Every so often, the Huntress ThreatOps Team receives questions from our partners asking for our perspective on IT security and malware related issues. We typically respond with quick/tactical feedback and close the ticket afterwards. However, many of these responses are great lessons to learn from. With that in mind, we proudly present our very first Ask Huntress response.
The Backstory
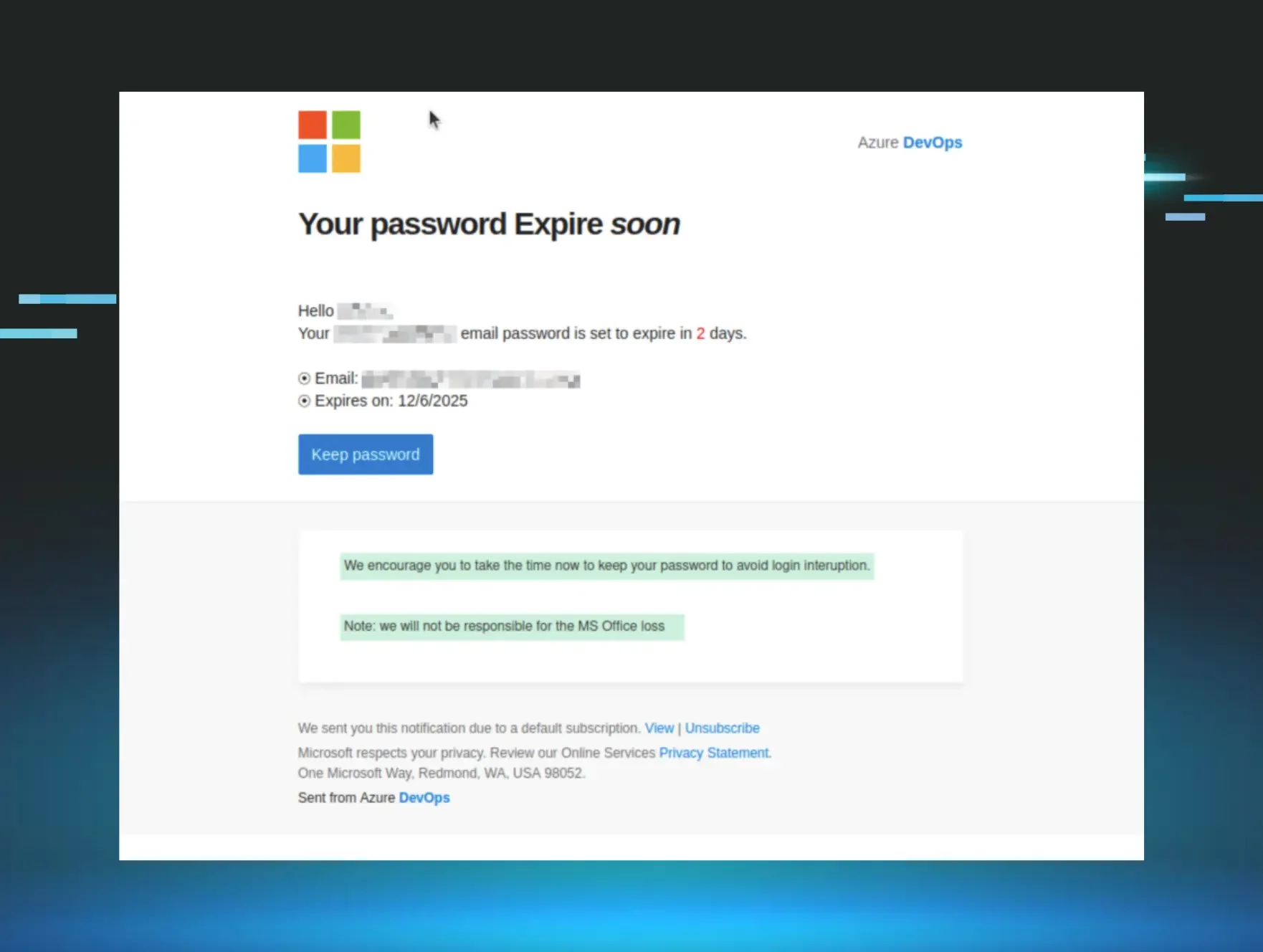
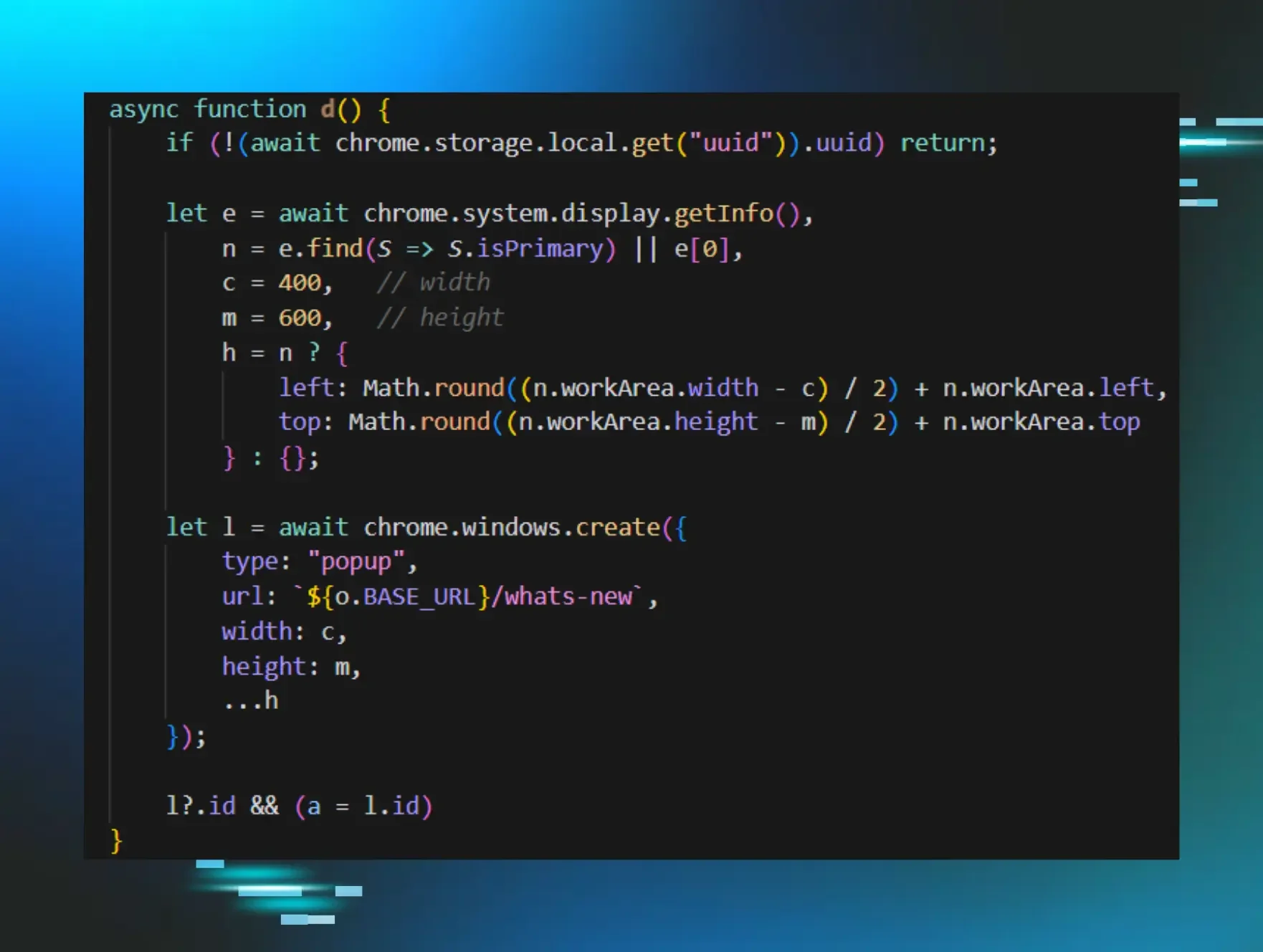
Today’s request came from a partner looking for feedback on how to defend against a campaign of phishing emails that slipped past their anti-spam solution. They forwarded our ThreatOps Team a copy of the phishing email and immediately