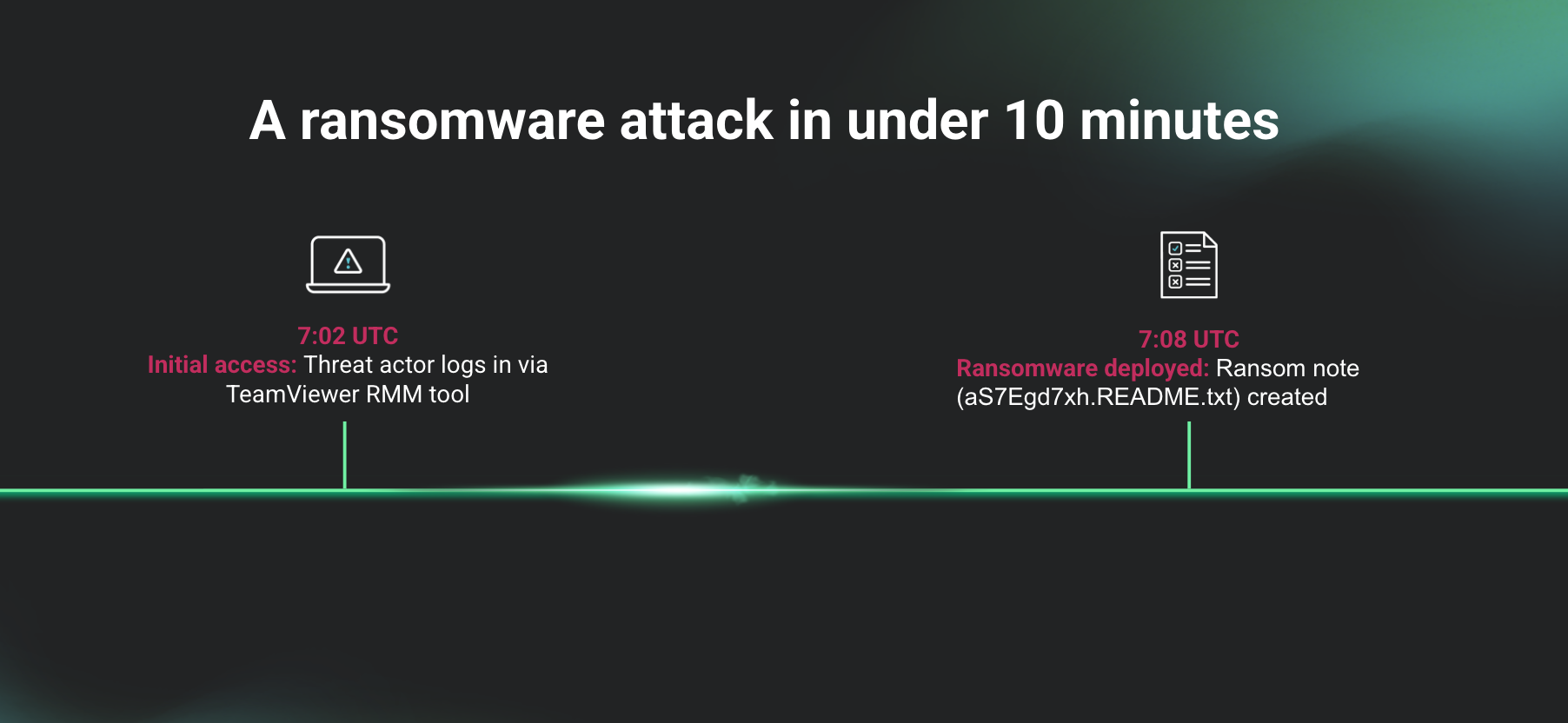
Our SOC recently uncovered a five-minute, 40-second LockBit attack.
