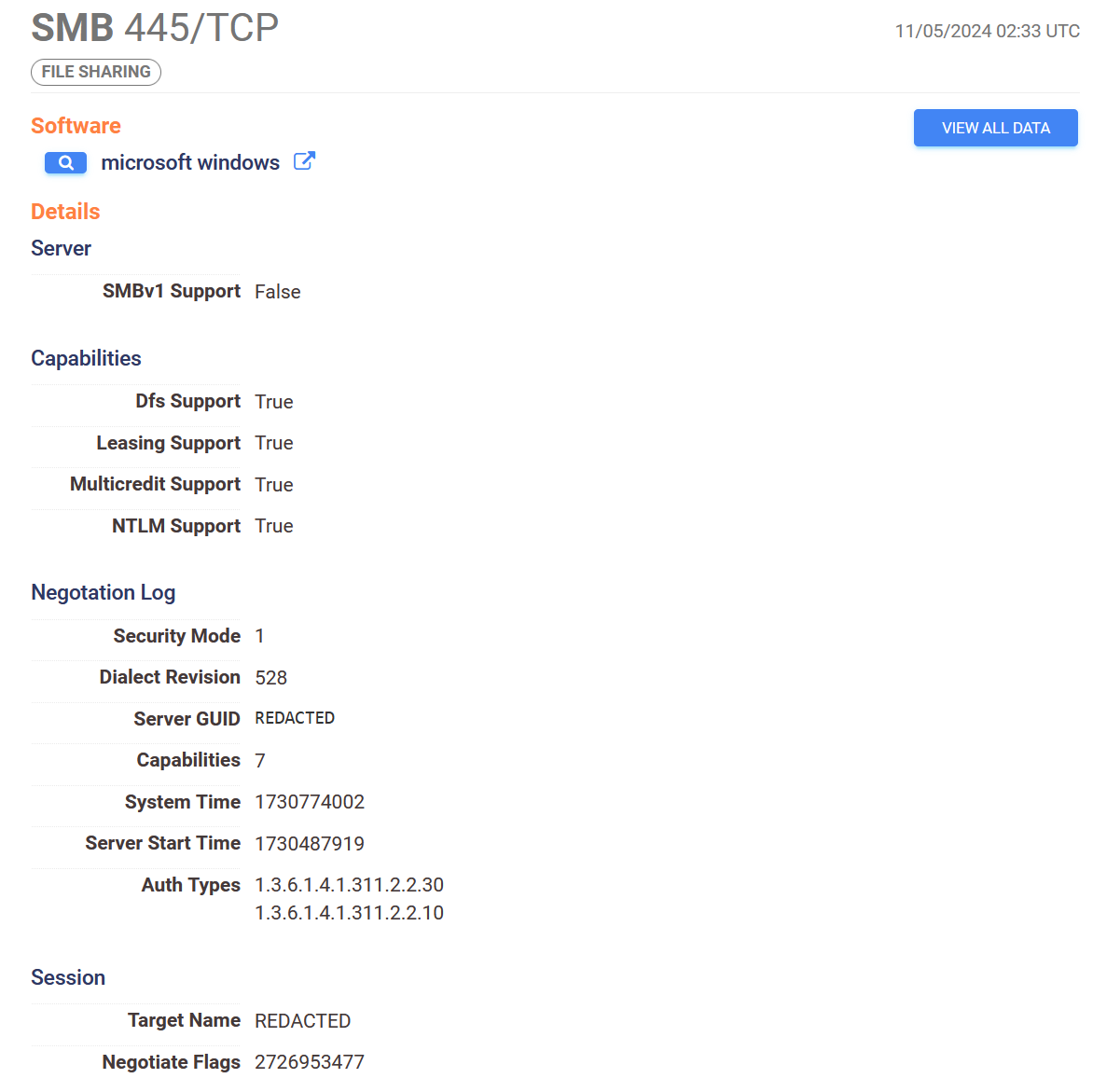
Huntress’ SOC caught some strange failed login attempts (Windows Security event ID 4625) within a partner’s environment. Now, failed logins are nothing new—everyone’s made a typo or two—but these were happening over server message block (SMB) and coming from hostnames often linked to the Metasploit framework. That’s a red flag.