we noticed it was tailored to impersonate the targeted company (in this blog, all company references have been replaced with VICTIMCOMPANY):
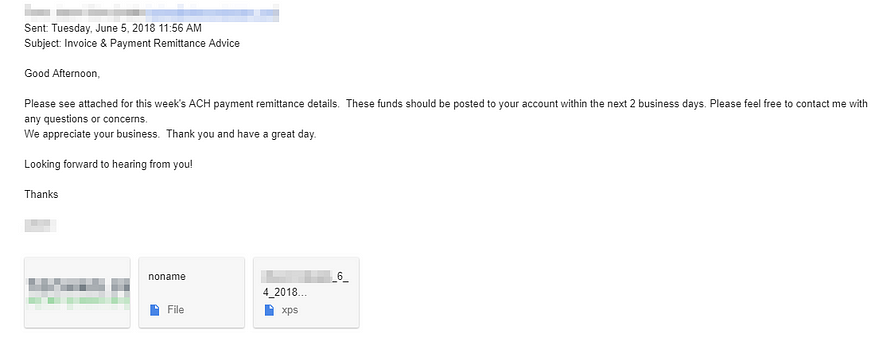
This phishing campaign used the age-old “Please remit payment” spiel to lure potential victims into opening the attached file. Although many of these attacks use tainted Microsoft Office documents, this particular email used an XML Paper Specification (.XPS) file. On Windows, the built-in XPS Viewer software will natively open these for you. Based on the attachment file name “VICTIMCOMPANY_6_4_2018 67389_pdf.xps”, it appeared the attacker attempted to convince recipients that this file was actually a form of .PDF file.