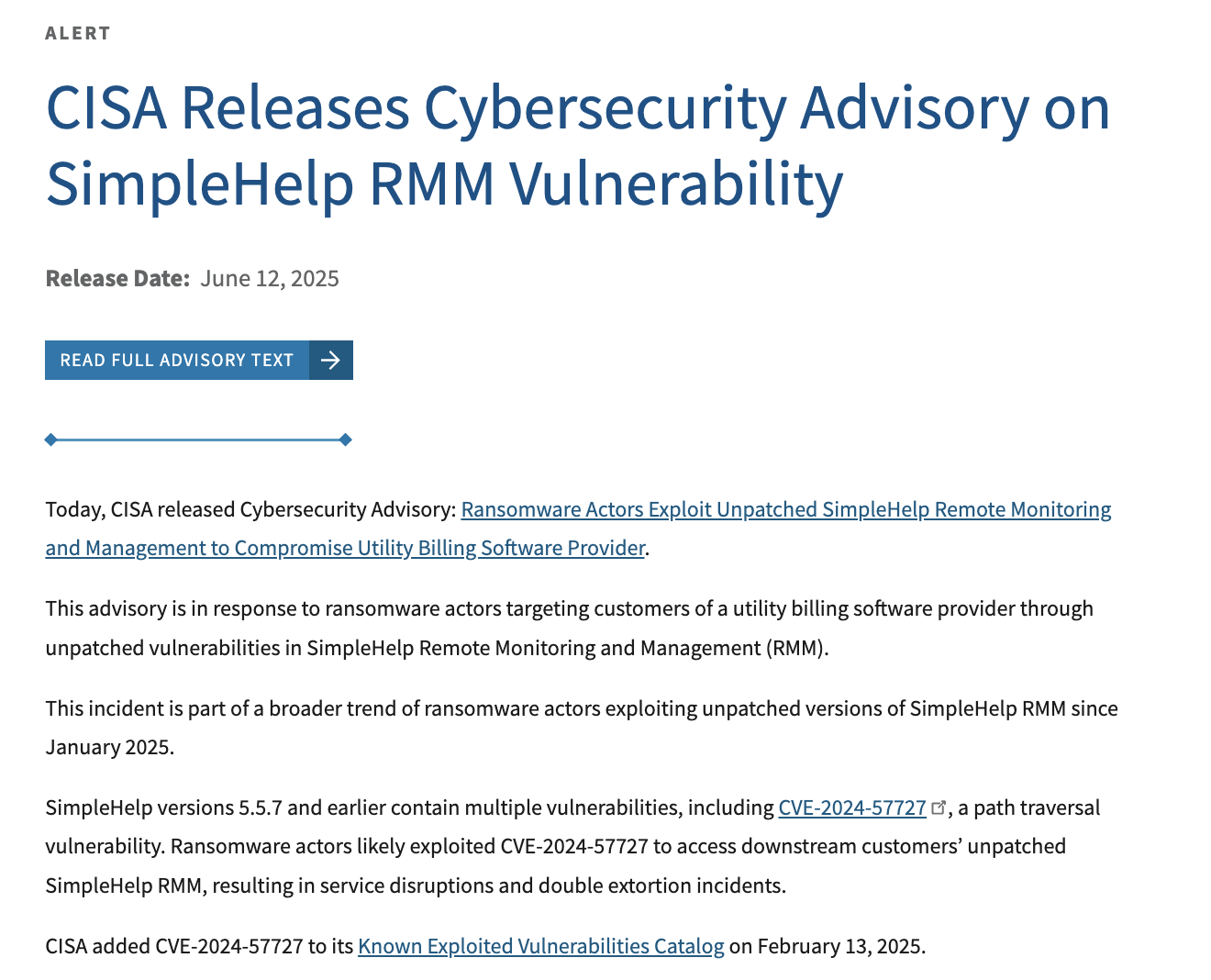
In June, a dentist office’s ransomware canaries were triggered for LockBit. After we tasked and reviewed the logs, we found the threat actor accessed a TeamViewer remote monitoring and management (RMM) tool to deploy the ransomware. The aS7Egd7xh.README.txt ransom note was created at 7:08 UTC, only around five minutes after the first initial access occurred at 7:02 UTC.
