At Huntress, we’ve made our name catching and wrecking the hackers who slip past defenses. Now, we’re making it hard for them to even get a foothold.
We're thrilled to announce the expansion of the Huntress Agentic Security Platform with two new proactive offerings: Managed Endpoint Security Posture Management (ESPM) and Managed Identity Security Posture Management (ISPM), both in Early Access.
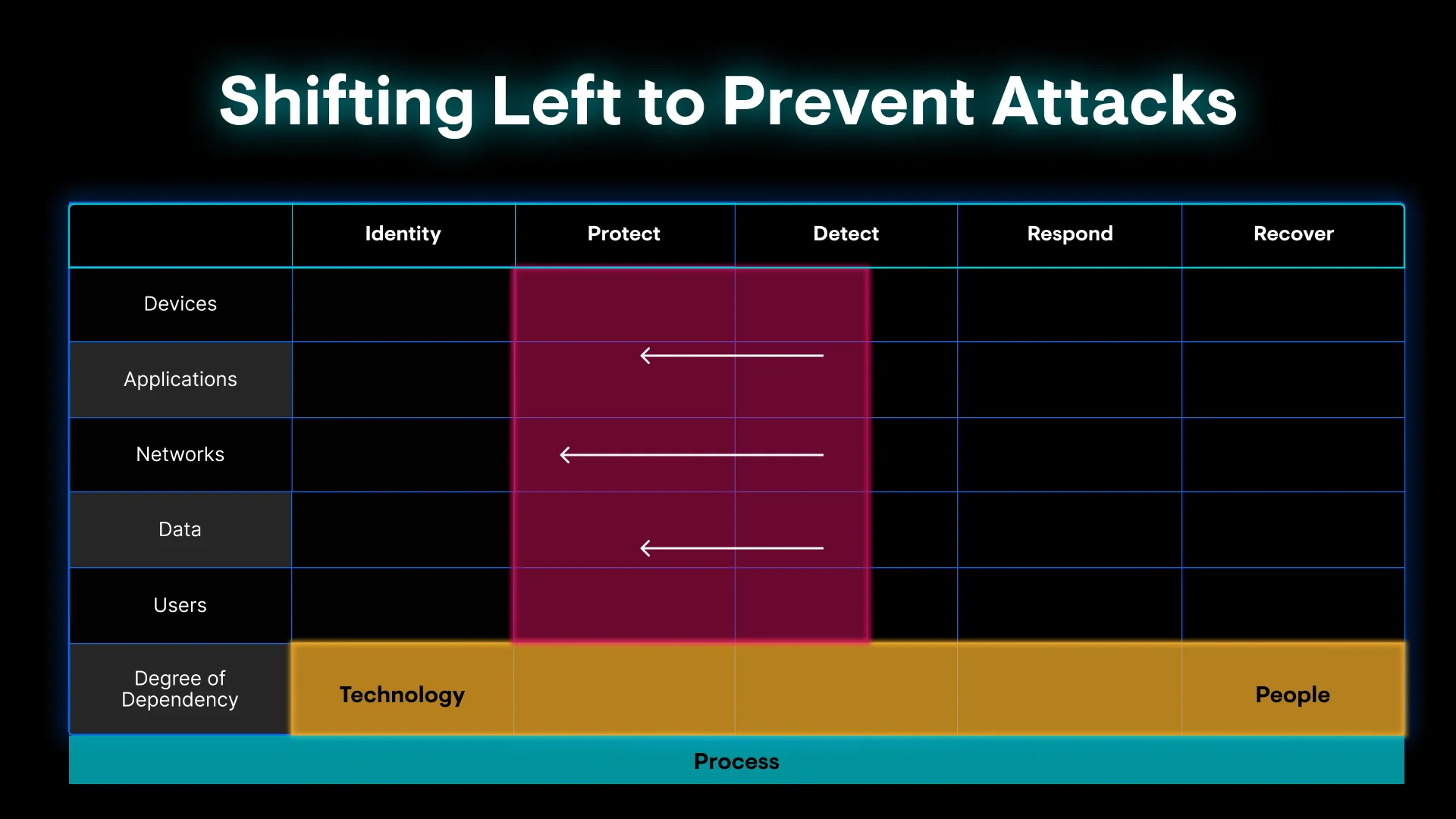
Why we’re shifting left
The reality of modern cybersecurity is that attackers don’t just “break in"—they simply log in using the gaps we leave open for them. Those gaps are the everyday “self fails” we all recognize: the legacy system nobody wants to touch, the “temporary” exception that became permanent, the one account that somehow never got multi-factor authentication (MFA) implemented, or the installed apps IT didn’t even know about.