Upon opening the attachment (within a sandboxed malware analysis environment), our suspicions were confirmed. This file was designed to convince people to click the “DOWNLOAD PDF” button. It also included text to warn the user that they should be prepared to provide their “professional email Credentials” in order to open this secure file 😉.
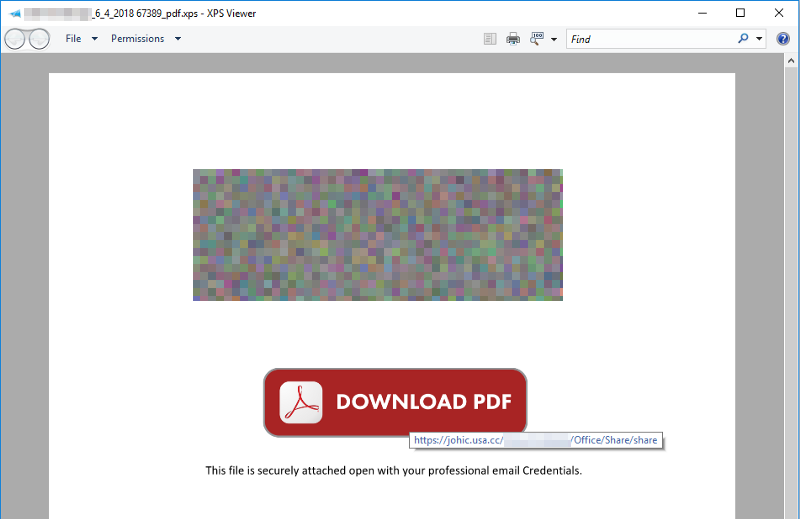
As illustrated in the above screenshot, hovering over “DOWNLOAD PDF” with your cursor revealed this button would take an unsuspecting victim to hxxps://johic.usa[.]cc/VICTIMCOMPANY/Office/Share/share. If you examine the URL, you can see the attacker even sprinkled a bit of social engineering into the mix by adding the “VICTIMCOMPANY” subdirectory to the web address. When our ThreatOps Team attempted to visit this site, it was already taken down. However, the fantastic URLScan.io website allowed us to recover a screenshot of what a similar credential harvesting attempt on the same subdomain looked like:
As you can see, the attacker mocked up content to look like Adobe Reader with a blurred invoice. Next, they used a pop-up to solicit the email address and password from the victim in order to “Open This Document”. Albeit unsophisticated, this general approach to deceive users often works like a charm. So what can we do about?
Layered Defense Advice
In this section of our Ask Huntress response, we’ll quickly share a few ways to deny, degrade, and disrupt the previously discussed scenario. To add a bit of structure, we’ll loosely follow Lockheed’s Cyber Kill Chain® framework when applicable.

Delivery: The attacker’s entire strategy hinged on the fact that recipients would be enticed to open an email attachment from a VICTIMCOMPANY employee. In this particular case, the email was sent from an open mail relay so checking Sender Policy Framework records could have screened this email (assuming the domain published their SPF records 😉. With that being said, SPF does not protect against attackers spoofing the “display name” or “header from” address — making user education a great first line of defense. Regularly validating users’ ability to question email authenticity and recognize common phishing strategies can go a long way. Lastly, you could always consider whether the .XPS file format should be accepted (unfortunately, techniques like this are generally brittle and risk hurting business productivity).