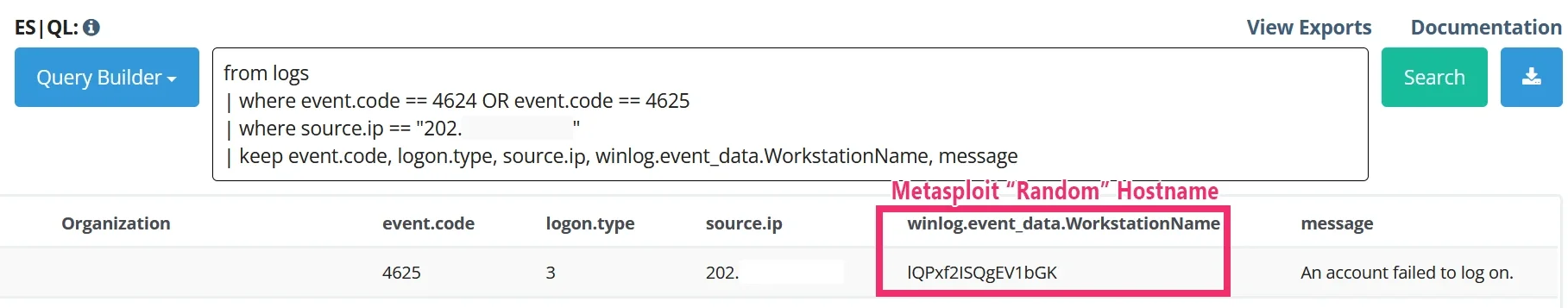
Cross-examining historic Managed SIEM data, Huntress successfully pivoted on the machine’s current and historic configuration to accurately conclude that the machine was unintentionally exposing port 445 (SMB) and port 3389 (RDP) to the public internet, resulting in adversarial brute-force attempts on both services.
In another proactive interaction, Managed SIEM’s capabilities played a key role in providing timely guidance to partner environments, stopping adversarial access before it could compromise the network. This shift from reacting to preventing incidents saved both time and costly calls to IR firms and cyber insurance providers.
Huntress further evaluated the configuration of this server, identifying it as a cloud appliance. Cloud security best-practice recommendations, including those suggested by the cloud service provider (CSP), ensured asset hardening from potential future intrusions.
Turning Alerts Into Action
Finally, a recent example came when the Huntress Managed EDR alerted our team to a massive credential dump happening at an attorney's office. It’s not the kind of thing anyone ever wants to see, but fortunately, it was caught in time.
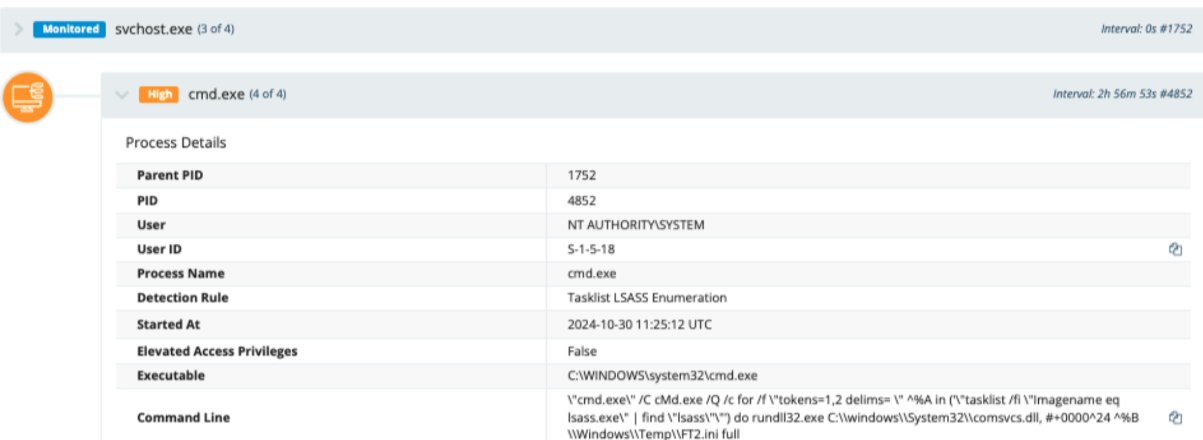
Huntress SOC analysts jumped into action with some quick forensic analysis and pinpointed the machine the threat actor had used to breach the network. Turning to Managed SIEM, a quick search was run for the compromised machine name and uncovered a list of user accounts that the attacker had taken control of.