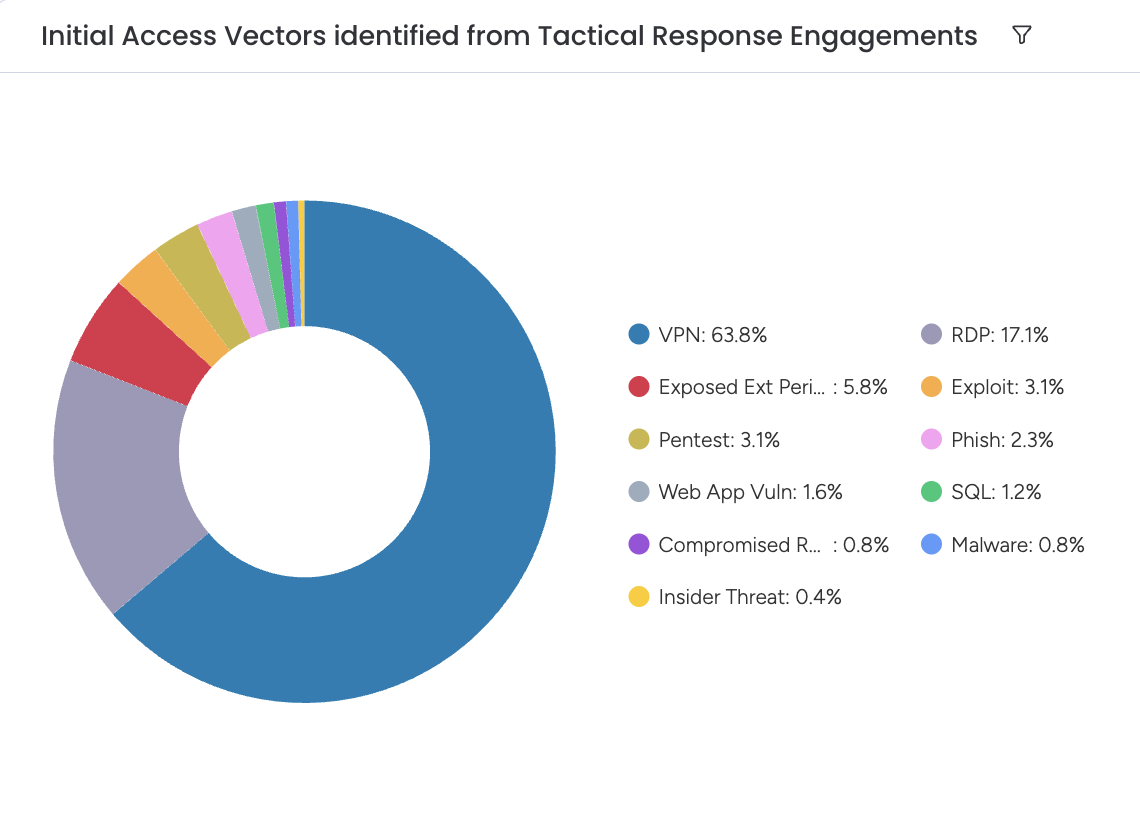
While the average time-to-ransom is 16.88 hours, according to the Huntress 2025 Cyber Threat Report, a 10-minute attack path is alarming. This spells out why it is absolutely essential to catch attackers as early as possible in the ransomware attack path.






