The first alerts showed up on February 19. Then again, on February 24. Initially, it was just small blips in a sea of alerts. The types of alerts that don't amount to much.
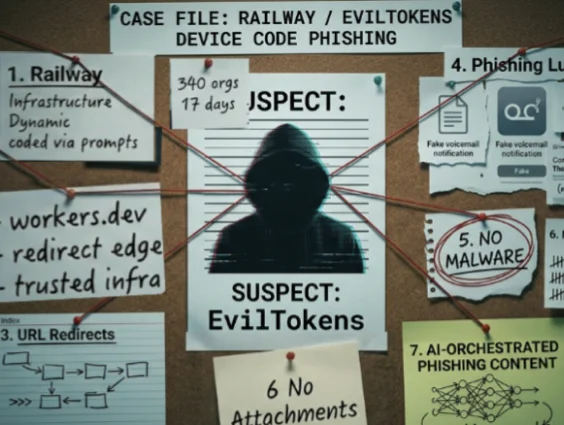
That all changed on March 2. What started as a trickle turned into a 16-day flood affecting 344 organizations across five countries. Within hours, Huntress was managing hundreds of incident reports, warning our partners and customers that the same device code phishing attack pattern was hitting organizations across the board at machine speed.
That campaign was EvilTokens, and it was clear that it wasn't just another phishing campaign.
In a recent discussion with Microsoft experts, EvilTokens: Big Cybercrime’s AI Platform Built to Bypass Your MFA, we broke down the mechanics of the campaign and what it reveals about the next phase of AI-enabled cybercrime.