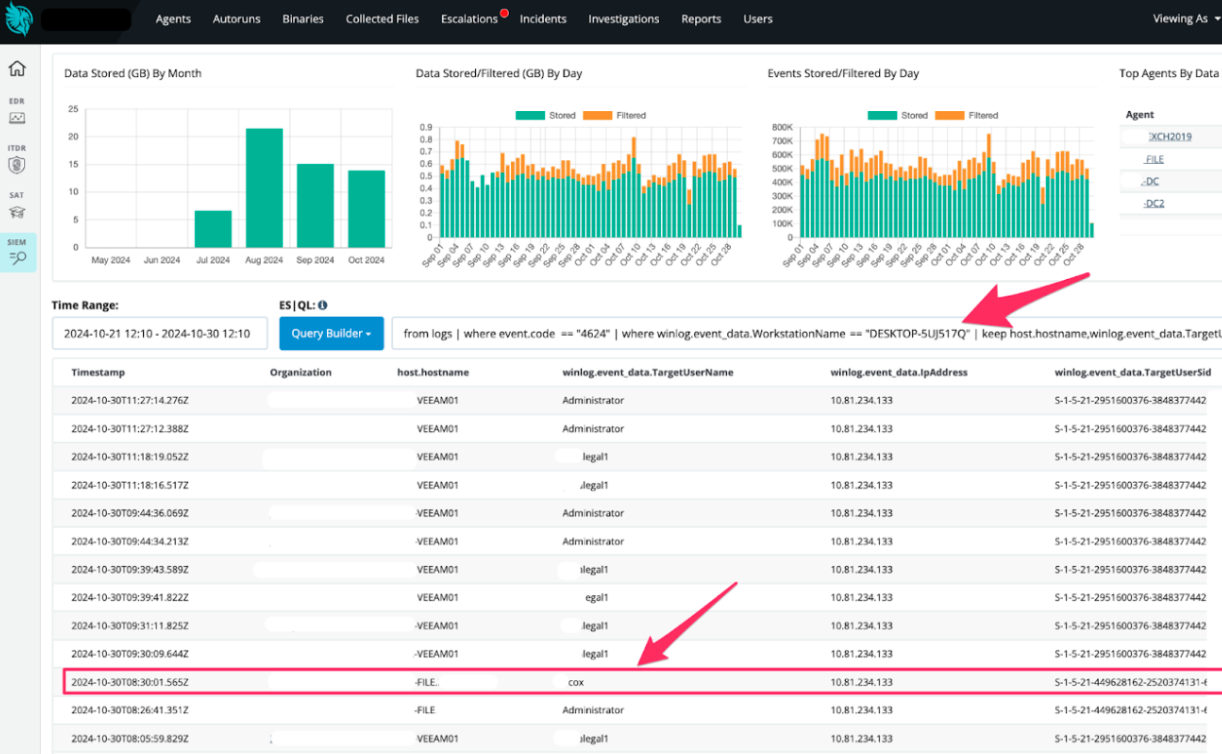
Managed SIEM helped the team uncover an additional user account the threat actor had taken control of—one that hadn’t been flagged earlier but would’ve been key for them to keep access to the network. Due to some hands-on hunting with Managed SIEM, the Huntress SOC was able to move from responding to an EDR alert to detecting, containing, and kicking the attacker out for good.
Defending What Matters
Threat hunting isn’t always straightforward. Leveraging numerous tools and disciplines can often lead to deeper discovery and defensive strategies. Managed SIEM builds on the defenses of Managed EDR and brings a new tool to an art form. While Managed SIEM continues to build and develop the threat detection capabilities designed by the Huntress team, it'll continue to play a key role in threat investigations. As adversaries get smarter, Huntress' resolve only grows stronger. We’ll continue leading the way, always ready to protect what matters most—our community.