Our 2026 Cyber Threat Report puts hard numbers behind those skeletons in the closet. We’ve seen a 277% surge in the abuse of remote monitoring and management (RMM) tools, as attackers turn trusted admin software into their own covert access channel.
The report also notes logins with a shady footprint—risky locations, malicious networks, or sketchy VPNs—now make up 37% of all identity threats we investigate.
Most organizations know they need to be more proactive and harden their environments, but they lack the bandwidth to constantly chase configuration drift, new and updated applications, or understand every nuance of how a new control will impact users. So the “spring cleaning” never really happens, and those self‑inflicted gaps are exactly what attackers monetize.
With ESPM and ISPM, we’re moving beyond detection and response into prevention. We’re translating the hacker tradecraft and threat intelligence gathered from the 4.8 million endpoints and 10 million identities we protect into proactive capabilities to stop more attacks before they ever start.
Turning "self fails" into real-world lessons
The Huntress SOC doesn’t just battle elite zero‑days. Often, incidents are caused by the quiet, messy reality of unauthorized apps, over-privileged accounts, and misconfigurations that overstretched teams never get around to cleaning up.
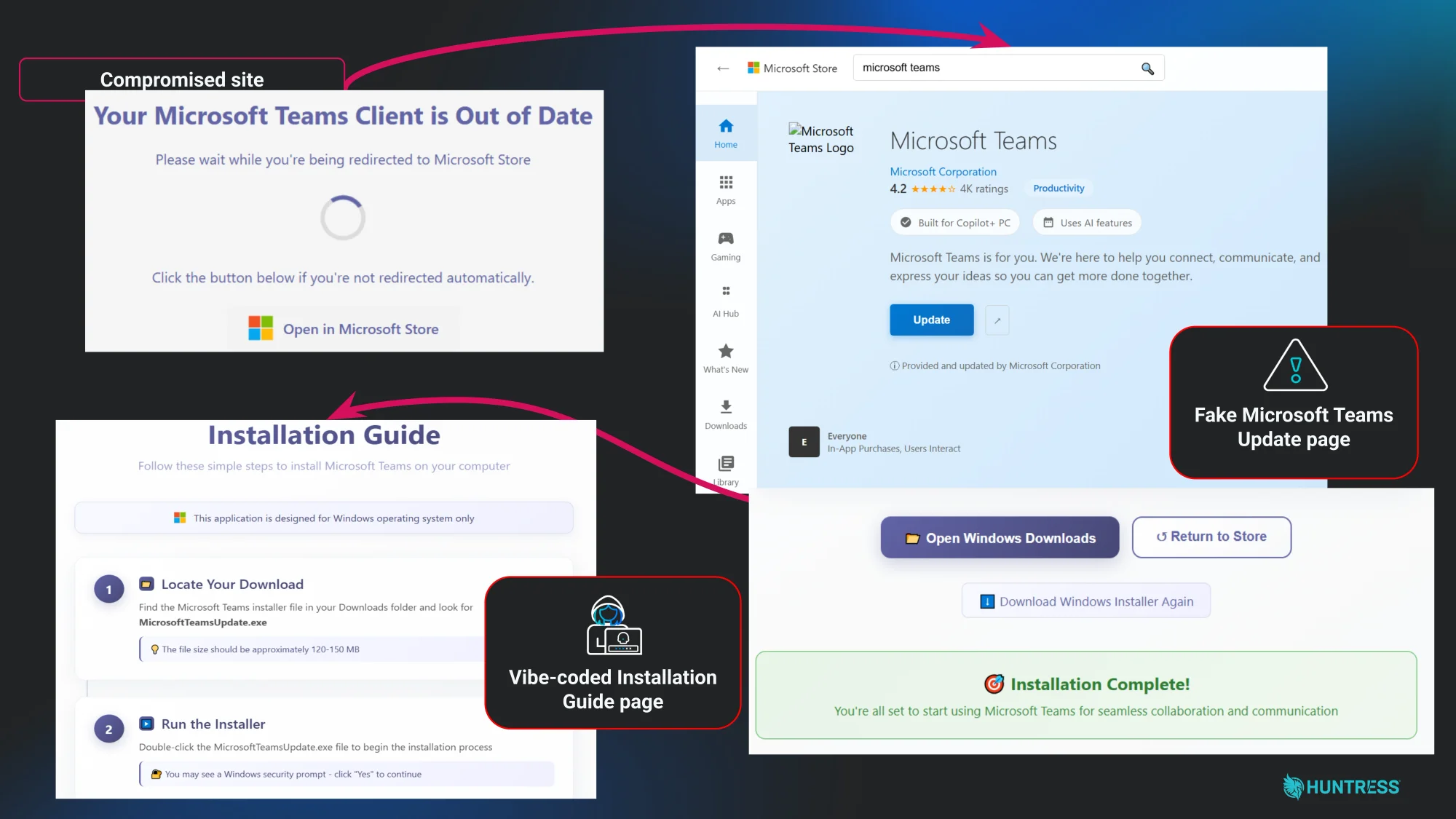
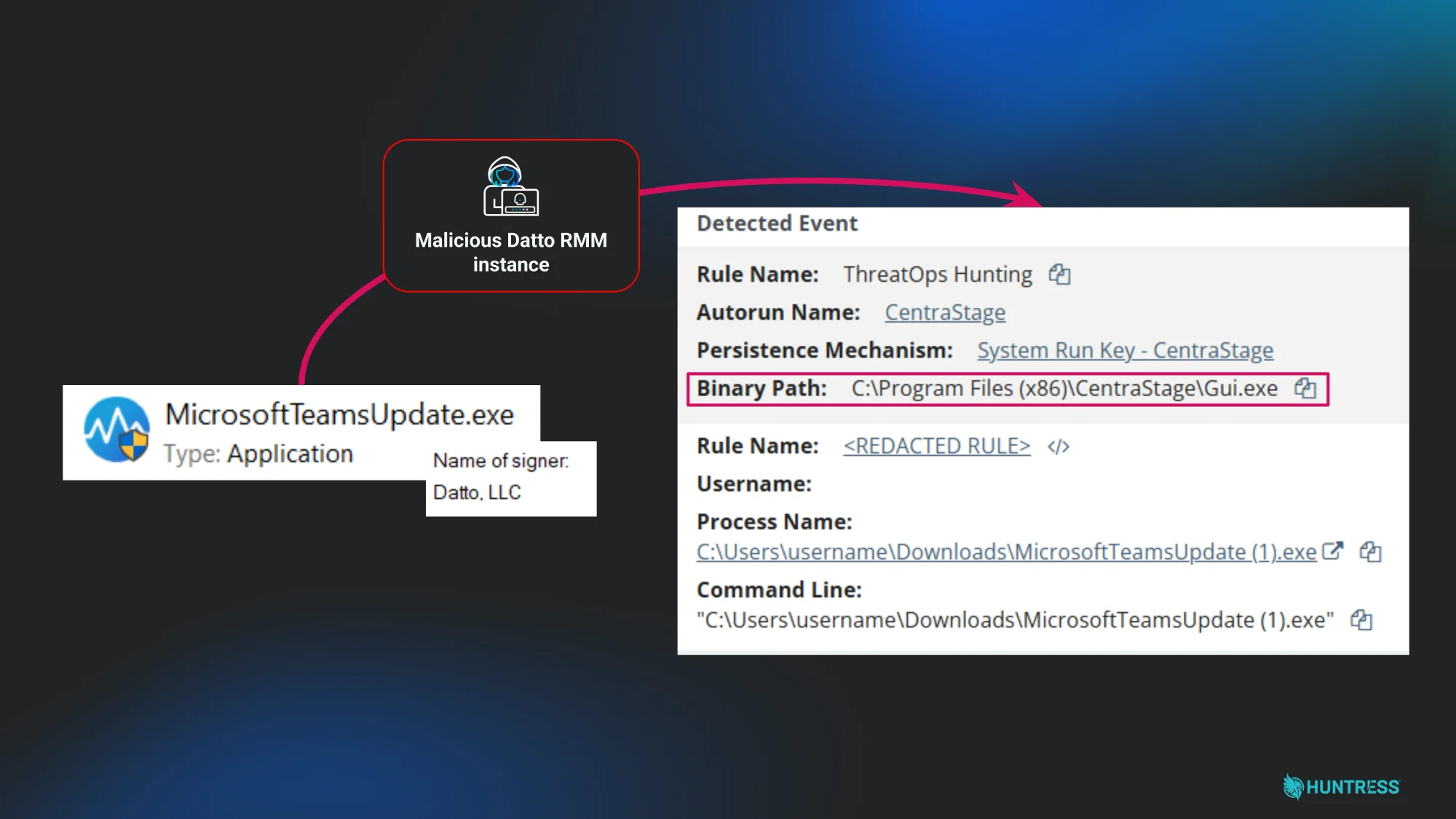
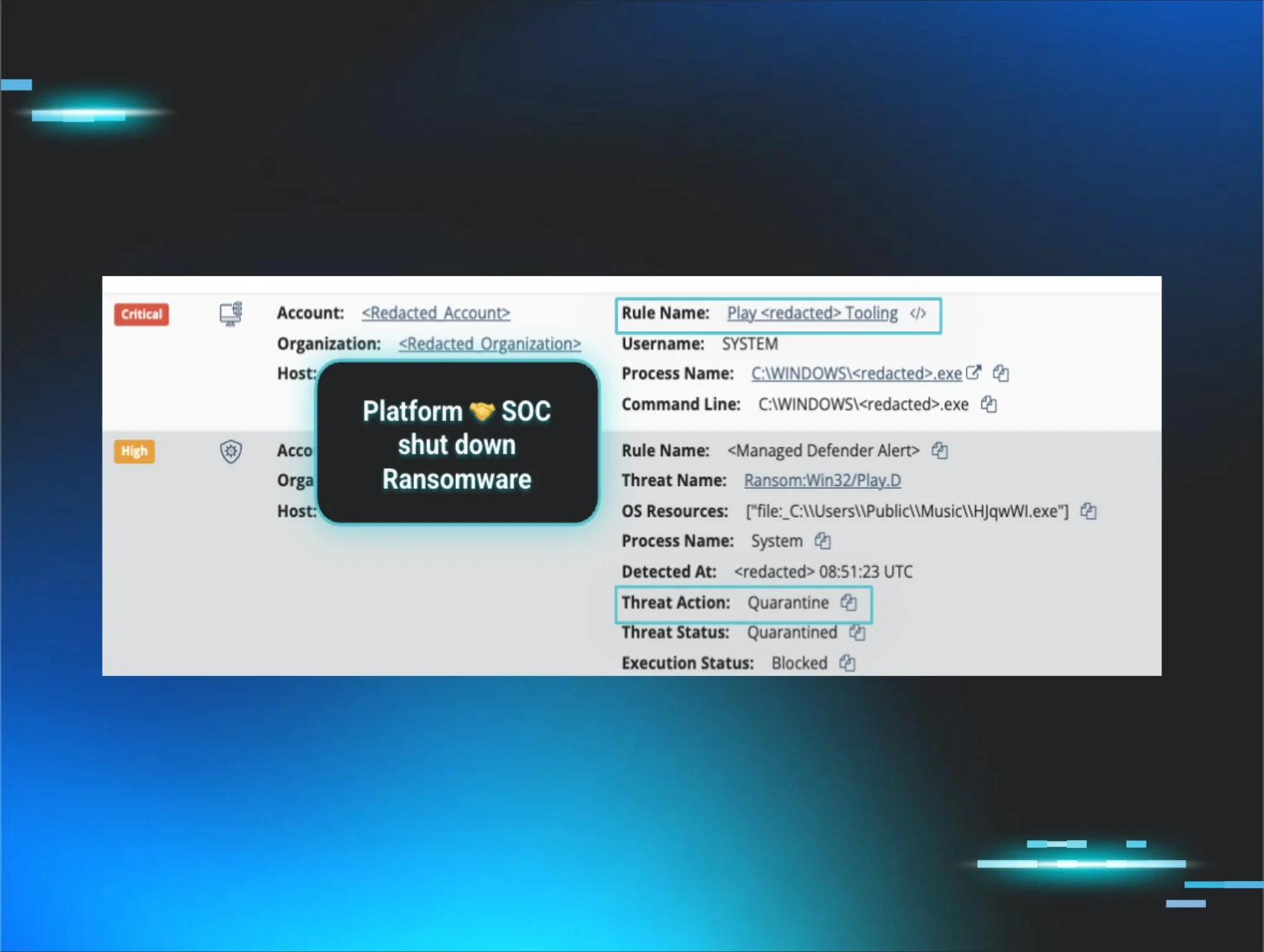
Rogue Datto RMM via fake Microsoft Store update
In a terrible tools‑turned‑against‑you moment, a user received a phishing email that sent them to what looked like a pixel‑perfect Microsoft Store page with star ratings, polished branding, and an emoji‑filled install guide. The site was actually hosted on a compromised domain, and the “update” they downloaded, MicrosoftTeamsUpdate.exe, was digitally signed by Datto, LLC.
Instead of dropping obvious malware, the attacker used it to deploy a rogue Datto RMM instance—“bring your own RMM” persistence hiding behind a trusted vendor signature that traditional AV is likely to ignore. The Tactical Response team within the Huntress SOC stepped in to remediate the rogue RMM and rip out the foothold.
Images depict an incident shut down by the Huntress AI-centric SOC caused by a rogue Datto RMM
This story underlines why endpoint security posture management matters: you have to know which RMM tools are allowed, where they came from, and when a “legitimate” agent suddenly appears in the wrong place at the wrong time.