How the EvilTokens device code phishing campaign was spotted
When our Security Operations Center (SOC) analysts started pulling the thread, they kept landing on Railway, a legitimate Platform-as-a-Service (PaaS) built for vibe coding. There were hundreds of login events, all routed through the same Railway infrastructure. That’s when the team knew this was more than just a blip. Something sketchy was happening when the same cloud IP address was hitting 50 organizations in a single week.
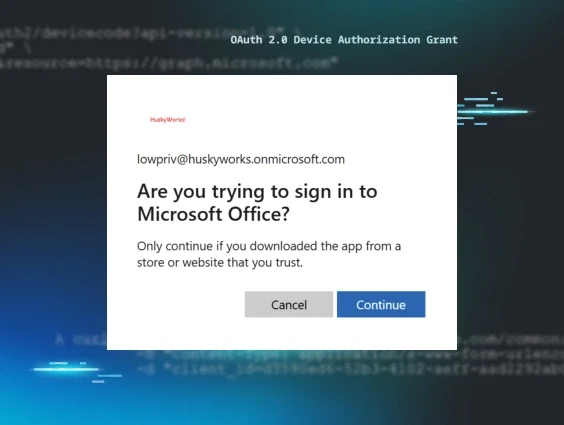
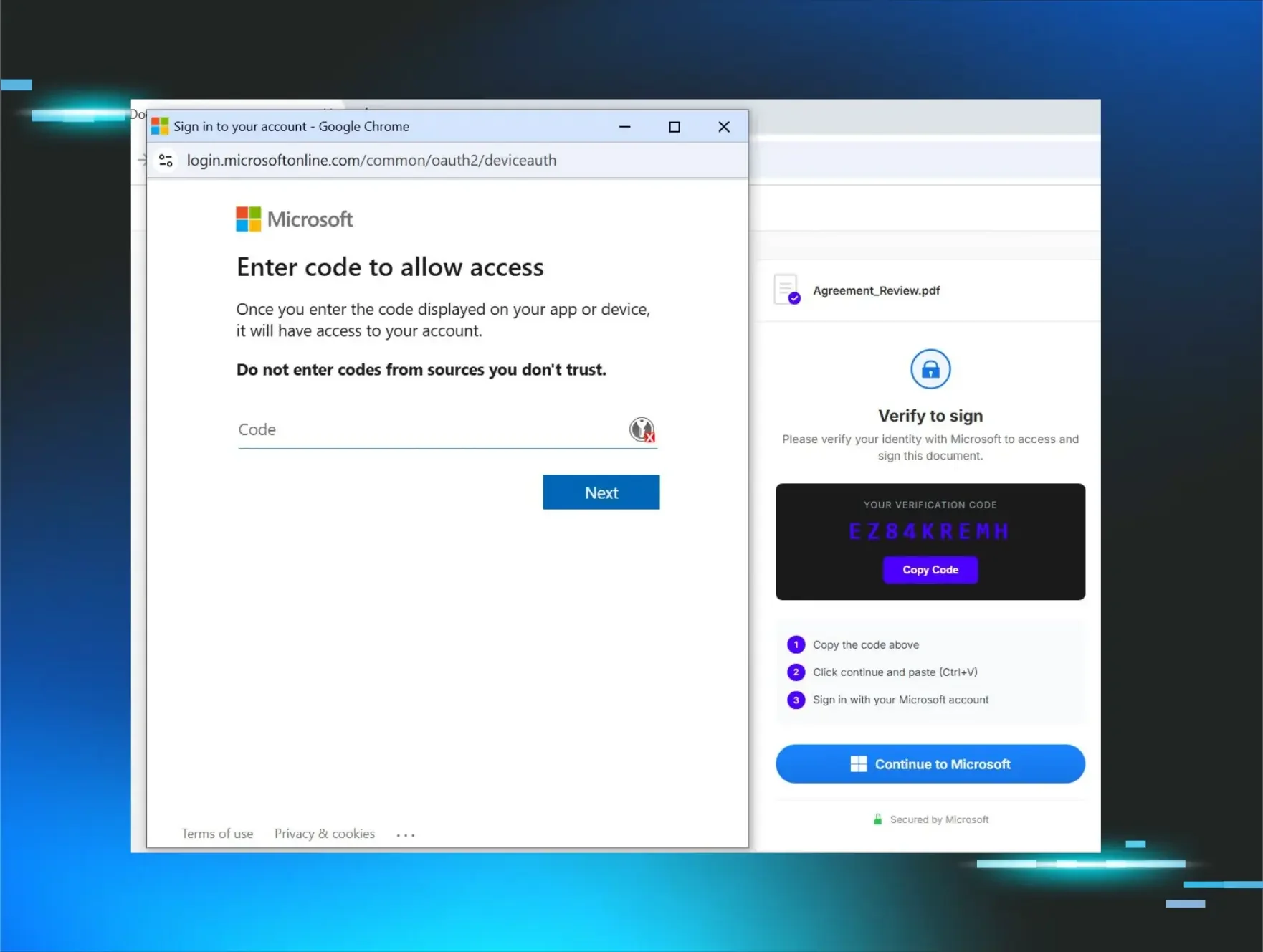
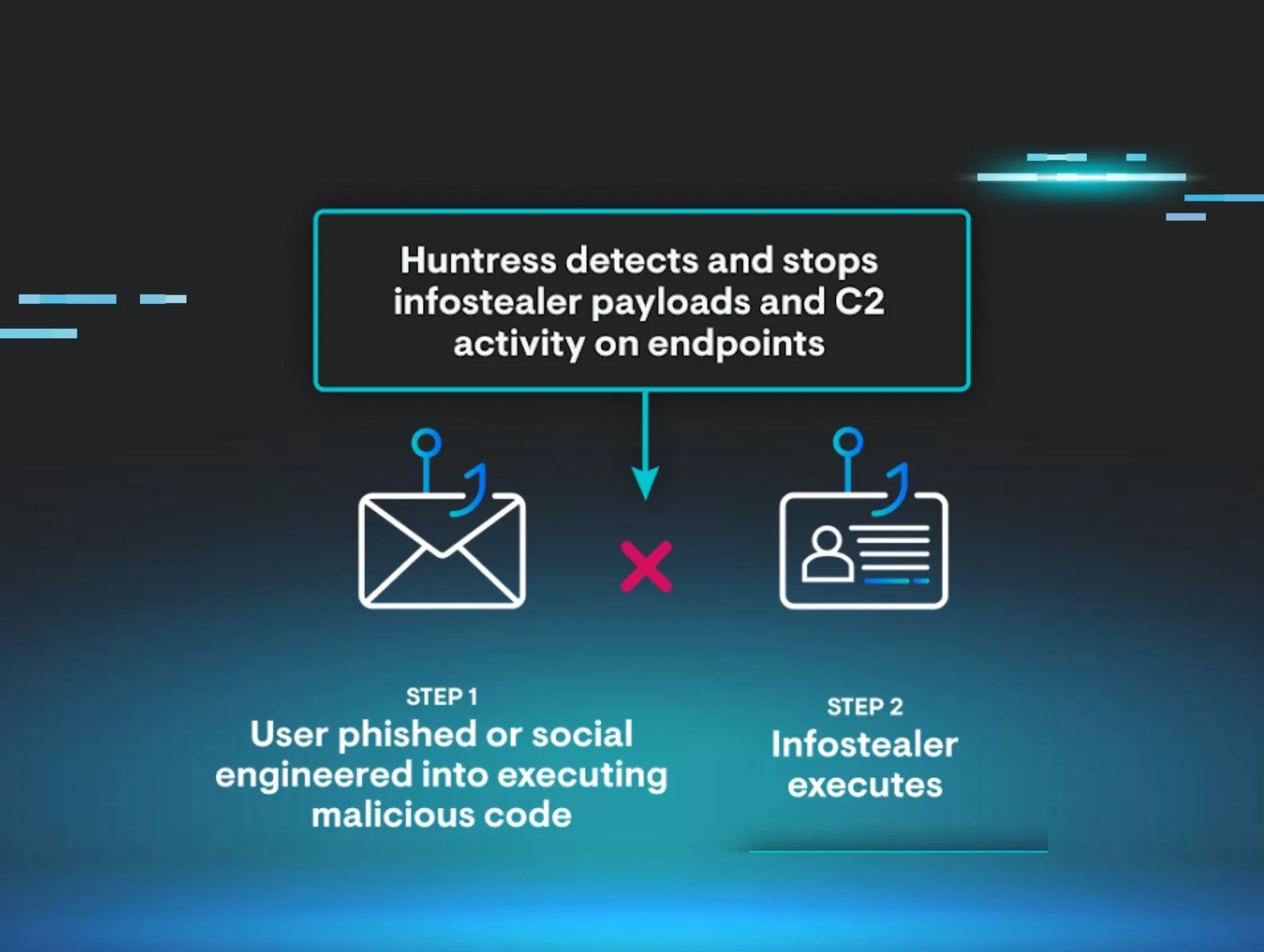