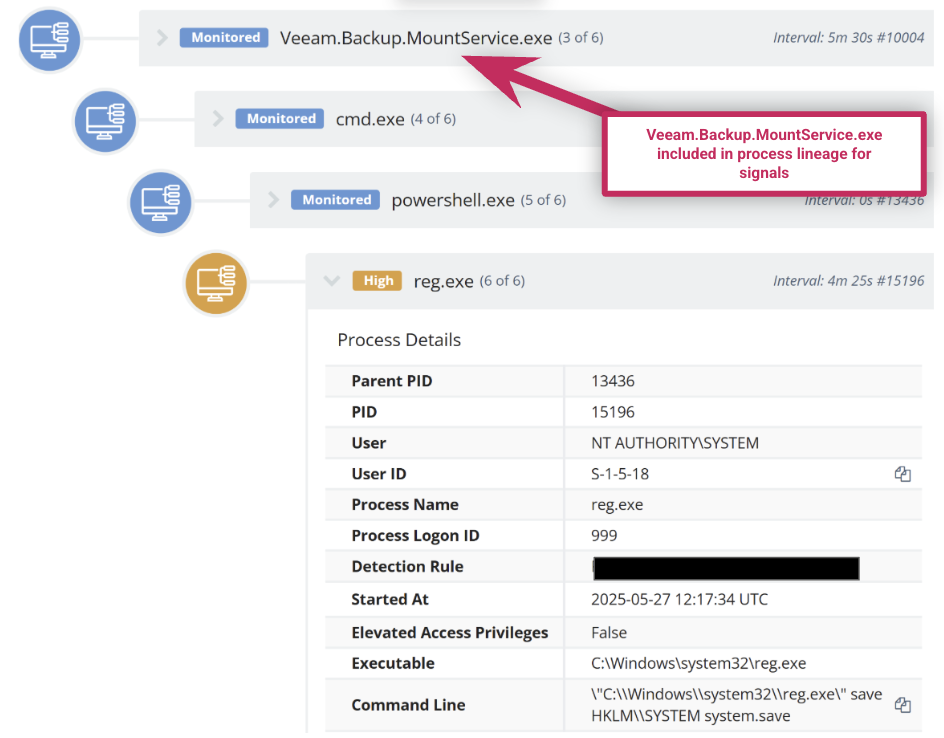
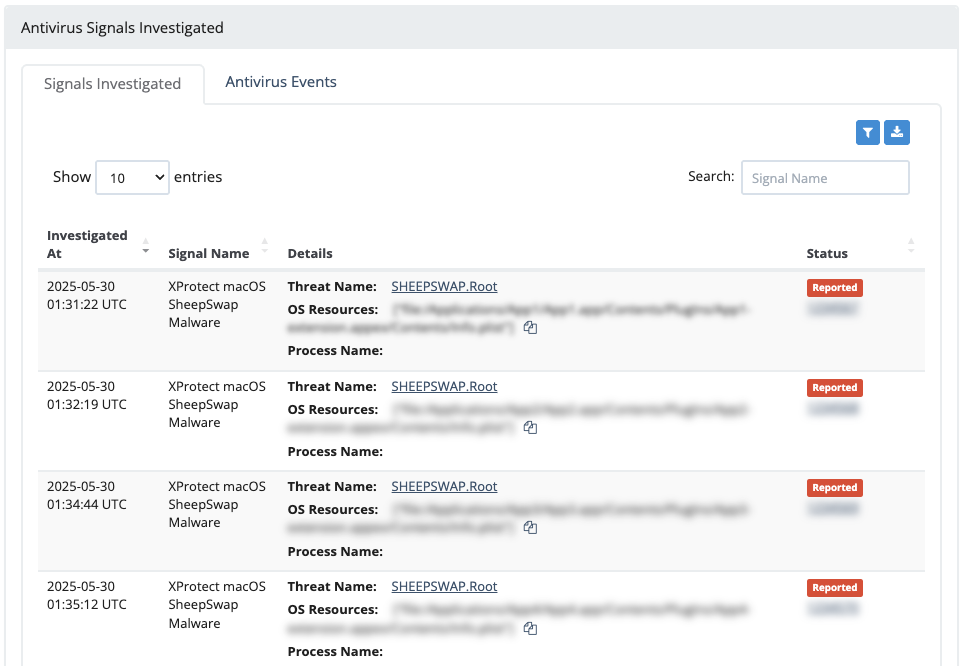 Huntress Managed Security Platform with investigated XProtect alerts
Huntress Managed Security Platform with investigated XProtect alerts