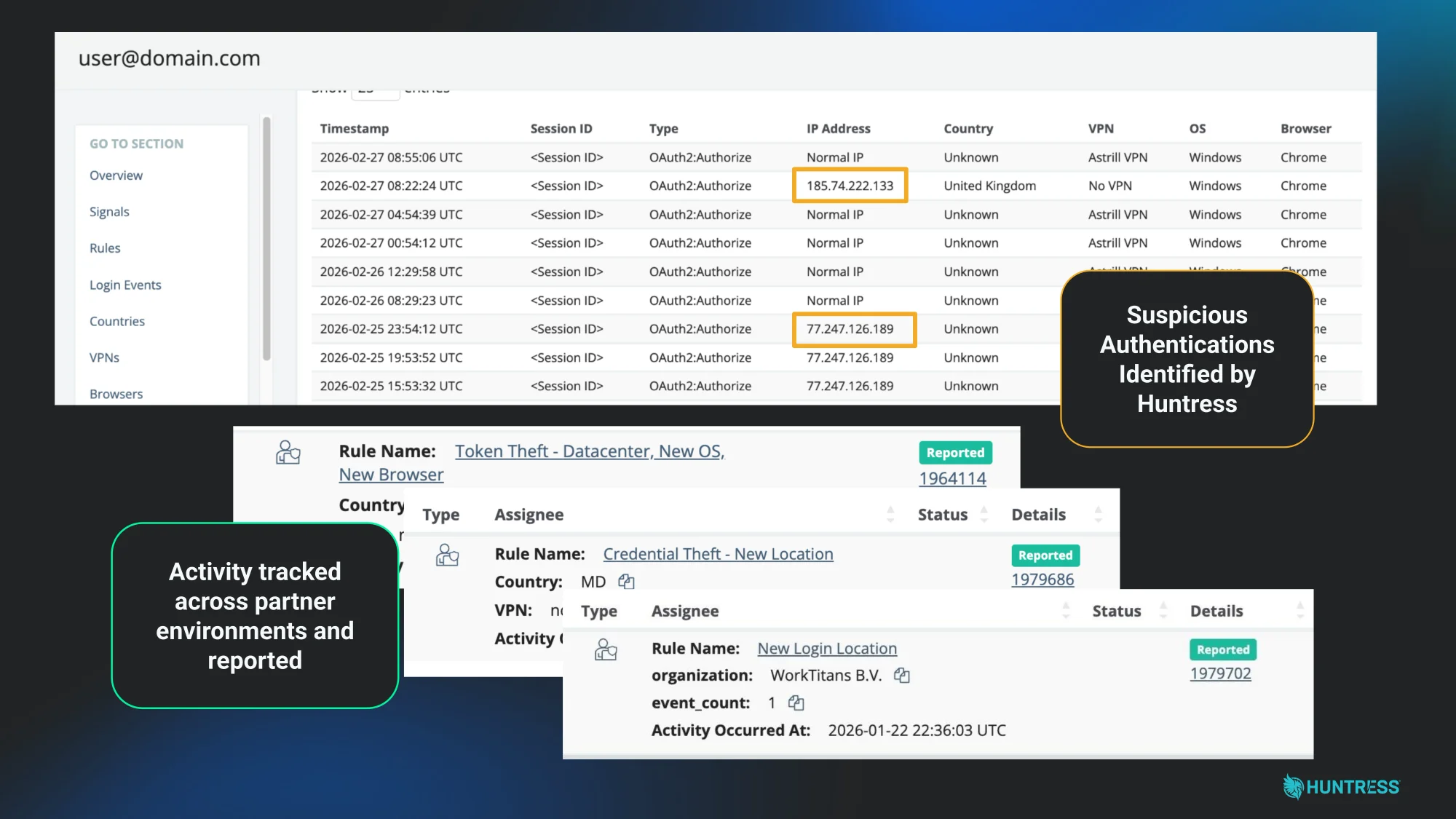
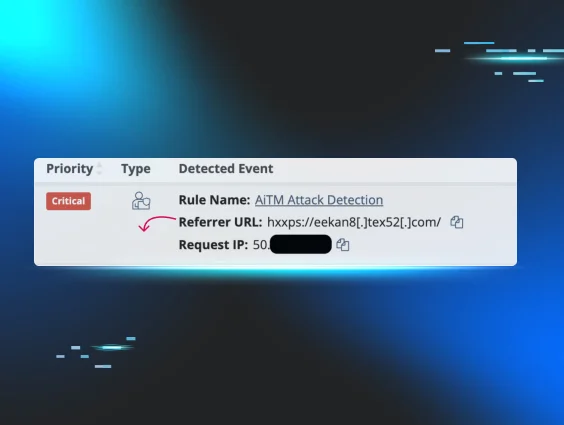
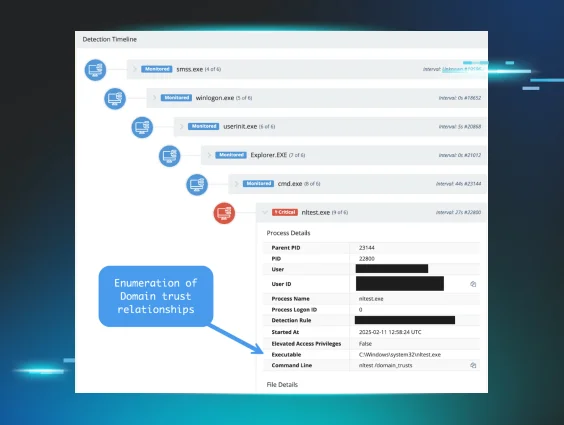
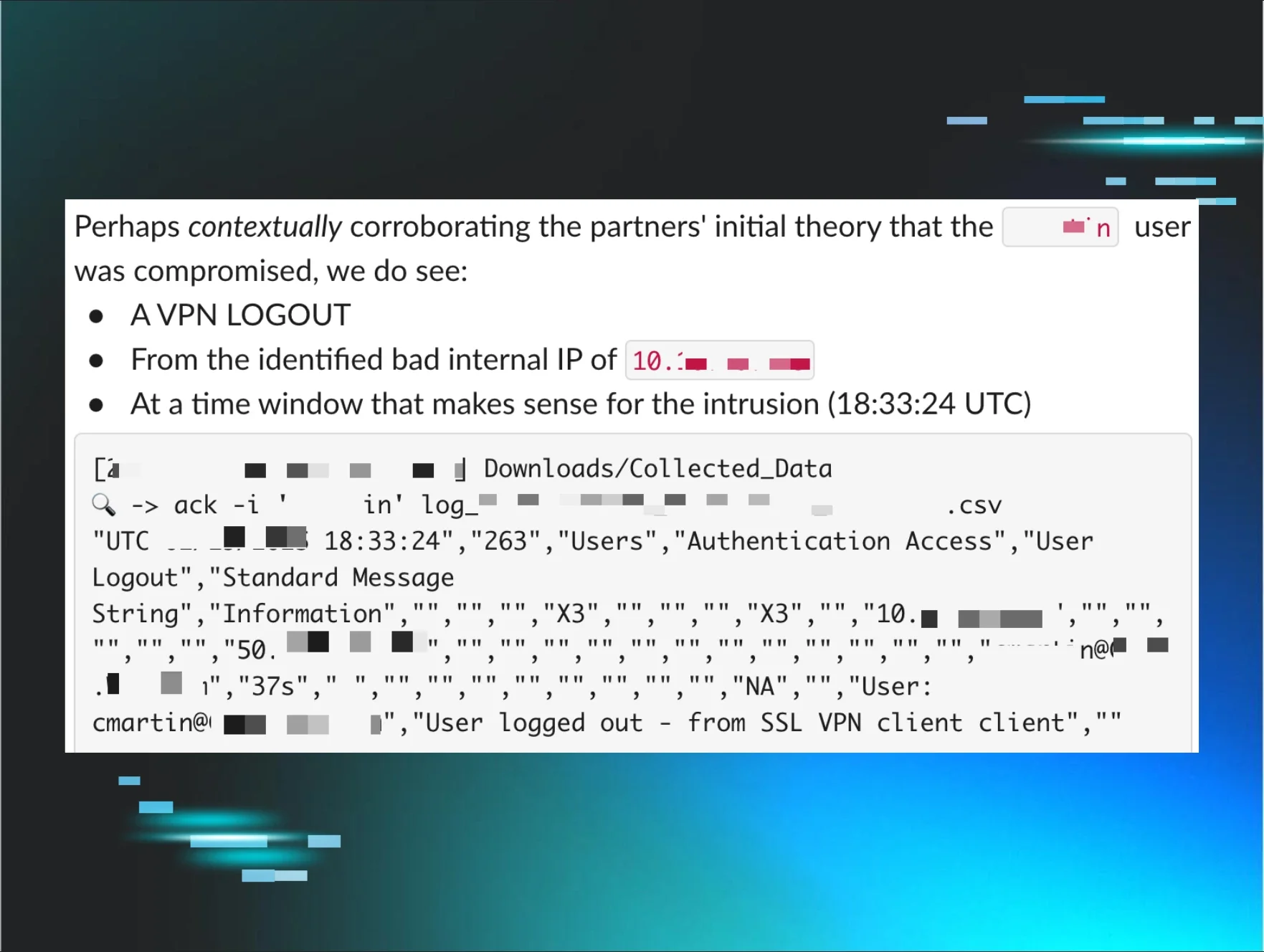
The one VPN account without MFA
In another recent incident, the Huntress AI-centric SOC detected a suspicious identity compromise originating from a highly unusual datacenter location.