The attack technique at the center of it all was device code phishing, which exploits a completely legitimate authentication flow. If you've ever set up Netflix on a smart TV and entered a code on your phone to authorize the app, you understand exactly how this works. You click a link and enter a standard authentication code.
In a device code phishing attack, attackers insert themselves into this process. They first initiate the authentication process, then follow up with a phishing email. You end up handing the attacker a fully valid session token when you enter the code. No stolen password, no malware, no multi-factor authentication (MFA) to defeat.
Sherrod DeGrippo, General Manager for Global Threat Intelligence at Microsoft, says:
"The user is doing something that feels totally normal. Nothing about this feels suspicious or like credential theft."
That's also what made EvilTokens worth building a product around.
EvilTokens is a phishing-as-a-service platform. Here’s what that means.
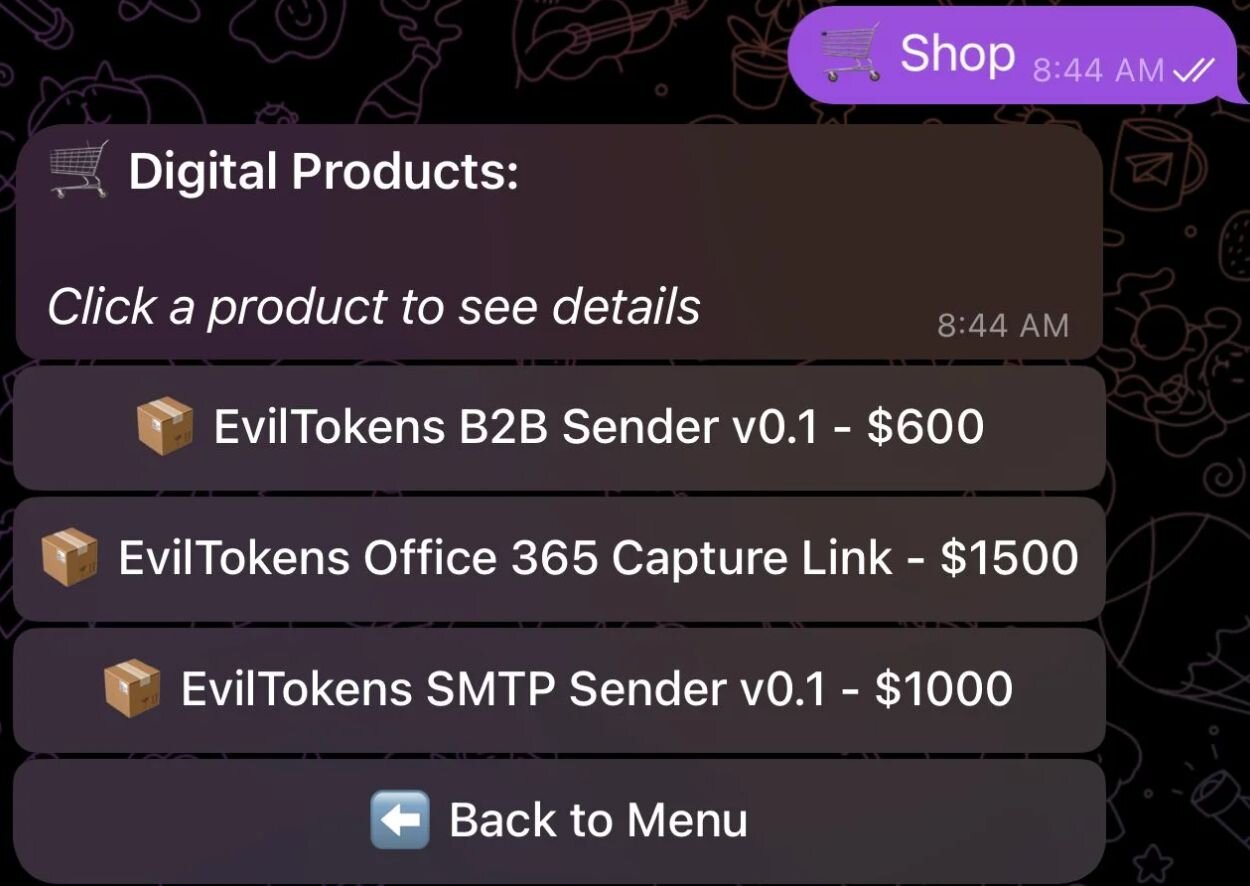
EvilTokens is a phishing-as-a-service (PhaaS) platform that sells phishing attacks at scale and at machine speed. Think of it like a SaaS product, except the product is a full-fledged attack kit. Aspiring cybercriminals can buy full access for around $1,500 plus a $500 maintenance fee. The phishing pages, the lures, the backend token capture, and the relay through Railway are all wrapped up into one convenient product sold on Telegram.
