The Origin Story
This is a hero's journey, just not the kind you think. No caped crusaders or radioactive spiders here. It's about a real-life hero fearlessly tackling log centralization, compliance, and pricing prediction. This is your story. While security information and event management (SIEM) plays a crucial role as a trusted sidekick, it's really about your transformative role in reshaping SIEM into an intuitive, affordable tool.
Rise and Fall

Like any epic saga, there are highs and lows. It begins with stability, disrupted by turmoil, leading to a critical turning point, and finally—boom—a triumph.
SIEM had long been comfortable in the industry, hailed as a savior for its pivotal role in gathering, storing, detecting, and reporting log data. Yet, as in any hero's journey, setbacks are inevitable. Users and MSPs soon discovered that SIEM wasn’t the all-powerful solution it was believed to be. Too often, many stumbled on hurdles like those mentioned in the 2022 Cybersecurity Insiders SIEM Report, including:
- a lack of skilled/trained staff to operate their SIEM effectively (41%)
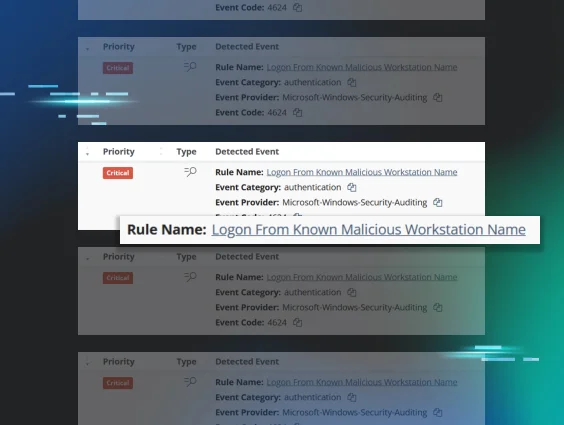
- too many false positives (37%)
- limited budgets (34%)
- system complexity (32%)
- poor integration/interoperability between security solutions (25%)
- having to create/refine rules manually (23%)
- difficulty implementing and deploying the solution (16%)
These pain points also dialed up the pressure to bring in outside help. The Exabeam SIEM Productivity Report noted that roughly 40% of organizations had to engage professional services to help deploy their SIEM to address the following needs:
- new module installation (15%)
- tuning (16%)
- incident response (23%)
- integrations (17%)
Despite its benefits, SIEM was still hard to use, difficult to deploy, and simply too noisy. Security practitioners knew something had to change. But change never comes easily.
The Evolution of SIEM
It was apparent SIEM had to get smarter, stronger, and more practical. To solve its users’ everyday problems, SIEM evolved from a tool-based product into a service-oriented platform known as managed detection and response (MDR). Though the typical management requirements shifted to MDR vendors, it wasn’t for the better. Much like when your favorite character dons a new costume, not everyone was happy with the updated look.

As of today, 50% of companies using SIEM believe they’re overpaying for MDR services, based on findings in the State of SIEM 2021 report. Worse yet, 50% of security practitioners had to upgrade their log source license because of the growth in log data. Additionally, 46% have been unable to log necessary data due to budget limitations based on their current license model. To find impactful fixes to these issues, we first had to understand the root of the problem. And we found the answers from the most heroic of sources—you.
We surveyed over 200 members of the Huntress community and discovered:
- 53% felt neutral about SIEM
- 25% were satisfied with SIEM
- 14% were dissatisfied with SIEM
And we learned the most common challenges were:
- high costs associated with SIEM
- lack of user-friendliness
- labor-intensive processes
- inadequate or insufficiently robust SIEM solutions
- excess volume of low-quality alerts
We heard you loud and clear. Now, here we are, at the turning point.
