There’s been a lot of chatter lately around two-factor authentication (2FA) and multi-factor authentication (MFA). We’re seeing more and more websites and applications enforcing 2FA—like Google recently announcing 2FA will be turned on by default for all accounts, plus Huntress has already hopped on the enforced MFA bandwagon.
But that led us to wonder: How easy is it for malicious threat actors to circumvent 2FA?
In a recent Tradecraft Tuesday episode, we talked about the various types of 2FA and if there’s a “right way” to set up 2FA (or even better, MFA). You can re-watch the episode here, or keep reading for some key takeaways and to see how easy it can be to sneak past 2FA.
What Is 2FA?
Two-factor authentication is a verification method that requires users to provide at least two forms of identification in order to access something.
Rather than just asking for a username and password, 2FA requires an additional verification factor, which can decrease the likelihood of a successful cyberattack. These factors can include:
- Knowledge (something only the user knows)
- Possession (something only the user has)
- Inherence (something only the user is)
- Location (somewhere only the user is)
Why Is 2FA Used?
When you think of authentication, you probably think of the typical username and password (that's the single factor). But as we all know, those passwords can easily be stolen, shared, reused or compromised in some way.
Instead of relying on a single factor, 2FA adds an additional layer of security by requiring another or multiple forms of authentication—in theory, making it harder for hackers and unauthorized users to gain access to your accounts or devices.
How Attacker Bypass 2FA
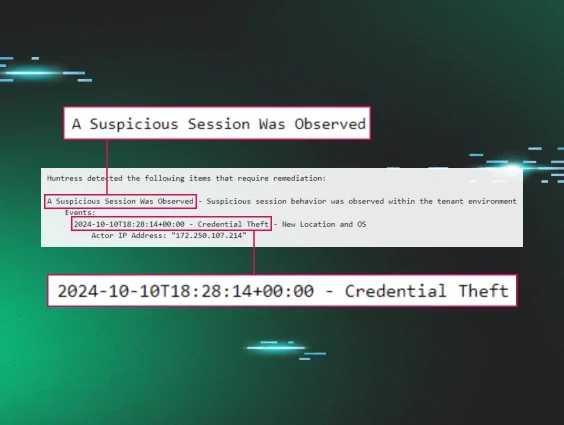
Because two-factor authentication adds that extra layer of security, a lot of people assume that makes it impenetrable. But, like almost anything these days, 2FA can be bypassed.
Let’s dive into just how easy it is to bypass 2FA. For the purposes of this example, we’re only going to pick on SMS-based authentication, which is a method that allows users to verify their identities with a code that is sent to them via text message.
The SIM Swapping Problem
As the avid cell phone and smartphone users that we all are, we know how phone carriers want to provide their customers with the best customer service. Unfortunately, that need to please can easily be exploited.
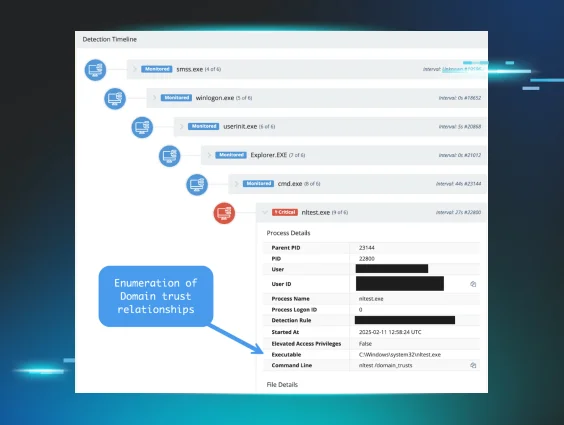
The image below illustrates how attackers can trick phone carriers through a tactic called SIM swapping. In a nutshell, SIM swapping is when a scammer steals your mobile phone number by assigning it to a new SIM card. By calling up your carrier’s customer service line and giving a few details about you, a hacker can claim that your original phone and SIM card were lost or destroyed and they have a new SIM card they’d like to activate.
Here’s a look at SIM swapping in action:

Let’s put this into the context of SMS-based 2FA. Can you see why SIM swapping could be a huge issue?
If an attacker knows your username and password and was successful in tricking your carrier into a SIM swap, once they enter your credentials now they receive the authentication code via text message and BOOM, they’re in. That so-called second factor is now bypassed—all because people are way more exploitable than technology.
Please note: We’re not trying to strike fear into your heart—actually, the most common targets of SIM swapping are celebrities, politicians or Forture 500 CEOs—but what we are trying to emphasize is that in this case, the security of your SMS authentication relies on the security of a third-party carrier, or lack thereof.
Is 2FA Worth Setting Up?
Yes, 100% it is. Layers are so important, and 2FA is another layer in your defense against attackers… but as we’ve seen, it isn’t perfect.
In our example, we showed just how bypassable SMS-based authentication is through SIM swapping or social engineering phone carriers. It’s clear that hackers are growing more sophisticated every day—with small amounts of information, there’s a lot of damage they can do. So if possible, avoid SMS-only authentication when you’re setting up 2FA.
And of course there’s the convenience argument. Some users will complain that 2FA is a pain for them because they need to take another step to log in. That’s understandable, but cybersecurity is always a trade-off. Given the sheer cost of security incidents today, a few extra steps are much less painful than dealing with a cyberattack.
And if there are a few key lessons we can leave you with, it’s these:
- Enable 2FA or MFA wherever possible. In addition to educating users to use unique passwords for each application, this will reduce the chance that their account is compromised.
- Leverage SSO with 2FA. This allows you to have a central location to disable user access.
- Educate your users on the benefits of using 2FA. Understanding the trade-offs may make the extra step less painful for users. And while we’re at it, remind users not to provide their 2FA tokens to anyone else.
If you want some more two-factor tips or want to see a live demo of a real 2FA bypass, watch our Tradecraft Tuesday episode here!