The lures themselves in this campaign were sophisticated and highly personalized to the victims' exact workflows. Construction bid proposals. DocuSign impersonations. Fake Microsoft forms. All with real company names, familiar language, and context that made sense.
That's what makes EvilTokens so effective. Because the attack doesn't look like an attack, it doesn't need to be sophisticated to succeed. But EvilTokens went several steps further.
Figure 1: EvilTokens product store
How AI made EvilTokens faster, smarter, and harder to detect
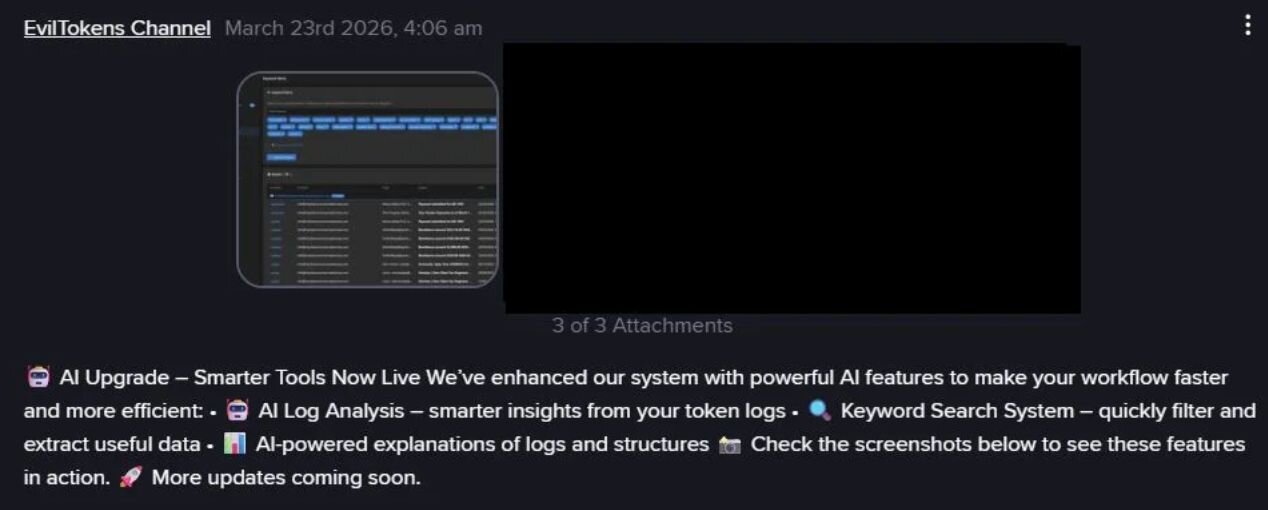
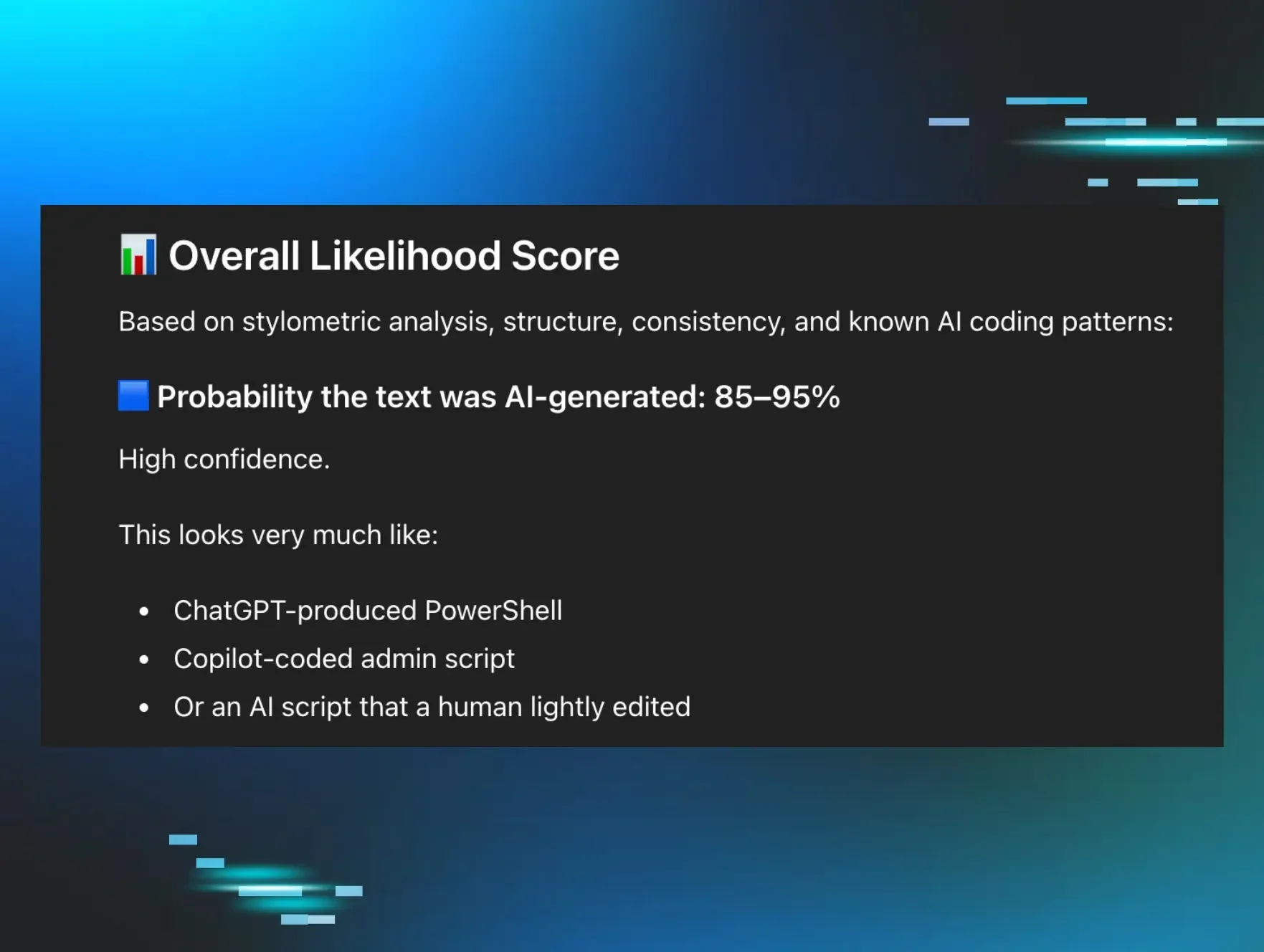
If you dig into the Telegram channels where EvilTokens was being marketed, you'll find explicit references to AI workflows built into the platform. AI for bypassing email filters, tailoring phishing lures, and identifying high-value financial targets.