A Turning Point
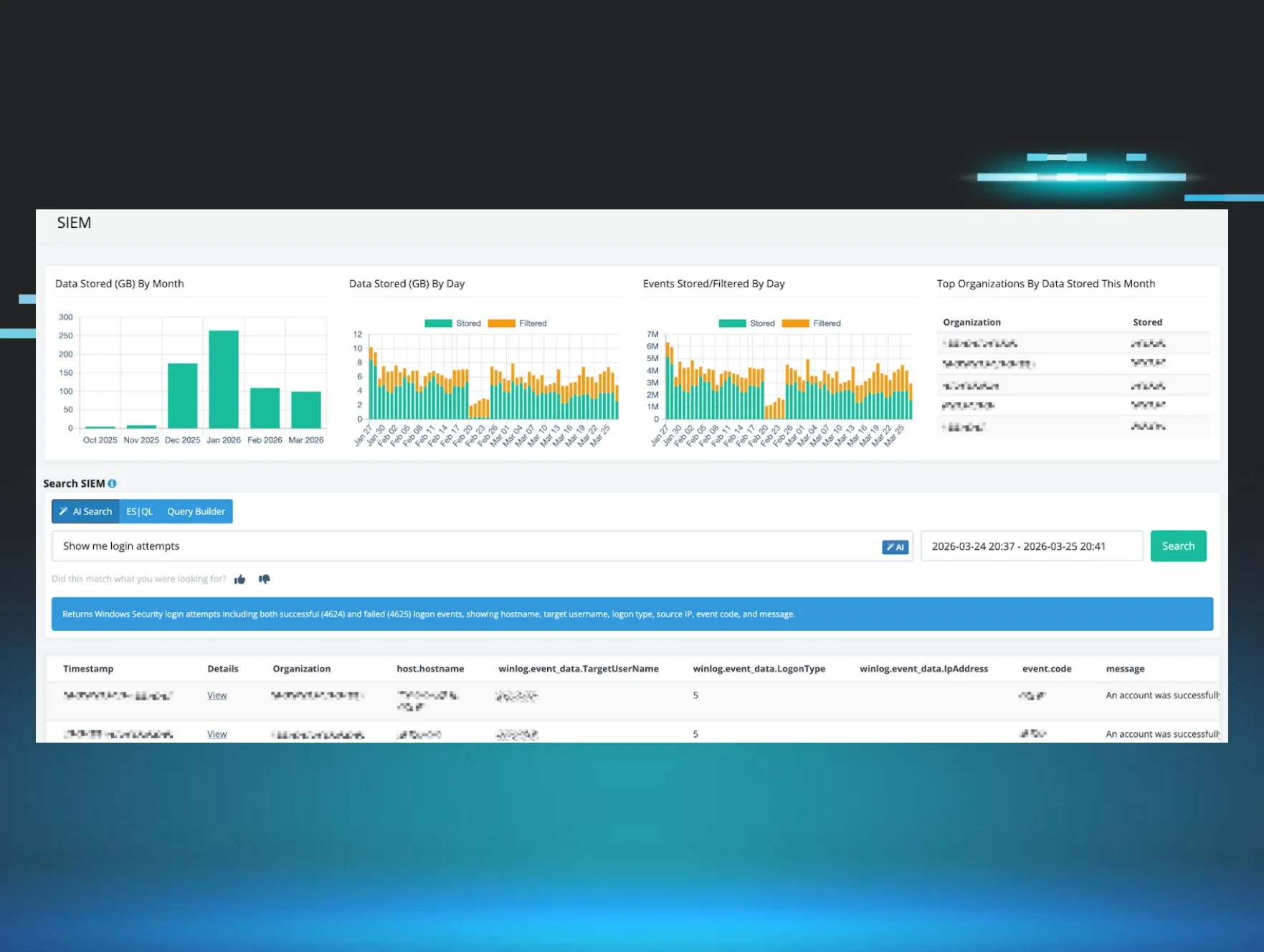
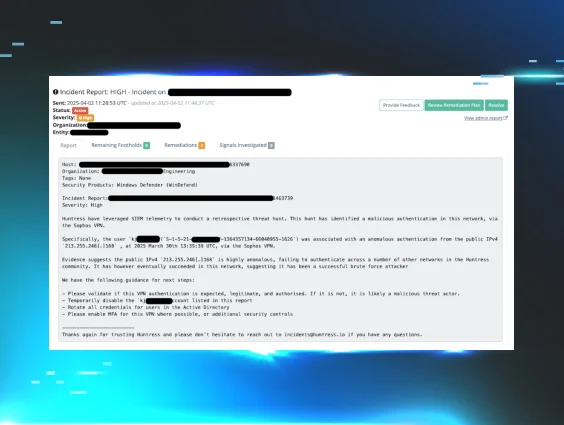
Introducing Huntress Managed SIEM, the brainchild born of your daily grind. Purpose-built to address your unique challenges, this new generation of SIEM can simplify security management by focusing on continuous monitoring, efficient control, and effective data collection, all within a financially viable framework. Our goal was clear: build a solution designed for your everyday needs. That’s why we stripped away unnecessary complexities and focused on core functionalities.
Three fundamental principles guided the creation of Managed SIEM:
- Give you more of what you need and less of what you don’t
- Ensure predictable pricing and budgeting
- Make it incredibly easy for you by having it managed by Huntress experts
Grounded in these three concepts, Managed SIEM delivers fresh, distinctive capabilities to the market.
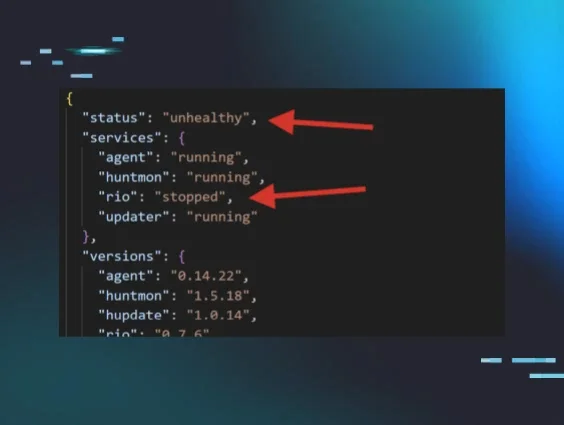
Smart Filtering
Sharpen your search scope and cut through the noise before it even starts. While filtering out needless noise isn’t new, an inverse funnel to collect data is. Log collection typically starts with gathering all sources first and then sifting through them to make sense of the data. The problem with this approach is comparable to having to identify one specific star in a galaxy with the naked eye. It’s nearly impossible. But if you can isolate a quadrant of that same galaxy using a star map, then you can easily mark your target. Smart Filtering is like that. It refines what you’re searching for to limit the range of noise from the start.
