An Educated Workforce is a Secure Workforce
Huntress SAT is a series filled with heroes, villains, and stories that stick with your employees. Your teams will go on an adventure as they level up their security skills in an unforgettable experience.


Huntress Security Awareness Training educates your learners about SOC 2 compliance with a memorable and engaging training program. Launch an employee-friendly security awareness training program to start speaking the language of SOC 2 security controls.
Huntress Security Awareness Training educates your learners about SOC 2 compliance with a memorable and engaging training program. Launch an employee-friendly security awareness training program to start speaking the language of SOC 2 security controls.
Huntress Security Awareness Training educates your learners about SOC 2 compliance with a memorable and engaging training program. Launch an employee-friendly security awareness training program to start speaking the language of SOC 2 security controls.
Struggling to train your employees about the importance of SOC 2? Instead of boring emails or long lectures, you’ll have access to story-based, animated trainings meant to engage learners and help them remember the basics of SOC 2 compliance.
Start your trial today to access the whole library.
Huntress SAT is built with resource-strapped teams in mind. It’s easy to use, fun, and provides high-quality security awareness training without the headaches.
Admins love it. Learners love it. Hackers hate it.
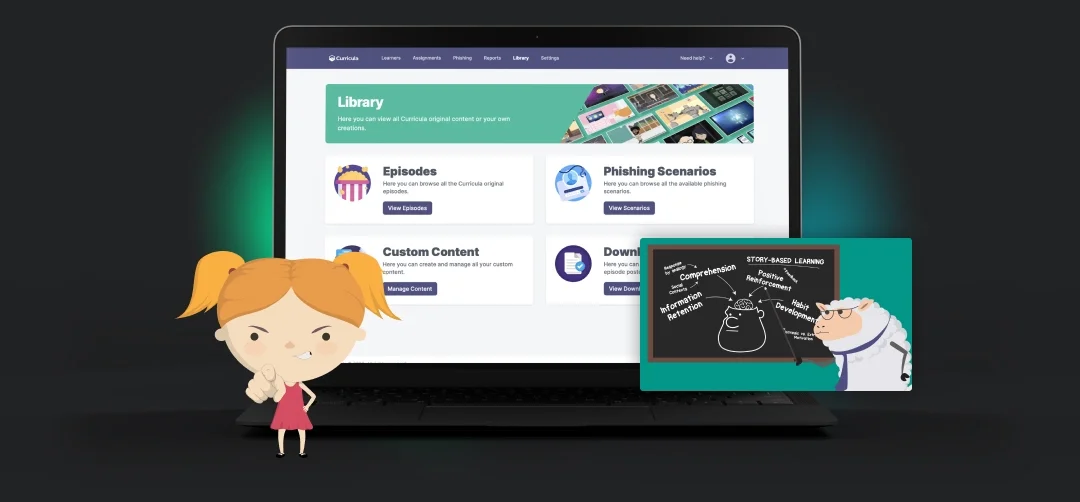
Get access to more than just SOC 2 compliance. With the full Huntress SAT library, you’ll see episodes on phishing, business email compromise, generative AI, and more.
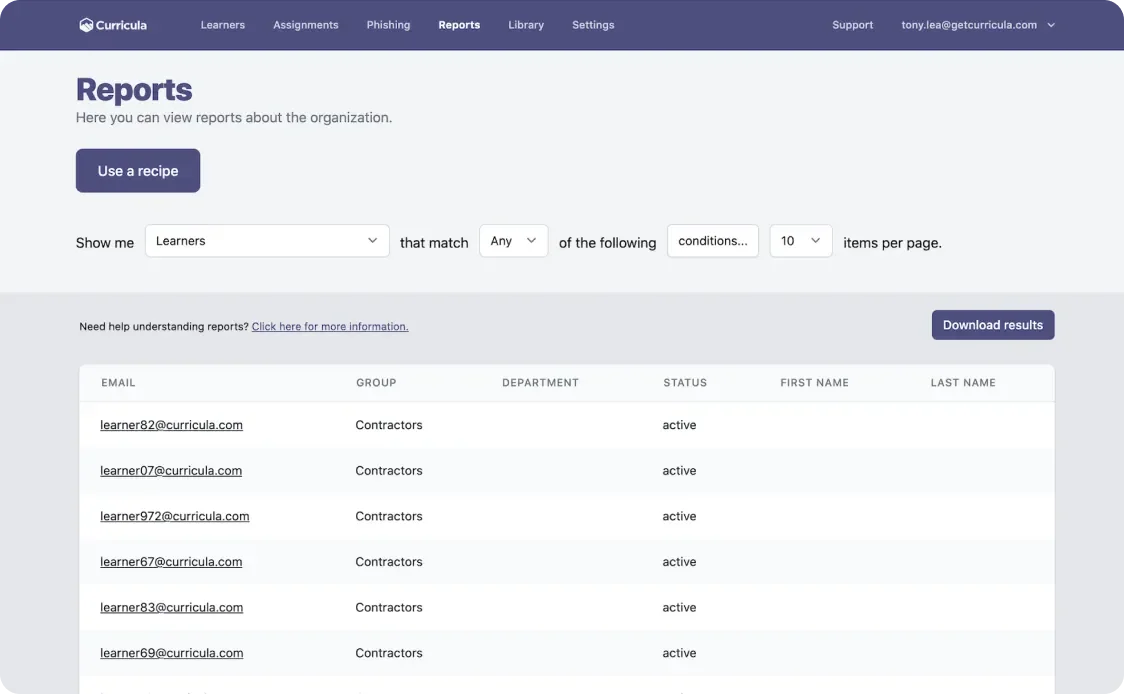
SOC 2 Compliance audits can be stressful, but not with Huntress SAT. Snapshot all of your security awareness training evidence and records in seconds. Your auditors will thank you for using Huntress SAT to demonstrate SOC 2 compliance of your required security awareness training program.
As your business grows, so do your regulations. Many customers will require your organization to achieve certain compliance certifications, such as SOC 2.
Huntress SAT will help you achieve SOC 2 compliance by training your employees and providing documentation for auditors. You could be on your way to a safer, more effective SOC 2 information security awareness training program with Huntress SAT—it only takes a few minutes.
Below you will find some of the most frequently asked questions about SOC 2.
No. In fact, SOC 2 isn’t a legal requirement for anyone. But with that being said SOC 2 is one of the most common compliance frameworks that organizations use to demonstrate security and compliance for protecting customer data.
Security is the only required criteria as part of any SOC 2 audit. Below is a summary of the five trust services criteria.
No. While SOC 2 may outline the controls needed, it is up to you and your organization to define what and how those controls operate. There is a lot of flexibility in SOC 2 that your auditor will ask how and why you got to your conclusion to implement those controls. Then they will ensure they are operating as expected.
What people are saying about Huntress Managed Security Awareness Training