When the team investigated, the root cause was a single user account that had somehow slipped through the cracks and was missing MFA. The threat actor easily bypassed standard login protocols, authenticating from a shadowy hosting provider known as "WorkTitans B.V."
An ITDR incident shut down by the Huntress AI-centric SOC caused by a single MFA gap
Once inside, the attacker immediately went to work. Instead of trying to break through the company's external defenses, they used their newly acquired, trusted internal account to blast out a wave of internal malicious emails. Because these emails were coming from inside the house, they bypassed nearly all of the organization's perimeter-oriented email defenses.
To make matters worse, our threat intelligence linked the attacker's tradecraft and infrastructure directly to overlapping activity with North Korean cybercrime syndicates. The stakes couldn't have been higher: an advanced, financially motivated threat actor lurking silently in the cloud.
The Huntress SOC immediately disabled the compromised identity to stop the internal phishing campaign in its tracks. This scenario highlights exactly why Managed ISPM is a necessity. It's incredibly difficult to ensure configurations are standardized 100% of the time. Managed ISPM continuously audits your identity posture to catch that one account missing MFA long before a nation-state actor finds it and uses it to bypass your perimeter
Taking the complexity out of posture management
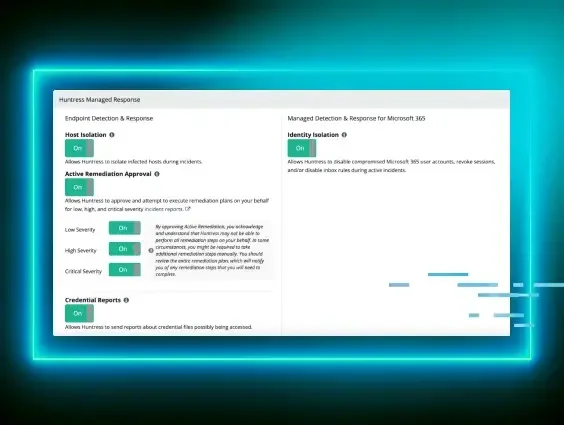
ESPM and ISPM are designed to take the required expertise and technical complexity of posture management off your plate and ensure a consistent, hardened security state across endpoints and identities to shrink your attack surface and reduce the number of security incidents.
Managed ESPM: Making endpoints attack-resistant
Managed ESPM reduces the attack surface hackers can abuse to compromise endpoints and get a foothold to apply their tradecraft. Managed ESPM shuts down the most common attack avenues–exploiting vulnerabilities and misconfigurations, installing their tools, and abusing legitimate apps–to make it hard for hackers to achieve their malicious objectives, like ransoming your data and systems, or stealing credentials.
Managed ISPM: Securing the new perimeter
Identity is the new perimeter, and that perimeter is often a mess of bad defaults and over-privileged accounts. Managed ISPM provides ongoing posture assessments for Microsoft 365, tapping into Entra ID and Conditional Access.
This isn't just a list of configs for you to maintain. We provide Managed Security Policies based on our expert identity security framework, informed by the tactics our SOC sees in the wild every day. Then we perform Continuous Enforcement to detect when settings drift from best practices and bring them back to a secure state automatically.
Our 2025 incident data shows that access policy and trust‑boundary violations—“shady” logins and risky access patterns—are the most common identity threats, followed closely by mailbox manipulation and persistence that often signal business email compromise (BEC). Managed ISPM is designed to harden those paths, so fewer of those threats ever become incidents to clean up.
The big picture: Unified defense for greater resilience
These new products weren’t built in silos; they're the proactive "left-of-boom" side of the Huntress platform.
-
Managed ESPM and Managed ISPM (along with our Managed Security Awareness Training) shrink the attack surface to stop easy wins for attackers.