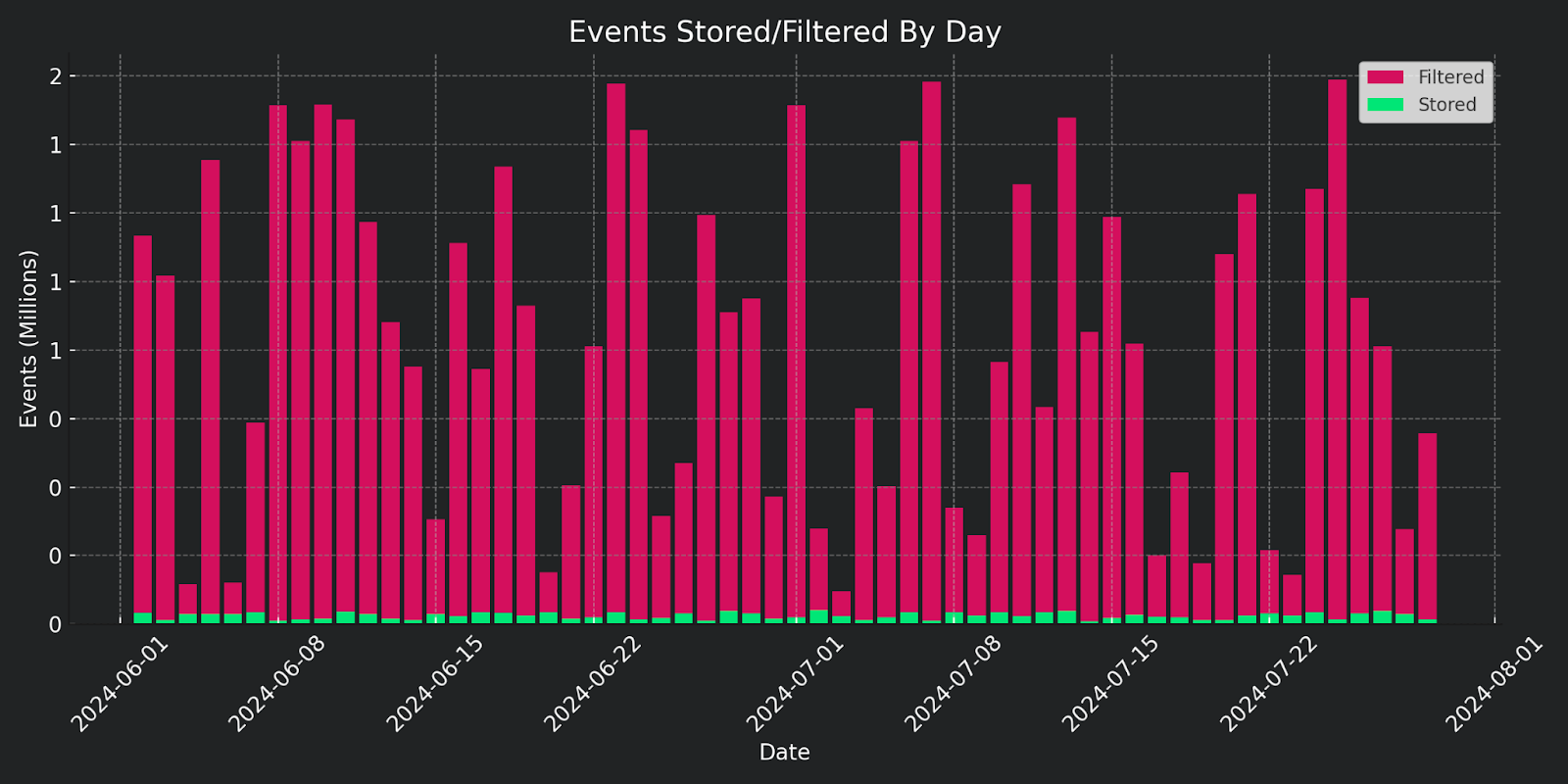
Predictable Pricing
SIEM pricing has always been a blocker for smaller businesses. In fact, pricing methodologies have heavily leaned towards consumption-based pricing. Think of the universe again. If you’re only searching for one specific star, you shouldn’t be billed because you had to scour whole galaxies just to find it. Otherwise, the costs add up quickly. Managed SIEM only focuses on your relevant data sources and filters out excess noise, significantly reducing your costs.
Managed SIEM has been designed as a solution that feels more like a partnership rather than just another product. It was built from the ground up with your experiences, needs, and insights placed front and center.
A New Beginning for SIEM
This is your moment of triumph. SIEM no longer needs to be an unwieldy, expensive platform. We heard you and answered with Managed SIEM, a human-centric solution for human-sized problems. It’s designed to serve you, not the other way around.
Managed SIEM is here to empower you—the real hero of the story.
Got ideas for a new feature or capability? Let’s build it together in The Product Lab.