DeGrippo says:
"Threat actors are using AI across the entire attack chain. From recon all the way to ransomware negotiations being automated."
The lures were role-specific, contextually relevant, and AI-generated to match each victim's exact workflow. And the device code itself was generated dynamically the moment a user landed on the phishing page, eliminating the timing window that had previously limited this type of attack. The operational maturity on display was striking.
Once a victim's token was captured, the platform could scan their inbox, calendar invites, and documents, and use that context to generate convincing follow-on attacks. Things like wire fraud emails written in the victim's own voice, automatically drafted and sent within minutes of token capture. Jamie Levy, Senior Director of Adversary Tactics at Huntress, put it this way:
"This is normally something that you'd have to have a human look at, a social engineer who could figure out how to craft this in the right voice. You can imagine that takes hours—and here we're limiting it down to minutes."
And by the time anyone noticed, the damage was already done, because the infrastructure EvilTokens ran through looked completely clean.
Why traditional email defenses failed against device code phishing
The emails traveled through legitimate Cisco Secure Email, Trend Micro, and Mimecast security controls. The URLs were clean. The authentication flows were real. The infrastructure was trusted.
This is exactly why so much of this attack slipped through defenses. Domain blocklists couldn't catch it. Spam filters didn't flag it. Even the MFA looked fine, because the user completed MFA correctly. They did exactly what they were trained to do. They just did it for the wrong session.
The phishing-as-a-service ecosystem behind EvilTokens
The scary part is that EvilTokens is far from an isolated event, according to both Levy and DeGrippo. It's a signal for what's to come.
The broader phishing-as-a-service ecosystem is thriving. Other kits like Tycoon2FA, BlueKit, and Kali365 are operating with similar levels of infrastructure and sophistication. Some threat actors run full customer service operations on Telegram, offering onboarding support and loyalty discounts. DeGrippo explained:
"The financially motivated threat landscape is an ecosystem. It is not siloed individual groups. It is people selling kits, selling infrastructure, buying and trading credentials."
And AI is accelerating all of it. The barrier to launching a targeted, convincing, and scaled phishing attack is lower than ever.
How to defend against device code phishing and MFA bypass attacks
The answer isn't more alerts. It's a smarter context.
It's not just asking whether an authentication event was successful, but whether it makes sense. Is this device the one the user normally authenticates from? Is this authentication flow consistent with their role? Tools like Microsoft Entra Conditional Access can enforce these contextual constraints and restrict device code flow to specific approved scenarios.
DeGrippo says:
"Adding more alerts does not solve this problem. So you actually need, as a defender, context on who is the user, what are they trying to access, and is it consistent with their normal workflow. You really have to think about behavior-based detection."
Phishing-resistant MFA, specifically FIDO2 and passkeys, is also critical. SMS-based MFA is not enough.
The good news is that defenders aren’t working alone. This campaign was caught because Huntress saw patterns across thousands of organizations simultaneously. When the pattern became clear, we pushed a conditional access policy across more than 60,000 tenants to block Railway's infrastructure outright. This response matched the campaign's own speed. That visibility is what makes scale work in the defenders' favor, too.
Levy and DeGrippo recommend these practical steps that you can start taking now:
-
Tighten conditional access policies, especially around device code authentication flows
-
Monitor for new device registrations and revoke refresh tokens if compromise is suspected
-
Move toward phishing-resistant MFA. FIDO2 and passkeys use public-key cryptography, meaning there's no replayable token for attackers to steal
-
Stop blaming users for clicking things that looked completely legitimate, because in attacks like this, they did nothing wrong
EvilTokens is a watershed moment. Individually, these techniques aren't new. But combined with orchestration, automation, and AI-assisted scale, they represent something genuinely different. The rules of phishing have changed. The attackers have a product roadmap. It’s time defenders build one too.