Cyber hygiene: Hackers love a mess
Good cyber hygiene isn’t a suggestion—it’s a must. Just like you wouldn’t skip brushing your teeth for weeks (we hope), you can’t ignore the security basics. Because when hygiene slips, attackers don’t hesitate to exploit the mess.
At Huntress, we see firsthand how poor credential management, misconfigurations, and forgotten accounts open the door to serious threats. But, we also see how a vigilant, expert Security Operations Center (SOC) and Managed Endpoint Detection and Response (EDR) turn the tables on malicious hackers. Let’s break down some real-world examples of hygiene failures, the chaos they caused, and how our team shut them down.
A forgotten account, a wide-open door
Credential hygiene is non-negotiable. A doctor’s credentials were compromised, giving a threat actor remote access to a medical network. From there, they:
✅ Moved laterally across systems
✅ Manipulated local firewalls to open pathways for deeper access
✅ Exploited an abandoned account from a former employee
The worst part is that account had been sitting there, unused for months. It was like an open invitation for attackers to walk right in. But our SOC caught the intrusion early, stopped their lateral movement, and helped the organization clean up their account hygiene for good.
Lesson learned: Regularly audit user accounts and disable access the minute an employee leaves. In other words, don’t leave doors unlocked.
"SOC Incident Walkthrough" with Anton Ovrutsky
Brute force meets bad hygiene
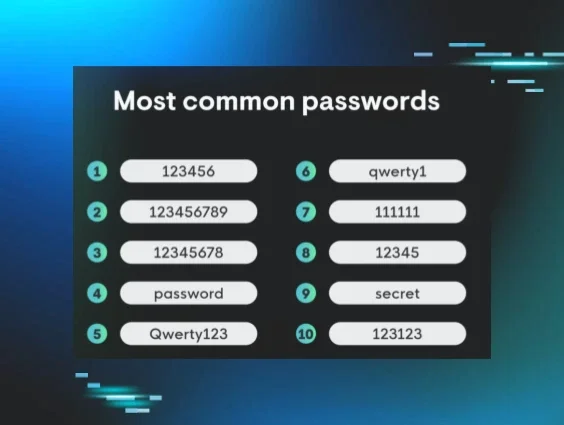
If at first you don't succeed, try again! A threat actor brute forced a manufacturer’s virtual private network (VPN) appliance and eventually cracked one account’s credentials, gaining a foothold inside the environment.
Once inside, they:
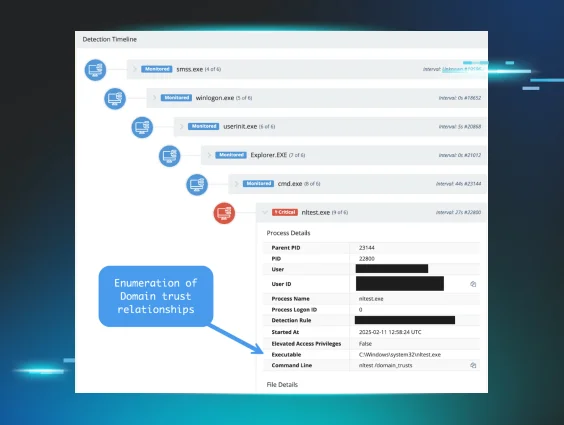
✅ Enumerated the domain, focusing on trust relationships and domain controllers
✅ Modified the registry and local firewall to enable lateral movement via RDP
Fortunately, our SOC caught them before they could spread further, cutting off access before real damage could be done.
Lesson learned: Enable multi-factor authentication (MFA) for all externally facing services, enforce strong passwords, and consider time-of-day restrictions for authentication.
A critical alert in the Huntress portal showing enumeration of Domain trust relationships
Logs showing firewall manipulation and registry modification
VPN compromise: The stealthy breach
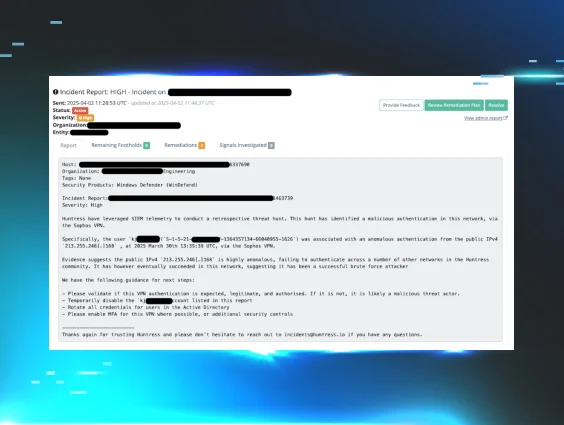
A threat actor gained unauthorized VPN access through compromised credentials at an industrial supply company. Once inside, they wasted no time:
✅ Creating local Administrator accounts on multiple hosts
✅ Modifying Windows Firewall settings to enable RDP access
✅ Running reconnaissance tools to map out the domain
The problem was the compromised credentials looked legitimate at first glance. But when our SOC started pulling investigative threads, we spotted the attack, stopped it, and worked with the partner to tighten VPN security.
Lesson learned: If you’re not monitoring VPN access, you’re flying blind. MFA is a must, and logging is your best friend.
An incident report from the Huntress portal showing our investigative process
Credential theft: Defending against it
Threat actors compromised the Fortigate VPN at a container manufacturing company and got their hands on a legitimate Active Directory account. Their next move?
✅ Try to steal credentials by dumping the Windows Registry
✅ Use compromised credentials to pivot deeper into the network
✅ Establish persistence for future attacks
Microsoft Defender caught the credential theft attempt and raised the alarm, but our SOC didn’t stop there. We dug deeper, traced the attack back to its source, and helped our partner lock down their VPN to prevent a repeat incident.
Lesson learned: Malicious hackers love to steal credentials. A strong defense means monitoring, early detection, and making sure your VPN isn’t an easy target.
A high-priority alert in the Huntress portal triggered by registry dumping
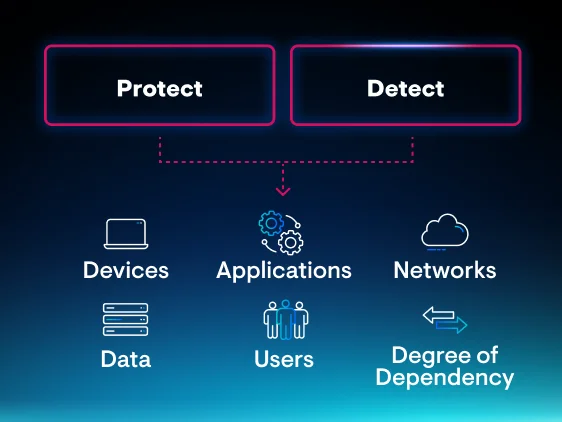
Bottom line: Cyber hygiene isn’t optional
Every single one of these attacks could’ve been worse—stolen data, ransomware, full domain compromise. But catching threats early and enforcing basic security hygiene made all the difference.
So ask yourself, “When was the last time I cleaned up my credentials?”
If you’re not sure—or if you’ve got lingering doubts—it’s time to put your defenses to the test. (Ab)use our free trial and find out if your cyber hygiene is up to par. Because attackers aren’t waiting, and neither should you.