TL;DR:
- Visit huntress.com/cmmc for the latest information on how Huntress helps support our customers and partners on their CMMC journey
- In our Huntress Hub, you’ll find guides and documentation, including our Shared Responsibility Matrix, Operations Guide, and Operations Plan.
- To support CMMC compliance, Huntress has a feature called Sensitive Data Mode, which blocks Huntress Security analyst access to potential CUI files, without compromising their ability to effectively detect and remediate threats. Read on for a deeper understanding of CMMC compliance and how Huntress helps.
Increasingly sophisticated cyber threats have placed greater demands on the security of organizations, particularly those in the supply chain for the Department of Defense (DoD). The Cybersecurity Maturity Model Certification (CMMC) was introduced to set a new bar for compliance and risk management assurance.
But navigating CMMC compliance—particularly as it has gone through several updates—can feel daunting. It’s essential to understand how tools like Huntress can fit into a compliant and secure framework.
A look at CMMC history from CMMC 1.0 to the 2024 Final Rule
CMMC 1.0 and initial challenges
Launched in 2020, CMMC 1.0 was built around five distinct maturity levels, each requiring external assessments. Vendors supporting organizations subject to CMMC also had to demonstrate compliance, either through their own CMMC assessment or by obtaining FedRAMP authorization. These high standards created substantial hurdles, particularly for smaller vendors, due to limited resources and high costs.
CMMC 2.0 brings simplification
By 2021, the framework evolved into CMMC 2.0, reducing the number of levels to three. This shift reduced the burden by removing new requirements to re-align Level 2 to NIST 800-171r2 and select requirements for Level 3 from NIST 800-172.
Importantly, external assessments became mandatory only for organizations at Level 3 and select Level 2 entities, gradually expanding over the course of the phased rollout. However, vendors serving CMMC-applicable organizations were still held to strict compliance requirements within the 1.0 rules.
The 2024 Final Rule and cloud service provider-specific changes
The 2024 32 CFR Part 170 "CMMC Final Rule" introduced noteworthy changes, especially in vendor requirements. Cloud service providers utilized to store, process, or transmit Controlled Unclassified Information (CUI) remain obligated to meet full CMMC compliance or FedRAMP authorization. However, cloud service providers that act solely as Security Protection Assets—tools that provide security without directly storing, processing, or transmitting CUI—are no longer required to undergo the same external assessments. Instead, the compliance responsibility shifts to the organizations using these tools to ensure that the security capabilities their vendors provide are adequate to meet the CMMC objectives.
What CMMC means for Huntress as a Security Protection Asset
The CMMC framework identifies Security Protection Assets as people, processes, or technology that provide security functions or capabilities to the contractor’s CMMC Assessment Scope.
Huntress is categorized as a Security Protection Asset, as we can help CMMC-bound organizations remain secure through our offerings:
-
Managed Endpoint Detection and Response (EDR) to protect endpoints
-
Managed Identity Threat Detection and Response (ITDR) to secure identities
-
Managed Security Awareness Training (SAT) to arm employees
-
Managed Security Information and Event Management (SIEM) to enhance defenses
Security Protection Assets—like Huntress—are to be evaluated based on their security capabilities and aren’t subject to separate compliance assessments themselves.
How Huntress supports CMMC compliance
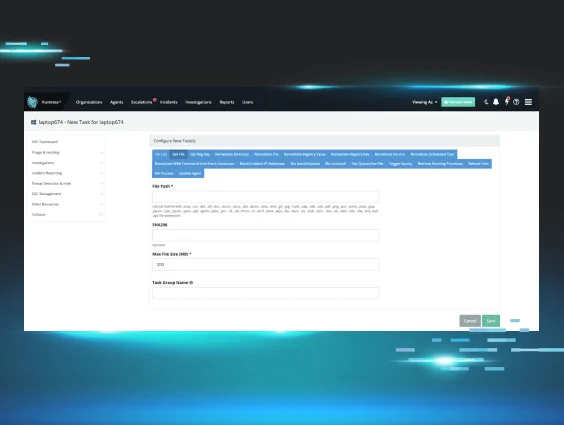
When managing cybersecurity in a CMMC-compliant environment, certain capabilities are required for handling files containing CUI during threat detections. For example, retrieving files for malware investigations could unwittingly expose sensitive information.
Recognizing this challenge, Huntress built our new Sensitive Data Mode—a configuration designed to strike the perfect balance between effective threat investigation and compliance requirements.
Huntress's Sensitive Data Mode explained
Here's what sensitive date mode delivers to help you support CMMC compliance:
1. Blocking SOC access to potential CUI files
Huntress now enables organizations to block our Security Operations Center (SOC) from accessing files likely to contain CUI during investigations. Huntress blocks high-risk file types (e.g., documents, spreadsheets) from being retrieved during investigations. This measure reduces risk and protects compliance.
Screenshot demonstrating file types excluded when Sensitive Data Mode is enabled.
2. Effective threat detection for analysts
Huntress analysts can still retrieve and analyze executable files, scripts, or other non-sensitive file types often associated with malicious activity. This means we can continue to deliver critical incident reports at 99% accuracy—without compromising compliance.
For an up-to-date list of the file types blocked with Sensitive Data Mode, please visit our knowledge base here.
Need to remain CMMC compliant? Let us know.
Sensitive Data Mode is available now and can be configured upon request by contacting support.
And be sure to book your demo with Huntress today.