Security awareness training (SAT) is supposed to make companies safer, but too often, it feels like just another box to check. While every SAT vendor will swear up and down that their solution is, in fact, a useful tool to shift user behaviors, the truth is that a lot of them don’t.
How do we know that? Well, studies show 60% of all breaches involve the human element. That’s because most vendors have been approaching it wrong, focusing simply on checking a compliance box, instead of connecting with adult learners in a way that actually shifts behaviors and produces real security outcomes.
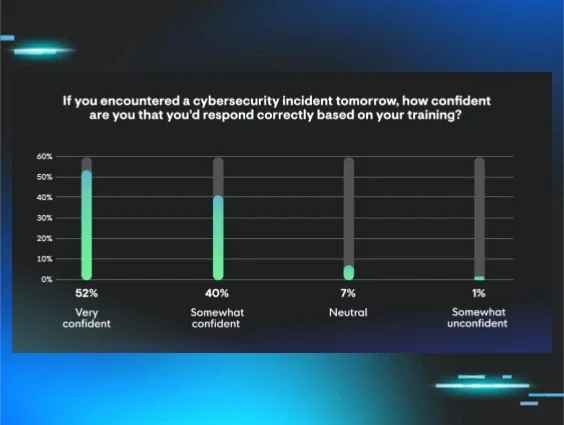
We’ve built our SAT on adult-learning principles that are proven to promote behavior changes, so we’re confident that our training is actually impactful. But we also realize that our own confidence may mean nothing to you. So, we decided it’s time to put our SAT to the test and see what a real expert in adult learning thought about it.
The expert we turned to: Dr. Joshua Stern
Dr. Stern has an M.A. and Ph.D. in Education from UCLA. He’s passionate about adult learning (andragogy) and has dedicated his career to creating unique and engaging learning experiences for adults around the globe.
With his extensive expertise in the adult-learning world, we asked him to conduct an in-depth review of Huntress Managed SAT to get a third-party expert’s view on how Managed SAT stacks up against the principles of andragogy to effectively shift employee behaviors to build a culture of security awareness.
Dr. Joshua Stern
From his findings, Dr. Stern put together the report, Superior Security Awareness Training is Developed with Research-Based Adult Learning Best Practices in Mind. It’s well worth a read.
Traditional SAT: What’s missing?
Most folks have sat through training sessions that seem to drag on forever, only to forget the content by the end of the day. The big reason why is that many programs don’t reflect how adults actually learn.
Drawing on the principles of adult learning, the report highlights that effective SAT should be:
Self-directed: Adults need to understand why the topic matters to them
Relevant: Content tied to real-life situations and challenges
Experience-based: Training should connect with what people already know
Problem-centered: It should focus on solving practical issues
Internally motivating: It must encourage a sense of purpose and mastery
When these principles aren’t present, training tends to feel disconnected and forgettable.
What the report found about our approach
Through his review, Dr. Stern found several strengths in the design of Managed SAT:
Engagement and relatability
Story-driven training with characters and scenarios piques curiosity and helps people see themselves in the lessons. The report notes that engaging formats like animation can make complicated topics easier to understand,and, critically, easier to remember.
Interactive experiences
Rather than relying on passive watching or reading, our lessons and simulations encourage users to make choices and experience realistic consequences. Gamification elements (like leaderboards and badges) also help keep the experience active and rewarding.
Ongoing training, not “one and done”
Security threats evolve, and so should training. The report validates that regular, consumable lessons and monthly phishing simulations do more to reinforce good habits than one big annual session everyone immediately forgets.
Real-world relevance
With new threats continuously popping up, timely updates are key. The report highlights that our content and phishing scenarios based on real-world threat intel help employees feel prepared for what they might actually encounter, turning theory into action.
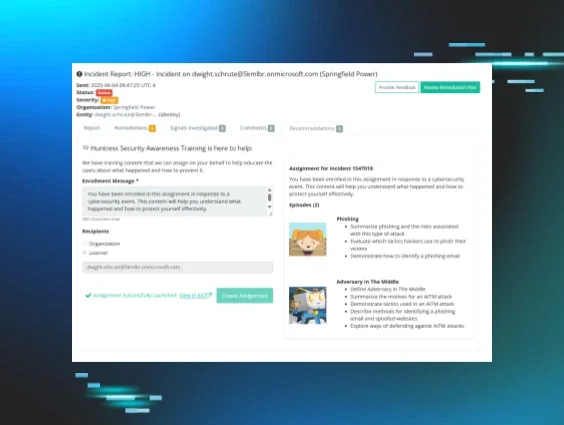
Supportive response to mistakes
Instead of punishing users for making mistakes in training, which leads to shame and hurts learning outcomes, the report commends a coaching approach that uses errors as learning opportunities. This helps build trust and encourages employees to speak up if something goes wrong for real.
Building a culture of security
The biggest takeaway? Truly effective SAT isn’t just about knowledge—it’s about shifting attitudes and fostering a culture where everyone feels responsible and empowered. Tools and policies matter, but a supportive, well-informed team makes all the difference.
We’re grateful for the thoughtful and thorough review from Dr. Stern, and we hope these insights will help everyone better understand what to look for in a security awareness training solution. If you’re interested in the full findings, we invite you to read the full report.