-
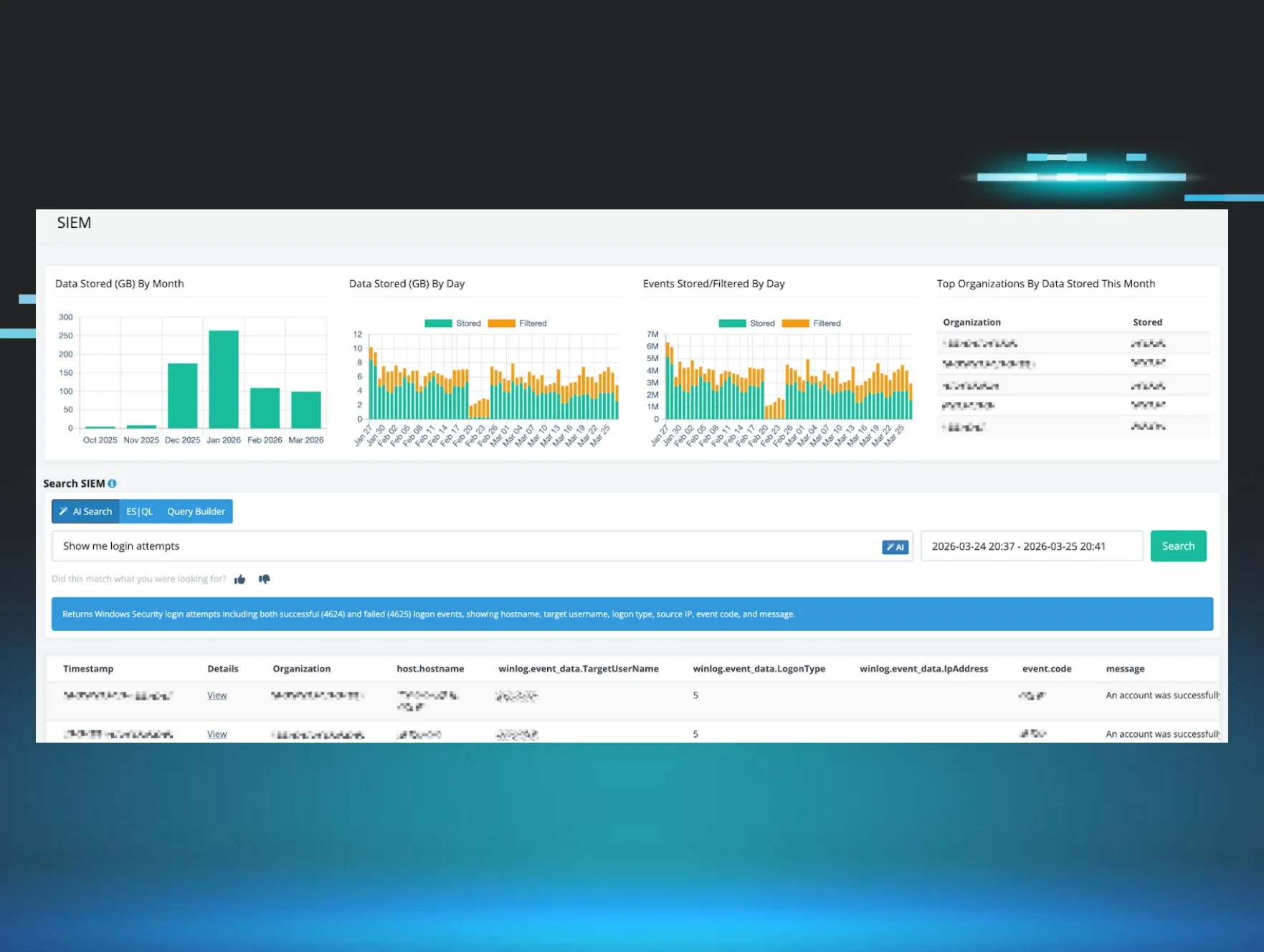
Managed EDR, Managed ITDR, and Managed SIEM (along with our 24/7 SOC) detect and respond to the attacks that breach defenses and require fast containment and remediation.
The result is a tighter loop. We see what attackers are doing in the wild, update our posture frameworks, and enforce those changes across your environment. When prevention falls short, we’re there to shut attackers down and kick them out before they can do damage.
Join Early Access
If you’re ready to stop attackers from treating your endpoints and identities like low‑hanging fruit:
-
Visit the Managed ESPM and Managed ISPM product pages to learn more.
-
If you’re an existing customer or partner, talk to your Huntress Account Manager about joining Early Access and whether your current deployment qualifies to try it for free.
We’re excited about the journey to come between now and General Availability later this summer. In the meantime, we’ll keep digging into real attacker tradecraft, telling honest stories about what we see in the wild, and turning those lessons into managed outcomes that make your environment harder to abuse and easier to defend.