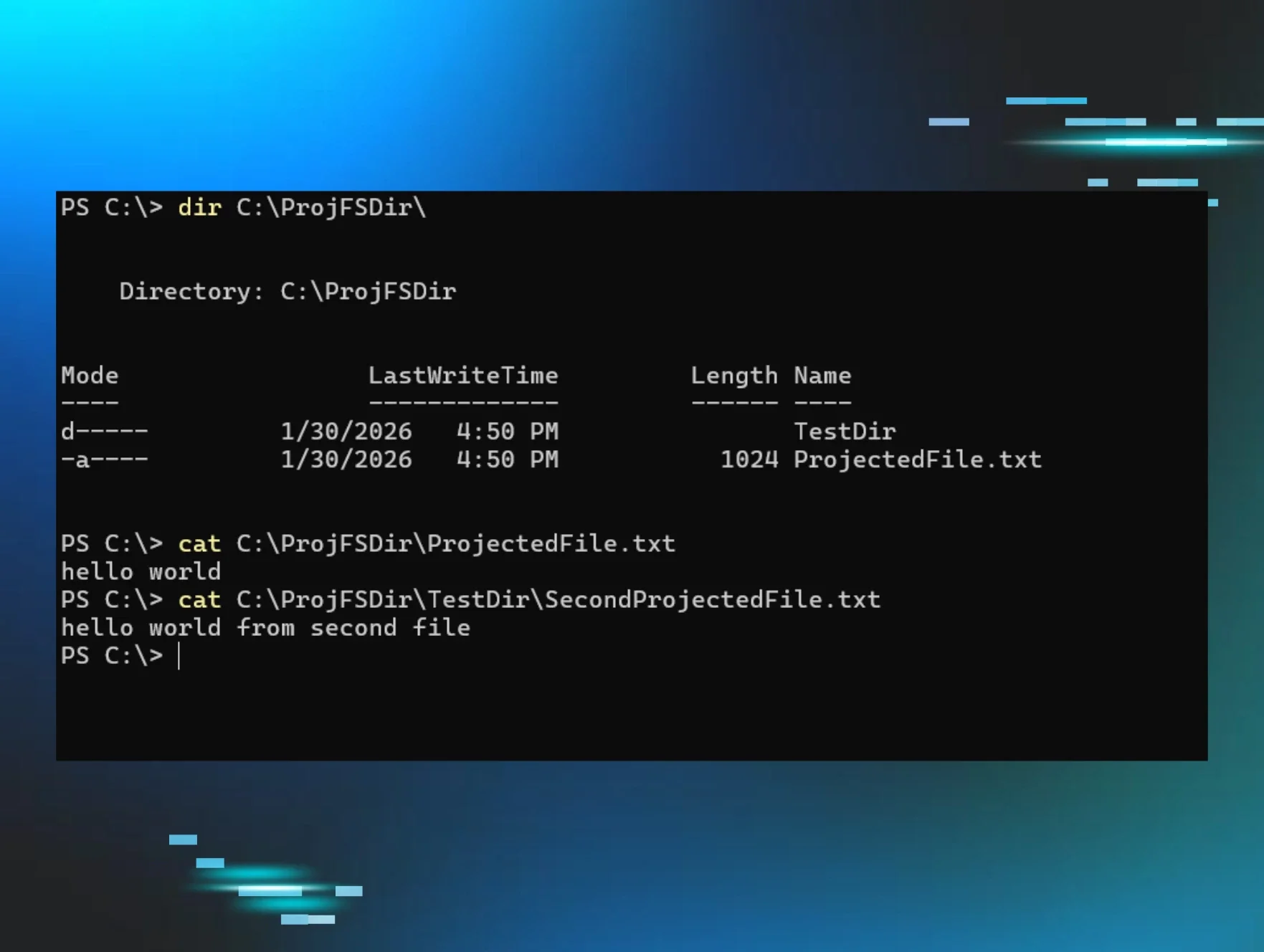
Exploitation: When it comes to cybersecurity, everyone wants to highlight how the offense only has to be right once. However, very few defenders consider that the same rule applies to foiling a hacker’s plan of attack. In this scenario, let’s assume the email was successfully delivered. If we can prevent the potential victim from ever visiting hxxps://johic.usa[.]cc/VICTIMCOMPANY, credentials will never be harvested. One of the most effective ways to do this is by checking the domain/URL’s reputation. For one off searches consider these free tools:
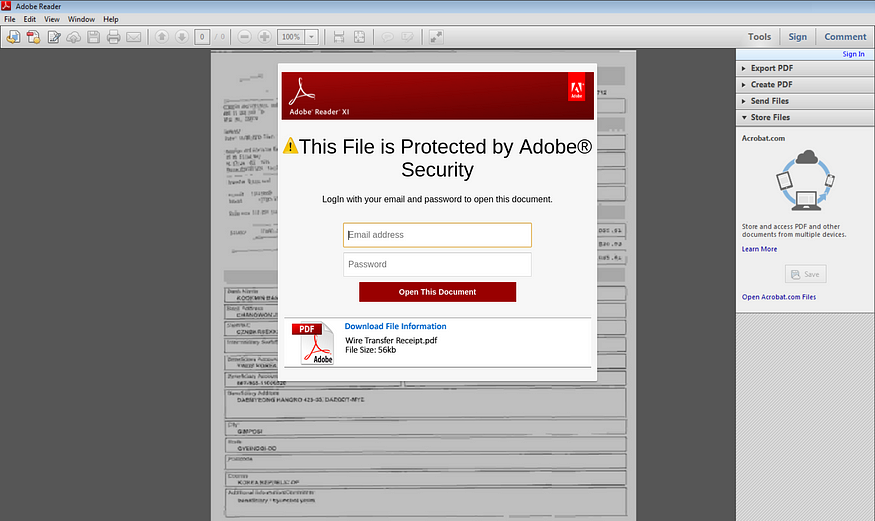
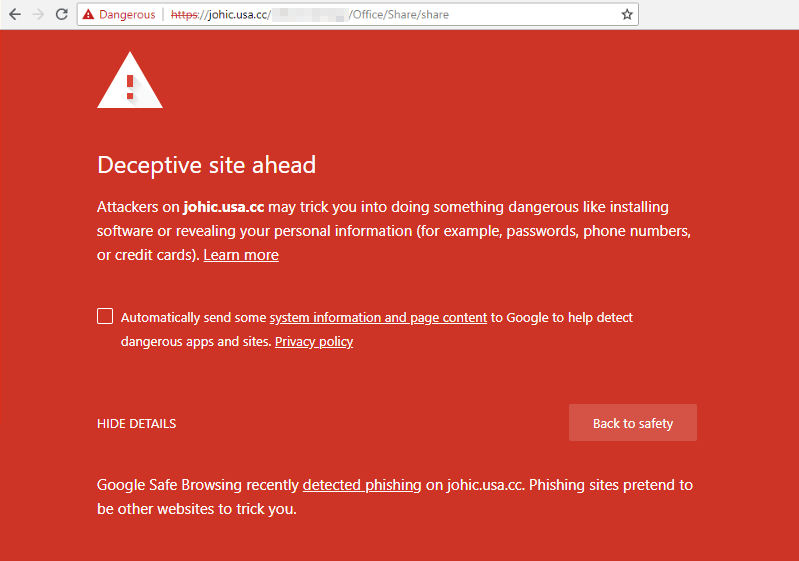
For automated reputation look-ups and blocking, there’s nearly a dozen security vendors who provide DNS reputation solutions for your routers, firewalls, and endpoints. It’s also worth mentioning that choosing a security focused web browser can also detect suspicious websites like this. Specifically, Google’s Chrome browser will not allow you visit this URL:
We can also deny the attacker from leveraging successfully gathered credentials by implementing multi-factor authentication (MFA). This phishing attempt was specifically going after email accounts. By leveraging Office 365 or G Suite’s built-in MFA, a compromised password would not be enough to give the attacker access (albeit password reuse issues may still exist).
Parting Thoughts
Nowadays, IT staff have to been keenly aware of what enables an attacker to be successful. With this knowledge, we can approach these hard-to-solve problems with a layered security approach. To address this specific scenario, our team would prioritize user security training/validation and multi-factor authentication to give us the best bang for the buck!
At Huntress, we invented a new layer of security specifically designed to disrupt hackers at the Installation Phase of the kill chain (we examine persistence mechanisms). Unlike antivirus, we don’t ask the question “Will this running application perform a malicious behavior?” Instead, we answer “Why is the application automatically running in the first place?”. This new approach complements your existing security investments and delivers you step-by-step remediation recommendations directly into your ticketing queue.
Looking to discover hacker footholds lurking within your networks? Sign up for our free trial and let us show you why our partners Ask Huntress!