
Huntress 2025 Cyber Threat Report


Download Your Report

Get details on the cyberattacks we saw most last year, learn key industry insights, and build strategies to outsmart the most malicious hackers. It's all in the Huntress 2025 Cyber Threat Report, and it's more than just a recap of last year's cyberattacks. It's packed with real-world tactics to stay ahead of hackers.
Here's a glimpse of what's inside
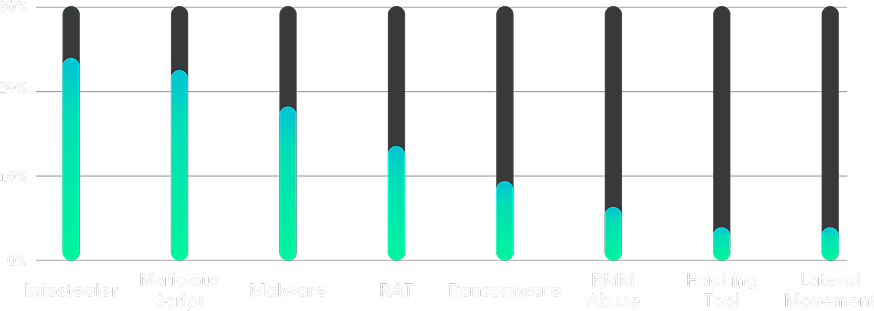
The top cyber threats of 2024
Infostealers thrived, accounting for a staggering 24% of incidents. Right behind them were malicious scripts at 22%, mainly due to their ability to dodge detection and automate attacks.
Healthcare and education are preferred targets.
These industries faced the brunt of attacks, accounting for 38% of all incidents.
Add tech, manufacturing, and government as well, and that’s another 32% of cyberattacks aimed at our most important sectors.

And that’s only the beginning. Download the 2025 Cyber Threat Report now and arm yourself with the knowledge to defend against whatever 2025 throws your way.
[PH] Learn More About Phishing
[PH] Huntress delivers everything you want from a security tool, all designed with the unique needs of outsourced IT and security teams in mind.
[PH] Phishing attempts can show up as messages from your bank, your boss, your utility providers, or even the government. One click from one user can compromise an entire network and inadvertently let hackers deploy ransomware, steal information, or worse.
[PH] The median time it takes for a user to click a link and enter information is less than 60 seconds. With a turnaround time that quick, it's no wonder phishing is one of the preferred methods used by hackers. (2024 Verizon Data Breach Report)




